Abstract
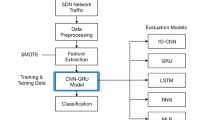
Software-defined networking (SDN) centralizes control, simplifying network management and configuration while simultaneously increasing vulnerability to attacks, such as large-scale Distributed Denial-of-Service (DDoS) attacks or network topology spoofing. Conventional intrusion detection methods that rely on feature engineering or static graph modeling often fail to capture the complex topological dependencies and dynamic temporal patterns inherent in network traffic. To address this issue, a dynamic multi-scale spatio-temporal graph neural network framework, named DMSTG-AD, is proposed for intrusion detection. The model employs Gated Recurrent Unit (GRU)-driven dynamic node embeddings, an adaptive adjacency matrix, and edge–node collaborative convolution to extract spatial dependencies, while multi-scale dilated convolutions and a bidirectional GRU jointly capture short-term fluctuations and long-term trends. A spatio-temporal cross-attention mechanism is designed to integrate spatial and temporal features, thereby enhancing anomaly detection capabilities. Experimental results demonstrate that the proposed DMSTG-AD model achieves a multi-classification accuracy of 99.34% on the CIC-IDS2017 dataset and an overall accuracy of 99.88% on the InSDN dataset, both of which significantly exceed those of existing mainstream methods. Ablation experiments further validate the critical importance of dynamic modeling, dual-channel feature extraction, and the cross-attention mechanism in improving detection performance. This study not only offers a novel approach for high-precision intrusion detection in SDN environments but also broadens the application prospects of dynamic graph neural networks in the field of network security.
Similar content being viewed by others
Data availability
The data supporting this study are available when reasonably requested from the corresponding author.
References
Tang, Y., Wang, W.-Z., Wang, W.-Y. & Xu, B.-W. Design and implementation of the interconnected architecture of SDN and traditional IP network. Computer Eng. Sci. 39, 2210 (2017).
Kreutz, D. et al. Software-defined networking: A comprehensive survey. Proc. IEEE 103, 14–76 (2014).
Yoon, C. et al. Flow wars: Systemizing the attack surface and defenses in software-defined networks. IEEE/ACM Trans. Networking 25, 3514–3530 (2017).
Taheri, R., Ahmed, H. & Arslan, E. Deep learning for the security of software-defined networks: A review. Cluster Comput. 26, 3089–3112 (2023).
Chica, J. C. C., Imbachi, J. C. & Vega, J. F. B. Security in SDN: A comprehensive survey. J. Netw. Comput. Appl. 159, 102595 (2020).
Balakrishnan, S., Ivy, B. P. U. & Ilango, S. S. A novel and secured intrusion detection system for wireless sensor networks using identity based online/offline signature. ARPN J. Eng. Appl. Sci. 13, 8544–8547 (2018).
Saathvika, S., Accamma, B. & Santhosh Kumar, B. in 2024 Control Instrumentation System Conference (CISCON). 1–7 (IEEE).
Mishra, P., Varadharajan, V., Tupakula, U. & Pilli, E. S. A detailed investigation and analysis of using machine learning techniques for intrusion detection. IEEE Commun. Surv. Tut. 21, 686–728 (2018).
Gu, J. & Lu, S. An effective intrusion detection approach using SVM with naïve Bayes feature embedding. Comput. Secur. 103, 102158 (2021).
Ahuja, N., Singal, G., Mukhopadhyay, D. & Kumar, N. Automated DDOS attack detection in software defined networking. J. Netw. Comput. Appl. 187, 103108 (2021).
Wu, K., Chen, Z. & Li, W. A novel intrusion detection model for a massive network using convolutional neural networks. IEEE Access 6, 50850–50859 (2018).
Malik, J. et al. Hybrid deep learning: An efficient reconnaissance and surveillance detection mechanism in SDN. IEEE Access 8, 134695–134706 (2020).
Bilot, T., El Madhoun, N., Al Agha, K. & Zouaoui, A. Graph neural networks for intrusion detection: A survey. IEEE Access 11, 49114–49139 (2023).
Caville, E., Lo, W. W., Layeghy, S. & Portmann, M. Anomal-E: A self-supervised network intrusion detection system based on graph neural networks. Knowl. Based Syst. 258, 110030 (2022).
Altaf, T., Wang, X., Ni, W., Liu, R. P. & Braun, R. NE-GConv: A lightweight node edge graph convolutional network for intrusion detection. Comput. Secur. 130, 103285 (2023).
Liu, H. & Lang, B. Machine learning and deep learning methods for intrusion detection systems: A survey. Appl. Sci. (Basel) 9, 4396 (2019).
ElSayed, M. S., Le-Khac, N.-A., Albahar, M. A. & Jurcut, A. A novel hybrid model for intrusion detection systems in SDNs based on CNN and a new regularization technique. J. Netw. Comput. Appl. 191, 103160 (2021).
Ravi, V., Chaganti, R. & Alazab, M. Recurrent deep learning-based feature fusion ensemble meta-classifier approach for intelligent network intrusion detection system. Comput. Electr. Eng. 102, 108156 (2022).
Assis, M. V., Carvalho, L. F., Lloret, J. & Proença, M. L. Jr. A GRU deep learning system against attacks in software defined networks. J. Netw. Comput. Appl. 177, 102942 (2021).
Elsayed, R. A., Hamada, R. A., Abdalla, M. I. & Elsaid, S. A. Securing IoT and SDN systems using deep-learning based automatic intrusion detection. Ain Shams Eng. J. 14, 102211 (2023).
Nguyen, T. G., Phan, T. V., Hoang, D. T., Nguyen, T. N. & So-In, C. Federated deep reinforcement learning for traffic monitoring in SDN-based IoT networks. IEEE Trans Cognit Commun Netw 7, 1048–1065 (2021).
Wang, H. & Li, W. DDosTC: A transformer-based network attack detection hybrid mechanism in SDN. Sensors 21, 5047 (2021).
Behera, A., Sahoo, K. S., Mishra, T. K. & Bhuyan, M. A combination learning framework to uncover cyber attacks in IoT networks. Internet of Things 28, 101395 (2024).
Guo, Y. et al. Traffic management in IoT backbone networks using GNN and MAB with SDN orchestration. Sensors 23, 7091 (2023).
Zhou, X. et al. Hierarchical adversarial attacks against graph-neural-network-based IoT network intrusion detection system. IEEE Internet Things J. 9, 9310–9319 (2021).
Lo, W. W., Layeghy, S., Sarhan, M., Gallagher, M. & Portmann, M. E-graphsage: A graph neural network based intrusion detection system for iot. arXiv preprint arXiv:2103.16329 (2021).
Lan, J. et al. E-minBatch GraphSAGE: An Industrial Internet Attack Detection Model. Security and Communication Networks 2022, 5363764 (2022).
Deng, P. & Huang, Y. Edge-featured multi-hop attention graph neural network for intrusion detection system. Comput. Secur. 148, 104132 (2025).
Wang, Y. et al. N-STGAT: Spatio-temporal graph neural network based network intrusion detection for near-earth remote sensing. Remote Sensing 15, 3611 (2023).
Duan, G., Lv, H., Wang, H., Feng, G. & Li, X. Practical cyber attack detection with continuous temporal graph in dynamic network system. IEEE Trans. Inf. Forensics Secur. 19, 4851–4864 (2024).
Duan, G., Lv, H., Wang, H. & Feng, G. Application of a dynamic line graph neural network for intrusion detection with semisupervised learning. IEEE Trans. Inf. Forensics Secur. 18, 699–714 (2022).
Xu, D., Ruan, C., Korpeoglu, E., Kumar, S. & Achan, K. Inductive representation learning on temporal graphs. arXiv preprint arXiv:2002.07962 (2020).
Benzekki, K., El Fergougui, A. & Elbelrhiti Elalaoui, A. Software‐defined networking (SDN): A survey. Secur. Commun. Netw. 9, 5803–5833 (2016).
Chen, Q. et al. An adaptive adjacency matrix-based graph convolutional recurrent network for air quality prediction. Sci. Rep. 14, 4408 (2024).
Dey, R. & Salem, F. M. in 2017 IEEE 60th international midwest symposium on circuits and systems (MWSCAS). 1597–1600 (IEEE).
Lea, C., Flynn, M. D., Vidal, R., Reiter, A. & Hager, G. D. in proceedings of the IEEE Conference on Computer Vision and Pattern Recognition. 156–165.
Sharafaldin, I., Lashkari, A. H. & Ghorbani, A. A. Toward generating a new intrusion detection dataset and intrusion traffic characterization. ICISSp 1, 108–116 (2018).
Elsayed, M. S., Le-Khac, N.-A. & Jurcut, A. D. InSDN: A novel SDN intrusion dataset. IEEE Access 8, 165263–165284 (2020).
Kipf, T. Semi-supervised classification with graph convolutional networks. arXiv preprint arXiv:1609.02907 (2016).
Veličković, P. et al. Graph attention networks. arXiv preprint arXiv:1710.10903 (2017).
Said, R. B., Sabir, Z. & Askerzade, I. CNN-BiLSTM: A hybrid deep learning approach for network intrusion detection system in software-defined networking with hybrid feature selection. IEEE Access 11, 138732–138747 (2023).
Ma, Z., Liu, Y., Chen, Y., Liu, Z. & Li, Y. XMF-GNN: A cross-modality dynamic fusion heterogeneous graph neural network for network intrusion detection. Neurocomputing https://doi.org/10.1016/j.neucom.2025.131285 (2025).
Le, H.-D. & Park, M. Enhancing multi-class attack detection in graph neural network through feature rearrangement. Electronics 13, 2404 (2024).
Shoukat, S., Gao, T., Javeed, D., Saeed, M. S. & Adil, M. Trust my IDS: An explainable AI integrated deep learning-based transparent threat detection system for industrial networks. Comput. Secur. 149, 104191 (2025).
Zhang, Y., Jue, C., Liu, W. & Ma, Y. GRAN: A SDN intrusion detection model based on graph attention network and residual learning. Comput. J. 68, 241–260 (2025).
Funding
This work is sponsored by the National Natural Science Foundation of China (NO.52578067).
Author information
Authors and Affiliations
Contributions
J.Z.: Conceptualization, Methodology, Software, Validation, Formal analysis, Writing-original draft preparation. D.Z.: Validation, Resources. Q.H.: Writing—review and editing, Formal analysis. M.L.: Writing—review and editing. Y. Y.: Writing—review and editing.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Zhao, J., Zhang, D., He, Q. et al. DMSTG-AD: an SDN intrusion detection method based on dynamic multi-scale spatio-temporal graph neural network. Sci Rep (2026). https://doi.org/10.1038/s41598-026-44360-4
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s41598-026-44360-4