Abstract
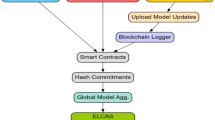
The Internet of Things (IoT) and emerging technologies have converged to drive the remarkable development of intelligent systems. The interconnection of physical objects, sensors, and tiny communication devices enables data aggregation, which is then forwarded to edge computing for local processing and analysis. Such a system improves response time and enhances network capabilities while managing the massive amount of collected data. On the other hand, existing approaches include cloud-based schemes that leverage edge-level offloading to control and manage demanding traffic. Furthermore, data security and network integrity are ensured by integrating blockchain technology with device identity authentication. However, in a dynamic environment, most approaches still incur interception and data eavesdropping, thereby affecting the reliability of connected communication channels. Therefore, developing trustworthiness and an authenticated system is a significant research challenge for the growth of smart systems. In this research, we introduce a lightweight, trusted AI-driven model to enhance security in complex systems and to ensure a more robust data-forwarding path over the long term. First, optimized methods are introduced that use an adaptive technique to explore network conditions and generate efficient data-transfer decision policies. Secondly, distributed and collaborative interactions are enabled across devices with minimal computing resources, thereby improving the system’s response time through load balancing. Ultimately, trust is continuously updated by leveraging real-time parameters and records of neighbours’ communication, thereby providing fault tolerance and trusted channels. The proposed model is verified and validated for efficacy through a wide range of simulations, and performance results demonstrate its superiority over existing approaches on realistic scenarios and metrics.
Similar content being viewed by others
Data availability
All data generated or analysed during this study are included in this published article.
References
Vermesan, O., Friess, P., Guillemin, P., Sundmaeker, H., Eisenhauer, M., Moessner, K., Le Gall, F., & Cousin, P. Internet of things strategic research and innovation agenda. In Internet of Things 7–151 (River Publishers, 2022).
Nag, A. et al. Exploring the applications and security threats of internet of thing in the cloud computing paradigm: A comprehensive study on the cloud of things. Trans. Emerg Telecommun Technol 35(4), e4897 (2024).
Badshah, A. et al. Smart cities’ big data: Performance and cost optimization with regional computing. IEEE Access (2024).
Silva, F. A., Fé, I., Silva, F. & Nguyen, T. A. Quantifying the impact of resource redundancy on smart city system dependability: A model-driven approach. Cluster Comput. 27(5), 6059–6079 (2024).
Garg, T., Gupta, S., Obaidat, M. S. & Raj, M. Drones as a service (DaaS) for 5g networks and blockchain-assisted IoT-based smart city infrastructure. Cluster Comput. 27(7), 8725–8788 (2024).
Zaman, M., Puryear, N., Abdelwahed, S. & Zohrabi, N. A review of IoT-based smart city development and management. Smart Cities 7(3), 1462–1501 (2024).
Gao, X., He, P., Zhou, Y. & Qin, X. Artificial intelligence applications in smart healthcare: A survey. Future Internet 16(9), 308 (2024).
Lu, Z., Afridi, I., Kang, H. J., Ruchkin, I. & Zheng, X. Surveying neuro-symbolic approaches for reliable artificial intelligence of things. J. Reliab. Intell. Environ. 10(3), 257–279 (2024).
Rachakonda, L. P., Siddula, M. & Sathya, V. A comprehensive study on IoT privacy and security challenges with focus on spectrum sharing in next-generation networks (5g/6g/beyond). High-Confid. Comput. 4(2), 100220 (2024).
Shayea, I. et al. Integration of 5G, 6G and IoT with low earth orbit (LEO) networks: Opportunity, challenges and future trends. Results Eng. 23, 102409 (2024).
Luo, Y. et al. Securing 5G/6G IoT using transformer and personalized federated learning: An access-side distributed malicious traffic detection framework. IEEE Open J. Commun. Soc. 5, 1325–1339 (2024).
Nguyen, T., Nguyen, H. & Gia, T. N. Exploring the integration of edge computing and blockchain IoT: Principles, architectures, security, and applications. J. Netw. Comput. Appl. 226, 103884 (2024).
Sharma, M., Tomar, A. & Hazra, A. Edge computing for industry 5.0: Fundamental, applications, and research challenges. IEEE Internet Things J. 11(11), 19070–19093 (2024).
Vu, T.-H., Jagatheesaperumal, S.K., Nguyen, M.-D., Van Huynh, N., Kim, S., & Pham, Q.-V. Applications of generative AI (GAI) for mobile and wireless networking: A survey. IEEE Internet Things J. (2024).
Shafique, T. et al. A review of energy hole mitigating techniques in multi-hop many to one communication and its significance in IoT oriented Smart City infrastructure. IEEE Access 11, 121340–121367 (2023).
He, S. et al. Collaborative sensing in Internet of Things: A comprehensive survey. IEEE Commun. Surv. Tutor. 24(3), 1435–1474 (2022).
Babu, E. S., Rao, M. S., Swain, G., Nikhath, A. K. & Kaluri, R. Fog-Sec: Secure end-to-end communication in fog-enabled IoT network using permissioned blockchain system. Int. J. Netw. Manag. 33(5), e2248 (2023).
Ahmed, A., Abdullah, S., Bukhsh, M., Ahmad, I. & Mushtaq, Z. An energy-efficient data aggregation mechanism for IoT secured by blockchain. IEEE Access 10, 11404–11419 (2022).
Qaddos, A. et al. A novel intrusion detection framework for optimizing IoT security. Sci. Rep. 14(1), 21789 (2024).
Naik, A. C. et al. Enhancing IoT security: A comprehensive exploration of privacy, security measures, and advanced routing solutions. Comput. Netw. 258, 111045 (2025).
Mishra, R., & Mishra, A. Current research on internet of things (IoT) security protocols: A survey. Comput. Secur. 104310 (2025).
Bekri, W., Jmal, R. & Fourati, L. C. Secure and trustworthiness IoT systems: Investigations and literature review. Telecommun. Syst. 85(3), 503–538 (2024).
Pathak, V. et al. A secure and lightweight trust evaluation model for enhancing decision-making in resource-constrained industrial WSNs. Sci. Rep. 14(1), 28162 (2024).
Aboubakar, M., Kellil, M. & Roux, P. A review of IoT network management: Current status and perspectives. J. King Saud Univ.-Comput. Inf. Sci. 34(7), 4163–4176 (2022).
Chamola, V., Peelam, M. S., Guizani, M., & Niyato, D. Future of connectivity: A comprehensive review of innovations and challenges in 7G smart networks. IEEE Open J. Commun. Soc. (2025).
Sefati, S. S. et al. A comprehensive survey on resource management in 6G network based on internet of things. IEEE Access (2024).
Dong, S. et al. Task offloading strategies for mobile edge computing: A survey. Comput. Netw. 254, 110791 (2024).
Asghari, A. & Sohrabi, M. K. Server placement in mobile cloud computing: A comprehensive survey for edge computing, fog computing and cloudlet. Comput. Sci. Rev. 51, 100616 (2024).
Chen, Z., Gan, W., Wu, J., Lin, H. & Chen, C.-M. Metaverse for smart cities: A survey. Internet Things Cyber-Phys. Syst. 4, 203–216 (2024).
Kong, L. et al. Edge-computing-driven internet of things: A survey. ACM Comput. Surv. 55(8), 1–41 (2022).
Alhowaide, A., Alsmadi, I. & Tang, J. Towards the design of real-time autonomous IoT NIDS. Cluster Comput. 26(5), 2489–2502 (2023).
Vankdothu, R. & Hameed, M. A. An effective congestion and interference secure routing protocol for Internet of Things applications in wireless sensor network. Wirel. Pers. Commun. 140(1), 143–161 (2025).
Patil, M., Chawhan, M., Umate, R., Madankar, A. & Neole, B. Energy efficient adaptive clustering with QoS-aware CBRP and grey wolf optimization clustering algorithm for mobile ad-hoc network (MANET). Discov. Comput. 28(1), 1–44 (2025).
Kumar, A. & Singh, D. Securing IoT devices in edge computing through reinforcement learning. Comput. Secur. 155, 104474 (2025).
Kumar, N. & Beniwal, R. A multi-constrained green routing protocol for IoT-based software-defined WSN. Concurr. Comput. Pract. Exp. 36(28), e8306 (2024).
Ilakkiya, N. & Rajaram, A. A secured trusted routing using the structure of a novel directed acyclic graph-blockchain in mobile ad hoc net- work internet of things environment. Multimed. Tools Appl. 83(40), 87903–87928 (2024).
Fei, H. et al. A novel energy efficient QoS secure routing algorithm for WSNs. Sci. Rep. 14(1), 25969 (2024).
Tang, J., Liu, G. & Pan, Q. A review on representative swarm intelligence algorithms for solving optimization problems: Applications and trends. IEEE/CAA J. Autom. Sin. 8(10), 1627–1643 (2021).
Acknowledgements
This work was funded by the Deanship of Graduate Studies and Scientific Research at Jouf University under grant No. (DGSSR-2025-NF-02-068).
Funding
This work was funded by the Deanship of Graduate Studies and Scientific Research at Jouf University under grant No. (DGSSR-2025-NF-02-068).
Author information
Authors and Affiliations
Contributions
Conceptualization, Mekhled Alharbi, Mamoona Humayun; Formal analysis, Khalid Haseeb and Mekhled Alharbi; Methodology, Atif Khan, NZ Jhanjhi and Khalid Haseeb; Supervision, Mamoona Humayun and Mekhled Alharbi; Validation, Muhammad Attique Khan and NZ Jhanjhi; Writing original draft, Atif Khan and Khalid Haseeb; Writing review & editing, Muhammad Attique Khan and Mekhled Alharbi.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Consent for publication
The authors provide consent for publication in this journal.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Alharbi, M., Haseeb, K., Jhanjhi, N.Z. et al. Blockchain-driven trust management and AI computing for sensor networks optimization. Sci Rep (2026). https://doi.org/10.1038/s41598-026-41302-y
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s41598-026-41302-y