Figure 1
From: Secure secondary utilization system of genomic data using quantum secure cloud
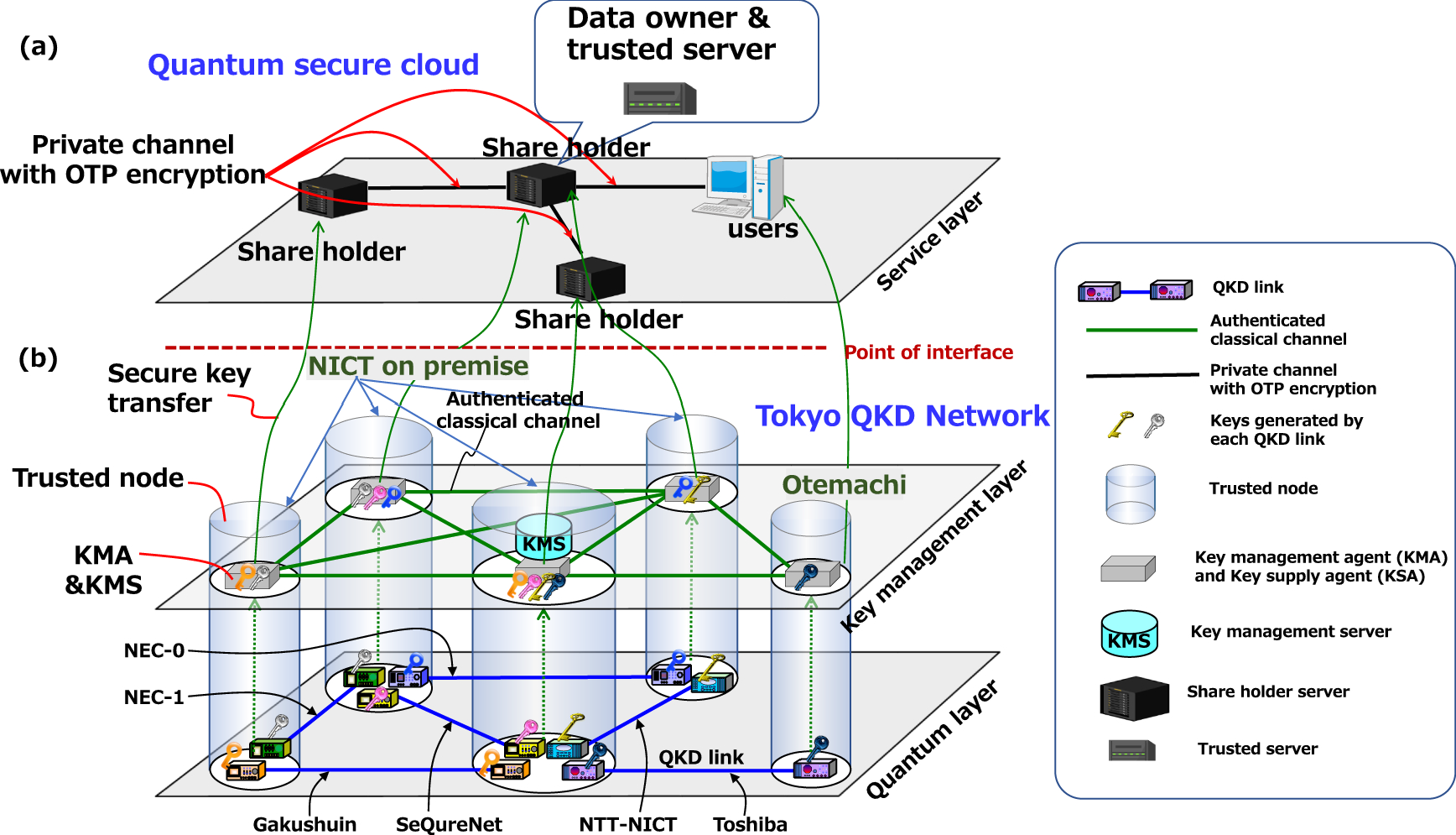
Conceptual view of Tokyo QKD Network. The QKD network works as a secure key supply infrastructure. (a) Service layre; Secret sharing or other services are installed in this QKD network. The data owner, the trusted server, share holders, and the user at the service layer communicate through OTP encrypted communication lines in which secure key are provided from the QKD network. Once supplied with the keys or random numbers, the key data in the QKD network are erased and the responsibility of key management moves to users at service layer. (b) quantum layer and key management layer; Generated keys in each QKD link are pushed up to servers, called key management agents (KMAs). Each KMA is set in a physically protected place, referred to as “a trusted node”. A key supply agent (KSA) is integrated to the KMA. The KSAs supply users the keys. A key management server (KMS) gathers link information and instructs KMAs to execute key relay according to request from the service layer.
