Abstract
Edge computing has emerged as a prominent trend in the field of information technology, offering flexible and robust resources for the industrial Internet. How to migrate container accurately is crucial for edge computing in the industrial Internet, as it plays a vital role in enhancing service response speed and safeguarding uninterrupted continuity of production operations. In this paper, we explore the problem of container migration in edge computing within the industrial Internet, aiming to reduce latency and enhance reliability. We establish a two-objective optimization model to comprehensively capture the container migration problem and formulate it as a constrained optimization model. The formulated model provides a systematic framework that effectively balances the trade-off between reducing latency and enhancing reliability. To tackle the migration strategy derived from the optimization model, we propose a migration algorithm based on the improved binary whale optimization algorithm. Our migration algorithm incorporates the adaptive probability and adaptive position weight within the hunting and searching operations, effectively enhancing the search efficiency during the solving process. The experimental results demonstrate the effectiveness of the established model in reducing the objective value, while the proposed migration algorithm surpasses existing algorithms by achieving an average reduction of at least 15.59% in the objective value.
Similar content being viewed by others
Introduction
Different from traditional industrial networks, the industrial Internet deeply integrates informatization and industrial production process, and comprehensively improves the intelligent level of industrial production and management. In the context of Industry 4.0, it will apply emerging information technologies such as Internet of things1, big data2, and artificial intelligence3to improve the performance and efficiency of smart factories4. Cloud computing, as a mature information technology, can provide powerful and on-demand computing resources to support the intelligence of manufacturing industry5. Although the servers in cloud computing are distributed, they are deployed in a small geographical range, which makes cloud computing still concentrated in the macro view. Cloud computing requires tasks to be transmitted to remote cloud servers through the core network for executing, and cannot meet the requirements of sensitive latency, high privacy and massive data transmission. However, the industrial Internet involves large numbers of real-time production links, and enterprises have high requirements for the privacy of their production parameters. Moreover, extensive data is generated by complex industrial manufacturing processes and large numbers of sensors deployed in factories. Therefore, cloud computing cannot adapt to the industrial Internet.
As a pivotal technology within the realm of next-generation information technology, edge computing is proposed to provide near computing services by edge servers deployed at the demand side. Edge computing can integrate network, computing, storage, and application resources near industrial terminals, and provide near computing services to meet the key requirements of the industrial Internet, such as agile connection, real-time processing, data processing and privacy protection6. Edge computing has paved the way for factories to solve various problems, such as intelligent analysis, big data, augmented reality, etc7. The industrial Internet of things has been applied in the manufacturing system to enhance the perception of industrial terminals8,9, and the combination of edge computing and industrial Internet of things will greatly improve their intelligent ability10.
The container is a virtualization technology used to isolate and run services along with their associated dependencies in computing environments. Compared with traditional virtual machines, containers are more lightweight, and have faster startup speed and lower performance overhead. Containers can be deployed and migrated across various edge servers without the need for service reconfiguration or adjustment. As a mean of packaging and delivering services, containers streamline the service management of edge computing11. Simultaneously, leveraging containers to deliver services can significantly reduce the operation and maintenance costs for edge computing12. When industrial terminals move from one coverage area of an edge server to another, the currently running containers may be halted, resulting in service interruption13. Therefore, ensuring the continuity and stability of container services for industrial terminals during their mobility process necessitates accurate container migration. By migrating containers from the source edge server to the destination edge server, continuous services are provided to industrial terminals, thus ensuring the uninterrupted progression of production processes.
Accurate container migration is important for edge computing in the industrial Internet, as it effectively mitigates service interruption duration and guarantees uninterrupted continuity of production operations. Inaccurate container migration will cause service interruptions or data loss, thereby imposing negative consequences on production operations and potentially leading to the collapse of the industrial system. Furthermore, latency and reliability are two key requirements in the industrial Internet owing to the specialized exigencies inherent to industrial operations. These two requirements embody the persistent need for real-time data processing and operational continuity to safeguard production efficiency in the industrial Internet. A significant proportion of production processes necessitate low latency to facilitate real-time data processing, ensuring timely and effective decision-making within the operational workflow. For example, in the manufacturing process of large precision mechanical parts (e.g., propellers), the lathe adjusts its parameters in real time according to the part’s shape and size. The long latency hinders the lathe adjust its cutting parameters in time and then causes the produced parts fail to meet the expected indicators. Compared with edge computing in other fields, edge computing in the industrial Internet must have higher reliability. Unreliable edge computing has the potential to result in irreversible and significant repercussions that could adversely impact operational efficiency and even lead to production accidents. For example, in some continuous production processes (e.g., steel making, pharmaceuticals, etc.), the production process must be carried out step by step without interruption. The failure of edge computing will destroy a batch of products and even damage the manufacturing equipment (e.g., steel furnaces and reactors).
This paper considers scenarios where industrial terminals exhibit mobility, wherein the distance between the industrial terminals and edge servers progressively changes over time. When the position of the industrial terminal exceeds the coverage range of its edge server, the continuous provision of high-quality services cannot be guaranteed. Therefore, container migration is necessary to provide uninterrupted services in accordance with the mobility of industrial terminals. This paper centers its focus on the scenario characterized by the mobility of industrial terminals and studies the container migration problem for edge computing in the industrial Internet, aiming to achieve a synergistic reduction in latency and enhancement in reliability. We establish a two-objective optimization model to formulate the container migration problem with the aim to minimize the latency and failure probability. The established model employs a refined model that encompasses transmission latency, link latency, and processing latency to characterize the latency associated with container migration. The established model transforms the objective of enhancing reliability as the problem of minimizing the failure probability of container migration, employing a quantitative approach based on Poisson process. In order to obtain the optimal migration strategy from solving the established model, we propose a novel migration algorithm based on the improved binary whale optimization algorithm. The whale optimization algorithm, inspired by the hunting behavior of humpback whales, has been widely used for solving optimization problems. However, the efficiency of the original whale optimization algorithm is relatively low when applied to the container migration optimization model. The proposed migration algorithm improves the original operations by introducing the adaptive probability and adaptive position weight in the hunting and searching operations, thus improving the search efficiency. Finally, we conduct a series of experiments to thoroughly validate and evaluate both the established model and the proposed algorithm. The main contributions of this paper are summarized as follows:
-
(1)
We establish a two-objective optimization model to capture the container migration problem and formulate it as a constrained optimization model. To achieve better optimization of the latency, we utilize a refined model that comprehensively captures the various factors contributing to the latency of container migration. This latency model encompasses not only the transmission latency but also the link latency and processing latency involved in the migration process. To address the challenge of enhancing reliability in container migration, we strategically redefine the objective as the minimization of the probability of encountering failures during the migration process. By adopting a quantitative approach, we leverage the application of Poisson process to accurately quantify the likelihood of such failures occurring.
-
(2)
We propose a novel migration algorithm that builds upon and enhances the binary whale optimization algorithm to obtain the optimal migration strategy from the established model. We employ the adaptive probability and adaptive position weight in the hunting and searching operations, thereby improving the search efficiency and effectiveness. By incorporating the adaptive probability and position weight, the migration algorithm dynamically adjusts the likelihood of performing specific search operations and assigns varying importance to different positions during the search process. These adaptive mechanisms effectively enhance the migration algorithm’s ability to explore the search space and optimize the container migration problem more efficiently.
-
(3)
We conduct extensive simulation experiments to validate the established system model and evaluate the effectiveness of the proposed migration algorithm. These experiments comprehensively investigate the influence of diverse system parameters on the optimization objective. We perform a comparative analysis of our migration algorithm against four existing algorithms to assess its efficiency and performance. The rest of this paper is organized as following. The second section reviews the related work. The third section introduces the system model. The migration algorithm is illustrated in the fourth section. In the fifth section, the established system model and proposed migration algorithm are evaluated. The sixth section concludes this paper.
Related work
Container deployment is primarily tailored for fixed terminal scenarios, where mobility is not a requirement of the terminal. In such scenarios, the emphasis lies in creating a stable container environment that remains stationary without the necessity of container transfers as the terminal relocates. In contrast, container migration is intended for scenarios where terminals are mobile, and containers need to move in sync with the terminals. However, despite the growing importance of container migration, the existing research in this area remains relatively limited compared to the extensive studies focused on container deployment. The majority of existing research primarily concentrates on container deployment, with comparatively limited investigation dedicated to container migration. To address the challenges associated with container migration, some researchers have begun to conduct investigations. In this section, we provide an overview of the existing research on container migration, highlighting the key contributions made in this domain.
Latency reduction
Latency is a critical performance metric in the container migration process, and reducing latency can significantly enhance system responsiveness and user experience. By minimizing the latency, the waiting time for containers can be reduced, leading to the improved container availability and performance. Therefore, the majority of existing research on container migration aims to decrease the latency as a primary objective.
Martin et al. proposed a general container migration framework named MAMF for fog computing14. They utilized the MAPE loop and genetic algorithm to migrate containers, aiming to reduce the latency. Machen et al. proposed a generic layered architecture for migrating containers among edge servers15. This architecture divides the migrated containers into multiple modules, aiming to reduce the download latency. Kimet al. conducted a study on the live container migration problem in edge computing and presented three zero-downtime migration techniques that leverage state duplication and state reproduction methods16. Their primary objective is to collectively minimize both response latency and network traffic during the migration process. Yin et al. studied the container-based service migration problem in edge computing for smart contract with the aim of reducing the service latency17. They proposed a migration mechanism that incorporates mobility awareness by considering various factors, including image file download, vehicle movement, and service density. Zhang et al. investigated the container migration problem within the realm of edge computing and Internet of vehicles with the aim to reduce the service latency while distributing the containers as evenly as possible18. They formulated the problem as a 0-1 programming model and proposed a container pre-migration strategy based on the vehicle trajectory prediction. Lou et al. studied the container migration problem with the consideration of the joint optimization of the layer download sequence and formulated it as a NP-hard model19. Their objective is to minimize the total startup latency, and to achieve this, they proposed a layer-aware algorithm for assigning containers to suitable edge servers. Shao et al. conducted a study on the container migration problem within the context of the Internet of vehicles and proposed a migration mechanism comprising three distinct components20. Their primary objective was to minimize the latency and proposed a migration algorithm based on an enhanced artificial bee colony algorithm. Lin et al. established a container migration model specifically tailored for the Internet of vehicles business scenario within the framework of edge computing and aimed to minimize the latency21. They devised a migration algorithm that employs dynamic programming and incorporates the shortest path principle to obtain the globally optimal solution for migration decision-making. Tang et al. studied the dependency-aware container scheduling problem in a heterogeneous mobile edge computing with the aim to minimize the latency from a long-term perspective22. They formulated the problem as a Markov decision process and proposed a policy gradient algorithm to solve this problem. Al-Tarawneh proposed a mobility-aware container migration algorithm for cloudlet-enabled Internet of things systems with the objective of reducing the latency23. His migration algorithm was developed based on an integrated multi-criteria decision-making method. Aleyadeh et al. conducted an investigation on the container orchestration problem within a hybrid computing environment and proposed an optimal container migration model to optimize the orchestration methods with a specific focus on latency and container dependencies24. Tang et al. studied the multi-user layer-aware online container migration in edge-assisted vehicular networks and proposed a migration algorithm to reduce the overall latency25. They introduced a feature extraction method that utilizes attention and long/short-term memory techniques. Additionally, they proposed a reinforcement learning algorithm based on policy gradients to facilitate the online migration decision-making. Thongthavorn and Rattanatamrong studied the multi-container migration problem in the wide area network by utilizing multiple TCP connections over a single direct path26. The objective of their migration approach is to attain an optimal balance between minimizing the total migration latency and ensuring a favorable average individual migration latency. Temp et al. presented a dynamic strategy for provisioning container registries, which takes into account the mobility of users27. The strategy involves the creation of new registries when the container provisioning latency exceed the acceptable thresholds and the removal of registries located far away from users.
Load balancing
In addition to reducing the latency, some researchers have placed an emphasis on load balancing as an objective in container migration. In the distributed edge computing system, load balancing plays a crucial role in ensuring the proper allocation of resources and preventing performance degradation or container unavailability due to overloaded nodes. By considering load balancing as a goal in container migration, researchers aim to leverage intelligent migration strategies and algorithms to evenly distribute the workload across edge servers, thereby improving the overall system performance and scalability.
Xin et al. conducted an investigation on the container migration problem within the realm of the power Internet of things and proposed a container migration mechanism to achieve the objective of load balancing28. They established a container migration model and devised a migration algorithm using an enhanced ant colony algorithm. Ma et al. presented a decision-making mechanism based on container migration in the context of the power Internet of things and established a container migration model of load balancing joint migration cost29. They designed a modified ant colony-based migration algorithm based on their proposed mechanism to solve the container migration problem. Li et al. presented a container migration strategy in the smart grid with a specific focus on addressing the issue of unbalanced load in the edge network under varying service requirements30. They designed a migration algorithm based on the ant colony algorithm to realize load balancing and reduce migration cost. Duan et al. conducted a study on the container migration problem and took into account the interference that may arise among multiple users31. They proposed a migration method to address resource competition and alleviate the challenge of overload on edge servers. Baburao et al. proposed a particle swarm optimization-based container allocation method to handle the load balancing problem in fog computing32. Patra et al. studied the problem of load balancing in the containerized cloud and established a system model consisting of five components33. They proposed a grey wolf optimization-based simulated annealing algorithm to solve their model. Singh et al. formulated the two-period resource allocation problem as a Stackelberg game with the consideration of the service level agreement34. They proposed an energy-efficient ensemble for container allocation, consolidation and migration for load balancing in software-defined edge computing environment. Hadeed and Abdullah evaluated the performance of the Docker container management system on resource constrained computers and designed several methods based on workload types to achieve the objective of load balancing35. They proposed a mechanism to prioritize the container balance between the edge and cloud. Zhang et al. designed a two-stage container management framework to optimize both the migration cost and the degree of load balancing36. To address the optimal strategy, they proposed a balance-aware container deployment algorithm and an adaptive threshold container migration algorithm. Aslanpour et al. proposed a performance-driven load balancing approach and designed a heterogeneous serverless edge architecture to configure and utilize the load balancing strategies37.
Brief summary
Existing work has predominantly focused on reducing latency and balancing loads, often overlooking the importance of reliability within the container migration process. However, within the context of the industrial Internet, the significance of reliability cannot be overstated, as it plays a pivotal role in ensuring the seamless continuity of industrial production. Uninterrupted and reliable operation is essential for maintaining productivity, quality, and efficiency in industrial settings. Any disruptions can have detrimental consequences, leading to financial losses, decreased customer satisfaction, and potential safety hazards. Consequently, it becomes imperative to highlight and prioritize the significance of reliability when devising and implementing the edge computing system within the scope of the industrial Internet. Different from the majority of existing studies that primarily concentrate on latency reduction or load balancing, our paper takes a novel approach by addressing both latency reduction and reliability enhancement simultaneously. The proposed approach consists of a novel two-objective container migration optimization model and a novel migration algorithm based on an improved binary whale optimization algorithm. In contrast to previous research endeavors, our approach goes beyond the conventional scope by extensively integrating the distinctive demands and limitations inherent in the industrial Internet domain. This comprehensive consideration of the specific requirements and constraints of the industrial environment ensures a high level of compatibility and applicability. By acknowledging and addressing the intricacies of industrial operations, our approach effectively caters to the unique challenges and complexities encountered within the industrial Internet.
System model and problem formulation
System model
Container model and migration strategy
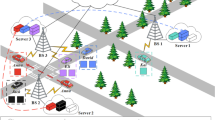
Figure 1 illustrates the container migration scenario in the intelligent factory, where a set of edge servers is responsible for processing task requests from mobile industrial terminals. As the industrial terminal moves from one geographical region to another, it becomes necessary to migrate the active containers to the destination region to uphold uninterrupted operations. This migration process is crucial in maintaining seamless continuities and ensuring that the containers remain accessible and functional throughout the movement. The regions covered by n edge servers are represented by set \(S = \{ {s_1},{s_2}, \cdots ,{s_n}\}\). Let set \(C = \{ {c_1}, \cdots ,{c_k}, \cdots ,{c_K}\}\) denote the collection of containers on the edge servers that are currently processing task requests from mobile industrial terminals. Each container possesses four attributes, namely its location, required computing resources, required storage resources, and required bandwidth resources. The four attributes of container \(c_k\) are denoted as \(L_k^c = (l_k^c,g_k^c)\), \({\psi _k}\), \({\tau _k}\), and \({\delta _k}\), respectively. As time progresses, the industrial terminal will move from its current region to the destination region. Let set \(S^{'} = \{s_1^{'},s_2^{'}, \cdots , s_n^{'}\}\) denote the destination region covered by the edge servers. Each edge server possesses four attributes, namely its location, computing resource capacity, storage resource capacity, and bandwidth resource capacity. The four attributes of edge server \(e_j\) are denoted as \(L_j^s = (l_j^s,g_j^s)\), \({\lambda _j}\), \({\mu _j}\), and \({\eta _j}\), respectively. Let \({C_j} = \{ {c_{j,1}},{c_{j,2}}, \cdots ,{c_{j,r}}\}\) denote the collection of containers initially deployed on edge server \(e_j\). The distance \(d_{i,j}\) between edge servers \(e_i\) and \(e_j\) is calculated by
Let binary variable \(x_{i,j}^k\) represent the migration strategy that denotes whether container \(c_k\) is migrated from source edge server \(e_i\) to edge server \(e_j\) in the destination region. If container \(c_k\) is migrated from source edge server \(e_i\) to destination edge server \(e_j\), then \(x_{i,j}^k=1\); otherwise, \(x_{i,j}^k=0\).
The container migration scenario in the intelligent factory.
Latency model
In the container migration process, latency is a crucial performance metric. When the location of industrial terminal changes, the container responsible for processing its tasks needs to be migrated from the current edge server to the destination edge server with the lowest latency. In order to optimize the latency more effectively, we employ a refined model that comprehensively accounts for the multiple factors influencing container migration latency. This refined latency model encompasses not only the transmission latency but also incorporates the link latency and processing latency associated with the migration process.
-
(1)
Transmission latency The transmission latency of container migration refers to the time required for the source edge server to transmit the container. Let \(TF_{i,j}^k\) denote the transmission latency of container \(c_k\) migrated from edge server \(e_i\) to edge server \(e_j\). \(TF_{i,j}^k\) is expressed as
$$\begin{aligned} TF_{i,j}^k = \frac{{{D_k}}}{{{W_b}lo{g_2}(1 + {\varphi _{i,j}})}}, \end{aligned}$$(2)in which \(D_k\) represents the data volume of container \(c_k\), \(W_b\) denotes the network bandwidth, and \({\varphi _{i,j}}\) represents the signal-to-noise ratio.
-
(2)
Link latency The link latency of container migration refers to the propagation delay incurred when the container is migrated from the source edge server to the destination edge server. Let \(TB_{i,j}^k\) denote the link latency incurred during the migration process of container \(c_k\) migrated from source edge server \(e_i\) to destination edge server \(e_j\). \(TB_{i,j}^k\) is expressed as
$$\begin{aligned} TB_{i,j}^k = \frac{{{d_{i,j}}}}{\phi } = \frac{{\sqrt{{{(l_i^s - l_j^s)}^2} + {{(g_i^s - g_j^s)}^2}} }}{\phi }, \end{aligned}$$(3)in which \({d_{i,j}} = \sqrt{{{(l_i^s - l_j^s)}^2} + {{(g_i^s - g_j^s)}^2}}\) represents the distance between edge servers \(e_i\) and \(e_j\), and \(\phi\) represents the signal propagation rate on the channel.
-
(3)
Processing latency The processing latency of container migration refers to the time required for the container to acquire resources on the destination edge server. In this paper, it is defined as the average processing time for the container to acquire computing resources, storage resources, and bandwidth resources on the destination edge server. Let \(TP_j^k\) represent the processing latency of container \(c_k\) on the destination edge server \(e_j\). \(TP_j^k\) is expressed as
$$\begin{aligned} TP_j^k = \frac{{\frac{{{\omega _k}}}{{\widehat{{\lambda _j}}}} + \frac{{{\tau _k}}}{{\widehat{{\mu _j}}}} + \frac{{{\delta _k}}}{{\widehat{{\eta _j}}}}}}{3} , \end{aligned}$$(4)in which \(\widehat{{\lambda _j}}\), \(\widehat{{\mu _j}}\), and \(\widehat{{\eta _j}}\) respectively represent the computing resource, storage resource, and bandwidth resource allocations that can be made by edge server \(e_j\) per unit of time. The total migration latency of container \(c_k\) migrated from edge server \(e_i\) to edge server \(e_j\) is expressed as
$$\begin{aligned} TT_{i,j}^k = TF_{i,j}^k + TB_{i,j}^k + TP_i^k. \end{aligned}$$(5)
Reliability model
The utilization of computing resources, storage resources, and bandwidth resources on destination edge server \(e_j\) is respectively expressed as
and
The average utilization of computing resources, storage resources, and bandwidth resources across all edge servers in the destination region is respectively expressed as
and
During the process of container migration from the source edge server to the destination edge server, there is a possibility of encountering excessive workload, ultimately leading to the failure, thereby reducing the system reliability and impacting the continuity of industrial production. The failure rate of container migration is measured by the edge server failures, where a smaller failure rate corresponds to higher reliability. By adopting a quantitative approach, we utilize Poisson process to accurately quantify the probability of such failures occurring. The failure rate of container migration is expressed as
\(\theta\) is caculated by
Problem formulation
The optimization objectives of this paper are to minimize the latency and maximize the reliability. The reliability can be enhanced by reducing the failure rate. Maximizing the reliability can equivalently be transformed into minimizing the failure rate. To address these two optimization objectives, a linear weighting method is employed to map reliability onto latency, establishing a container migration model. The optimization objectives are achieved by minimizing the overall objective function. Objective function F(X) is expressed as
in which X is the unknown matrix with element \(x_{i,j}^k\), \(\Upsilon\) is the compromise coefficient. The failure rate is mapped onto the total latency through \(\Upsilon\), which is expressed as
\(\alpha \in (0,1)\) is the weight coefficient, which is utilized to adjust the weight of the two objectives. As \(\alpha\) increases, the impact of latency on the objective value becomes more significant, whereas as \(\alpha\) decreases, the impact of the failure rate on the objective value becomes more significant. \({\left( {\cdot } \right) ^{\max }}\) is used to obtain the maximum value of the input. \({\theta ^{\max }}\) is calculated by
The container migration model is mathematically formulated as a constrained optimization problem, represented by the objective function (17) along with associated constraints (18)-(22). By formulating the container migration as a constrained optimization problem, the model provides a quantitative approach to finding the optimal migration strategy that optimizes the specified objective while adhering to the defined constraints.
s.t.
Each edge server can run different types of containers, providing services to multiple industrial terminals simultaneously. However, due to the limited resource capacity, only a certain amount of containers can be run at a given moment. Constraints (18), (19), and (20) respectively limit the resource requests of migrating containers to the destination edge server, ensuring that the computing, storage, and bandwidth resource capacities of the destination edge server are not exceeded. Constraint (21) imposes a binary constraint on the migration strategy, allowing only two possible options: either to migrate the container to the destination edge server or not. Constraint (22) restricts that a container can only be migrated to one destination edge server.
Description of the proposed migration algorithm
Algorithm overview
The established container migration model is a complex discrete optimization problem with multiple constraint conditions, requiring a comprehensive search of the solution space due to the existence of multiple feasible solutions. The whale optimization algorithm exhibits several advantages over other optimization algorithms, such as rapid convergence, robust global search capabilities, and inherent suitability for parallelization. We adopt the whale optimization algorithm as the foundational algorithm. We discretize it and propose some improvements to its operations. Accordingly, we propose a migration algorithm based on the improved binary whale optimization algorithm to solve the container migration model. Specifically, we initially employ binary encoding at the initialization phase to adapt the established container model. Furthermore, in the hunting operation, we employ the adaptive probability to replace the previous fixed one. The adaptive probability enhances the initial global search capability of the migration algorithm. Subsequently, in the later stages, it prioritizes local search, effectively maintaining the diversity and convergence of the search process. Next, in the searching operation, we introduce adaptive position weights to enhance the algorithm’s ability to precisely locate the position of the prey, thereby improving the search efficiency and performance of the algorithm. Finally, during the iterative update of the algorithm, the whales are categorized into the best group, moderate group, and worst group based on their fitness values. Subsequently, a portion of the worst group is replaced by whales from the best group, thereby accelerating the solution space exploration process. The pseudocode for the migration algorithm based on the improved binary whale optimization algorithm is presented as Algorithm 1.
The migration algorithm based on the improved binary whale optimization algorithm
Encoding
The whale optimization algorithm is primarily designed for addressing continuous optimization problems, whereas the container migration problem in the context of industrial Internet involves a combinatorial optimization problem, necessitating improvements in its encoding scheme. We employ binary encoding, as illustrated in Fig. 2. In the two-dimensional encoding scheme, the horizontal elements represent the identifiers of the containers to be migrated, while the vertical elements represent the identifiers of the edge servers. The encoding scheme consists of only two values, 0 and 1, where “1” indicates that the container is migrated to the corresponding edge server, and “0” indicates that the container is not migrated to the corresponding edge server. Therefore, migration strategies can be derived from the encoding scheme, thereby guiding the migration of containers.
The encoding scheme.
Encircling prey
Within the effective search range of the solution space, each whale represents a potential solution, where its position denotes the location of the solution within the search space. The whale’s swimming speed and direction indicate the direction and distance of the solution’s variation within the search space. The whale’s position is characterized by multiple dimensions, where the location within a dimension corresponds to an element within the encoding scheme. During the iterative process of the algorithm, assuming the current best solution as a global approximation, other individual whales update their position information based on the difference in their positions compared to the current best solution. The update procedure is expressed as
and
in which t denotes the current iteration count, \(x_t^*\) represents the position of the best whale in the population, \(x_t\) represents the position of the current whale, and D represents the absolute difference in position between the best whale and current whale. A and D are calculated by
and
in which \(r_1\) and \(r_2\) are two random numbers between 0 and 1, and a is a linear decay parameter. a gradually decreases from 2 to 0 as the algorithm iterates, calculated by
Containers are migrated as a whole, necessitating the mapping of continuous domain coordinates to discrete domain values after updating the positions of the whales. We achieve this by converting the real-valued positions into fuzzy values through a mapping function, and then transforming them into binary numbers to obtain the discrete position information. \(x_t\) is discretized by
in which \(\zeta\) is a random number between 0 and 1.
Improved bubble-net feeding based on the adaptive probability
Whales continuously narrow down the encircling circle around their prey while employing a spiral ascending motion to pursue their hunting behavior. We replace the previous fixed probability with an adaptive probability p1, which allows whales to enhance the diversity and convergence of the search during the algorithm’s iterative process. p1 is calculated by
in which \(\omega\) represents the control parameter. The new position of the whale is calculated by
and
in which b is shape parameter of the whale’s spiral hunting behavior, l is a random number between -1 and 1, and \(D^{''}\) represents the absolute difference in position between the best whale and current whale.
When \(|A| < 1\), whales probabilistically choose to shrink the prey enclosure or to launch an attack on the prey using the spiral hunting strategy, expressed as
in which p is a random number between 0 and 1. After updating the whale’s position, \(x_{t+1}\) is discretized using Eq. (28).
Improved prey search based on the adaptive weight
When \(|A| \ge 1\), whales engage in a random search behavior with a certain probability while shrinking the prey encircling area. During this time, the position update of a whale primarily depends on the position information of a randomly selected whale from the population. We employ an adaptive position weight to enable whales to more accurately locate the prey, thereby enhancing the search efficiency and performance of the algorithm. The adaptive position weight w is expressed as
in which \(\varepsilon\) represents the weight of the position. The new position of the whale is calculated by
and
in which \(x_{rand}\) represents the position information of a randomly selected whale from the population, and \(D^{'}\) represents the absolute difference between the position of the selected whale and the current whale. After updating the whale’s position, \(x_{t+1}\) is discretized using Eq. (28).
Experiment and analysis
Experimental setup
To validate the established model and assess the performance of the proposed migration algorithm, we conduct a comprehensive set of numerical simulation experiments in this section. The experiments are performed on a computer equipped with the Intel (R) Core(TM) i7-10750H CPU running at a base frequency of 2.6 GHz, 16 GB of RAM, and a 64-bit operating system. The migration algorithms are implemented with Java under JDK 1.8 development environment. The experiment commences with a comparative analysis of the efficacy of our migration algorithm against other migration algorithms. Subsequently, it assesses the established migration model by investigating the impact of system parameters on the objective value. When assessing the migration algorithm, these algorithms are configured with identical population sizes (L), and they share the same maximum number of iterations (T). The default simulation parameters are shown in Table 1. To ensure the comprehensiveness of the experiments, the parameters are provided as ranges rather than fixed values. Accordingly, experimental parameters are generated randomly within the specified parameter ranges. For example, the number of containers to be migrated can range from 0 to 40, inclusive. This approach is adopted to capture the variability and explore a wider range of scenarios, enabling a more robust evaluation of the established model and the performance of the proposed algorithm.
Comparison of the migration algorithms
In this section, a comparative analysis is conducted to validate the performance of the proposed migration algorithm by comparing it with existing algorithms. The experiments in this section encompass the evaluation of five distinct migration algorithms, namely:
-
(1)
MA-IBWOA: Our proposed migration algorithm based on the improved binary whale optimization algorithm.
-
(2)
MA-GA: The migration algorithm based on the genetic algorithm.
-
(3)
MA-GWOA: The migration algorithm based on the grey wolf optimization algorithm.
-
(4)
MA-RA: The migration algorithm based on the random algorithm.
-
(5)
MA-BWOA: The migration algorithm based on the binary whale optimization algorithm.
Figure 3 illustrates the comparative evaluation of the migration algorithms’ performance across different numbers of iterations. This experiment provides insights into the migration algorithms’ effectiveness and efficiency as the number of iterations varies, allowing for a comprehensive analysis of their behavior and performance characteristics. With the increase in the number of iterations, it can be observed that the objective values of the migration algorithms continuously decrease. Compared to other migration algorithms, MA-IBWOA achieves the lowest final objective value. When quantitatively comparing MA-IBWOA with MA-GA, MA-GWOA, MA-RA, and MA-BWOA, the relative errors in their final objective values are determined as 20.64%, 41.89%, 65.88%, and 33.61%, respectively. MA-RA exhibits the highest final objective value, with an increase of 65.88% compared to MA-IBWOA. MA-GA achieves a relatively low final objective value, but the final objective value of MA-IBWOA is still 17.11% lower than that of MA-GA. The reason for the superior performance of MA-IBWOA lies in its utilization of adaptive probabilities during hunting behavior, which helps maintain diversity and convergence in search during algorithmic iterations. Additionally, MA-IBWOA incorporates adaptive position weights during prey search to enhance the precision of whale positioning, thereby improving its search efficiency and performance.
Comparison of migration algorithms’ performance under different numbers of iterations.
Figure 4 presents a comparative evaluation of the running time of migration algorithms, considering an equal number of containers. This figure provides insights into the performance and efficiency of these algorithms in terms of their execution time under identical container configurations. It can be observed that MA-RA exhibits the shortest running time, primarily due to its random strategy for migration, which avoids the time-consuming iterative computations towards optimization. However, this search mode significantly weakens the search performance of MA-RA, resulting in higher objective values, as confirmed by Fig. 3. MA-GWOA exhibits the longest running time, primarily due to the gray wolf optimization algorithm’s iterative update process. In each iteration, it requires sorting the wolf pack based on fitness values and selecting the top three individuals. Additionally, the distance between the wolves and the prey is primarily determined based on the positions of the top three wolves. The whale optimization algorithm shares similarities with the grey wolf optimization algorithm as both employ a strategy of surrounding and then attacking the prey. However, the difference lies in the whale optimization algorithm’s approach, which utilizes information from its own position and the surrounding environment to determine the distance between the whale and the prey. The whale then approaches the prey in a spiral ascending manner. Consequently, MA-BWOA exhibits a lower running time compared to MA-GWOA. The running time of MA-IBWOA is lower compared to those of MA-GWOA and MA-GA, but higher than that of MA-BWOA. This can be attributed to the fact that in each iteration update, MA-IBWOA sorts the whale population and replaces the lower-ranked individuals with the higher-ranked ones, ensuring that more elite whales can progress to the next generation. The additional operations in MA-IBWOA, while extending its running time beyond that of MA-BWOA, concurrently enhance the solution accuracy. Although MA-IBWOA has a slightly higher running time compared to MA-BWOA, with an increase of 17.24%, Fig. 3 demonstrates that MA-IBWOA achieves a lower objective value compared to MA-BWOA. Specifically, the objective value has decreased by 25.15%. This indicates that MA-IBWOA’s disadvantage in running time can be entirely offset by the enhancement in solution accuracy. Therefore, MA-IBWOA is more appropriate for addressing the container migration model elucidated in this paper, consequently yielding migration strategies.
Comparison of migration algorithms’ running time.
Comparison of migration algorithms’ performance and running time under different numbers of containers to be migrated.
Figure 5 presents a comparative comparison of the performance and running time of migration algorithms under varying numbers of containers to be migrated. This figure provides a comprehensive evaluation of these algorithms’ performance across different container configurations. It can be observed from Fig. 5a that as the number of containers to be migrated increases, the objective values consistently rise, and the magnitude of increase is relatively significant. This is attributed to the inherent relationship between the increasing number of containers to be migrated and the corresponding increase in overall latency. The objective values of MA-GA, MA-GWOA, MA-IBWOA, MA-RA, and MA-BWOA increase by 272.9%, 322.99%, 235.7%, 303.71% and 339.51% respectively. It can be seen that MA-IBWOA exhibits the smallest increase in magnitude. Under the same number of containers to be migrated, MA-IBWOA achieves the smallest objective value compared to other migration algorithms. Furthermore, as the number of containers to be migrated increases, the difference between MA-IBWOA and other migration algorithms becomes increasingly significant. Based on the observations from Fig. 5b, it can be noted that the running time of the migration algorithms consistently increases with an increase in the number of containers to be migrated. The running time of MA-GA, MA-GWOA, MA-IBWOA, MA-RA, and MA-BWOA increase by 259.66%, 287.4%, 242.44%, 2.67% and 282.13% respectively. The underlying reason behind this phenomenon is that the solution space experiences an exponential growth with an increase in the number of containers to be migrated, thus leading to a corresponding increase in the running time of the migration algorithms.
To provide a comprehensive validation of the proposed migration algorithm, a comparative analysis was conducted by evaluating its performance against existing migration algorithms across various trajectories of the mobile industrial terminal. Table 2 presents the objective values of migration algorithms under different trajectories, while Fig. 6 visually depicts their performance through the box plot. The results indicate that there is significant variation in the objective values of the same migration algorithm under different trajectories. This can be attributed to the disparities in coverage and resource availability of edge servers across different trajectories. However, under the same trajectory, MA-IBWOA consistently achieves the smallest objective values. Additionally, the average objective value of MA-IBWOA is also smaller than that of the other migration algorithms. Compared to MA-GA, MA-GWOA, MA-RA, and MA-BWOA, MA-IBWOA exhibits average objective value reductions of 15.59%, 30.18%, 40.08%, and 25.25% respectively.
Objective values of migration algorithms in different trajectories.
Evaluation of the system model
Figure 7 illustrates the impact of the weight coefficient on objective values. As the value of \(\alpha\) increases, the objective values show an upward trend. Specifically, when \(\alpha\) increases from 0.1 to 0.4, the objective values exhibit a slow and gradual increase. As \(\alpha\) further increases from 0.4 to 0.6, the upward trend in objective values becomes smoother. Finally, as \(\alpha\) continues to increase from 0.6 to 0.9, the upward trend in objective values becomes more pronounced. Quantitatively, the segmented slopes of these three segments are 783.31, 325.86, and 6885.42, respectively. With an increase in \(\alpha\), the influence of latency on the objective value becomes increasingly significant, while a decrease in \(\alpha\) leads to a more pronounced impact of the failure rate on the objective value.
Objective values under different weight coefficients.
The number of edge servers under different numbers of containers to be migrated.
Figure 8 illustrates the number of edge servers under different numbers of containers to be migrated. It can be observed that as the number of containers to be migrated increases, the number of edge servers within the destination region also increases continuously. Examining the specific data points, it is evident that with a migration of 10 containers, the number of edge servers stands at 9. However, as the number of containers to be migrated escalates to 50, the number of edge servers rises to 20. This trend suggests a proportional relationship, where a higher number of containers necessitates a greater number of edge servers to handle the migration process effectively. The underlying reason for this phenomenon lies in the need to accommodate the increasing number of containers during the migration process. Each container requires resources, which are provided by the edge servers. As the number of containers to be migrated rises, a larger pool of edge servers is required to distribute the workload adequately and ensure efficient migration.
Figure 9 illustrates the impact of the control parameter on objective values. It can be observed that as \(\omega\) gradually increases from 1 to 3, the objective value gradually decreases. This trend suggests that increasing the value of \(\omega\) leads to a reduction in the objective value, indicating improved optimization performance. The decreasing objective value indicates that the algorithm is moving closer to the optimal solution. However, when \(\omega\) exceeds 3, the objective value starts to increase with further increments of \(\omega\). This unexpected change suggests that excessively high values of \(\omega\) can have a detrimental effect on the optimization process, leading to a deterioration in the objective value. Remarkably, the minimum value of the objective value is achieved when \(\omega\) is set to 3. This finding implies that the optimal balance between exploration and exploitation is achieved with this specific value of the control parameter. Consequently, based on this observation, the control parameter \(\omega\) of the proposed migration algorithm is deliberately set to 3 in this paper to achieve the best possible optimization outcome. By extensively evaluating the impact of the control parameter on the objective values, the optimal value of \(\omega\) is determined. Subsequently, the adaptive probability obtained through Eq. ( 29) can assist the proposed migration algorithm in better maintaining search diversity and convergence during iterations.
Objective values under different control parameters.
Figure 10 illustrates the impact of the position weight parameter on objective values. It can be observed that as the value of \(\varepsilon\) increases, the objective value exhibits a distinct pattern. Initially, as \(\varepsilon\) increases, the objective value gradually decreases. This decline suggests an improvement in optimization performance as the migration algorithm explores different positions. However, the trend shifts when \(\varepsilon\) reaches a certain threshold. Beyond this point, the objective value starts to gradually increase with further increments of \(\varepsilon\). This change indicates that excessively high values of \(\varepsilon\) can have a negative impact on the optimization process, leading to a deterioration in the objective value. When the value of \(\varepsilon\) is equal to 5, the objective value is minimized. Therefore, in this paper, the position weight parameter \(\varepsilon\) of the proposed migration algorithm is set to 5. Subsequently, the adaptive position weight, calculated through Eq. (33), is used to assist the migration algorithm in accurately locating the prey’s position, thereby improving the algorithm’s search efficiency and performance.
Objective values under different position weight parameters.
Conclusions
This paper aims to address the challenge of edge computing container migration faced by mobile industrial terminals in the industrial Internet, with a focus on reducing latency and enhancing reliability. We establish a two-objective optimization model to comprehensively capture the container migration problem and formulate it as a constrained optimization model. Our model incorporates a refined latency model and employs the Poisson process to accurately quantify the probability of failure. By adopting this comprehensive approach, we provide a robust and efficient solution to the container migration problem in the industrial Internet. The established model offers a systematic framework that balances the trade-off between latency reduction and reliability enhancement, ultimately improving the overall performance and effectiveness. To address the migration strategy derived from the established model, we propose a migration algorithm based on the improved binary whale optimization algorithm. Our proposed algorithm incorporates the adaptive probability and adaptive position weight within the hunting and searching operations, effectively enhancing the search efficiency during the solving process. The experiments conducted in this paper validate the effectiveness of the established model by demonstrating consistent evaluation results that align with the expected outcomes. The experimental findings substantiate the superior performance of our migration algorithm compared to existing algorithms. In the future, we will investigate the container migration problem coupled with path planning for mobile industrial terminals. In some scenarios, where only the starting point and destination of the mobile industrial terminals are provided, their movement paths are not predetermined. In such cases, it is possible to integrate the path planning for mobile industrial terminals with the container migration decision-making process for joint optimization. Our plan involves establishing a joint model that simultaneously optimizes terminal paths and container migration. Additionally, we will design a parallel algorithm to solve the optimal path and migration strategy.
Data availability
The datasets used and/or analyzed during the current study available from the corresponding author on reasonable request.
References
Soori, M., Arezoo, B. & Dastres, R. Internet of things for smart factories in industry 4.0, a review. Internet of Things and Cyber-Physical Syst. 3, 192–204, https://doi.org/10.1016/j.iotcps.2023.04.006 (2023).
Kumar, D., Singh, R. K., Mishra, R. & Vlachos, I. Big data analytics in supply chain decarbonisation: A systematic literature review and future research directions. Int. J. Prod. Res. 62, 1489–1509. https://doi.org/10.1080/00207543.2023.2179346 (2024).
Soori, M., Dastres, R., Arezoo, B. & Jough, F. K. G. Intelligent robotic systems in industry 4.0: A review. J. Adv. Manuf. Sci. Technol. 4, 2024007, https://doi.org/10.51393/j.jamst.2024007 (2024).
Rao, K. S. et al. AI and ML in IR4.0: A short review of applications and challenges. Malays. J. Sci. Adv. Technol. 4, 141–148, https://doi.org/10.56532/mjsat.v4i2.291 (2024).
Jiang, H. Design and implementation of intelligent manufacturing system based on sensor networks and cloud computing technology. Opt. Quantum Electron. 56, 278. https://doi.org/10.1007/s11082-023-05923-1 (2024).
Jin, X., Hua, W., Wang, Z. & Chen, Y. A survey of research on computation offloading in mobile cloud computing. Wirel. Networks 28, 1563–1585. https://doi.org/10.1007/s11276-022-02920-2 (2022).
Sharma, M., Tomar, A. & Hazra, A. Edge computing for industry 5.0: Fundamental, applications and research challenges. IEEE Internet Things J. https://doi.org/10.1109/JIOT.2024.3359297 (Early Access) (2024).
Lins, R. G. & Givigi, S. N. Cooperative robotics and machine learning for smart manufacturing: Platform design and trends within the context of industrial internet of things. IEEE Access 9, 95444–95455. https://doi.org/10.1109/ACCESS.2021.3094374 (2021).
Liu, C., Su, Z., Xu, X. & Lu, Y. Service-oriented industrial internet of things gateway for cloud manufacturing. Robotics Comput. Manuf. 73, 102217. https://doi.org/10.1016/j.rcim.2021.102217 (2022).
Zhao, Y., Hu, N., Zhao, Y. & Zhu, Z. A secure and flexible edge computing scheme for AI-driven industrial IoT. Clust. Comput. 26, 283–301. https://doi.org/10.1007/s10586-021-03400-6 (2023).
Dogani, J., Namvar, R. & Khunjush, F. Auto-scaling techniques in container-based cloud and edge/fog computing: Taxonomy and survey. Comput. Commun. 209, 120–150. https://doi.org/10.1016/j.comcom.2023.06.010 (2023).
Oleghe, O. Container placement and migration in edge computing: concept and scheduling models. IEEE Access 9, 68028–68043. https://doi.org/10.1109/ACCESS.2021.3077550 (2021).
Wang, S., Xu, J., Zhang, N. & Liu, Y. A survey on service migration in mobile edge computing. IEEE Access 23511–23528, https://doi.org/10.1109/ACCESS.2018.2828102 (2018).
Martin, J. P., Kandasamy, A. & Chandrasekaran, K. Mobility aware autonomic approach for the migration of application modules in fog computing environment. J. Ambient Intell. Humaniz. Comput. 11, 5259–5278. https://doi.org/10.1007/s12652-020-01854-x (2020).
Machen, A., Wang, S., Leung, K. K., Ko, B. J. & Salonidis, T. Live service migration in mobile edge clouds. IEEE Wirel. Commun. 25, 140–147. https://doi.org/10.1109/MWC.2017.1700011 (2018).
Kim, T., Al-Tarazi, M., Lin, J. W. & Choi, W. Optimal container migration for mobile edge computing: Algorithm, system design and implementation. IEEE Access 9, 158074–158090. https://doi.org/10.1109/ACCESS.2021.3131643 (2021).
Yin, L., Li, P. & Luo, J. Smart contract service migration mechanism based on container in edge computing. J. Parallel Distributed Comput. 152, 157–166. https://doi.org/10.1016/j.jpdc.2021.02.023 (2021).
Zhang, W., Luo, J., Chen, L. & Liu, J. A trajectory prediction-based and dependency-aware container migration for mobile edge computing. IEEE Trans. Serv. Comput. 16, 3168–3181. https://doi.org/10.1109/TSC.2023.3290023 (2023).
Lou, J., Luo, H., Tang, Z., Jia, W. & Zhao, W. Efficient container assignment and layer sequencing in edge computing. IEEE Trans. Serv. Comput. 16, 1118–1131. https://doi.org/10.1109/TSC.2022.3159728 (2023).
Shao, S., Tian, S., Guo, S. & Qiu, X. Container-based internet of vehicles edge application migration mechanism. Comput. Mater. Continua 75, 4867, https://doi.org/10.32604/cmc.2023.038280 (2023).
Lin, X. et al. Container application migration algorithm in internet of vehicles. Intell. Autom. Soft Comput. 29, 915–926, https://doi.org/10.32604/iasc.2021.018513 (2021).
Tang, Z., Lou, J. & Jia, W. Layer dependency-aware learning scheduling algorithms for containers in mobile edge computing. IEEE Trans. Mobile Comput. 23, 3444–3459. https://doi.org/10.1109/TMC.2021.3139995 (2023).
Al-Tarawneh, M. A. B. Mobility-aware container migration in cloudlet-enabled IoT systems using integrated muticriteria decision making. Int. J. Adv. Comput. Sci. Appl. 11, 694–701, https://doi.org/10.14569/IJACSA.2020.0110983 (2020).
Aleyadeh, S., Moubayed, A., Heidari, P. & Shami, A. Optimal container migration/re-instantiation in hybrid computing environments. IEEE Open J. Commun. Soc. 3, 15–30. https://doi.org/10.1109/OJCOMS.2022.3140272 (2022).
Tang, Z. et al. Multi-user layer-aware online container migration in edge-assisted vehicular networks. IEEE/ACM Trans. Netw. 32, 1807–1822. https://doi.org/10.1109/TNET.2023.3330255 (2024).
Thongthavorn, W. & Rattanatamrong, P. Multi-container application migration with load balanced and adaptive parallel tcp. 2019 Int. Conf. High Perform. Comput. Simul. 55–62, https://doi.org/10.1109/HPCS48598.2019.9188218 (2019).
Temp, D. C., Souza, P. S. S., Lorenzon, A. F., Luizelli, M. C. & Rossi, F. D. Mobility-aware registry migration for containerized applications on edge computing infrastructures. J. Netw. Comput. Appl. 217, 103676. https://doi.org/10.1016/j.jnca.2023.103676(2023).
Xin, C., Yang, D., Ma, Z., Wang, Q. & Wang, Y. A load balancing container migration mechanism in the edge network. 10th Int. Conf. Comput. Eng. Netw. 1414—1422, https://doi.org/10.1007/978-981-15-8462-6_161 (2020).
Ma, Z., Shao, S., Guo, S., Wang, Z. & Xiong, A. Container migration mechanism for load balancing in edge network under power internet of things. IEEE Access 8, 118405–118416. https://doi.org/10.1109/ACCESS.2020.3004615 (2020).
Li, K., Chang, C., Yun, K. & Zhang, J. Research on container migration mechanism of power edge computing on load balancing. 6th IEEE Int. Conf. Cloud Comput. Big Data Anal. 386–390, https://doi.org/10.1109/ICCCBDA51879.2021.9442546 (2021).
Duan, J. et al. IEEE Int. Performance. Comput. Commun. Conf. 1–8, 2021. https://doi.org/10.1109/IPCCC51483.2021.9679421 (2021).
Baburao, D., Pavankumar, T. & Prabhu, C. S. R. Load balancing in the fog nodes using particle swarm optimization-based enhanced dynamic resource allocation method. Appl. Nanosci. 13, 1045–1054. https://doi.org/10.1007/s13204-021-01970-w (2023).
Patra, M. K., Misra, S., Sahoo, B. & Turuk, A. K. Gwo-based simulated annealing approach for load balancing in cloud for hosting container as a service. Appl. Sci. 12, 11115. https://doi.org/10.3390/app122111115 (2022).
Singh, A., Aujla, G. S. & Bali, R. S. Container-based load balancing for energy efficiency in software-defined edge computing environment. Sustain. Comput. Inform. Syst. 30, 100463. https://doi.org/10.1016/j.suscom.2020.100463 (2021).
Hadeed, W. & Abdullah, D. B. Load balancing mechanism for edge-cloud based priorities containers. Int. J. Wirel. Microw. Technol. 12, 1–9. https://doi.org/10.5815/ijwmt.2022.05.01 (2022).
Zhang, W., Chen, L., Luo, J. & Liu, J. A two-stage container management in the cloud for optimizing the load balancing and migration cost. Futur. Gener. Comput. Syst. 135, 303–314. https://doi.org/10.1016/j.future.2022.05.002 (2022).
Aslanpour, M., Toosi, A. N., Cheema, M. A., Chhetri, M. B. & Salehi, M. A. Load balancing for heterogeneous serverless edge computing: A performance-driven and empirical approach. Futur. Gener. Comput. Syst. 154, 266–280. https://doi.org/10.1016/j.future.2024.01.020 (2024).
Acknowledgements
This work was partly supported by the Scientific Research Program Funded by Education Department of Shaanxi Provincial Government (No. 23JP164), and the National Natural Science Foundation of China (No. 62301425).
Author information
Authors and Affiliations
Contributions
X.J. established the system model, X.J. and S.H. proposed the migration algorithm, X. J. and Y.C. conceived the experiments, S.H. conducted the experiments, X.J. and S.H. analysed the results. All authors reviewed the manuscript.
Corresponding author
Ethics declarations
Competing interests
Te authors declare no competing interests.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Jin, X., He, S. & Chen, Y. Container migration for edge computing in industrial Internet with joint latency reduction and reliability enhancement. Sci Rep 14, 25394 (2024). https://doi.org/10.1038/s41598-024-77086-2
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1038/s41598-024-77086-2
Keywords
This article is cited by
-
ATLAS: adaptive threat-learning algorithm for secure container migration in heterogeneous multi-cloud environments
Cluster Computing (2025)
-
FlexiMigrate: enhancing live container migration in heterogeneous computing environments
Cluster Computing (2025)