Abstract
Cyclic quantum teleportation schemes requires at least the existence of three collaborators acting all as senders and receivers of quantum information, each one of them has an information to be transmitted to the next neighbour in a circular manner. Here, new cyclic quantum teleportation scheme is proposed for perfectly transmitting cyclically three arbitrary unknown two-qubit states (\(\alpha \), \(\beta \) and \(\gamma \)) among the three collaborators. In this scheme, Alice can send to Bob the quantum information contained in her two-qubit state \(\alpha \) and receive from Charlie the quantum information contained in the two-qubit state in his possession \(\gamma \) and similarly, Bob can transmit to Charlie the quantum information contained in his two-qubit state \(\beta \) through a quantum channel of twelve-qubit state consisting of a six-qubit cluster state and a six-qubit entangled state by sequentially and cyclically performing Bell state measurements. Subsequently, each one of the three participants can afterwards retrieve his own desired two-qubit state using classical channel and by performing appropriate unitary Pauli operators and we have shown that our proposed scheme performs efficiently.
Similar content being viewed by others
Introduction
In the field of secure transmission of confidential information, the quantum teleportation (QT) is considered as protocol that allows the transfer of unknown quantum information, not only indecipherable but also imperceptible between two remote entities without loss of value. This opens the door to secure communication protocols over long distances and thus offers a reliable solution for the future quantum internet1,2,3. The first scientific scheme that discusses QT as a protocol of secure transmission of quantum information contained in an unknown quantum state, was first developed by Bennet et al.4, where they found that quantum information from an unknown quantum state can be perfectly transmitted from a sender, say Alice, to a distant receiver, say Bob, via a maximally pre-shared entangled quantum channel, without physical transfer of the discussed system itself. In a more convincing way, after the measurement the unknown quantum state of the discussed physical system disappears from the transmitting entity to appear in the more distant receiving entity at the same time, without loss of information, and without taking into account the distance between the two entities using classical communication and quantum entanglement5,6,7,8. Without this recent discovery, which has become in our time the most important principle of quantum mechanics, today we would not be talking about something called QT of an unknown quantum state according to the principles of quantum mechanics at the time, which considered something like this forbidden and impossible i.e. Heisenberg’s principle of uncertainty. For this reason, QT is the incipient and direct result of this great discovery and is therefore the one who can better explain and provide an impressive explanation for the phenomenon of quantum entanglement and the huge success that we can achieve if we are lucky enough to have it maximally among quantum entities9,10,11,12,13,14.
Experimentally, several physical systems have been transmitted with encouraging results15,16,17,18,19,20,21,22. Since QT is essentially a transmission protocol, it was obvious that most of attention will be focused on its effectiveness according to the different systems studied and the possibility of continuing its success in the presence of new constraints, for example, case of long distance23 or also the quantum channel pre-shared between sender and receiver, such as Einstein–Podolsky–Rosen (EPR) state24, Greenberger–Horner–Zeilinger (GHZ) state25,26, GHZ-like state27,28,29, Werner (W) state30,31, W-like state32 and cluster state33,34,35,36. Building on prior research37, this work investigates faithful teleportation using an arbitrary shared quantum state (qubit) between Alice and Bob. The authors introduce a general criterion to determine if this channel can teleport any d-qubit state accurately, regardless of the specific channel state. This new method offers a significant advantage; it’s simpler to implement in experiments compared to existing protocols. A novel d-qudit teleportation protocol is presented in Ref.38. This scheme utilizes the tensor product state of n-generalized Bell states as the quantum channel, allowing for faithful state transmission. Additionally, the implementation of multi-qubit quantum teleportation and a deterministic secure communication protocol under the control of multiple agents are reported in39. Practically, parts responsible for QT can be extended to other parts with more tasks as needed as possible. The extension of QT to multipartite QT is known as controlled quantum teleportation (CQT)40, which is an integral part of quantum teleportation networks41 and could be the cornerstone of the future quantum internet. In 2013, an original novel protocol for bidirectional controlled quantum teleportation (BCQT) was firstly presented by Zha et al.42, where Alice and Bob decides together to teleport their quantum states to each other under the supervision of a controller, say Charlie using five-qubit cluster states. Interesting, Yuan and Zhang43 have suggested an asymmetric BQT scheme feasible with present experimental technologies by using a four-qubit cluster state and a Bell state as a quantum channel. In addition, Wanbin et al.44 have theoretically proposed three BQCT schemes, allowing bidirectional teleportation between two participants with another as the controller, by utilizing seven-qubit maximally entangled states. BCQT has been well received by researchers in the field of information transmission and has been applied using many different entangled pre-shared quantum channel, as for example GHZ states45, five-qubit entangled states46, five-qubit composite GHZ-Bell states47, six-qubit entangled states48, seven-qubit entangled states49, eight-qubit entangled state50 and multi-qubit entangled states51. In 2017, an other novel protocol for cyclic quantum teleportation (CYQT) was originally proposed by Chen et al.52, where three collaborators Alice, Bob and Charlie all decides to teleport their single-qubit quantum states among themselves using a six-qubit entangled state. Immediately after, Sang53 proposed a controlled CYQT protocol introducing a fourth co-operator playing the role of supervisor David, implying that Alice, Bob and Charlie could exactly share their quantum states if David gave his consent46,54,55,56,56. Recently, Verma57 suggested a new scheme for CYQT, where four co-operators Alice, Bob, Charlie and David can cyclically teleport their single-qubit state among themselves by using two G-states.
In our work, an efficient cyclic quantum teleportation of three arbitrary two-qubit states using a six-qubit cluster state and a six-qubit entangled state is proposed. In our scheme, Alice has an unknown two-qubit state containing two qubits \(\alpha _0\) and \(\alpha _1\), Bob has a second unknown two-qubit state containing qubits \(\beta _0\) and \(\beta _1\), and the third collaborator Charlie has also a third unknown two-qubit state containing two qubits \(\gamma _0\) and \(\gamma _1\). The goal of our CYQT scheme is to teleport the two-qubit state in Alice’s possession to his near neighbour Bob, and Bob must transmit his two-qubit state to his neighbour Charlie and also the third co-operator Charlie can teleport his unknown two-qubit state to Alice. To achieve this, the three parties must first share a quantum channel containing twelve-qubit distributed among the three collaborators, each of them has four qubits. Next, each collaborator must to perform Bell state measurements on his two qubits to be transmitted and his two out of these four qubits of the quantum channel. Finally, each one of them might to perform suitable Pauli unitary operators on his resulting state to obtain the original state and this after, of course, receiving measurement results by classical channel from the responsible sender.
The outline of this article is organized as follows: In “Three arbitrary two-qubit states to be transmitted and selected twelve-qubit entangled quantum channel”, we introduced the cyclic quantum teleportation scheme with a mention of the construction of the used pre-shared entangled twelve-qubit quantum channel, the three target states to be teleport for Alice to Bob, from Bob to Charlie and from Charlie to Alice respectively. “Cyclic quantum teleportation of three arbitrary two-qubit states among the three users” details the execution of cyclic quantum teleportation scheme of the three arbitrary two-qubit entangle entangled state. “Protocol success probability and efficiency” analysis the amout data of classical information, the success probability and the protocol performance by calculating the efficiency factor of the proposed CYQT scheme. Concluding remarks are given in “Concluding remarks”.
Three arbitrary two-qubit states to be transmitted and selected twelve-qubit entangled quantum channel
In this section, we aim to represent the quantum channel used, the unknown selected target states and the CYQT protocol steps. Suppose that there are three participants, employing twelve-qubit entangled states combining a six-qubit cluster state and a six-qubit entangled state as a quantum channel. Alice has an unknown two-qubit state \(|{\psi }\rangle _{\alpha }\) to teleport to Bob, Bob has a second unknown two-qubit state \(|{\psi }\rangle _{\beta }\) to teleport to Charlie, and similarly Charlie has a third unknown two-qubit state \(|{\psi }\rangle _{\gamma }\) to teleport to Alice through a quantum channel. The quantum channel linking the three participants Alice, Bob and Charlie take the form
the six-qubit cluster state \(|{C_{6}}\rangle \) used in the quantum channel above has the form
and the six-qubit entangled state \(|{\psi _{6}}\rangle \) can be described as follows
Construction of the quantum channel
Quantum circuit illustrating the construction of the twelve-qubit quantum channel combining a six-qubit cluster state and a six-qubit entangled state using H-gate and CNOT-gate.
The quantum channel in the simplest case is a twelve-qubit entangled state shared between the three participants Alice, Bob and Charlie, which can be realized by applying Hadamard (H) and Controlled-Not (CNOT) quantum gates (see the Fig. 1). Firstly, the product state of twelve-qubit state initialized to \(|{0}\rangle \) is used as the input state \(|{\phi _{0}}\rangle \) in the quantum circuit, which can be expressed as
then, performing H-gates on qubits (1, 4, 7, 10, 11, 12), the input state \(|{\phi _{0}}\rangle \) is converted to \(|{\phi _{1}}\rangle \) as follows
after that, several CNOT-gates need to be performed on the following qubit pairs (1;2), (1;3), (4;5), (4;6), (7;8) and (7;9), qubits 1, 4, 7 control qubits (2;3), (5;6) and (8;9) respectively. Afterwards, the quantum channel takes the form (1). Where Alice holds qubits (5,6,7,10), Bob holds qubits (1,8,9,11) and Charlie holds qubits (2,3,4,12). The twelve-qubit entangled state can be rewritten as
Description of the proposed CYQT scheme
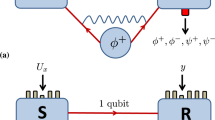
In this scheme, each one of three participants has an arbitrary unknown two-qubit state to teleport to the next neighbour. Alice has an unknown two-qubit state \(|{\psi }\rangle _{\alpha }= a_0 |{00}\rangle _{\alpha _0\alpha _1} + a_1 |{11}\rangle _{\alpha _0\alpha _1}\) to teleport to Bob, Bob has a second unknown two-qubit state \(|{\psi }\rangle _{\beta }= b_0 |{00}\rangle _{\beta _0\alpha _1} + b_1 |{11}\rangle _{\beta _0\beta _1}\) to teleport to Charlie, while Charlie has a third unknown two-qubit state \(|{\psi }\rangle _{\gamma }= c_0 |{00}\rangle _{\gamma _0\gamma _1} + c_1 |{11}\rangle _{\gamma _0\gamma _1}\) to teleport to Alice through the quantum channel discussed above. Where \(a_0\), \(a_1\), \(b_0\), \(b_1\), \(c_0\), \(c_1\) are arbitrary complex coefficients with \(|a_0|^2+|a_1|^2=1\), \(|b_0|^2+|b_1|^2=1\) and \(|c_0|^2+|c_1|^2=1\). The description of our CYQT scheme is shown in Fig. 2. Alice wants to transmit \(\alpha _0\) and \(\alpha _1\) to Bob, Bob wants to transmit his own two qubits \(\beta _0\) and \(\beta _1\) to Charlie, and similarly Charlie wants to transfer the two qubits in its possession \(\gamma _0\) and \(\gamma _1\) to Alice.
Description of the protocol of CYQT, each one of the three observers Alice, Bob and Charlie has a two-qubit state (\(\alpha _0\), \(\alpha _1\)), (\(\beta _0\),\(\beta _1\)) and (\(\gamma _0\),\(\gamma _1\)) respectively to teleport among themselves via quantum channel and by performing BSM.
CYQT protocol steps
The three participants Alice, Bob and Charlie, are spatially separated and entangled by a quantum channel, which means that the quantum information will be transmitted using the pre-shared quantum channel as well as other classical communication channels. The steps used to make our CYQT scheme are organized as follows:
-
After combining the three arbitrary two-qubit states to be transmitted with the twelve-qubit quantum channel, Alice carries out Bell state measurements (BSM) on qubits \(\alpha _0\) and \(A_2\), and will send to Bob the result of her measurement by classical communication channel.
-
Bob carries out BSM on qubits \(\beta _0\) and \(B_2\), and will send his BSM results to Charlie by classical communication channel.
-
Charlie carries out BSM on qubits \(\gamma _0\) and \(C_2\), and will send to Alice the result of his measurement by classical communication channel.
-
Alice carries out a second BSM on qubits \(\alpha _1\) and \(A_4\), and will send to Bob the result of his last measurement by classical communication channel.
-
Charlie carries out his second BSM on qubits \(\gamma _1\) and \(C_1\), and will send to Alice the result of his measurement by classical communication channel.
-
Bob ends the cycle of Bell state measurements, by carrying out BSM on qubits \(\beta _1\) and \(B_4\), and will send his BSM results to Charlie by classical communication channel.
Based on the received results, Alice, Bob and Charlie can recover the initial two-qubit quantum state send by Charlie, Alice and Bob respectively by applying appropriate unitary transformations (I, X, \(i\) \(Y\),Z).
Cyclic quantum teleportation of three arbitrary two-qubit states among the three users
To teleport the three arbitrary two-qubit state among the three collaborators Alice, Bob and Charlie as described in Fig. 2, one has to follow the CYQT protocol steps well detailed in “CYQT protocol steps” (see the Fig. 3). The combined state of the whole subsystems can be expressed as
Step 1: To implement the cyclic quantum teleportation protocol, Alice takes the first step by applying a BSM on her qubits \(\alpha _0\) and \(A_2\), the BSM basis is given by,
After measurement, if Alice’s BSM result was \(|{\Phi ^{+}}\rangle _{\alpha _0A_2}\), the state of the remaining sixteen subsystems suddenly collapsed to
Step 2: Immediately, Bob realize the second step in this protocol by carrying out a BSM on his qubits \(\beta _0\) and \(B_2\) in the same basis suggested in Eq. (8). Suppose that Bob’s BSM result was also \(\left| \Phi ^+\right\rangle _{\beta _0B_2}\), the state of the remaining fourteen subsystems suddenly collapsed to
Step 3: Basing on the same BSM basis proposed in Eq. (8), the third party Charlie ends the first cycle of the discussed CYQT by performing a BSM on his qubits \(\gamma _0\) and \(C_2\). If Charlie’s BSM result was \(\left| \Phi ^+\right\rangle _{\gamma _0C_2}\), the state of the remaining twelve subsystems collapsed to
Step 4: In the following steps, the three parties will realize the second cycle of the discussed CYQT. In this step, Alice carry out a second BSM on her qubits \(\alpha _1\) and \(A_4\). If Alice’s new BSM result was \(\left| \Phi ^+\right\rangle _{\alpha _1A_4}\), the state of the remaining ten subsystems would collapse into
at the end of this step, it is clear that Bob received Alice’s two-qubit state.
Step 5: In this sense, Charlie re-perform a second BSM on his qubits \(\gamma _1\) and \(C_4\). If Charlie’s new BSM result was \(\left| \Phi ^+\right\rangle _{\gamma _1C_4}\), the state of the remaining height qubits collapsed to
Step 6: Finally, Bob ends the second cycle of our proposed CYQT by performing the last BSM on his qubit \(\beta _1\) and \(B_4\). If Bob’s last BSM result was \(|{\Phi ^+}\rangle _{\beta _1B_4}\), the remaining six qubits might collapse to the state below
This final state can be expressed as
with
which are exactly the desired three two-qubit arbitrary states sends respectively by Bob to Charlie, by Charlie to Alice and by Alice to Bob. This means that receivers will not need to do any conversion to get the original sent states. This in the case when the BSMs results were respectively \(|{\Phi ^+}\rangle _{\alpha _0A_2}\), \(|{\Phi ^+}\rangle _{\beta _0B_2}\), \(|{\Phi ^+}\rangle _{\gamma _0C_2}\), \(|{\Phi ^+}\rangle _{\alpha _1A_4}\), \(|{\Phi ^+}\rangle _{\gamma _1C_4}\) and \(|{\Phi ^+}\rangle _{\beta _1B_4}\). For other possible BSM outcomes, receivers will have to apply appropriate transformations before they can exactly retrieve the original ones. Due to classical communication, receivers will be able to know exactly which Pauli unitary operators will be necessary to recover the exactly ones. To be precise, there would be \(2^{12}=4096\) possible measurement states (see the Table 1). Each one of them will have a certain series of appropriate unitary transformations that must be applied before the original transmitted information states can be reliably recuperated. We will not go over all of them, first because they are many, and secondly, because necessary transformations will be clear and intuitive. But despite that, and for more clarification, we discussed the first four of them. In table below, we can find the first four possible BSM result cases and their necessary conversions. Whatever the result of applied measurements, Alice, Bob and Charlie will be able to recover the original transmitted information states and thus we can be sure that the proposed CYQT protocol runs perfectly in all cases.
Quantum circuit illustrating the scheme of the proposed CYQT protocol of three two-qubit state \(|{\psi }\rangle _{\alpha }\), \(|{\psi }\rangle _{\beta }\) and \(|{\psi }\rangle _{\gamma }\) using a twelve-qubit state \(|{\psi }\rangle _{12}\) combining a six-qubit cluster state and a six-Bell state. The double lines decodes the classical wires and \(``U''\) decode Pauli unitary operations I, X, iY and Z. The output states \(|{\psi ^{'}}\rangle _{\alpha }\), \(|{\psi ^{'}}\rangle _{\beta }\) and \(|{\psi ^{'}}\rangle _{\gamma }\) represented the recovered states at the end of the teleportation protocol.
Panel (a) presents the quantum circuit fidelity, giving information about the accuracy of quantum teleportation protocol. Panel (b) shows the Teleportation Density, showing the distribution and characteristics of quantum states after teleportation.
Using Qiskit, the code (Fig. 3) prepares the quantum and classical registers. After defining a Toffoli gate matrix, it builds a quantum circuit that carries out several quantum operations. These measures correspond to the steps described above of the CYQT protocol. To transmit the quantum states, Alice, Bob, and Charlie each execute Bell State Measurements (BSM) on their individual qubits in the CYQT protocol. These procedures, which involve the use of CNOT gates, Hadamard gates, and measurements, appear in the circuit. A unitary gate that reflects the outcomes of the BSMs executed by the three parties is applied at the circuit’s conclusion. In order to represent the successful teleportation of the initial states between the parties, the circuit collapses the quantum state into a final state. the circuit show how the quantum operations transfer to the steps in the article, where each step is a particular party executing a BSM and collapsing the quantum state correspondingly. As described in the attached paper, the circuit functions as an implementation of a quantum circuit for CYQT, allowing the teleportation of arbitrary quantum states between multiple parties.
The fidelity of the quantum circuit is shown along the X-axis from 0 to 900 in the graph Fig. 4a. The number of shots varies. Data points are common, appearing approximately every 100 frames. On the Y-axis, the fidelity is shown as a range between 0.02 and a little above 0.12. The fidelity shows significant variation across different shot counts, with no clear increasing or negative tendency. Initially, fidelity increases significantly from zero shots to approximately one hundred. After about 300 shots, it stabilizes in the upper half of the graph after fluctuating for a while. The fidelity reaches its maximum at around 700 shots, or 0.12. The fidelity, on the other hand, reaches its minimum approximately 0.04, 200 shots after the beginning increase. When you get over 300 shots, fidelity seems to settle off even more. In the last \(600--900\) shots, there is less variation, but there are still obvious fluctuations. It also means that the performance of the circuit can vary depending on a number of factors or quantum processes like decoherence. In general, there is not an obvious increase or decrease trend, even when fidelity stabilizes at the end, indicating to the detailed dynamics of the quantum system.
The left side of graph Fig. 4b shows a three-dimensional grid that represents the density matrix components along the z-axis. This grid represents Alice’s (the first sender) unknown state. Alice unkown variable was given a randowm value to represent the density matrix, we could repeat the process for Bob and Charlie, but with different values. Every block in the grid represents a matrix element, and the element’s value is indicated by its height. All elements are non-negative and range from 0 to 0.25 on the z-axis scale, with a maximum value of 0.25. The color blue, doesn’t change continuously.
Protocol success probability and efficiency
As we have already shown, Alice, Bob and Charlie each have to apply two Bell state measurements, i.e. there will be a total of six Bell state measurements. So, we’ll have 4096 possible Bell state measurements results. The probability of each result is given by
\(\bullet \) The total success probability can be expressed as
\(\bullet \) The average lack of information S can be expressed as
it means that results have all equal probabilities. To study the performance of communication protocols58, we often calculate the efficiency factor defined by
where \(q_t\) denotes the number of qubits have been teleportated during the execution of the protocol (here it was three arbitrary two-qubit state i.e. 6 teleported qubits). And, \(q_s\) denotes the total number of qubits of the quantum channel used for teleportation (here we used a combination of a six-qubit cluster state and a six-qubit entangled state i.e. 12 entangled qubits), which means that the proposed protocol has an efficiency that can reach \(50\%\).
Concluding remarks
In summary, an original and perfect protocol of cyclic quantum teleportation by using a combination of six-qubit cluster state and six-qubit entangled state as quantum channel is presented for the first time. Where, the three distant parties Alice, Bob and Charlie are not only senders of information but also receivers of information. Alice can send an arbitrary two-qubit state to Bob and receive an arbitrary two-qubit state from Charlie and Bob can transmit an arbitrary two-qubit state to Charlie by performing Bell state measurements and appropriate unitary Pauli transformations after receiving the Bell state measurement results sent by others by classical way. In our scheme, the proposed quantum channel can be constructed by applying Controlled-Not gate and Hadamard gate on a twelve-qubit states all initialized to \(\left| 0\right\rangle \) which has been implemented experimentally. During the execution of the protocol, the three collaborators choose the same basis of Bell states to perform the necessary measurements on the qubits they have. In fact, each of the three parties must perform two Bell state measurements on their qubits, which means that there will be a total of six Bell state measurements, so there will be 4096 possible output states. All these cases have equal probabilities and the protocol offers a success probability of up to 100%. Particular attention was paid to the performance of the proposed protocol by calculating the information transfer efficiency factor and it was observed that this efficiency can reach 50%, which is a very important and honourable percentage. Finally, it is hoped that the results obtained and the proposed protocol will bring an additional advantage in the world of quantum communication and data transmission. This proposed protocol offers a novel and secure method for transmitting quantum information between three distant parties. It enables not only sending but also receiving information, thereby enhancing the efficiency of quantum communication. However, generalizing this approach to other quantum teleportation tasks (like CBCQT) or applying it to larger systems might pose challenges. Further investigation and analysis are necessary to determine the protocol’s effectiveness in these scenarios. We will address this question in a future work.
Data availability
The datasets used and/or analyzed during the current study available from the corresponding author on request.
References
Kimble, H. J. The quantum internet. Nature 453, 1023–1030 (2008).
Slaoui, A., Ikken, N., Btissam Drissi, L., & Ahl Laamara, R. Quantum communication protocols: From theory to implementation in the quantum computer. In Quantum Computers—From Fundamentals to Technology (IntechOpen, 2023).
Ikken, N., Slaoui, A., Ahl Laamara, R. & Drissi, L. B. Bidirectional quantum teleportation of even and odd coherent states through the multipartite Glauber coherent state: Theory and implementation. Quantum Inf Process 22, 391 (2023).
Bennett, C. H. et al. Teleporting an unknown quantum state via dual classical and Einstein-Podolsky–Rosen channels. Phys. Rev. Lett 70, 1895 (1993).
Steane, A. Quantum computing. Rep. Progr. Phys. 61, 117 (1998).
Horodecki, R., Horodecki, P., Horodecki, M. & Horodecki, K. Quantum entanglement. Rev. Mod. Phys. 81, 865 (2009).
Brassard, G., Cleve, R. & Tapp, A. Cost of exactly simulating quantum entanglement with classical communication. Phys. Rev. Lett 83, 1874 (1999).
Einstein, A., Podolsky, B. & Rosen, N. Can quantum-mechanical description of physical reality be considered complete. Phys. Rev. 47, 777 (1935).
Ma, X. S. et al. Quantum teleportation over 143 kilometres using active feed-forward. Nature 489, 269–273 (2012).
Gisin, N. & Thew, R. Quantum communication. Nat. Photon. 1, 165–171 (2007).
Heo, J. et al. Implementation of controlled quantum teleportation with an arbitrator for secure quantum channels via quantum dots inside optical cavities. Sci. Rep. 7, 1–12 (2017).
Chen, J., Li, D., Liu, M., Yang, Y. & Zhou, Q. Quantum controlled teleportation of bell state using seven-qubit entangled state. Int. J. Theor. Phys. 59, 1402–1412 (2020).
Vaidman, L. Teleportation of quantum states. Phys. Rev. A 49, 1473 (1994).
Xiao-Ming, X., Li, D., Ya-Jun, G. & Feng, C. Controlled quantum teleportation of a one-particle unknown state via a three-particle state. Commun. Theor. Phys. 48, 261 (2007).
Riebe, M. et al. Deterministic quantum teleportation with atoms. Nature 429, 734–737 (2004).
Bouwmeester, D. et al. Experimental quantum teleportation. Nature 390, 575–579 (1997).
Verma, V. & Prakash, H. Standard quantum teleportation and controlled quantum teleportation of an arbitrary n-qubit information state. Int. J. Theor. Phys. 55, 2061–2070 (2016).
Ma, P. C., Chen, G. B., Li, X. W. & Zhan, Y. B. Bidirectional controlled quantum teleportation in the three-dimension system. Int. J. Theor. Phys. 57, 2233–2240 (2018).
Li, X. & Deng, F. Controlled teleportation. Front. Comput. Sci. China 2, 147–160 (2008).
Na, C., Dongxiao, Q., Hong, Y. & Changxing, P. Perfect quantum controlled teleportation via a novel three-particle partially entangled channel. J. China Univ. Posts Telecommun. 22, 45–50 (2015).
Pirandola, S. & Braunstein, S. L. Physics: Unite to build a quantum Internet. Nature 532, 169–171 (2016).
Boschi, D., Branca, S., De Martini, F., Hardy, L. & Popescu, S. Experimental realization of teleporting an unknown pure quantum state via dual classical and Einstein-Podolsky-Rosen channels. Phys. Rev. Lett. 80, 1121 (1998).
Barrett, M. D. et al. Deterministic quantum teleportation of atomic qubits. Nature 429, 737–739 (2004).
Rigolin, G. Quantum teleportation of an arbitrary two-qubit state and its relation to multipartite entanglement. Phys. Rev. A 71, 032303 (2005).
Dong, J. & Teng, J. F. Controlled teleportation of an arbitrary N-qudit state using non-maximally entangled GHZ states. Eur. Phys. J. D 49, 129–134 (2008).
Espoukeh, P. & Pedram, P. Quantum teleportation through noisy channels with multi-qubit GHZ states. Quantum Inf. Process. 13, 1789–1811 (2014).
Zhang, B., Liu, X. T., Wang, J. & Tang, C. J. Quantum teleportation of an arbitrary N-qubit state via GHZ-like states. Int. J. Theor. Phys. 55, 1601–1611 (2016).
Nandi, K. & Mazumdar, C. Quantum teleportation of a two-qubit state using GHZ-like state. Int. J. Theor. Phys. 53, 1322–1324 (2014).
Yuan, W. Quantum teleportation of an arbitrary three-qubit state using GHZ-like states. Int. J. Theor. Phys. 54, 851–855 (2014).
Zuo, X., Liu, Y., Zhang, W. & Zhang, Z. Simpler criterion on W state for perfect quantum state splitting and quantum teleportation. Sci. China Phys. Mech. Astron. 52, 1906–1912 (2009).
Cao, H. J. & Song, H. S. Teleportation of a single-qubit state via unique W state. Int. J. Theor. Phys. 46(6), 1636–1642 (2007).
Man, Z. X., Xia, Y. J. & An, N. B. Quantum teleportation of an unknown N-Qubit W-Like state. JETP Lett. 85, 662–666 (2007).
Liu, Z. M. & Zhou, L. Quantum teleportation of a three-qubit state using a five-qubit cluster state. Int. J. Theor. Phys. 53, 4079–4082 (2014).
Li, Y. H., Li, X. L., Nie, L. P. & Sang, M. H. Quantum teleportation of three and four-qubit state using multi-qubit cluster states. Int. J. Theor. Phys. 55, 1820–1823 (2016).
Li, Y. H., Sang, M. H., Wang, X. P. & Nie, Y. Y. Quantum teleportation of a four-qubit state by using six-qubit cluster state. Int. J. Theor. Phys. 55, 3547–3550 (2016).
Sisodia, M. & Pathak, A. Comment on quantum teleportation of eight-qubit state via six-qubit cluster state. Int. J. Theor. Phys. 57, 2213–2217 (2018).
Cheung, C. Y. & Zhang, Z. J. Criterion for faithful teleportation with an arbitrary multiparticle channel. Phys. Rev. A 80, 022327 (2009).
Zhang, Z., Liu, Y. & Wang, D. Perfect teleportation of arbitrary n-qudit states using different quantum channels. Phys. Lett. A 372, 28–32 (2007).
Zhang, Z. J. & Man, Z. X. Many-agent controlled teleportation of multi-qubit quantum information. Phys. Lett. A 341, 55–59 (2005).
Karlsson, A. & Bourennane, M. Quantum teleportation using three-particle entanglement. Phys. Rev. A 58, 4394 (1998).
van Loock, P. & Braunstein, S. L. Multipartite entanglement for continuous variables: A quantum teleportation network. Phys. Rev. Lett. 84, 3482 (2000).
Zha, X. W., Zou, Z. C., Qi, J. X. & Song, H. Y. Bidirectional quantum controlled teleportation via five-qubit cluster state. Int. J. Theor. Phys. 52, 1740–1744 (2013).
Yuan, H. & Zhang, Z. Asymmetric bidirectional quantum qubit teleportation scheme via six-qubit Bell-cluster state. Laser Phys. Lett. 20, 105207 (2023).
Zhang, W., Li, B. & Zhang, Z. Cyclic deterministic bidirectional quantum controlled teleportation with maximally seven-qubit entangled state. Laser Phys. Lett. 17, 125202 (2020).
Hassanpour, S. & Houshmand, M. Bidirectional teleportation of a pure EPR state by using GHZ states. Quantum Inf. Process. 15, 905–912 (2016).
Chen, Y. Bidirectional controlled quantum teleportation by using five-qubit entangled state. Int. J. Theor. Phys. 53, 1454–1458 (2014).
Li, Y. H. & Nie, L. P. Bidirectional controlled teleportation by using a five-qubit composite GHZ-Bell state. Int. J. Theor. Phys. 52, 1630–1634 (2013).
Duan, Y. J., Zha, X. W., Sun, X. M. & Xia, J. F. Bidirectional quantum controlled teleportation via a six-qubit entangled state. Int. J. Theor. Phys. 53, 3780–3786 (2014).
Duan, Y. J., Zha, X. W., Sun, X. M. & Xia, J. F. Bidirectional quantum controlled teleportation via a maximally seven-qubit entangled state. Int. J. Theor. Phys. 53, 2697–2707 (2014).
Zhang, D., Wei, X., Wei, Z. & Yan, L. Bidirectional and asymmetric quantum controlled teleportation via maximally eight-qubit entangled state. Quantum Inf. Process 14, 3835–3844 (2015).
Zadeh, M. S. S., Houshmand, M. & Aghababa, H. Bidirectional quantum teleportation of a class of n-qubit states by using (\(2n+2\))-qubit entangled states as quantum channel. Int. J. Theor. Phys. 57, 175–183 (2018).
Chen, Y. X., Du, J., Liu, S. Y. & Wang, X. H. Cyclic quantum teleportation. Quantum Inf. Process 16, 1–201 (2017).
Sang, Z. Cyclic controlled teleportation by using a seven-qubit entangled state. Int. J. Theor. Phys. 57, 3835–3838 (2018).
Ting, G., Feng-Li, Y. & Zhi-Xi, W. Controlled quantum teleportation and secure direct communication. Chin. Phys. 14, 893 (2005).
Wang, T. Y. & Wen, Q. Y. Controlled quantum teleportation with Bell states. Chin. Phys. B 20, 04037 (2011).
Li, Y. H., Li, X. L., Sang, M. H., Nie, Y. Y. & Wang, Z. S. Bidirectional controlled quantum teleportation and secure direct communication using five-qubit entangled state. Quantum Inf. Process 12, 3835–3844 (2013).
Verma, V. Cyclic quantum teleportation via G-states. Mod. Phys. Lett. B 35, 2150145 (2021).
Kao, S. H., Chia-Wei, T. & Hwang, T. Enhanced multiparty controlled QSDQ using GHZ state. Commun. Theor. Phys. 55, 1007 (2011).
Acknowledgements
Princess Nourah bint Abdulrahman University Researchers Supporting Project number (PNURSP2024R407), Princess Nourah bint Abdulrahman University, Riyadh, Saudi Arabia. Also, Ahmed A. Abd El-Latif would like to thank Prince Sultan University for their support.
Funding
Princess Nourah bint Abdulrahman University Researchers Supporting Project number (PNURSP2024R407), Princess Nourah bint Abdulrahman University, Riyadh, Saudi Arabia.
Author information
Authors and Affiliations
Corresponding authors
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher's note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Slaoui, A., El Kirdi, M., Ahl Laamara, R. et al. Cyclic quantum teleportation of two-qubit entangled states by using six-qubit cluster state and six-qubit entangled state. Sci Rep 14, 15856 (2024). https://doi.org/10.1038/s41598-024-63395-z
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1038/s41598-024-63395-z
Keywords
This article is cited by
-
Multiparty joint remote state preparation via a GHZ-class network
Quantum Information Processing (2026)
-
Bipartite and tripartite entanglement in an optomechanical ring cavity
Journal of Russian Laser Research (2026)
-
Geometry and quantum brachistochrone analysis of multiple entangled spin-1/2 particles under all-range Ising interaction
Scientific Reports (2025)
-
Bidirectional multi-nodes quantum teleportation using discrete-time quantum walk
Scientific Reports (2025)
-
Quantum Interferometric Power Versus Local Quantum Uncertainty in Bell Coherent States Under Amplitude Damping
Brazilian Journal of Physics (2025)