Abstract
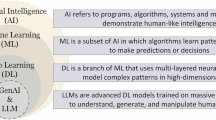
This paper presents an AI-based generative model to address the cybersecurity threats in software development for Small and Medium Enterprises (SMEs). The model aims to address the unique challenges SMEs face in implementing effective cybersecurity practices by leveraging generative AI to enhance threat detection, prevention, and response. Initially, we conducted a multivocal literature review (MLR) and an empirical survey to identify and validate cybersecurity threats and the generative AI practices used in secure software development for SMEs. An expert panel review was then assigned for the process of artificial neural network (ANN) and interpretive structural model (ISM). The ANN model can predict potential cybersecurity threats by learning from historical data and software development patterns. ISM is used to (1) structure and visualize (2) relations between identified threats and mitigation approaches and (3) offer a combined, multi-layered risk management methodology. A case study was conducted to evaluate the effectiveness of the proposed model. The evaluation has shown that the model significantly enhances SME online security and enables rapid adoption of sophisticated AI-based practices for detecting and responding to primary and advanced cyber threats. Phishing and ransomware received high assessments (Advanced), whereas some advanced techniques, e.g., AI-guided evasion and zero-day attacks, were at early stages of development (Understanding and Development). The general results indicated that generative AI can help organizations enhance SME cybersecurity, and some efforts are underway to develop use cases for advanced threats further. The AI-based generative model is a viable and scalable approach to the cybersecurity of SME software development. Such AI-based practices will enable SMEs to effectively protect themselves against various cyber threats systematically. Future studies should focus on developing contemporary threat strategies and on the impediments to global implementation, particularly in less resource-rich settings.
Similar content being viewed by others
Data availability
All data generated or analyzed during this study are included in this manuscript. If someone wants to request the data from this study, kindly contact “Rafiq Ahmad Khan” ( [rafiqahmadk@gmail.com](mailto: rafiqahmadk@gmail.com) ).
References
Almeida, F. Comparative analysis of EU-based cybersecurity skills frameworks. Comput. Secur. 151, 104329 (2025).
Birthriya, S. K., Ahlawat, P. & Jain, A. K. Detection and prevention of spear phishing attacks: A comprehensive survey. Comput. & Security, 151, 104317 (2025).
Yan, P. & Talaei Khoei, T. Securing the internet of things: A comprehensive review of ransomware attacks, detection, countermeasures, and future prospects. Franklin Open. 11, 100256 (2025).
Chanda, R. C., Vafaei-Zadeh, A., Hanifah, H. & Nikbin, D. Assessing cybersecurity awareness among bank employees: A multi-stage analytical approach using PLS-SEM, ANN, and fsQCA in a developing country context. Comput. & Security, 149, 104208 (2025).
Waelchli, S. & Walter, Y. Reducing the risk of social engineering attacks using SOAR measures in a real world environment: A case study. Comput. & Security, 148, 104137 (2025).
Ali, J. et al., A deep dive into cybersecurity solutions for AI-driven IoT-enabled smart cities in advanced communication networks. Comput. Commun. 229, 108000 (2025).
Al Aamer, A. K. & Hamdan, A. Cyber security awareness and smes’ profitability and continuity: literature review, in Emerging Trends and Innovation in Business and Finance, (eds Khoury, R. E. & Nasrallah, N.) ed Singapore: Springer Nature Singapore, 593–604. (2023).
Chaudhary, S., Gkioulos, V. & Katsikas, S. A quest for research and knowledge gaps in cybersecurity awareness for small and medium-sized enterprises. Comput. Sci. Revi.. 50, 100592, (2023).
Nadella, G. S. et al., Generative AI-Enhanced Cybersecurity Framework for Enterprise Data Privacy Management. Computers. 14, 55 (2025).
Khan, H. U. et al. AI-driven cybersecurity framework for software development based on the ANN-ISM paradigm. Sci. Rep. 15, 13423 2025.
Coppolino, L., D’Antonio, S., Mazzeo, G. & Uccello, F. The good, the bad, and the algorithm: The impact of generative AI on cybersecurity. Neurocomputing. 623, 129406 (2025).
Khan, R. A., Khan, H. U., Alwageed, H. S., Hashimi, H. A. & Keshta, I. 5G networks security mitigation model: an ANN-ISM hybrid approach. IEEE Open. J. Commun. Soc. 6, 881–925 (2025).
Alzahrani, A. & Khan, R. A. Secure software design evaluation and decision making model for ubiquitous computing: A two-stage ANN-Fuzzy AHP approach. Comput. Hum. Behavior. 108109 (2023).
Hathal, S., Alwageed & Ghani, A. Ismail. Keshta, Rafiq. Ahmad.Khan, Abdulrahman. Alzahrani, Muhammad. Usman. Tariq, and An empirical study for mitigating sustainable cloud computing challenges using ISM-ANN. PLOS ONE. 19, 1–34, (2024).
Wong, L. W., Lee, V. H., Tan, G. W. H., Ooi, K. B. & Sohal, A. The role of cybersecurity and policy awareness in shifting employee compliance attitudes: Building supply chain capabilities. Int. J. Inf. Manag. 66, (2022).
Caniglia, A., Dentamaro, V., Galantucci, S. & Impedovo, D. FOBICS: Assessing project security level through a metrics framework that evaluates DevSecOps performance. Inf. Software Technol. 178, 107605, (2025).
Rawindaran, N. et al., Enhancing Cyber Security Governance and Policy for SMEs in Industry 5.0: A Comparative Study between Saudi Arabia and the United Kingdom, Digital. 3, 200–231 2023.
Kaur, R., Klobučar, T. & Gabrijelčič, D. Harnessing the power of language models in cybersecurity: A comprehensive review. Int. J. Inf. Manag. Data Insights, 5, 100315 (2025).
Olusanya, O. O., Jimoh, R. G., Misra, S. & Awotunde, J. B. A neuro-fuzzy security risk assessment system for software development life cycle. Heliyon, 10, e33495 (2024).
Dutta, I. K., Ghosh, B., Carlson, A., Totaro, M. & Bayoumi, M. Generative Adversarial Networks in Security: A Survey, in 11th IEEE Annual Ubiquitous Computing, Electronics & Mobile Communication Conference (UEMCON), 0399–0405 (2020).
ul Haq, F., Suki, N. M., Zaigham, H., Masood, A. & Rajput, A. Exploring AI Adoption and SME Performance in Resource-Constrained Environments: A TOE–RBV Perspective with Mediation and Moderation Effects. J. Digital Econ., (2025).
Olatunji, A. P., Alozie, E., Olagunju, H. & Udensi, F. A Systematic Review of the Role of Artificial Intelligence in Cybersecurity, in IEEE 5th International Conference on Electro-Computing Technologies for Humanity (NIGERCON), 1–6. (2024).
Gupta, A. K., Dixit, N., Kumar, S., Rawat, P. & Madhumita A Novel Hybrid Approach for Threat Detection in Cyber Security using AI algorithm, in International Conference on Computing, Sciences and Communications (ICCSC), 1–6. (2024).
Zavodna, L., Ueberwimmer, M. & Frankus, E. Barriers to the implementation of artificial intelligence in small and medium sized enterprises: pilot study. J. Econ. Management, 46, 331–352 2024.
Sharma, O., Sharma, A. & Kalia, A. MIGAN: GAN for facilitating malware image synthesis with improved malware classification on novel dataset. Exp. Syst. Appl. 241, 122678 (2024).
Sharma, P., Kumar, M., Sharma, H. K. & Biju, S. M. Generative adversarial networks (GANs): Introduction, Taxonomy, Variants, Limitations, and applications. Multimedia Tools Applications, 2024.
Morrison, O. M., Pichi, F. & Hesthaven, J. S. GFN: A graph feedforward network for resolution-invariant reduced operator learning in multifidelity applications. Comput. Methods Appl. Mech. Eng. 432 117458, (2024).
Levshun, D., Levshun, D. & Kotenko, I. ForecaState: Framework for industrial Internet of Things state forecasting using recurrent neural networks with hyperparameters optimization. Engi. App. Artificial Intelligence, 159, 111627 (2025).
Khadidos, A. O. et al. CyberSentry: Enhancing SCADA security through advanced deep learning and optimization strategies. Int. J. Critical Inf. Protection. 50, 100782 (2025).
Agrafiotis, G. et al. A Deep Learning-based Malware Traffic Classifier for 5G Networks Employing Protocol-Agnostic and PCAP-to-Embeddings Techniques, presented at the Proceedings of the 2023 European Interdisciplinary Cybersecurity Conference, Stavanger, Norway, (2023).
Das, S., Tariq, A., Santos, T., Kantareddy, S. S. & Banerjee, I. Recurrent neural networks (RNNs): Architectures, training Tricks, and introduction to influential research, in Machine Learning for Brain Disorders, (ed Colliot, O.) ed New York, NY: Springer US, 117–138. (2023).
Crisostomo, J., Bacao, F. & Lobo, V. Machine learning methods for detecting smart contracts vulnerabilities within Ethereum blockchain – A review, Exp. syst. Appl.268, 126353 (2025).
Udas, P. B., Karim, M. E. & Roy, K. S. SPIDER: A shallow PCA based network intrusion detection system with enhanced recurrent neural networks. J. King Saud University - Computer Inf. Sci. 34, 10246–10272 (2022).
Alahmari, A. & Duncan, B. Cybersecurity Risk Management in Small and Medium-Sized Enterprises: A Systematic Review of Recent Evidence, in 2020 International Conference on Cyber Situational Awareness, Data Analytics and Assessment (CyberSA), 1–5. (2020).
Leotta, M., Ricca, F., Marchetto, A. & Olianas, D. An empirical study to compare three web test automation approaches: NLP-based, programmable, and capture and replay. J. Software: Evol. Process. 36, e2606 (2024).
Khan, R. A., Akbar, M. A., Rafi, S., Almagrabi, A. O. & Alzahrani, M. Evaluation of requirement engineering best practices for secure software development in GSD: An ISM analysis. J. Software: Evolution Process. vol. n/a, 1–19, (2023).
Rajan, R. et al. Developing a modified total interpretive structural model (M-TISM) for organizational strategic cybersecurity management. Technol. Forecasting Soc. Change. 170, 120872. (2021).
Etemadi, N., Van Gelder, P. & Strozzi, F. An ISM Modeling of Barriers for Blockchain/Distributed Ledger Technology Adoption in Supply Chains towards Cybersecurity. Sustainability. 13, 4672, (2021).
Garousi, V., Felderer, M. & Mäntylä, M. V. Guidelines for including grey literature and conducting multivocal literature reviews in software engineering. Inf. Software Technol. 106, 101–121 2019. (2019).
Itodo, C. & Ozer, M. Multivocal literature review on zero-trust security implementation, Comput. & Security. 141, 103827 (2024).
Akbar, M. A., Smolander, K., Mahmood, S. & Alsanad, A. Toward successful DevSecOps in software development organizations: A decision-making framework. Inf. Software Technol.. 147, 106894, (2022).
Al-Matouq, H., Mahmood, S., Alshayeb, M. & Niazi, M. A maturity model for secure software design: A multivocal study. IEEE Access. 8, 215758–215776 (2020).
Wagner, S. et al., Status Quo in Requirements Engineering: A Theory and a Global Family of Surveys. ACM Trans. Softw. Eng. Methodol, 28, 1–48, (2019).
M. Humayun, M. Niazi, M. Assiri, and M. Haoues, Secure Global Software Development:A Practitioners’ Perspective, Appl. Sci. 13, 2465 (2023).
Ilyas, M., Khan, S. U., Khan, H. U. & Rashid, N. Software integration model: An assessment tool for global software development vendors. J. Software: Evolution Process. vol. n/a, e2540, (2023).
Creswell, J. W. Research design: qualitative, quantitative and mixed methods approaches, 3rd edition: Sage, London, (2009).
Lethbridge, T. C., Sim, S. E. & Singer, J. Studying software engineers: data collection techniques for software field studies. Empirical Softw. Eng., 10, 311–341 2005.
Lee, S. C. Prediction of concrete strength using artificial neural networks. Eng. Struct. 25, 849–857 (2003).
Leong, L. Y., Hew, T. S., Tan, G. W. H. & Ooi, K. B. Predicting the determinants of the NFC-enabled mobile credit card acceptance: A neural networks approach. Exp. Syst. Appl., 40, 5604–5620 (2013).
Chan, F. T. & Chong, A. Y. A SEM–neural network approach for Understanding determinants of interorganizational system standard adoption and performances. Decis. Support Syst. 54, 621–630 (2012).
Zhang, H. et al. A Framework for Designing Fair Ubiquitous Computing Systems, arXiv preprint arXiv:2308.08710, (2023).
Chong, A. Y. L. Predicting m-commerce adoption determinants: A neural network approach. Exp. Syst. Appl. 40, 523–530 (2013).
Hertz, J., Krogh, A., Palmer, R. G. & Horner, H. Introduction To the Theory of Neural Computation Ed (American Institute of Physics, 1991).
Alnaizy, R., Aidan, A., Abachi, N. & Jabbar, N. A. Neural network model identification and advanced control of a membrane biological reactor. J. Membrane Sep. Technol. 2, 231 (2013).
Sage, A. P. Interpretive Structural Modeling: Methodology for Large Scale Systems 1–445 (McGraw-Hill,, 1977).
Ravi, V. & Shankar, R. Analysis of interactions among the barriers of reverse logistics. Technological Forecasting and Social Change, 72, 1011–1029 (2005).
Rafi, S., Akbar, M. A., Mahmood, S., Alsanad, A. & Alothaim, A. Selection of devops best test practices: A hybrid approach using ISM and fuzzy TOPSIS analysis. J. Software: Evol. Process. 34, e2448 (2022).
Qureshi, K. M. et al. Exploring the lean implementation barriers in small and Medium-Sized enterprises using interpretive structure modeling and interpretive ranking process. Appl. Syst. Innov. 5, 84 (2022).
Talib, F., Rahman, Z. & Qureshi, M. R. An interpretive structural modeling approach for modeling the practices of total quality management in service sector. Int J. Modelling Oper. Management, Inderscience, 1, 223–250, (2011).
Rafi, S. et al. Exploration of DevOps testing process capabilities: An ISM and fuzzy TOPSIS analysis, Appl. Soft Comput., 116, 108377 (2022).
Sakar, C., Koseoglu, B., Toz, A. C. & Buber, M. Analysing the effects of liquefaction on capsizing through integrating interpretive structural modelling (ISM) and fuzzy Bayesian networks (FBN), Ocean Engineering, 215, 107917 (2020).
Patel, M. N., Pujara, A. A., Kant, R. & Malviya, R. K. Assessment of circular economy enablers: Hybrid ISM and fuzzy MICMAC approach. J. Clean. Production, 317, 128387 (2021).
Ali, S., Huang, J., Khan, S. U. & Li, H. A framework for modelling structural association amongst barriers to software outsourcing partnership formation: an interpretive structural modelling approach. J. Software: Evol. Process. 32, e2243 (2020).
Ali, S. et al. Analyzing the interactions among factors affecting cloud adoption for software testing: a two-stage ISM-ANN approach. Soft Computing, 26, 8047–8075 (2022).
Qureshi, K. M. et al. Accomplishing Sustainability in Manufacturing System for Small and Medium-Sized Enterprises (SMEs) through Lean Implementation. Sustainability, 14, 9732 (2022).
Qureshi, M. R. & Kumar, P. An integrated model to identify and classify the key criteria and their role in the assessment of 3PL services providers. Asia Pac. J. Mark. Logistics, 20, 227–249 (2008).
Qureshi, M. R. & Kumar, P. Modeling the logistics outsourcing relationship variables to enhance shippers’ productivity and competitiveness in logistical supply chain. Int. J. Productivity Perform. Management, 56, 689–714 (2007).
Azeez, N. A. et al. Adopting automated whitelist approach for detecting phishing attacks, Comput. & Security., 108, 102328 (2021).
Ferrag, M. A. et al., Generative AI in Cybersecurity: A Comprehensive Review of LLM Applications and Vulnerabilities, Internet of Things and Cyber-Physical Systems, (2025).
Ain, Q. U., Javed, A. & Irtaza, A. DeepEvader: An evasion tool for exposing the vulnerability of deepfake detectors using transferable facial distraction blackbox attack. Eng. App. Artificial Intell. 145, 110276 (2025).
Patsakis, C., Casino, F. & Lykousas, N. Assessing LLMs in malicious code deobfuscation of real-world malware campaigns. Exp. Syst. Appl., 256, 124912 (2024).
Austin, A., Holmgreen, C. & Williams, L. A comparison of the efficiency and effectiveness of vulnerability discovery techniques. Inf. Softw. Technol. 55, 1279–1288 (2013).
Nobles, C. The weaponization of artificial intelligence in cybersecurity: A systematic review. Procedia Comput. Sci. 239, 547–555 (2024).
Iturbe, E., Llorente-Vazquez, O., Rego, A., Rios, E. & Toledo, N. Unleashing offensive artificial intelligence: Automated attack technique code generation. Comput. & Security. 147, 104077 (2024).
Andreoli, A., Lounis, A., Debbabi, M. & Hanna, A. On the prevalence of software supply chain attacks: Empirical study and investigative framework. For. Sci. Int.: Digital Investigation. 44, 301508, (2023).
Arivudainambi, D., Varun Kumar, K. A., & Visu, P. Malware traffic classification using principal component analysis and artificial neural network for extreme surveillance. Comput. Commun. 147, 50–57 (2019).
Al-Subaiey, A., Al-Thani, M., Abdullah Alam, N., Antora, K. F. & Khandakar, A. and S. M. A. Uz Zaman, Novel interpretable and robust web-based AI platform for phishing email detection. Comput. Electrical Eng. 120, 109625 (2024).
Lin, Z. et al. Tracking phishing on Ethereum: Transaction network embedding approach for accounts representation learning, Comput. & Security., 135, 103479 (2023).
Majgave, A. B. & Gavankar, N. L. Automatic phishing website detection and prevention model using transformer deep belief network. Comput. & Security., 147, 104071 (2024).
Nanda, M., Saraswat, M. & Sharma, P. K. Enhancing cybersecurity: A review and comparative analysis of convolutional neural network approaches for detecting URL-based phishing attacks, e-Prime-Advances in Electrical Engineering, Electronics and Energy, 8, 100533 (2024).
Sushma, K. S. N., Viji, C., Rajkumar, N., Ravi, J., Stalin, M., & Najmusher, H. Healthcare 4.0: A Review of Phishing Attacks in Cyber Security. Procedia Computer Sci., 230, 874–878 (2023).
Habbal, A., Ali, M. K. & Abuzaraida, M. A. Artificial Intelligence Trust, Risk and Security Management (AI TRiSM): Frameworks, applications, challenges and future research directions. Exp. Syst. Appl., 240, 122442 (2024).
Kumar, A. et al. Advances in DeepFake detection algorithms: Exploring fusion techniques in single and multi-modal approach. Inf. Fusion. 118 102993 (2025).
Rabhi, M., Bakiras, S. & Di Pietro, R. Audio-deepfake detection: adversarial attacks and countermeasures. Exp. Syst. Appl. 250, 123941 (2024).
Djenna, A., Belaoued, M., Lifa, N. & Moualdi, D. E. Proactive Anti-Ransomware cybersecurity approach. Procedia Comput. Sci. 238, 821–826 (2024).
Gaber, M. G., Ahmed, M. & Janicke, H. Malware detection with artificial intelligence: A systematic literature review. ACM Comput. Surv, 56, 148 (2024).
Jáñez-Martino, F., Alaiz-Rodríguez, R., González-Castro, V., Fidalgo, E. & Alegre, E. Spam email classification based on cybersecurity potential risk using natural language processing. Knowledge-Based Syst., 310, 112939 (2025).
Ma, K. P., Ryu, D. J. & Lee, S. J. Reverse Analysis Method and Process for Improving Malware Detection Based on XAI Model. Computers, Materials Continua, 81, 4485–4502 (2024).
Sîrbu, A. G. & Czibula, G. Automatic code generation based on Abstract Syntax-based encoding. Application on malware detection code generation based on MITRE Attack techniques. Exp. Syst. Appl., 264, 125821 (2025).
Vouvoutsis, V., Casino, F. & Patsakis, C. Beyond the sandbox: Leveraging symbolic execution for evasive malware classification. Comput. & Security., 149, 104193 (2025).
Wang, M., Zhang, Y. & Wen, W. Improved capsule networks based on Nash equilibrium for malicious code classification. Comput. & Security., 136 103503 (2024).
Alghawli, A. S. A. & Radivilova, T. Resilient cloud cluster with DevSecOps security model, automates a data analysis, vulnerability search and risk calculation. Alexandria Eng. J., 107, 136–149 (2024).
Althar, R. R., Samanta, D., Kaur, M., Singh, D. & Lee, H. N. Automated Risk Manage. Based Softw. Secur. Vulnerabilities Manage. IEEE Access, 10, 90597–90608, (2022).
Casola, V., De Benedictis, A., Mazzocca, C. & Orbinato, V. Secure software development and testing: A model-based methodology. Comput. & Security. 137, 103639 (2024).
del-Hoyo-Gabaldon, J. A., Moreno-Cediel, A., Garcia-Lopez, E., Garcia-Cabot, A. & de-Fitero-Dominguez, D. Automatic dataset generation for automated program repair of bugs and vulnerabilities through SonarQube, SoftwareX, 26, 101664 (2024).
Kirilchuk, S., Reutov, V., Nalivaychenko, E., Shevchenko, E. & Yaroshenko, A. Ensuring the security of an automated information system in a regional innovation cluster. Transp. Res. Procedia, 63, 607–617 (2022).
Schuckert, F., Katt, B. & Langweg, H. Insecurity Refactoring: Automated Injection of Vulnerabilities in Source Code. Comput. & Security. 128, 103121 (2023).
Fotis, F. Cyberattacks: economic impacts and risk management strategies. Procedia Comput. Sci. 251, 672–677 (2024).
McIntosh, T. et al., Harnessing GPT-4 for generation of cybersecurity GRC policies: A focus on ransomware attack mitigation. Comput. & Security. 134, 103424 (2023).
Burriss, S. K. et al. , Redesigning an AI bill of rights with/for young people: Principles for exploring AI ethics with middle and high school students. Comput. Educ.: Artificial Intell. 7, 100317 (2024).
Wu, W., Wang, S., Ding, G. & Mo, J. Elucidating trust-building sources in social shopping: A consumer cognitive and emotional trust perspective. J. Retailing Consumer Services. 71, 103217 (2023).
Gershfeld, I. & Sturm, A. Evaluating the effectiveness of a security flaws prevention tool, Inf. Software Technol. 170, 107427 (2024).
Zheng, W., Deng, P., Gui, K. & Wu, X. An Abstract Syntax Tree based static fuzzing mutation for vulnerability evolution analysis, Inf. Software Technol., 158, 107194 (2023).
Cai, Z. et al. Generative adversarial networks: A survey toward private and secure applications. ACM Comput. Surv, 54, 132, (2021).
Chen, P., Du, X., Lu, Z. & Chai, H. Universal adversarial backdoor attacks to fool vertical federated learning. Comput. & Security. 137,103601 (2024).
Guo, X. Towards Automated Software Testing with Generative Adversarial Networks, in 2021 51st Annual IEEE/IFIP International Conference on Dependable Systems and Networks - Supplemental Volume (DSN-S), 21–22. (2021).
Huang, L., Liu, H., Liu, Y., Shang, Y. & Li, Z. A Generative Adversarial Imitation Learning Method for Continuous Integration Testing, in 2024 5thInternational Seminar on Artificial Intelligence, Networking and Information Technology (AINIT), 1084–1089. (2024).
Jati, A. et al. Adversarial attack and defense strategies for deep speaker recognition systems. Comput. Speech & Language, 68, 101199 (2021).
Tan, H. et al. Adversarial Attack and Defense Strategies of Speaker Recognition Systems: A Survey. Electronics. 11, 2183, (2022).
Charles, V., Emrouznejad, A. & Gherman, T. A critical analysis of the integration of blockchain and artificial intelligence for supply chain. Annals Oper. Res. 327, 7–47 (2023).
Rahman, M. S., Khalil, I., Atiquzzaman, M. & Bouras, A. A lightweight practical consensus mechanism for supply chain blockchain. High-Confidence Computing, 5, 100253 (2025).
Aloupogianni, E. et al., AI-Driven Optimization of Small Cell Deployment for Beyond 5G Networks. Procedia Comput. Sci. 238, 908–913 (2024).
Patel, O. AI-Driven smart contracts. J. Artif. Intell. & Cloud Comput., 1–9, (2024).
Sarker, I. H., Furhad, M. H. & Nowrozy, R. Cybersecurity: an Overview, security intelligence modeling and research directions. SN Comput. Sci. 2, 18 (2021).
Zacharis, A., Katos, V. & Patsakis, C. Integrating AI-driven threat intelligence and forecasting in the cyber security exercise content generation lifecycle. Int. J. Inform. Security, 23, 2691–2710, (2024).
Azeem Akbar, M., Mahmood, S., Alsanad, A. & Com, A. Toward successful devsecops in software development organizations: A Decision-Making framework. Inf. Softw. Technol. 147, 0227 (2022).
Kannan, G., Pokharel, S. & Sasi Kumar, P. A hybrid approach using ISM and fuzzy TOPSIS for the selection of reverse logistics provider. Resources, Conservation Recycling, 54, 28–36 (2009).
Agarwal, A. & Vrat, P. Modeling attributes of human body organization using ISM and AHP. Jindal J. Bus. Res. 6, 44–62 (2017).
Soni, M. End to End Automation on Cloud with Build Pipeline: The Case for DevOps in Insurance Industry, Continuous Integration, Continuous Testing, and Continuous Delivery, (2015).
Attri, R., Grover, S., Dev, N. & Kumar, D. Analysis of barriers of total productive maintenance (TPM). Int. J. Syst. Assur. Eng. Manag. 4, 365–377 (2013).
Warfield, J. N. Developing interconnection matrices in structural modeling. IEEE Trans. Syst. Man. Cybernetics. SMC-4, 81–87 (1974).
Raluca Brasoveanu, Yusuf Karabulut, and Ivan Pashchenko. 2022. Security Maturity Self-Assessment Framework for SoftwareDevelopment Lifecycle. In The 17th International Conference on Availability, Reliability and Security, August 23–26,2022, Vienna, Austria. ACM, New York, NY, USA 8 Pages (ARES 2022).
Gary & McGraw Sammy. Migues, and J. West, Building Security In Maturity Model (BSIMM) Version 6, 1–65, (2015).
Team, S. U. Standard CMMI Appraisal Method for Process Improvement (SCAMPI) A, Version 1.3: Method Definition Document, Handbook CMU/SEI-2011-HB-001March (2011).
Aldin, N. A. N., Abdellatif, W. S. E., Elbarbary, Z. M. S., Omar, A. I. & Mahmoud, M. M. Robust speed controller for PMSG wind system based on Harris Hawks optimization via wind speed estimation: A real case study. IEEE Access. 11, 5929–5943 (2023).
Khan, R. A. et al. An evaluation framework for communication and coordination processes in offshore software development outsourcing relationship: using fuzzy methods. IEEE Access. 7, 112879–112906 (2019).
Khan, T. A. et al. Secure IoMT for disease prediction empowered with transfer learning in healthcare 5.0, the concept and case study. IEEE Access. 11, 39418–39430 (2023).
Elghanam, E., Ndiaye, M., Hassan, M. S. & Osman, A. H. Location selection for wireless electric vehicle charging lanes using an integrated TOPSIS and binary goal programming method: A UAE case study. IEEE Access. 11, 94521–94535 (2023).
Krishnamoorthy, P. et al. Effective scheduling of Multi-Load automated guided vehicle in spinning mill: A case study. IEEE Access. 11, 9389–9402 (2023).
Khan, R. A., Khan, S. U., Alzahrani, M. & Ilyas, M. Security assurance model of software development for global software development vendors. IEEE Access. 10, 58458–58487 (2022).
Acknowledgements
This work was funded by Princess Nourah bint Abdulrahman University Researchers Supporting Project number (PNURSP2026R896), Princess Nourah bint Abdulrahman University, Riyadh, Saudi Arabia.
Funding
This work was funded by Princess Nourah bint Abdulrahman University Researchers Supporting Project number (PNURSP2026R896), Princess Nourah bint Abdulrahman University, Riyadh, Saudi Arabia.
Author information
Authors and Affiliations
Contributions
All the authors equally contributed to this manuscript:1. Mujtaba Awan contributed to the conceptualization and methodology of the research, conducted the data analysis, and wrote the original draft of the manuscript. He also contributed to the manuscript review and revision.2. Abu Alam led the design of the research framework and was involved in data collection. Hathal also assisted with writing the discussion and managing the manuscript’s revision process.3. Rafiq Ahmad Khan contributed to data collection and validation, especially at the level of the technical implementation of the study. Hussein contributed to data analysis and manuscript revision.4. Hathal S. Alwageed contributed professionally by providing the software and tools for data analysis, helping support the statistical analysis, and contributing to the interpretation of the results. Ismail helped in the final editing and formatting of the manuscript.5. Sarra Ayouni participated in designing the methodology and drafting the review of the literature related to the subject. Sarra also critically revised the manuscript and ensured the clarity and quality of the final draft. She was also partially involved in fundraising for this study.6. Alaa Omran Almagrabi contributed to the study planning, offered professional guidance on the results interpretation, and wrote the manuscript. He is also involved in the critical review of the findings and the literature review.All authors have read and approved the final manuscript. The work was carried out with extraordinary contributions from all the authors, as explained above.
Corresponding authors
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary Information
Below is the link to the electronic supplementary material.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Awan, M., Alam, A., Khan, R.A. et al. A generative AI-driven cybersecurity framework for small and medium enterprises software development: an ANN-ISM approach. Sci Rep (2026). https://doi.org/10.1038/s41598-026-37614-8
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s41598-026-37614-8