Abstract
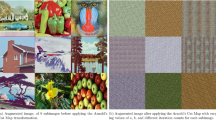
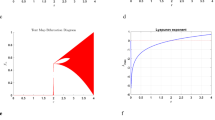
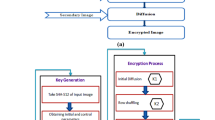
The rapid growth of Internet of Things (IoT) devices has increased the demand for encryption techniques that simultaneously ensure high security strength with low computational complexity and real-time feasibility under resource constraints. The proposed SCD–CHAOS, a novel hybrid chaotic image encryption technique that combines dual chaotic dynamics based on the Tent and Henon maps with an entropy-driven adaptive dynamic S-Box mechanism. Unlike traditional chaos-based permutation–diffusion architectures which rely on static substitution structures, the proposed technique introduces entropy-guided nonlinear transformation combined with hybrid chaotic key synthesis to significantly improve confusion capability, diffusion uniformity, and key sensitivity while preserving deterministic reversibility. For the purpose of standardized benchmarking and computational efficiency in IoT environments, the input images are uniformly down-scaled to \(64\times 64\) prior to encryption. Various experimental evaluations of the benchmark images demonstrate a near-ideal entropy in average of 7.9991 bits, Number of Pixels Change Rate average 99.6226%, unified average change intensity reaching average of 33.4732%, and correlation coefficients of encrypted images approaching zero in all directions, confirming strong resistance against statistical and differential attacks. Key sensitivity analysis achieves NPCR/ UACI values of up to 99.6221% and 33.4717%, respectively. The Lyapunov exponent analysis reports robust chaotic behavior with values of up to 1.4628. The detection performance shows a structural similarity index in average of 0.9994 for original vs Decrypted images, peak signal-to-noise ratio mean of 9.6250dB, and mean Square Error mean of around 6904.83. The encryption and decryption processes require only 0.00619 seconds and 0.00261 seconds for \(64\times 64\) images, demonstrating real-time feasibility, making SCD-CHAOS a robust and scalable encryption technique for secure image transmission in next-generation IoT networks.
Similar content being viewed by others
Data availability
Some or all data, model, or codes that support the findings of this study are available from the corresponding author upon reasonable request.
References
Jha, B., Singh, P. K. & Verma, V. R. A novel image encryption algorithm using tent and lorenz chaotic system. Soft Comput. 1–22 (2026).
Yogi, B. & Kumar Khan, A. Tcaskd: A lightweight hybrid cryptosystem using tent map and cellular automata for secure shared-key derivation. 9, 70198. Wiley Online Library, (2026).
Shi, R.-H., Yang, Y.-G., Xu, G.-B., Jiang, D.-H. & Jiang, D.-H. Dynamic rgb zimage encryption algorithm with pixel-value-driven partitioning and a newly designed three-dimensional chaotic map. Multimedia Syst. 32(2), 85 (2026).
Liang, Y., Peng, B., Liu, R., Kang, N. & Zhou, H. An image compression-encryption algorithm based on bp neural network optimized with fireworks algorithm. Sci. Rep. (2026)
Yogi, B., Majumdar, R. & Ghosh, P. Hypzac: Advanced image encryption via hybrid h-pattern zigzag and arnold cat map chaotic dynamics. SN Comput. Sci. 7(2), 212 (2026).
Kanwal, S. et al. A new image encryption technique based on sine map, chaotic tent map, and circulant matrices. Secur. Commun. Netw. 2022(1), 4152683 (2022).
Chen, Y., Xie, S. & Zhang, J. A hybrid domain image encryption algorithm based on improved henon map. Entropy 24(2), 287 (2022).
Zheng, J. & Zeng, Q. An image encryption algorithm using a dynamic s-box and chaotic maps. Appl. Intell. 52(13), 15703–15717 (2022).
Akraam, M., Rashid, T. & Zafar, S. An image encryption scheme proposed by modifying chaotic tent map using fuzzy numbers. Multimedia Tools Appl. 82(11), 16861–16879 (2023).
Rezaei, B., Ghanbari, H. & Enayatifar, R. An image encryption approach using tuned henon chaotic map and evolutionary algorithm. Nonlinear Dyn. 111(10), 9629–9647 (2023).
Liu, H., Liu, J. & Ma, C. Constructing dynamic strong s-box using 3d chaotic map and application to image encryption. Multimedia Tools Appl. 82(16), 23899–23914 (2023).
Kulkarni, A. G., Prajwalasimha, S., Kulkarni, N., Karuppusamy, D., Dharmappa, R. & Bagga, Y. Bl-iea: A bit-level image encryption algorithm using transformation and chaotic skew tent map based substitution for fingerprint images. In 2024 Third International Conference on Electrical, Electronics, Information and Communication Technologies (ICEEICT), 1–7 (2024). IEEE
Mohammad, S. N. H. & Mandangan, A. Colour image encryption and decryption using arnold’s cat map and henon map. Int. J. Adv. Res. Comput. Think. Data Sci. 1(1), 41–52 (2024).
Youssef, M. et al. Enhancing satellite image security through multiple image encryption via hyperchaos, svd, rc5, and dynamic s-box generation. IEEE Access 12, 123921–123945 (2024).
Shahid, U. et al. Blockchain driven medical image encryption employing chaotic tent map in cloud computing. Sci. Rep. 15(1), 6236 (2025).
Mohi Ud Din S., Shah, T., Alblehai, F., Nooh, S. & Jamal, S. S. A combinatory approach of non-chain ring and henon map for image encryption application. Sci. Rep. 15(1), 1781 (2025).
Ali, J., Jamil, M. K. & Ali, R. Gulraiz: Extended fractional transformation based s-box and applications in medical image encryption. Multimedia Tools Appl. 1–17 (2025)
Malik, A. W., Zahid, A. H., Bhatti, D. S., Kim, H. J. & Kim, K.-I. Designing s-box using tent-sine chaotic system while combining the traits of tent and sine map. IEEE Access 11, 79265–79274 (2023).
Ali, R., Jamil, M. K., Alali, A. S., Ali, J. & Afzal, G. A robust s box design using cyclic groups and image encryption. Ieee Access 11, 135880–135890 (2023).
Vijayakumar, M. & Ahilan, A. An optimized chaotic s-box for real-time image encryption scheme based on 4-dimensional memristive hyperchaotic map. Ain Shams Eng. J. 15(4), 102620 (2024).
Hazzazi, M. M., Baowidan, S. A., Yousaf, A. & Adeel, M. An innovative algorithm based on chaotic maps amalgamated with bit-level permutations for robust s-box construction and its application in medical image privacy. Symmetry 16(8), 1070 (2024).
Alali, A. S., Ali, R., Jamil, M. K. & Ali, J. Gulraiz: Secure medical image encryption with hyperelliptic curve based s-boxes. Sci. Rep. 15(1), 18179 (2025).
Sarmila, K. & Manisekaran, S. Iot enabled data protection with substitution box for lightweight ciphers. Egypt. Inf. J. 29, 100620 (2025).
Hanis, S. & Jegadish Kumar, K. Implementation and testing of an image encryption algorithm using a novel chaotic map. IETE J. Res. 1–17 (2026).
Manikandan, S., Linkkesh, A., Sreenivasan, S., Thanikaiselvan, V., Subashanthini, S. & Amirtharajan, R. Autoencoder-based image encryption using hybrid scrambling, diffusion, and dimensionality reduction. Res. Eng. 108977 (2026).
Khashei, M., Ahmadi, M. & Chahkoutahi, F. A mean weighted squared error-based neural classifier for intelligent pattern recognition in smart grids. Int. J. Electr. Power Energy Syst. 170, 110972 (2025).
Li, Y., Zhang, Y., Jia, D., Gao, S. & Zhang, M. Noise impact analysis in computer-generated holography based on dual metrics evaluation via peak signal-to-noise ratio and structural similarity index measure. Appl. Sci. 15(11), 6047 (2025).
Tiwari, A., Diwan, P., Diwan, T. D., Miroslav, M. & Samal, S. A compressed image encryption algorithm leveraging optimized 3d chaotic maps for secure image communication. Sci. Rep. 15(1), 14151 (2025).
Tiwari, A., Diwan, P., Diwan, T. D., Miroslav, M. & Samal, S. A compressed image encryption algorithm leveraging optimized 3d chaotic maps for secure image communication. Sci. Rep. 15(1), 14151 (2025).
Palmér, M., Åkesson, Å., Ljungberg, M., Kuzcera, S., Gryska, E., Coursey, E., Heckemann, R.A., Dahm Kähler, P., Maier, S. E. & Leonhardt, H. Preoperative risk assessment of endometrial cancer using histogram analysis of weighted and quantitative mri images. Abdom. Radiol. 1–11 (2025).
Majumdar, R., Modak, S., Dey, S., Bhattacharjee, S. K., Bachhar, S. & Yogi, B. An efficient image cipher based on lorenz system and cellular automata rule 105. In 2025 International Conference on Artificial Intelligence and Emerging Technologies (ICAIET), 1–6 (2025). IEEE
Yogi, B., Khan, A. K. & Roy, S. Cellular automata based key distribution for lightweight hybrid image encryption with elliptic curve cryptography. Sci. Rep. 15(1), 34437 (2025).
Xie, P. et al. Sub-region based histogram analysis of amide proton transfer-weighted mri for predicting tumor budding grade in rectal adenocarcinoma: a prospective study. Eur. Radiol. 35(3), 1382–1393 (2025).
Nithya, C. et al. Secure gray image sharing framework with adaptive key generation using image digest. Sci. Rep. 15(1), 8854 (2025).
Majumdar, R., Ghosh, P., Modak, S., Biswas, A., Khatun, F. & Yogi, B. Chaos-driven image encryption using zigzag patterns and chebyshev dynamics. In 2025 International Conference on Artificial Intelligence and Emerging Technologies (ICAIET), 1–6 (2025). IEEE
Majumdar, R., Modak, S., Biswas, A., Ghosh, P. & Yogi, B. Icar30: Image encryption combining ikeda map and cellular automata rule 30. In International Symposium on Artificial Intelligence, 413–426 (2025). Springer.
Yogi, B. & Khan, A. K. Efficient shared secret key distribution using cellular automata for hybrid cryptosystems. Franklin Open 100465 (2025).
Cao, X. et al. Boundary aware microscopic hyperspectral pathology image segmentation network guided by information entropy weight. Front. Oncol. 15, 1549544 (2025).
Majumdar, R., Mallick, T., Mahajan, S., Paral, I., Roy, S. & Yogi, B. A hybrid approach to image encryption using rule 150 cellular automata and lozi map. In 2025 International Conference on Artificial Intelligence and Emerging Technologies (ICAIET), 1–6 (2025). IEEE
Peng, J. & Chen, C. Rpcc: Rectified pearson correlation coefficient for radiance fields optimization. IEEE Signal Process. Lett. (2025).
Lee, J. C., Park, H. W. & Kang, Y. N. Feasibility study of structural similarity index for patient-specific quality assurance. J. Appl. Clin. Med. Phys. 26(3), 14591 (2025).
Hosseini-Siyanaki, M. et al. Multi-energy evaluation of image quality in spectral ct pulmonary angiography using different strength deep learning spectral reconstructions. Acad. Radiol. 32(5), 2953–2965 (2025).
Milovic, C., Tejos, C., Silva, J., Shmueli, K. & Irarrazaval, P. Xsim: A structural similarity index measure optimized for mri qsm. Magn. Reson. Med. 93(1), 411–421 (2025).
Alexan, W., Hosny, K. & Gabr, M. A new fast multiple color image encryption algorithm. Clust. Comput. 28(5), 1–34 (2025).
Alshehri, H. Secure image encryption using a 4d chaotic system and langton’s ant cellular automaton. Sci. Rep. 15(1), 41918 (2025).
Alexan, W., Shabasy, N. H. E., Ehab, N. & Maher, E. A. A secure and efficient image encryption scheme based on chaotic systems and nonlinear transformations. Sci. Rep. 15(1), 31246 (2025).
Al-Dayel, I., Nadeem, M. F., Khan, M. A. & Abraha, B. S. An image encryption scheme using 4-d chaotic system and cellular automaton. Sci. Rep. 15(1), 19499 (2025).
Qayyum, T., Shah, T., Khan, I. & Popa, I.-L. A design of multiple color image encryption scheme based on finite algebraic structures. Sci. Rep. 15(1), 42571 (2025).
Alexan, W. et al. A new multiple image encryption algorithm using hyperchaotic systems, svd, and modified rc5. Sci. Rep. 15(1), 9775 (2025).
Liu, Z., Wang, Y., Liu, J., Feng, J. & Zhang, L. Y. A newly image encryption scheme based on 3-d coupled map lattice and baker map. Cybersecurity 9(1), 103 (2026).
Funding
Open access funding provided by Manipal University Jaipur. No funding was received for conducting this study.
Author information
Authors and Affiliations
Contributions
All the authors have equal contribution.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Yogi, B., Majumdar, R., Ghosh, P. et al. SCD-CHAOS: dynamic S-box and chaotic hybrid adaptive image encryption using multi-map diffusion. Sci Rep (2026). https://doi.org/10.1038/s41598-026-43981-z
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s41598-026-43981-z