Abstract
Two fundamental prerequisites are needed for symmetric encryption techniques. Diffusion is the first of them. Confusion is the most significant and second factor. Substitution box (S-box) structure in these algorithms typically satisfies this condition. S-box architectures need to be robust as a result. The encryption procedure will therefore be hard to crack if the S-box is cryptographically sound. Getting a powerful S-box, however, is a challenging issue. Recent research has demonstrated that the security of a cryptosystem may be significantly improved by switching from static to dynamic S-boxes. Consequently, it is now essential to create new, secure S-boxes. In this paper, we proposed a practical method for generating dynamic S-boxes using a specific class of hyperelliptic curves defined over prime fields. The method involves selecting a large prime number and a random integer as parameters, iterating through candidate points on the curve, and applying a filtering condition to extract valid points. These points are then processed using a two-dimensional function and modular reduction to produce a list of unique values. If 256 unique values are obtained, they are reshaped into a \(16 \times 16\) S-box matrix. Computational results show that our approach can produce cryptographically robust S-boxes with a security level similar to certain existing S-boxes constructed using alternative mathematical structures. Compared to alternative solutions, our S-box exhibits exceptional non-linearity and resilience, effectively fending off both linear and differential assaults. The results of our investigation highlight how well this hyperelliptic curve-based S-box works to improve medical picture security.
Similar content being viewed by others
Introduction
The requirement for thorough multimedia security has become essential in the contemporary digital era. As multimedia content spreads across the digital world, it is increasingly important to ensure the confidentiality, integrity, and accessibility of these assets1. Multimedia data is crucial to our daily lives, our businesses, and society as a whole, from priceless family images kept in cloud services to sensitive corporate videos shared within networks2. It has never been more important to safeguard these digital valuables against illegal access, alteration, and harmful assaults. However, multimedia security presents a variety of difficulties. Large and varied multimedia files are frequently present, including high-resolution photos, lossless audio, and high-definition films. These data types need to be secured, which necessitates the use of powerful and adaptable cryptographic techniques. Furthermore, security measures must be both durable and flexible due to the expanding threat landscape of cyberattacks and the ongoing development of multimedia technologies3. The use of cryptographic methods is one of the pillars of multimedia security, and at the core of many encryption algorithms is a crucial element known as the substitution box, or S-box4,5. Based on a secret key, an S-box is a mathematical transformation that replaces input data elements with corresponding output data elements. With the addition of a non-linear layer, it is far more difficult for attackers to decrypt the original data without the right key. S-boxes are not only fundamental to encryption but also crucial for multimedia security. They are employed to secure multimedia content in various ways, including, Data Encryption, Watermarking, Steganography, Access Control, and Digital Rights Management (DRM).
The most often used strategies for enhancing information security are those based on elliptic curves. We will specifically focus on elliptic curve cryptography (ECC) and the many approaches proposed by many experts in this field. The elliptic curve was initially used as a public key cryptosystem in 1985 by Miller6. Additionally, it was shown that the ECC cryptosystem is twenty percent more effective than the Diffie–Hellman algorithm. Koblatiz et al.7 presented the concept of a discrete logarithmic issue which is applied to construct a highly secure, quick, and effective security system. An effective method to multiply the elliptic curve points and their resources is provided in8 and compared with binary and nonadjacent approaches. It has been found that ECC, which uses a shorter key length than RSA, is more secure overall. In9, an elliptic curve is used over a prime field to generate elliptic curve points, and then each point’s x and y coordinates are added. The modulo function is then used to construct various numbers of \(4\times 4\) S-boxes. A \(4\times 4\) S-box was developed in10 by using elliptic curves over \(GF(2^{4})\). Shah et al.11 used the Mordell elliptic curves over Galois fields with elements 256,512,2048. The authors in12 used a supersingular elliptic curve to design an \(8 \times 8\) S-box. The used y-coordinates of points (x, y) satisfying a specific supersingular elliptic curve. The authors in13 introduce a resource-efficient encryption scheme based on the Hyperelliptic Curve Cryptosystem (HECC) to address these challenges. The suggested method shows up to a 40% reduction in computing expenses and at least a 40% decrease in transmission overhead when compared to existing schemes, making it an attractive option for wireless data security. Vijayakumar et al.14 examined how well hyperelliptic curves of the genera 2, 3, 4 and 6 performed and contrasted their findings with ECC. Additionally, it provides a thorough analysis of the performance of HECC approaches across a wide range of applications. The authors in15 used a methodology based on HECC in protecting transmitted medical data and images. They demonstrate its effectiveness by successfully obfuscating medical transcription data of various sizes within sample photos while preserving high average PSNR values (55–70 dB), low average MAE values (0.2–0.7), and average values for SSIM, SC, and correlation coefficient of 0.1. The suggested method in16 makes use of Elgamal encryption, includes hyperelliptic curve cryptography for double-layer encryption, and uses fuzzy logic to choose integers that are crucial for determining cloud storage security. Hyperelliptic curve cryptography uses double-based ECC and point addition for key creation. MATLAB is used to validate this dual security model, evaluating its effectiveness in protecting data stored in the cloud as well as the consequences for cost and execution time. Results highlight how much better protection the two-layer security offers than what is now available. While secure communications and authentication are two areas where hyperelliptic curve cryptography has found use, its potential for multimedia security has yet to be fully realized. Only a small amount of research has looked at how hyperelliptic curves can be adjusted to the unique challenges given by multimedia data. In a world that is becoming more connected and data-driven, it seeks to offer insightful analysis and practical solutions for safeguarding multimedia assets. An effective method that makes use of Mobius transformation and Frobenius automorphism composition was given by Ali et al.17. They were able to obtain two very nonlinear permutations that have very high cryptographic strength and can generate millions of S-boxes. The suggested generator’s dynamic behavior is investigated by defining the conditions for generating separate S-boxes and verifying that the created S-boxes have a uniform probability distribution. The study18 proposes an approach for constructing substitution boxes (S-boxes) using a fractional-order (FO) 4D hyperchaotic system. The S-box is built up of permutation, exclusive-or (XOR) operations, and hyperchaotic sequences produced by the FO 4D hyperchaotic system. A robust medical picture encryption system19 is constructed using a fuzzy subset of integers ranging from 1 to 256 that is distinguished by membership values. A rigorous mathematical procedure is used to determine the S-box entries. To verify the newly developed S-box’s dependability and security, several conventional analyses are conducted. The suggested encryption method is also designed using this recently developed S-box. A comprehensive comparative analysis tailored to picture encryption techniques has been carried out to evaluate the algorithm’s performance. A new strategy for generating a strong initial S-box is suggested using the chaotic Rabinovich–Fabrikant fractional order (FO) system in20. The numerical results of the FO chaotic Rabinovich–Fabrikant system are produced to utilize the four-step Runge Kutta technique/Adams–Bashforth–Moulton method. A unique key-based permutation approach is also offered to improve the original S-box’s functioning and create the final S-box. The study21 presents a new approach that uses the night-tour algorithm, 2D Henon chaotic map permutation, and a suggested fractional-order (FO) 4D hyperchaotic system to encrypt grayscale pictures of any dimension. To increase the effectiveness of picture encryption, the suggested FO4D hyperchaotic system is used to produce chaotic sequences that are then used to reorder and scramble all of the image pixels. To create another layer of diffusion, 2D Henon chaotic Map permutation is employed. Additionally, to improve the resilience of the encryption, the Knight-tour technique is used by beginning at a selected point and performing a given round on the scrambled picture. This study22 proposes a new and secure picture encryption technique to guarantee the safe transmission of color images. It is based on the fractional-order (FO) 4D hyperchaotic system (4D-HCS) and Arnold Cat map (ACM). The suggested solution primarily relies on bit-wise XOR operations, substitution, permutation, and pixel rotation. Pixel rotation in a color picture using ACM removes significant correlations between adjacent pixels without obfuscating the information. After the red, green, and blue color channels have been separated, permutations can be added to increase confusion. FO 4D-HCS hyperchaotic sequences are utilized to dilute the color picture pixel values by replacement.
Razaq et al.23 introduced a novel method to S-box design based on a pair of coset graphs and a newly defined row and column vector operation on a square matrix. Based on a unique substitution-box generation algebraic approach that combined a large-order permutation group with a finite cyclic group, the authors24 suggested a revolutionary medical picture encryption algorithm. The suggested created S-box’s security performance is evaluated by analyzing and assessing several standard security metrics. The newly suggested medical picture encryption technique uses the created S-box, as well as bit-plane slicing, circular shifting, and XOR operations, to provide increased security and robustness while encrypting critical imaging data. The authors in25 presented a method for creating a high-quality quantum tent map using the generalized quantum dot system. To demonstrate its chaotic behavior concerning control settings and beginning circumstances, they initially presented a quantum tent map. Through time series analysis and the calculation of the Lyapunov exponent, they confirmed the existence of chaos. They then created a chaotic S-box using this new map. The authors next investigated the potential of producing strong S-boxes by combining two fractional stochastic models with three components of the suggested quantum tent map.
In this article, we used s special hyperelliptic curve over a prime field to design an S-box of good cryptographic strength as compared to S-boxes based on elliptic curves. To this day, no S-box on the hyperelliptic curve is available in the literature. We defined a function on points satisfying the hyperelliptic curves and found 256 unique values to design an S-box.
The rest of the article is divided into five sections. Section “2” deals with preliminaries. The proposed algorithm is described in Section “3”. Analysis of S-boxes has been made in Section “4”. We employed the proposed S-boxes in image encryption in Section “5”. Section “6” concludes the study.
Preliminaries
In this section, we will present some basic definitions related to Hyperelliptic curves.
Field extension
Let \(\mathbb {F}\) be any field and \(\mathbb {K}\) be its subset such that \(\mathbb {K}\) is also a field under the binary operations induced by \(\mathbb {F}\) then \(\mathbb {F}\) is called an extension field of \(\mathbb {K}\) and \(\mathbb {K}\) is called subfield of \(\mathbb {F}\)26.
Hyperelliptic curve
Let \(\mathbb {F}\) be a finite field, a hyperelliptic curve C of genus \((g\ge 1)\) over the \(\mathbb {F}\) is a set of all points (x, y) which satisfy the equation
where \(p(x) \in \mathbb {F}[x]\) is a polynomial of degree at most \(g, q(x)\in \mathbb {F}[x]\) is a monic polynomial of degree at most \(2g+1\)27.
The curve C is called non-singular if there are no points \((x,y)\in \mathbb {F} \times \mathbb {F}\) which satisfy both partial derivatives \(p'(x)y-q'(x)=0\) and \(2y+p(x)=0\).
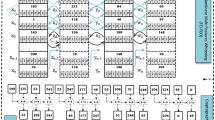
Proposed algorithm for designing S-boxes
In this section, we delve into a straightforward method for creating S-boxes with strong cryptographic properties. This construction approach relies on a hyperelliptic curve defined over a prime field \(\mathbb {F}_{p}\). The proposed algorithm consists of the following five steps
-
1.
Choose the curve \(C: u^2+vu=v^5+5v^4+6v^2+v+a\).
-
2.
Choose \(a \in \{1,2,3,\ldots ,p-1\}\) and a large prime p so that C has at least 256 distinct points.
-
3.
Define the following function on (v, u) points satisfying the curve C,
$$\begin{aligned} \psi (v,u)= {\left\{ \begin{array}{ll} u-a+v \pmod {p} & : v \le a\\ u+a \pmod {p} & : otherwise\\ \end{array}\right. } \end{aligned}$$ -
4.
Apply modulo 256 to reduce the outputs of \(\psi\) in the set \(\{0,1,2,\ldots ,255\}\).
-
5.
Choose first 256 unique values and reshape them as a \(16 \times 16\) matrix.
Algorithm for S-box generation using hyperelliptic curve.
For calculations, we choose \(p=4999, a=4019\) then the S-box \(\hbox{S}(4999,4019)\) is displayed in the Table 1.
Security analysis of S-box
In this section, security evaluations were carried out on the generated S-box to assess its resilience to cryptographic attacks. An S-box must meet the following requirements to ensure robust cryptographic resilience.
-
1.
Bijectiveness and balanacedness.
-
2.
Nonlinearity (NL).
-
3.
Strict avalanche criteria (SAC).
-
4.
Bit independence criteria (BIC).
-
5.
Differential uniformity (DU).
-
6.
Linear approximation (LAP).
Subsequently, the results of these evaluations were contrasted with those of frequently employed S-boxes to establish their efficacy.
Bijectiveness and balanacedness
An S-box must make sure that each input value is mapped to a single, distinct output value and that every output value is generated from a different input value to meet the requirements for bijectivity. The employment of the inverse of the S-box is necessary in cryptographic algorithms to facilitate the decryption process, highlighting the importance of a bijective S-box in such algorithms. Additionally, compared to their bijective counterparts, non-bijective S-boxes have worse cryptographic characteristics.
When the number of zeros and ones in a boolean function’s truth table is equal, the function is said to be balanced. A balanced S-box is one in which each of its constituent boolean functions demonstrates balance. An imbalanced S-box can compromise the security of cryptographic techniques as its output distribution is inclined towards specific bit values for certain or all of its input values. The proposed S-box S(4990, 4019) is balanced and bijective.
Nonlinearity (NL)
The degree to which an S-box deviates from a linear relationship between its input and output bits is referred to as nonlinearity. Simply put, you can’t anticipate the output bits of an S-box with any degree of accuracy by utilizing a simple linear combination of its input bits. In the world of cryptography, maintaining a high level of nonlinearity in an S-box is essential since it improves system security by preventing attacker efforts to infer input bits from output bits. Several statistical tests, including the correlation coefficient and Walsh transform, can be used to gauge the degree of nonlinearity.
Strict avalanche criteria (SAC)
The strict avalanche criterion, which mandates that each output bit changes with a probability of 0.5 when a single bit in the input is flipped, is necessary for an S-box to pass security requirements. In other words, it is anticipated that the S-box will exhibit maximum diffusion, which means that even a tiny change in the input will cause a substantial change in the output. In cryptography, the SAC property is crucial because it guarantees that even a small change in the S-box input will result in a significant change in the output. Because of this property, it is difficult for attackers to extract the original input data from the output.
Bit independence criteria (BIC)
According to the Bit Independence Criteria, the bits of the S-box input and output should be highly independent of one another. To put it another way, modifications to one input bit should not necessarily result in modifications to a particular output bit, and vice versa. The S-box’s security and confusion features are improved by the input and output bits’ absence of correlation or independence, which also increases its resistance to cryptanalysis.
Linear approximation probability (LAP)
The likelihood that an S-box may be approximated by a linear function is quantified by its Linear Approximation Probability (LAP). In plainer language, this metric assesses how much a binary vector that represents an S-box’s input and output are correlated.
One must examine all potential pairings of input and output vectors and count the number of pairs that meet a preset linear equation to compute the LAP of an S-box. The ratio of pairings that satisfy the linear equation and 0.5 is known as the LAP. Generally speaking, S-boxes with low LAP are thought to be more resistant to cryptographic attacks.
Differential approximation probability (DP)
The maximum frequency difference between two separate input differences that result in a particular output difference, across all feasible input differences, is referred to as the differential uniformity (DU) of an S-box. This metric assesses the biggest discrepancy between the probabilities of two input differences producing a specific output difference. Understanding the mechanics of differential attacks can be accomplished with the help of this characterization. Attackers look for input deviations that increase the likelihood of a specific output variation, and S-boxes with higher differential uniformity can fend off such strategies.
Fixed and reverse fixed points
The goal of an S-box is to prevent fixed points, which means that no input values will map to themselves throughout the transformation. Cryptographers depend on this work to assess the robustness and resilience of S-box-based cryptographic algorithms against various cryptographic attacks, which is crucial for comprehending the security features, shortcomings, and general effectiveness of these algorithms. The proposed S-box as listed in Table 2 has no fixed or reverse fixed point.
Image encryption
The utilization of the proposed S-box in the realm of encrypting medical images demonstrates a potential avenue for enhancing data security and privacy within healthcare systems. Strong protection against unauthorized access and online threats is required due to the delicate nature of medical images, which frequently contain sensitive patient information. When the innovative S-box is incorporated into encryption techniques, it offers a way to enhance the security of these priceless medical assets. The S-box enables the development of complicated encryption algorithms that thwart adversaries’ attempts to undermine the security of medical images by increasing the non-linearity and confusion aspects of encryption methods. In the constantly changing world of healthcare technology and information security, this novel technique has the potential to significantly protect patient privacy and guarantee the accuracy of medical data. We employed the CBC mode of AES to encrypt plain images with the proposed S-box. The corresponding images are displayed in Figs. 1, 2, 3, 4, 5, 6, 7 and 8. The Fig. 9 depicts the strength against salt and pepper noise with different intensity levels and Table 3 discusses the different tests for an image encryption.
Plain and cipher X-Ray image.
Plain and cipher ECG image.
Histograms of plain and cipher ECG image.
Histograms of plain and cipher X-Ray image.
Plain and cipher ultrasound image.
Histogram of plain and cipher ultrasound image.
Plain and cipher MRI image.
Histogram of plain and cipher MRI image.
Salt and pepper noise with 0.01 and 0.1 density.
Key sensitivity analysis
Keyspace analysis determines how many different keys may be created and used. For a brute-force assault to effectively decode data, an attacker must try a greater number of keys, hence a bigger key space is desirable. Brute force assaults include constantly trying each key until the correct one is identified. This improves the encryption method’s security since brute force assaults become more costly and time-consuming when the key space is expanded. The proposed scheme used a key of 256 bits and a random vector of 128 bits so the key space is \(2^{384} \gg 2^{100}\).
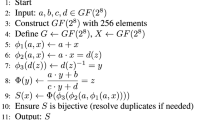
Image decryption algorithm.
Conclusion
We present a novel method for image encryption by building a robust S-box based on hyperelliptic curves in this article. Our in-depth examination highlights this method’s effectiveness in preventing various cryptographic assaults and assuring the safety of crucial medical images in healthcare applications. We have created a strong and effective encryption strategy by utilizing the special qualities of hyperelliptic curves, outperforming existing techniques in terms of both security and computational effectiveness. Our work helps to strengthen the security of healthcare information systems by maintaining the confidentiality and integrity of medical imagery. Protecting medical images is crucial because they house sensitive patient data. The results of our study show that hyperelliptic curve-based S-boxes have the potential to enhance the security of medical images. We believe that our findings present new opportunities for constructing S-boxes using advanced hyperelliptic curve techniques and secure image encryption. We are interested in exploring isogeny graph techniques for S-boxes and image encryption using hyperelliptic curves in the future. We strongly encourage further investigation into this approach within the domains of cryptography and health informatics.
Data availability
The datasets analyzed during the current study are available at https://www.kaggle.com/datasets/luffyluffyluffy/the-uscsipi-image-database/code.
References
Singh, M. & Singh, A. K. A comprehensive survey on encryption techniques for digital images. Multimed. Tools Appl. 82(8), 11155–11187 (2023).
Parvees, M. Y. M., Samath, J. A., Raj, I. K. & Bose, B. P. A colour byte scrambling technique for efficient image encryption based on combined chaotic map: Image encryption using combined chaotic map. In International Conference on Electrical, Electronics, and Optimization Techniques (ICEEOT), Chennai, India 1067–1072 (2016).
Kamal, S. T., Hosny, K. M., Elgindy, T. M., Darwish, M. M. & Fouda, M. M. A new image encryption algorithm for Grey and color medical images. IEEE Access 9, 37855–37865 (2021).
Ustun, D. & Sahinkaya, S. Design of secure S-Boxes via novel 2D-Zettle chaotic map and ABC algorithm for robust image encryption. Math. Comput. Simul. (2025).
Jamal, S. S., Ali, R., Jamil, M. K., Nooh, S. A. & Alblehai, F. Secure S-box construction with 1D chaotic maps and finite field theory for block cipher encryption. Alex. Eng. J. 125, 278–296 (2025).
Miller, V. S. Use of elliptic curves in cryptography. In Conference on the Theory and Application of Cryptographic Techniques 417–426 (Springer, Berlin, 1985).
Koblitz, N., Menezes, A. & Vanstone, S. The state of elliptic curve cryptography. Des. Codes Crypt. 19(2), 173–193 (2000).
Kodali, R. K., Patel, K. H. & Sarma, N. Energy efficient elliptic curve point multiplication for WSN applications. In National Conference on Communications (NCC) 1–5 (IEEE, IIT Delhi, 2013).
Khalid, I., Jamal, S. S., Shah, T., Shah, D. & Hazzazi, M. M. A novel scheme of image encryption based on elliptic curves isomorphism and substitution boxes. IEEE Access 9, 77798–77810 (2021).
Farwa, S., Sohail, A. & Muhammad, N. A novel application of elliptic curves in the dynamical components of block ciphers. Wirel. Pers. Commun. 115(2), 1309–1316 (2020).
Shah, T., Aljaedi, A., Hazzazi, M. M. & Alharbi, A. R. Design of nonlinear components over a Mordell elliptic curve on galois fields. Comput. Mater. Continua71(1), (2022).
Pali, I. A. et al. Construction of an s-box using suppersingular elliptic curve over finite field. J. Hunan Univ. Nat. Sci.50(7), (2023).
Choudary, S. A., Nasar, W. & Javaid, Q. Efficient signcryption schemes based on hyperelliptic curve cryptosystem. In 2011 7th International Conference on Emerging Technologies 1–4 (2011).
Vijayakumar, P., Vijayalakshmi, V. & Zayaraz, G. Comparative study of hyperelliptic curve cryptosystem over prime field and its survey. Int. J. Hybrid Inf. Technol. 7(1), 137–146 (2014).
Prasanalakshmi, B. et al. Improved authentication and computation of medical data transmission in the secure IoT using hyperelliptic curve cryptography. J. Supercomput. 78(1), 361–378 (2022).
Pandian, A. P. Development of secure cloud based storage using the Elgamal hyper elliptic curve cryptography with fuzzy logic based integer selection. J. Soft Comput. Paradigm 2(1), 24–35 (2020).
Ali, R., Ali, J., Ping, P. & Jamil, M. K. A novel S-box generator using Frobenius automorphism and its applications in image encryption. Nonlinear Dyn. 112(21), 19463–19486 (2024).
Ullah, S., Liu, X., Waheed, A. & Zhang, S. S-box using fractional-order 4D hyperchaotic system and its application to RSA cryptosystem-based color image encryption. Comput. Stand. Interfaces 103980 (2025).
Razaq, A., Maghrabi, L. A., Ahmad, M., Aslam, F. & Feng, W. Fuzzy logic-based substitution-box for robust medical image encryption in telemedicine. IEEE Access 12, 7584–7608 (2024).
Ullah, S., Liu, X., Waheed, A. & Zhang, S. An efficient construction of S-box based on the fractional-order Rabinovich–Fabrikant chaotic system. Integration 94, 102099 (2024).
Ullah, S., Liu, X., Waheed, A., Zhang, S. & Li, S. Novel grayscale image encryption based on 4D fractional-order hyperchaotic system, 2D Henon map and knight tour algorithm. Phys. Scr. 99(9), 095248 (2024).
Ullah, S., Liu, X., Waheed, A., & Zhang, S. Provably secure color image encryption algorithm based on FO 4D-HCS and ACM. Soft Comput. 1–18 (2024).
Razaq, A., Alhamzi, G., Abbas, S., Ahmad, M. & Razzaqu, A. Secure communication through reliable S-box design: A proposed approach using coset graphs and matrix operations. Heliyon 9(5), e15902 (2023).
Razaq, A., Maghrabi, L. A., Ahmad, M. & Naith, Q. H. Novel substitution-box generation using group theory for secure medical image encryption in E-healthcare. AIMS Math. 9(3), 6207–6237 (2024).
Hematpour, N., Gharari, F., Ors, B. & Yalcin, M. E. A novel S-box design based on quantum tent maps and fractional stochastic models with an application in image encryption. Soft. Comput. 28(7), 6235–6268 (2024).
Bailey, D. V. & Christof Paar, P. Efficient arithmetic in finite field extensions with application in elliptic curve cryptography. J. Cryptol. 14, 153–176 (2001).
Cohen, H., Frey, G., Avanzi, R., Doche, C., Lange, T., Nguyen, K. & Vercauteren, F. editors Handbook of Elliptic and Hyperelliptic Curve Cryptography (CRC Press, 2005).
Murtaza, G., Azam, N. A. & Hayat, U. Designing an efficient and highly dynamic substitution-box generator for block ciphers based on finite elliptic curves. Secur. Commun. Netw.2021, 3367521 (2021).
Razaq, A. et al. A novel construction of substitution box involving coset diagram and a bijective map. Secur. Commun. Netw. 48, 1–6 (2017).
Murtaza, G., Azam, N. A. & Hayat, U. Designing an efficient and highly dynamic substitution-box generator for block ciphers based on finite elliptic curves. Secur. Commun. Netw. 2021, 1–14 (2021).
Khan, M., Shah, T., Mahmood, H., Gondal, M. A. & Hussain, I. A novel technique for the construction of strong S-boxes based on chaotic Lorenz systems. Nonlinear Dyn. 70(3), 2303–2311 (2012).
Siddiqui, N., Naseer, A. & Ehatisham-ul-Haq, M. A novel scheme of substitution-box design based on modified Pascal’s triangle and elliptic curve. Wirel. Pers. Commun. 116(4), 3015–3030 (2021).
Shadab, M., Jawed, Md. S. & Sajid, M. Substitution box construction using transfer? Function assisted metaheuristic and booster algorithm: a hybrid approach. Secur. Priv. 8(1), e462 (2025).
Savadkouhi, M. B. & Tootkaboni, M. A. S-boxes design based on the Lu–Chen system and their application in image encryption. Soft Comput. 1–22 (2024).
Xi, J., Fan, C. & Yu, G. Design and implementation of dynamic s-boxes based on non-degenerate discrete chaotic systems. Phys. Scr. 99(11), 115222 (2024).
Zhao, M., Yuan, Z., Li, L., & Chen, X. B. A novel efficient S-box design algorithm based on a new chaotic map and permutation. Multimed. Tools Appl. 1–20 (2024).
Alali, A. S., Ali, R., Jamil, M. K., Ali, J. & Gulraiz, Dynamic S-box construction using Mordell elliptic curves over galois field and its applications in image encryption. Mathematics12(4), 587 (2024).
Akkasaligar, P. T. & Biradar, S. Selective medical image encryption using DNA cryptography. Inf. Secur. J. A Glob. Perspect. 29(2), 91–101 (2020).
Cao, W., Zhou, Y., Chen, C. P. & Xia, L. Medical image encryption using edge maps. Signal Process. 132, 96–109 (2017).
Kamal, S. T., Hosny, K. M., Elgindy, T. M., Darwish, M. M. & Fouda, M. M. A new image encryption algorithm for grey and color medical images. IEEE Access 9, 37855–37865 (2021).
Acknowledgements
The authors extend their appreciation to Princess Nourah Bint Abdulrahman University for funding this research under Researchers Supporting Project number (PNURSP2025R231), Princess Nourah Bint Abdulrahman University, Riyadh, Saudi Arabia.
Author information
Authors and Affiliations
Contributions
All authors contributed equally.
Corresponding author
Ethics declarations
Competing interests
There are no perceived biases due to personal affiliations among the authors.
Code availability
The code for algorithm of S-box generation can be accessed at https://github.com/Ali7409/Secure-Medical-Image-Encryption-with-Hyperelliptic-Curve-based-S-Boxes.git.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Alali, A.S., Ali, R., Jamil, M.K. et al. Secure medical image encryption with hyperelliptic curve based S-boxes. Sci Rep 15, 18179 (2025). https://doi.org/10.1038/s41598-025-02102-y
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1038/s41598-025-02102-y
Keywords
This article is cited by
-
Designing nonlinear component of block cipher over finite chain ring \(F_2\left[x\right]/\left\langle x^{10}\right\rangle\) and RGB image encryption
Multimedia Tools and Applications (2025)