Abstract
In joint operations, Command and Control (C2) Networks are crucial to operational effectiveness, directly impacting the coordination and efficiency of the operational system. As the interdependence between Information and Communication (IC) Networks and Command and Control (C2) Networks becomes increasingly tight, cascading failures have emerged as a significant factor affecting network reliability. This paper investigates the resilience of cascading failures in coupled dependency networks of command and control and Information and Communication (IC) Networks. It proposes an asymmetric group-dependency coupled network model and introduces four improved load redistribution strategies based on this model. To address the cascading failure issue caused by the one-way dependency between Command and Control (C2) Networks and Information and Communication (IC) Networks, the paper uses a nonlinear capacity-load model to simulate the cascading failure process of the coupled network and conducts simulation experiments under different attack modes and parameters to comprehensively evaluate the resilience of the coupled network. The results show that the four proposed load redistribution strategies effectively enhance the resilience of the coupled network under various attack modes and intensities. In particular, the comprehensive redistribution strategy (CR) demonstrates higher robustness and resilience across multiple scenarios. Additionally, the study reveals that simply increasing the node load capacity and repair capability does not always lead to improved resilience performance for the coupled network. Experimental results demonstrate that the proposed comprehensive redistribution strategy achieves 15-20% improvement in network resilience compared to traditional methods, with optimal performance observed at overload parameter \(\delta =0.6\) and recovery coefficient \(\eta =0.5\).
Similar content being viewed by others
Introduction
In recent years, with the development of information technology, the interdependence between networks has increased significantly, encompassing various aspects such as information, energy, resources, and services1. Different types of networks (e.g., communication, power, transportation) are interconnected, forming a complex system of interactions2. Coupled networks in real-world scenarios reflect the intricate interdependencies among infrastructures, such as power plants relying on water supply systems and water supply systems relying on power networks2. These network couplings increase the complexity and vulnerability of the system, where a failure on one network can trigger cascading failures on multiple networks3,4,5.
Studies have shown that due to coupling characteristics, networks become exceptionally fragile when exposed to random failures6. In such cases, even minor disruptions in one network can lead to cascading collapses across the entire system7. For example, in a system composed of coupled networks A and B, the failure of certain nodes in network A may disrupt the functionality of nodes in network B, and this disruption can be sent to network A, creating a cycle of failures that may result in the complete collapse of the coupled network. Ultimately, only the largest connected component of the surviving nodes continues to function. Recently, increasing attention has been paid to the robustness of coupled networks. Researchers have proposed various new models to enhance the robustness of coupled networks with functional impairments8.
As the core link in military command and decision-making systems, Command and Control (C2) Networks are closely integrated with information and communication networks, forming an interdependent network. The cascading failure process in interdependent networks differs significantly from that in single-layer networks: In interdependent networks, failures in one network layer can propagate to other layers through dependency relationships, leading to broader system failures9,10. Therefore, studying the cascading failure mechanisms of interdependent networks is critical to ensuring the stability and robustness of Command and Control (C2) Networks.
Although existing studies have provided some effective methods and approaches for analyzing the robustness of Command and Control (C2) Networks, certain limitations remain11,12,13,14. First, current research often views Command and Control (C2) Networks as isolated entities, lacking an analysis of their coupling with other networks (e.g., information and communication networks). Second, traditional studies primarily define the importance of nodes and cascading failure models based on network topology, failing to fully account for the heterogeneity of the nodes. Finally, Command and Control (C2) Networks possess unique hierarchical and specialized characteristics, and conventional evaluation metrics often fail to effectively capture their robustness features. These shortcomings limit a comprehensive understanding of cascading failure behavior in Command and Control (C2) Networks within complex interdependent environments.
In response, this chapter proposes a robustness research method for cascading failures in interdependent networks, with adaptive extensions tailored to the unique needs of Command and Control (C2) Networks. A model of an interdependent network with asymmetric group dependency between Command and Control (C2) Networks and Information and Communication (IC) Networks is constructed, considering the mutual dependencies and load distribution between the two networks. The main contributions of this paper are: 1. We propose an asymmetric group dependency model that addresses the limitation of existing one-to-one dependency models by incorporating realistic many-to-one dependencies with threshold-based failure criteria. 2. We develop four novel load redistribution strategies that consider both local node attributes (similarity, residual capacity) and global network properties (two-layer centrality), going beyond traditional weight-based redistribution. 3. We introduce a comprehensive redistribution strategy (CR) that dynamically combines multiple factors to optimize load distribution under various attack scenarios. 4. We provide extensive experimental validation showing 15–20% improvement in network resilience compared to existing baseline methods.”
Construction of the interdependent network model
The core components of the command and control (C2) network include intelligence sensing nodes, firepower strike nodes, and command control nodes. The C2 network is highly dependent on the support of the information and communication (IC) network, which provides the essential transmission infrastructure enabling the smooth flow of command and control messages and intelligence coordination information among core nodes such as sensing, strike, and control elements. This facilitates the transformation of information superiority into decision and action superiority. The robustness of the IC network directly affects the operational efficiency and combat effectiveness of the C2 network. As the fundamental infrastructure linking operational elements, the IC network is also responsible for information transmission and processing, ensuring continuity and interaction among all components in the operational network. With the support of the IC network, various functional combat units can respond rapidly and coordinate efficiently, thereby ensuring the overall effectiveness of joint operations.
To this end, this chapter constructs a coupled dependency network model, integrating the physical-layer Information and Communication (IC) Network and the logical-layer Command and Control (C2) Network. The IC network is composed of various communication technologies such as fiber optics, satellites, and shortwave radio, forming a multi-channel, redundant, and reconfigurable transmission infrastructure. At the logical layer, operational elements such as firepower strike, intelligence sensing, and command control are abstracted as nodes in the C2 network, where edges represent paths of information interaction, enabling complex command and decision-making processes. The coupling between the physical and logical layers is realized through the natural mapping between physical entities and corresponding C2 nodes, ensuring inter-layer influence and dynamic interaction.
By integrating the functions of both the physical and logical layers, this model enhances the coordination and interaction among operational elements, effectively capturing the complex structure and dynamic nature of modern warfare networks. The following sections provide a formal description of each network layer based on complex network theory. Information and Communication (IC) Network Definition. Assume the Information and Communication (IC) Network is denoted as \(G_W = (V, W_a, E)\), where the node set is defined as \(V = \{\nu _1, \nu _2, \cdots , \nu _{N_W}\}\), with \(\nu _i\) representing a communication node in the Information and Communication (IC) Network. \(N_W\) denotes the total number of nodes. The attribute set of the nodes is represented as \(W_a = \{(w_i \mid \nu _i)\}\), including each node’s initial load and carrying capacity. The edge set is defined as \(E = \{e_1, e_2, \cdots , e_{M_W}\}\), where \(e_i = \{(e_{jk} \mid \nu _j \times \nu _k)\}\) represents the communication relationships between different nodes, and \(M_W\) denotes the number of edges. The existence of edges is primarily determined by infrastructure deployment, hierarchical dependencies, and operational requirements. While generally stable, the network topology may vary dynamically during mission execution. The nodes of the Information and Communication (IC) Network are denoted as C-type nodes.
Command and Control (C2) Network Definition. In the command and control (C2) network, different types of nodes and their interrelations are abstracted as nodes and edges in a complex network. Specifically, the node set \(V_G = \{S, D, I\}\) represents three functional roles: S: Sensing nodes for intelligence acquisition,D: Command and decision-making nodes, I: Firepower strike nodes. The edge type set is defined as \(EG = \{(S-S, S-D, D-S, D-D, D-I)\}\), representing various interactions among different functional nodes. The C2 network exhibits heterogeneous components, multi-point interactions, multi-domain integration, and dynamic evolution characteristics, forming a complex and adaptive network structure suitable for modeling modern operational scenarios. In this model, edge attributes in the C2 network are not explicitly considered for simplification.
The Command and Control (C2) Network relies on the information and communication network to realize command and control functionalities. Although the acquisition and processing of intelligence information and commands are circulated within the command network, the actual exchange of information between nodes is conducted via the information and communication network nodes.
To establish the dependency relationship between the Command and Control (C2) Network and the information and communication network, the following assumptions are made:
-
1.
Each node in the operational network has a single dedicated function. Specifically, node C in the information and communication network can only perform information transmission; node S in the Command and Control (C2) Network is limited to information acquisition and intelligence processing; node D is responsible solely for issuing commands and making decisions; and node I is exclusively used for command and control attacks.
-
2.
Although the information and communication network is abstracted from physical devices, it is assumed that spatiotemporal constraints are ignored during communication tasks. Therefore, we do not consider how the Command and Control (C2) Network relies on the connectivity conditions of the information and communication network.
Based on the above assumptions, when the Command and Control (C2) Network depends on the information and communication network, we can construct an interdependent network model composed of both. The interdependent network is defined as follows:
Definition (interdependent network): Let the information and communication network be denoted as \(G_W\) and the corresponding Command and Control (C2) Network as \(G_G\). The coupling relationship between the two networks is represented by \(E_D = \{(E_{GW}, E_{WG})\}\), indicating that the Command and Control (C2) Network depends on the information and communication network.
If a dependency exists from node \(\nu _G^i\) to node \(\nu _W^j\), we define \(E_D(\nu _G^i, \nu _W^j) = 1\). For the sake of computational convenience, we also set \(E_D(\nu _W^j, \nu _G^i) = 1\). The set of dependent nodes and edges form a dependency network denoted as \(G_D\). The combined system, integrating all networks mentioned above, constitutes a two-layer interdependent Command and Control (C2) Network, represented as:
The adjacency matrix representation of the bi-layer interdependent operational network is:
where \(S_G\) represents the adjacency matrix of the Command and Control (C2) Network. Similarly, \(S_W\), \(S_{GW}\), and \(S_{WG}\) are the adjacency matrices of the Information and Communication (IC) Network and the interdependent network, respectively.
The dependency relationships in the interdependent network include various forms such as one-to-one, one-to-many, and many-to-one, which define the interaction patterns between the layers of the network. Among them, group dependency is a one-to-many relationship, where a key node supports the operation of multiple subordinate nodes, thereby enhancing the overall stability of the network.
According to the description in the definition of the bi-layer interdependent network, the constructed interdependent network model is shown in Fig. 1. In the Fig. 1, the Command and Control (C2) Network consists of nodes and edges, corresponding to the three types of command and control nodes, including \(S\), \(D\), and \(I\). The Information and Communication (IC) Network consists of information communication nodes, corresponding to different communication support units. Based on the dependency network, the Command and Control (C2) Network and the Information and Communication (IC) Network form an asymmetric coupling relationship.
The DGCN architecture diagram of CSOS.
The information flow model based on communication nodes is shown in Fig. 2. From the Fig. 2, it can be observed that the red solid lines represent the overall information flow of the command and control chain, while the gray dashed lines represent information transmitted through the Information and Communication (IC) Network. According to the dependency rules, the most typical command communication chain “S\(\rightarrow\)S\(\rightarrow\)D\(\rightarrow\)I” (the dynamic command control link follows the “intelligence acquisition \(\rightarrow\) intelligence processing \(\rightarrow\) command control \(\rightarrow\) fire strike” rule to form a kill chain) will transform into “S\(\rightarrow\)C\(\rightarrow\)S\(\rightarrow\)C\(\rightarrow\)D\(\rightarrow\)C\(\rightarrow\)I”, and other types of command control links can similarly be derived. Once the information communication nodes in Fig. 2 are damaged, the command control chain will be disrupted, and the command control network will lose its combat capability. Therefore, the coupling relationship between the command control network and the Information and Communication (IC) Network is more closely intertwined and crucial.
Information flow model based on communication nodes.
Our proposed model addresses the three identified limitations as follows:
-
Limitation 1 (isolation analysis): Our two-layer interdependent network model explicitly captures the coupling between C2 and IC networks, analyzing their mutual dependencies and cascading failure propagation.
-
Limitation 2 (topology-only focus): Our load redistribution strategies consider node heterogeneity through similarity measures, functional types, and residual capacities, not just topological properties.
-
Limitation 3 (inadequate metrics): Our resilience metric B considers both network layers simultaneously, providing a more comprehensive evaluation of C2 network robustness.
Two-layer interdependent network cascading failure model
The interdependent edges reflect the correlations between sub-networks in terms of material, energy, and information exchange. The more frequent the exchange, the greater the mutual influence between the networks. The strength of this mutual influence is called interdependency strength. Interdependency strength measures the closeness of the connection between inter-coupled nodes in two networks and also indicates the extent to which one network influences and controls the other.
Most common interdependent network models are based on a one-to-one dependency pattern, which lacks feedback characteristics. Many studies on the resilience of interdependent networks also rely on this pattern. However, in practice, such strict dependencies are rarely observed. The one-to-many dependency scenario, as mentioned earlier, is relatively common, also known as group dependence. If any of the dependent nodes (communication network nodes) fails, according to traditional analysis methods, the dependent nodes (Command and Control (C2) Network nodes) will also fail. As a result, attacking a small number of nodes can potentially lead to the collapse of the entire interdependent network. However, real-world networks are not as fragile. In the two-layer interdependent Command and Control (C2) Network, there are many alternative communication methods available within the Information and Communication (IC) Network. When the command network relies on the Information and Communication (IC) Network, as long as a certain proportion of the dependent nodes continue to function properly, the dependent command and control nodes will not fail. Based on the above analysis, this paper constructs a cascading failure model for Command and Control (C2) Networks based on asymmetric group dependency.
Asymmetric dependency failure
An asymmetric dependency network is a unidirectional dependent network structure in which the nodes of one subnet depend on the nodes of another subnet, but this dependency relationship is asymmetric. Therefore, the operation and stability of the network primarily depend on the state of the nodes in the dependency relationship, which makes the network exhibit specific vulnerabilities when certain nodes fail15. For the nodes that depend on other subnets, when all the dependent nodes fail or are no longer in the largest connected component, the node will fail, and its stability is entirely dependent on the state of the dependent nodes. For the nodes of the dependent subnet, when their connections to other nodes break and they are no longer in the largest connected component, the node will fail, affecting the stability of all the nodes and subnets that depend on it. The failure mechanism of asymmetric dependency networks highlights the importance of unidirectional dependency relationships for network stability. Failures may propagate along the dependency chain, triggering a broader network collapse. Therefore, in complex network design and management, particular attention should be given to the protection and redundancy of critical dependency nodes to enhance the robustness and anti-damage capability of the network16. Figure 3 illustrates the failure process of asymmetric dependency in the two-layer interdependent Command and Control (C2) Network.
Information flow model based on communication nodes.
The dependent Information and Communication (IC) Network node \(C_1\) (a C-type node in the IC network) is initially attacked and fails, leading to the removal of all edges connected to it. The failed node is marked in gray, and the disconnected edges are depicted using dashed lines, while the dependency relationships between networks remain represented by solid arrows.
In the second failure stage, two Command and Control (C2) Network nodes—\(D_2\) (a command node) and \(S_4\) (a sensing node)—which depend solely on \(C_1\), also fail due to the loss of their only supporting communication node. Following this, node \(I_5\) (a firepower strike node) also fails, as it no longer belongs to the largest connected component of the Command and Control (C2) Network.
In the third failure stage, the disconnection of edges between command and control nodes and the failed communication nodes \(C_1\) and \(C_3\) causes additional failures. Specifically, nodes \(D_4\) and \(I_6\) in the Command and Control (C2) Network—both of which were exclusively connected to \(C_1\) and \(C_3\), respectively—become isolated from the largest connected component and thus fail. However, node \(S_2\) remains functional because, despite the disruption of its connection to \(C_4\), it still maintains connectivity to the rest of the network through alternative paths.
This scenario illustrates the cascading nature of asymmetric dependency: failures in critical IC nodes can rapidly propagate to multiple dependent C2 nodes, especially when the dependency is one-to-many and there are no redundant communication paths.
Since no additional nodes meet the failure criteria, the failure process halts and reaches a stable state. The above example illustrates the fundamental process of failure propagation caused by node dependency. However, considering that in real-world scenarios, the dependency between the Command and Control (C2) Network and the Information and Communication (IC) Network is not strictly one-to-one but involves asymmetric dependencies, this chapter adopts an asymmetric group dependency approach to better reflect actual conditions when constructing an interdependent network model. The process of node failure under this model is introduced in detail below.
In Fig. 3, the nodes marked as \(G_i\) represent the largest connected component of surviving nodes in each network layer after cascading failures. When a node is no longer part of the largest connected component \(G_i\), it is considered functionally failed even if not directly attacked.
Asymmetric group dependency failure
There is a default rule for asymmetric dependency failure: as long as a node’s dependency relationship remains intact, dependency failure will not occur, as exemplified by node \(G_2\) in Fig. 3. Based on the above analysis, in Fig. 4, \(a\) and \(b\) are two nodes in Network A that depend on Network B. Solid lines represent edges that are still active, while dashed lines represent edges that are about to fail17.
Information flow model based on communication nodes.
As shown in Fig. 4, there exists a unidirectional asymmetric group dependency relationship between Network A and Network B, and the scale of the dependency can vary. If node \(v_x\) depends on \(n\) communication nodes, the capacity of node \(v_x\) is \(C_x\), and the capacity of the dependent nodes is \(C_x^i\). The communication connectivity index of node \(v_x\) is expressed as follows:
When the dependent information communication nodes fail, the summation elements in \(\zeta _x\) will decrease accordingly, while \(n\) will remain unchanged. If the upper limit of the communication connectivity index is set as \(\bar{\zeta }\), the normalized connectivity index is expressed as \(\tilde{\zeta } = \zeta / \bar{\zeta }\). In the asymmetric group dependency failure model, the communication connectivity index decreases as the dependent communication nodes are destroyed. When the index falls below the threshold \(\tau\) (default threshold \(\tau = 0.6\)), the Information and Communication (IC) Network can no longer ensure that the command and control nodes complete information flow. The threshold \(\tau =0.6\) follows the recommended threshold from existing literature15, which has been empirically validated for effective discrimination of dependency failures. Consequently, the Command and Control (C2) Network nodes will fail conditionally. For node \(a\) in Fig. 4, two-thirds of its dependent nodes remain intact, and its connectivity index satisfies \(\tilde{\zeta }_a > \tau\), so \(a\) remains functional. However, node \(b\) fails because only one-quarter of its dependent nodes remain, and its connectivity index satisfies \(\tilde{\zeta }_b < \tau\).
Overload failure model
In the cascading failure process of interdependent networks, in addition to the failures caused by inter-network dependencies, it is also necessary to consider failures induced by internal operational mechanisms within each layer. In the case of the information and communication network, each node has an inherent capacity limit. When the load on a node exceeds its maximum allowable capacity, the node may fail, thereby triggering cascading failures across the network. A similar phenomenon can occur in the Command and Control (C2) Network when service processing becomes overloaded.
The capacity-load model is particularly suitable for describing such scenarios. Based on this model, and taking into account the heterogeneity between the Command and Control (C2) Network and the information and communication network in the interdependent structure, we establish an overload-induced cascading failure model for each network layer. This model is further integrated with an asymmetric group dependency model to reflect realistic node-level interactions18.
The cascading failure process due to overload proceeds as follows: each node initially has a predefined load. When a node fails due to an attack or other causes, its load is redistributed to other nodes according to specified rules. The nodes receiving the redistributed load have a certain probability of failure depending on the new load level. If any of these nodes fail, another round of load redistribution and failure is triggered.
For the information and communication network, the redistributed load is spread among all nodes in the network. In contrast, in the Command and Control (C2) Network, the redistributed load is only assigned to nodes of the same functional type. This distinction reflects the structural and functional heterogeneity between the two layers and ensures the model’s alignment with operational constraints19,20.
Cascading failure process in two-layer interdependent networks
In interdependent networks, the importance of a single node should be comprehensively evaluated by considering its roles in multiple networks, its connectivity, and its impact on overall stability. In such networks, “global” nodes, due to their multiple interconnections, may exhibit high vulnerability, and their failure could trigger cascading failures across the networks.
To effectively manage interdependent networks, it is crucial to assess the role and vulnerability of nodes within multiple networks to prevent the potential spread of systemic damage. Based on this discussion, a reasonable approach is to consider the entire coupled system rather than focusing on just one network within it and to protect the nodes that significantly influence the entire coupled network. By simulating and analyzing the propagation process of cascading failures, the interdependent relationship between the Command and Control (C2) Network and the Information and Communication (IC) Network can be described in detail. This understanding helps to deeply analyze network vulnerabilities, optimize network design and operations, and develop more effective protection and recovery strategies.
In the interdependent network composed of the Command and Control (C2) Network and the Information and Communication (IC) Network, preventing and analyzing cascading failures is a key objective for ensuring network robustness. To achieve this, the cascading failure process within the network must be modeled in detail. This section provides a brief introduction to the modeling process for cascading failures in interdependent networks, including the necessary steps and methods.
Initial node load
In interdependent networks, node load refers to the volume of tasks carried by each node. Specifically, the initial load is defined as the amount of information a node needs to process in order to complete a specific task. This load directly affects the node’s functionality and operational state within the network. By defining the initial load of nodes, we can evaluate the workload they must handle under normal conditions, which in turn helps identify the overall load distribution and potential vulnerabilities in the network.
The initial load of a node is generally related to either local or global information volume. Node betweenness is a key metric for evaluating its importance in the entire network. A higher betweenness indicates that the node acts as a bridge on more shortest paths and therefore has greater influence and a higher initial load. Thus, a node’s load is determined not only by its own attributes, but also by its position and connectivity within the network structure.
The node weight reflects its processing capacity and resources in the local network, while the sum of the weights of its neighboring nodes represents the local information volume. A higher node weight implies stronger processing capabilities and therefore a need to handle more tasks and load. Similarly, the greater the sum of neighbor weights, the more important the node is in the network, and the higher its initial load should be.
The initial load of node i can be adjusted using parameters \(\alpha\) and \(\beta\) to flexibly reflect load distribution under different network conditions. The specific formula is as follows:
In the above expression, \(\alpha \ge 0\) and \(\beta > 0\) are parameters that control the initial load intensity. \(w_i\) represents the weight of node i, and \(M_i\) denotes the set of neighboring nodes of node i. By adjusting these parameters, one can separately control the impact of the node’s own weight and that of its neighbors on the initial load, helping to better simulate task allocation under different scenarios.
The betweenness \(B_i\) of node i is defined mathematically as:
here, \(g_{jk}\) represents the total number of shortest paths between nodes j and k, while \(g_{jk}(i)\) represents the number of those paths that pass through node i.
Node capacity
In interdependent networks, nodes with larger initial loads are generally more critical to the network. These nodes may undertake more tasks or engage in more interactions with other nodes during the processing of information and services. Consequently, these important nodes often have less residual capacity, as a significant portion of their resources is allocated to supporting the core functions of the network. The relationship between the initial load and capacity of these key nodes highlights their essential role in maintaining the overall functionality of the network.
In contrast, less important nodes usually have smaller loads and more idle capacity. These nodes play relatively minor roles in the network, handling fewer tasks and interactions, leading to lower utilization of their capacity. Due to their lighter loads, they offer greater redundancy and buffering capabilities, which can provide critical support and supplementary functions in certain scenarios.
To more accurately capture the complex relationship between a node’s importance and its load, this paper adopts a nonlinear model to define node capacity. This model incorporates the nonlinear relationship between node capacity and load, allowing for a more realistic representation of the dynamic characteristics of nodes under different conditions. Through this nonlinear modeling approach, the actual performance and functionality of nodes in interdependent networks can be better reflected. The definition of node capacity is as follows:
In this equation, \(C_i\) represents the capacity of node \(v_i\), where \(\lambda\) and \(\gamma\) are capacity adjustment parameters. These parameters allow the ratio between node capacity and initial load to be flexibly adjusted, with \(\lambda \in (0,1)\) and \(\gamma > 0\).
By introducing a nonlinear model to define node capacity, this approach provides a more comprehensive means of capturing the dynamic characteristics of node importance and residual capacity in interdependent networks. This model offers a more precise tool for analyzing and predicting the performance of networks under varying load and failure conditions. It supports more effective network optimization and management strategies, providing a solid theoretical foundation for enhancing the overall robustness and stability of the network.
Node state determination
In the interdependent network model, each node can exist in one of three states: “Overloaded,” “Failed,” and “Normal.” These states reflect the operational conditions of a node under varying load and failure scenarios. The “Normal” state indicates that the node is operating stably within its capacity range. The “Overloaded” state indicates that the node’s load has exceeded its capacity limit but remains within a manageable range. The “Failed” state signifies that the node can no longer operate normally and has completely lost its functionality.
The overload coefficient \(\delta \in (0,1)\) represents the node’s capacity to handle loads beyond its capacity, indicating the margin within which the node can still function after exceeding its capacity. The recovery factor \(\eta \in (0,1)\) reflects the node’s repairability, determining the probability of a node recovering from the failed state to the normal state. These two parameters play a critical role in the dynamic transitions of node states, simulating the node’s performance under overload conditions and the success rate of the recovery process.
The state of a node is dynamically determined based on its load \(L_i(t)\) and capacity \(C_i\):
-
1.
Normal State: If the node’s load \(L_i(t)\) does not exceed its capacity \(C_i\) (i.e., \(L_i(t) \le C_i\)), the node is in the “Normal” state.
-
2.
Overloaded State: If the node’s load exceeds its capacity but remains within its manageable range (i.e., \(C_i < L_i(t) \le (1+\delta )C_i\)), the node is in the “Overloaded” state. In this state, the node has a probability of failure, given by:
$$\begin{aligned} p_i = \frac{L_i(t) - C_i}{\delta C_i} \end{aligned}$$(7)where \(p_i\) denotes the probability of node failure, consistently used throughout the text.
If a random number \(r_1 \in [0,1]\) is less than or equal to \(p_i\), the node transitions to the “Failed” state.
-
3.
Failed State: If the node’s load \(L_i(t)\) exceeds its upper processing limit (i.e., \(L_i(t) > (1+\delta )C_i\)), the node enters the “Failed” state and can no longer fulfill its functions.
For nodes in the “Failed” state, a recovery mechanism is implemented during subsequent simulation experiments, allowing them to return to the “Normal” state through technical repairs. The recovery condition is that a random number \(r_2 \in [0,1]\) must be less than or equal to the recovery factor \(\eta\). This mechanism simulates the technical repair process and recovery success rate observed in real-world networks, providing the model with more realistic dynamic recovery capabilities.
By introducing the three node states (“Normal,” “Overloaded,” and “Failed”) and a dynamic determination mechanism, this study can more accurately simulate the behavior of nodes and their interdependencies in Command and Control (C2) Networks and Information and Communication (IC) Networks.
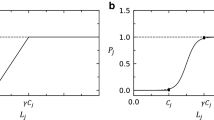
In summary, the transitions between different node states are illustrated in Fig. 5.
Information flow model based on communication nodes.
As shown in Fig. 5, normal nodes are vulnerable to external attacks or cascading effects, where increased load may cause them to become overloaded or fail, exposing the network’s fragility. Overloaded nodes can recover by redistributing their load to neighboring nodes; however, if neighboring nodes are unable to accommodate additional load, the overloaded nodes will still fail, highlighting the limitations of the network’s self-adjustment mechanisms. Failed nodes require technical means for recovery, which is time-consuming and dependent on resource allocation.
Overall, the dynamic changes in node states reflect the vulnerabilities and recovery capacities of coupled complex networks. This underscores the need for effective management of both self-repair and external recovery strategies.
Node load redistribution process
In complex networks, when a node fails, the task load it carried must be redistributed to maintain the stable operation of the overall system. This load redistribution process helps prevent widespread performance degradation or functional interruptions caused by the failure of a single node. In practical Command and Control (C2) Networks, this process of redistributing the load of failed nodes can be mapped to scenarios where a command and control node exceeds its capacity to manage simultaneous tasks, requiring some command tasks to be transferred to other related nodes. Similarly, it can also be mapped to intelligence processing nodes that face a surge in collaborative processing tasks due to emergencies, exceeding their own processing capabilities and necessitating collaboration with other processing nodes.
Load redistribution among nodes of the same type must adhere to specific rules, whereby load can only be shared among same-layer, same-type neighboring nodes. In Information and Communication (IC) Networks, this paper assumes that nodes are not categorized by type, and the load of a failed node can be directly transferred to neighboring nodes. In Command and Control (C2) Networks, however, load redistribution must prioritize the functional type of the nodes (e.g., reconnaissance intelligence, firepower strike) to ensure that the load is transferred to functional, non-failed neighboring nodes of the same type. This approach ensures the functionality and stability of the network.
Load redistribution strategy
In the load redistribution strategy, once a node is determined to have failed, its load is redistributed to non-failed neighboring nodes of the same type according to a specific strategy. The objective of the load redistribution strategy is to achieve a uniform distribution of load across the network by reasonably updating the load status of neighboring nodes. This helps prevent local nodes from becoming overloaded, thereby avoiding cascading failures.
Residual capacity coefficient of overloaded nodes
To more accurately describe the remaining load capacity of nodes after load redistribution, a residual capacity coefficient, denoted as\(\mu\), is introduced. This coefficient quantifies the remaining carrying capacity of an overloaded node after redistributing its load, satisfying the condition \(0< \mu < 1\). A reasonable setting of this coefficient can effectively enhance the network’s robustness and prevent nodes from continuous failure due to overload.
The residual load capacity of an overloaded node \(p_i\) is expressed as \(\mu C_i\), indicating the remaining load it can carry.
At time \(t\), the failed node \(p_i\) redistributes its load proportionally to neighboring non-failed nodes \(p_k\). The specific amount of load transferred is determined by the proportion \(\Pi _{i k}\).
here, \(\Pi _{ik}\) represents the proportion of load redistribution, which depends on the adopted load redistribution strategy and the carrying capacity of neighboring nodes.
Special cases in load redistribution
During the load redistribution process, there are two special cases:
-
1.
When \(\mu = 1\): The node only redistributes the excess load that exceeds its capacity, maintaining a normal state. This means the node can still handle the load within its capacity range.
-
2.
When \(\mu = 0\): The node redistributes all of its load, akin to the case of a failed node. This represents a special case of overload.
From the above analysis, it can be seen that in the design of Command and Control (C2) Networks, the robustness of the network can be effectively enhanced by properly designing and implementing node load allocation strategies. Specifically, a well-designed load distribution strategy can ensure that, in the event of node failure or overload, the excess load is reasonably redistributed to neighboring nodes. This helps maintain the normal functioning of the overloaded node while minimizing the risk of successive failures among its neighbors, thereby allowing the system to continue operating in a stable state.
Taking command and control nodes within the network as an example, this load redistribution strategy can be interpreted in real-world scenarios as a mechanism by which a command and control node, when facing a command task that exceeds its processing capacity, selects an appropriate collaborative processing method to ensure that command information continues to flow in an orderly and effective manner among various operational elements.
Node load redistribution strategy
Cascading failures in complex network systems refer to a phenomenon where the failure of local nodes or links triggers a chain reaction, resulting in significant degradation of network performance or even total network collapse. To effectively mitigate the spread of cascading failures, load redistribution strategies play a critical role in reallocating the load after node failures. Existing studies have proposed various load redistribution strategies, including average distribution, global distribution, and local preferential distribution, and have demonstrated that different strategies have a significant impact on network robustness. However, traditional redistribution strategies often overlook the heterogeneity of nodes in the network, failing to fully account for functional differences, structural characteristics, and the dynamic changes in node residual capacity during the cascading failure process. As a result, these strategies exhibit certain limitations in practical applications.
In current research on complex networks, one commonly used load redistribution strategy is the Weight Redistribution (WR)strategy. This strategy posits that when a node fails in the network, its neighboring nodes with higher weights will receive more of the failed node’s load. The WR strategy involves certain idealized assumptions during load redistribution, neglecting the functional and structural differences between nodes as well as the impact of their actual residual capacities. This disregard for heterogeneity often leads to an imbalance in load redistribution in dynamic network environments, exacerbating the propagation of cascading failures and significantly reducing overall network robustness.
When redistributing load, the amount should be adjusted based on the functional differences between nodes to avoid overburdening nodes with significantly different functions. Additionally, the actual residual capacity of nodes should be incorporated into the load redistribution strategy. Load redistribution strategies that consider residual capacity can effectively reduce the risk of overloaded node failures, thereby enhancing the network’s dynamic stability and robustness.
For the asymmetric interdependent network model constructed in this paper, four new load redistribution strategies are proposed to adapt to different network structures and failure scenarios. These strategies include:
Node Similarity Redistribution Strategy (considering local node attributes), Residual Capacity Redistribution Strategy (considering local node attributes), Double-Layer Centrality Redistribution Strategy (considering global node attributes), Integrated Redistribution Strategy(considering both local and global attributes).
Simulation experiments are conducted to evaluate the impact of these strategies on network robustness. The details of each strategy are elaborated in the following sections.
Node similarity redistribution strategy (SR)
The Node Similarity Redistribution Strategy (SR) is a load redistribution method that reallocates the load of failed nodes to their neighboring nodes based on the similarity between nodes. This strategy assumes that the weight of a node reflects its capacity, while the load represents the tasks it undertakes. The smaller the weight difference \(|w_i - w_k|\) between node \(p_i\) and its connected node \(p_k\), the higher their functional similarity. Therefore, when a node fails, the load is preferentially transferred to neighboring nodes with similar functionality to minimize the transfer loss caused by differences in performance and functionality.
The load redistribution proportion \(\Pi _{ik}^{SR}\) in the Node Similarity Redistribution Strategy is calculated as follows:
where \(\Gamma _i\) is the set of non-failed nodes of the same type that are connected to the failed node \(p_i\). This formula ensures that the load is preferentially distributed to similar nodes with smaller weight differences, thereby maintaining the local stability and continuity of the network.
By redistributing the load of failed nodes to nodes with similar functionality and capacity, the strategy reduces transfer losses caused by differences in performance and functionality, thus improving the local stability of the network. During local failures or attack events, the strategy effectively maintains business continuity among similar nodes, ensuring that local parts of the network can continue operating without significant impact. However, in cases of large-scale or global attacks, the Node Similarity Redistribution Strategy may lack flexibility and fail to effectively utilize all network resources to counter widespread failures. The local nature of this strategy limits its adaptability when facing large-scale failures.
In summary, the Node Similarity Redistribution Strategy enhances the local stability of the network by optimizing load transfers, making it suitable for addressing localized failures or small-scale attacks. However, when the network faces large-scale attacks, the global adaptability of this strategy is limited. Therefore, it needs to be combined with other load redistribution strategies to improve the overall robustness and resilience of the network.
Residual capacity redistribution strategy (SCR)
Residual capacity refers to the difference between a node’s capacity \(C_i(t)\) and its current load \(L_i(t)\) at any given time \(t\). It reflects the node’s ability to handle additional load and serves as a key metric for measuring the resources available when facing extra stress. The size of the residual capacity determines a node’s carrying ability during the load transfer or redistribution process. In cases of node failure or overload, residual capacity is used to redistribute the load to non-failed neighboring nodes of the same type. The redistribution proportion \(\Pi _{ik}^{SCR}\) for the Residual Capacity Redistribution Strategy is expressed as follows:
here, \(C_i(t)\) denotes the capacity of node \(i\) at time \(t\), and \(\Gamma _i\) represents the set of neighboring nodes of the same type that are connected to node \(i\) and have not failed. This formulation indicates that the load is preferentially allocated to nodes with larger residual capacities, in order to reduce the risk of cascading failures caused by overload.
The residual capacity allocation strategy distributes load based on the remaining processing capacity of nodes, effectively preventing the occurrence of new cascading failures. This strategy can dynamically adjust according to the real-time state of each node, enhancing the flexibility and adaptability of load redistribution. As a result, the network is better equipped to respond to unexpected events or localized failures.
Due to its localized nature, the residual capacity allocation strategy focuses primarily on the available capacity of neighboring nodes. However, this may lead to the neglect of the global network structure and other critical factors, potentially resulting in suboptimal global performance.
By dynamically adjusting load distribution in real time, the residual capacity allocation strategy can significantly enhance the robustness of the network and reduce the likelihood of cascading failures. Nevertheless, because it emphasizes local node conditions, it may, in certain scenarios, overlook structural optimization at the global level, thereby impacting overall network performance and stability.
Two-layer centrality-based allocation strategy (two layer local, TL)
The two-layer centrality-based allocation strategy (TL) optimizes node selection and load distribution by calculating the local centrality of nodes in a two-layer network, thereby improving the overall robustness and connectivity of the network.
The local centrality \(C_l(i)\) is used to measure a node’s influence within the network. It is determined primarily by its directly connected neighbors (direct neighbors) and secondary neighbors (near neighbors). The specific formula is as follows:
where \(m(u)\) represents the number of nodes whose shortest path to node \(i\) is less than 3, and \(\Phi _i\) and \(\Phi _j\) are the sets of neighbors of node \(i\) and its neighboring nodes, respectively. By calculating local centrality, critical nodes with higher influence in the two-layer network can be identified.
This strategy combines the Command and Control (C2) Network and the Information and Communication (IC) Network into a coupled system \(G=(G_G, G_D, G_W)\), which is further extended to \(G=(Z, (L_A, L_B, L_{AB}))\). The composite network \(Z\) consists of \(2N\) nodes, with the edges in the network divided into three parts: \(L_A\), representing the edges within the Command and Control (C2) Network; \(L_B\), representing the edges within the Information and Communication (IC) Network; and \(L_{AB}\), representing the coupling relationships between the Command and Control (C2) Network and the Information and Communication (IC) Network. This coupled network model allows for a better evaluation of the global importance of nodes.
In the two-layer network model, critical nodes with the highest association are identified and protected by searching the composite network \(Z\), thereby preventing their failure. The selection process considers not only the direct neighbors of the nodes but also the nodes connected to them in the other coupled network, comprehensively evaluating their influence and contribution to global connectivity.
When a node fails or its load needs to be redistributed, the load allocation ratio of node \(i\) is given by:
where \(c_k\) is the centrality of node \(k\), and \(\Gamma _i\) represents the set of active neighboring nodes directly connected to node \(i\). This formula ensures that the load is preferentially distributed to nodes with higher centrality, maintaining the global connectivity and stability of the network.
By utilizing centrality metrics of the two-layer network, critical nodes are prioritized during load distribution, ensuring the overall connectivity of the network. This strategy effectively protects core nodes against multi-node attacks, enhancing the network’s overall stability and resilience. However, the need for real-time calculation of two-layer centrality increases computational and communication overhead. If not effectively managed, the concentration of load on central nodes may lead to their overload, resulting in more severe network failures.
Comprehensive allocation strategy (CR)
The comprehensive allocation strategy (CR) is a hybrid approach that integrates multiple load distribution methods through weighted combination. Its goal is to optimize the load distribution process by considering the similarity, centrality, and residual capacity of nodes in the network comprehensively. This strategy combines the node similarity-based allocation strategy (SR), the residual capacity-based allocation strategy (SCR), and the two-layer centrality-based allocation strategy (TL) to create a more flexible and robust distribution method.
In the comprehensive allocation strategy, the load allocation ratio for each node is calculated using the following formula:
where \(\theta _1\), \(\theta _2\), and \(\theta _3\) are the mixing weights of each strategy, satisfying \(\theta _1 + \theta _2 + \theta _3 = 1\). The initial values of \(\theta\) are set to \(1/3\). By adjusting these weights, the comprehensive allocation strategy can flexibly combine the advantages of different strategies to achieve optimal load distribution.
The comprehensive allocation strategy integrates the strengths of various load distribution strategies, taking into account node similarity (SR), node centrality (TL), and node residual capacity (SCR). This approach ensures a more comprehensive and flexible load distribution process. By combining different strategies, the overall optimization capability is enhanced, enabling the network to exhibit higher robustness and survivability under various load and attack scenarios. This strategy can adapt dynamically to different attack patterns and network states, improving the network’s ability to cope with uncertain environments and dynamic changes.
However, the design and implementation of the comprehensive allocation strategy are complex, requiring precise adjustment of multiple parameters and coordination among strategies to ensure its effectiveness and stability. Overcoming these challenges, especially in the adjustment of weight parameters and strategy coordination, requires in-depth research and optimization.
By combining multiple load distribution methods, the comprehensive allocation strategy significantly improves the robustness and adaptability of Command and Control (C2) Networks and Information and Communication (IC) Networks. Nevertheless, its practical application must address the high complexity of design and implementation. Special attention is needed in optimizing weight parameter adjustment and strategy coordination to ensure its effectiveness and reliability in various environments.
Experimental analysis
Experimental parameter settings
The experiments are conducted with Command and Control (C2) Network size \(N_H=100\) nodes, Information and Communication (IC) Network size \(N_C=200\) nodes. Both networks are generated using the Barabási–Albert (BA) model. The node weights (\(w_i\)) are randomly assigned within the range of1,10 following uniform distribution. Each simulation scenario is repeated 300 times to ensure statistical robustness.
Experimental setup and metrics
In a joint operations confrontation environment, network attacks are generally classified into **random attacks** and **intentional attacks**. Random attacks involve randomly selecting several nodes to disable, whereas intentional attacks disable nodes in a specific order based on their importance. In the two-layer interdependent network composed of a Command and Control (C2) Network and an Information and Communication (IC) Network, different networks exhibit different attack patterns. For example, in different command and control phases, the adversary may target specific nodes in the Command and Control (C2) Network or randomly destroy nodes in the communication network. Based on the targets and intent of the attacks on the interdependent network, attack patterns can be categorized into the following four types:
-
1.
Random Attack of the Physical Network (RAP): Randomly select a proportion \(f\) of nodes in the Information and Communication (IC) Network for attack, rendering them inoperative.
-
2.
Intentional Attack of the Physical Network (IAP): Select a proportion \(f\) of nodes from the Information and Communication (IC) Network in descending order of degree and disable them through targeted attacks.
-
3.
Random Attack of the Command Network (RAC): Randomly select a proportion \(f\) of nodes from the Command and Control (C2) Network for attack, rendering them inoperative.
-
4.
Intentional Attack of the Command Network (IAC): Select a proportion \(f\) of nodes from the command network in descending order of degree and disable them through targeted attacks.
Different attack patterns may have varying impacts on the resilience of the network. Combining the asymmetric dependency failure model and the overload cascading failure model to analyze the failure process in two-layer interdependent networks reveals that random or intentional attacks on nodes in the Information and Communication (IC) Network invariably lead to failures in the command network. Therefore, the command network is more vulnerable. Any disruption within the network can result in severe consequences, including “failure, disconnection, and paralysis.”
Performance comparison of load redistribution strategies
The resilience of a Command and Control (C2) Network is generally defined as the system’s ability to maintain its original command functions, characteristics, and organizational structure under external disruptions. In this chapter, the resilience of two-layer interdependent networks refers to the system’s ability to sustain command and control performance after some nodes in the network fail. Due to the presence of a Command and Control (C2) Network within the two-layer interdependent network, performance evaluation becomes more realistic. Here, a resilience evaluation metric is defined as follows:
The ratio of remaining functional nodes is used to evaluate the survivability of the network. In this context, \(N_H\) and \(N_C\) represent the total number of nodes in the Command and Control (C2) Network and the information and communication network, respectively, while \(N_H^O\) and \(N_C^O\) denote the number of operational (non-failed) nodes in each network.
Using the ratio of remaining functional nodes to assess network survivability is of great significance. This metric directly reflects the functional integrity retained by the network after attacks or failures, and it measures the ability of the Command and Control (C2) Network to maintain information transmission and command chain coherence under disruption. It thereby demonstrates the network’s fault tolerance and robustness.
A high ratio of remaining functional nodes indicates that the network can tolerate partial node failures while maintaining continuity in critical operations. Since different types of attacks (e.g., random vs. targeted) impact the network differently, analyzing this ratio enables the evaluation of network survivability under various attack scenarios and supports the optimization of protection strategies.
Moreover, this metric is suitable for dynamic assessment, allowing commanders to monitor the network’s survivability in real time during operations and make timely decisions. Its simplicity and intuitiveness make it applicable to a wide range of network topologies, establishing it as an effective tool for evaluating the survivability of complex network structures.
By analyzing the ratio of remaining functional nodes, researchers can identify and prioritize the protection of critical nodes, thereby maximizing the network’s survivability and fault tolerance. This provides scientific guidance for the protection and design of Command and Control (C2) Networks.
Impact of attack patterns on network resilience
This study aims to investigate the survivability of two-layer interdependent networks by conducting simulation experiments based on Command and Control (C2) Networks. The objective is to analyze the performance of different network types within such a complex interdependent structure.
Following the interdependent Command and Control (C2) Network modeling method described above, we construct the network by first generating the Command and Control (C2) Network and the corresponding information and communication network, based on predefined network sizes and inter-node dependency relationships. Specifically, the scale of the Command and Control (C2) Network is set as \(N_H\), and that of the information and communication network as \(N_C\). By establishing dependency links between nodes in the two networks, an interdependent Command and Control (C2) Network is ultimately formed.
To reduce randomness in the experiments, each type of network is generated 300 times under given parameters. The simulation software used is Python, running on Windows 10, with hardware configured as Intel(R) Core(TM) i7-10750H CPU @ 2.60GHz.
Network scale validation: Additional validation experiments were conducted on networks of varying scales:
-
Small-scale: \(N_H=50, N_C=100\);
-
Medium-scale (baseline scenario): \(N_H=100, N_C=200\);
-
Large-scale: \(N_H=200, N_C=400\).
The results consistently show the proposed strategies perform effectively across all network sizes, with minor performance variations.
Resilience experiments under different attack patterns
Attacks on the Information and Communication (IC) Network
In this experiment, the resilience of the network under different attack intensities on the Information and Communication (IC) Network was analyzed, considering various load redistribution strategies. The simulation results are shown in the following Figures. In Fig. 6, the red curve (attack intensity \(P = 2\)) and the blue curve (attack intensity \(P = 6\)) represent the experimental outcomes. The results indicate that when the attack intensity is \(P = 2\), the performance of the Information and Communication (IC) Network significantly declines in the initial stage, but over time, the network gradually stabilizes. This phenomenon suggests that the network possesses some self-healing capability, with various load redistribution strategies helping the network progressively return to a relatively stable state. In particular, the four proposed improvement strategies all contribute to enhancing the network’s resilience, with the Comprehensive Redistribution Strategy (CR) showing the most significant effect. The CR strategy achieves the best performance because it comprehensively considers node betweenness changes, performance differences, and remaining capacity, making the load distribution more flexible and effective.
Network performance change curve under random attacks in information and communication networks.
However, as shown in Fig. 7, when the attack intensity increases to \(P = 6\), the decline in network performance becomes more pronounced. The experiment shows that at higher attack intensities, intentional attacks (targeting critical nodes) cause more severe damage than random attacks. This is because critical nodes often bear a large load, and once they fail, other nodes struggle to share the load, triggering large-scale cascading effects. In this case, intentional attacks almost cause the entire network to collapse, exposing the significant vulnerability of the network under high-intensity targeted attacks.
Network performance change curve under intentional attacks in information and communication networks.
The experimental results indicate that the Comprehensive Redistribution Strategy (CR) performs exceptionally well in improving the resilience of the Information and Communication (IC) Network, effectively reducing network performance loss under different attack conditions. However, intentional attacks cause more harm to the network than random attacks, especially under high attack intensities. Therefore, the study suggests that during wartime, securing key nodes in the Information and Communication (IC) Network is crucial. Based on the results from both random and intentional attacks, protecting sensitive information such as the locations and capacities of key nodes is vital. In network design and optimization, special attention should be given to the protection of critical nodes, ensuring emergency backups, and preparing and optimizing resilience and recovery resources to enhance the overall robustness and resilience of the network.
Attacks on the Command and Control (C2) Network
The attack intensity P is defined as the proportion of nodes initially attacked or disabled within the network. As shown in Fig. 8, in the case of random attacks on the Command and Control (C2) Network, the network performance change curves indicate that both the red curve (attack intensity \(P = 2\)) and the blue curve (attack intensity \(P = 6\)) demonstrate that the network performance quickly stabilizes after relatively few iterations. This is similar to the behavior of the physical layer network under random attacks, suggesting that the Command and Control (C2) Network can adapt and recover its performance relatively quickly when subjected to random attacks. In contrast, when the Command and Control (C2) Network experiences intentional attacks, the decline in network performance is much more significant. Figure 9 shows that intentional attacks (i.e., attacks targeting key nodes within the network) have a far greater impact on network performance than random attacks, highlighting the network’s high vulnerability under intentional attacks. The failure of critical nodes leads to a severe weakening of network connectivity and cascading failures, significantly degrading overall network performance.
Network performance change curve under random attacks in Command and Control (C2) Networks.
Network performance change curve under intentional attacks in Command and Control (C2) Networks.
Among all four load redistribution strategies, the Comprehensive Redistribution Strategy (CR) stands out with significant advantages, effectively enhancing the resilience of the Command and Control (C2) Network. This is because the CR strategy fully considers node similarity, centrality, and remaining capacity, enabling flexible adjustment of load distribution to cope with different types of attacks. However, even with the CR strategy in place, the network still exhibits a mix of robustness and vulnerability when facing intentional attacks, indicating that the network remains at significant risk under targeted attacks.
The Command and Control (C2) Network exhibits differentiated stability and resilience under different types of attacks. After random attacks, the network can quickly stabilize, but intentional attacks have a more significant impact on network performance, further emphasizing the need to focus on protecting critical nodes in the design and defense strategies to enhance the overall robustness and resilience of the network.
The attacks on the Information and Communication (IC) Network and the Command and Control (C2) Network are closely related in terms of network structure and functionality. The Information and Communication (IC) Network is primarily responsible for data transmission and sharing, while the Command and Control (C2) Network is the core platform for decision-making and command issuance. In actual combat, these two networks are often interdependent, with the Information and Communication (IC) Network ensuring data transmission for the Command and Control (C2) Network, while the Command and Control (C2) Network coordinates various operational units through the Information and Communication (IC) Network. Therefore, attacking either of these networks can indirectly affect the stability and operational effectiveness of the other network. This chapter investigates the different types of attacks on these two networks and reveals their robustness differences under various attack scenarios, as well as the impact of their coupling relationship on overall system stability.
Impact of different attack methods on network resilience: Random attacks cause less damage to the network compared to intentional attacks. Intentional attacks typically target critical nodes or links in the network, leading to cascading failures and their spread, which can deliver a fatal blow to the entire network. The performance of the Information and Communication (IC) Network and the Command and Control (C2) Network differs significantly when subjected to the same attack method. The Information and Communication (IC) Network demonstrates strong self-healing ability under random attacks but is prone to failure under intentional attacks; the Command and Control (C2) Network, on the other hand, can quickly recover and stabilize under random attacks but exhibits extreme vulnerability under intentional attacks.
Effectiveness of different load redistribution strategies on network recovery: The Comprehensive Redistribution Strategy (CR) demonstrates the best recovery performance across all attack scenarios. This strategy fully considers node betweenness, remaining capacity, and load distribution differences, enabling it to effectively mitigate the risks brought by cascading failures under various attack conditions, thus enhancing the overall resilience of the network.
Differences in resilience between single-layer networks and coupled networks: The performance of a single-layer network under attack is closely related to its topological structure. In contrast, a coupled network has a more complex chain reaction due to the interdependence between networks. Therefore, in coupled networks, cascading failures across networks are more likely under intentional attacks, posing a greater threat to the overall stability of the network.
By designing two typical scenarios—intentional attacks and random attacks—and implementing attacks on both the Information and Communication (IC) Network and the Command and Control (C2) Network, the experiment ensures the comprehensiveness of the scenarios and the objectivity of the results. The use of various load redistribution strategies for comparative analysis in different attack scenarios reveals the strengths and weaknesses of different strategies, providing multiple options for improving network resilience. Through the experiments on the four types of attacks, the study unveils the resilience performance of the Information and Communication (IC) Network and the Command and Control (C2) Network under various attack scenarios and their interrelationships. The experimental results indicate that intentional attacks pose a much greater threat to the network than random attacks, especially when precise strikes on critical nodes can trigger cascading failures throughout the entire network. Therefore, network design and defense strategies should prioritize the protection of critical nodes, comprehensively employing load redistribution and cross-network coordination strategies to enhance the overall robustness and resilience of the operational network.
Resilience experiment under different attack intensities
In this experiment, we fix the recovery coefficient \(\eta = 0.3\) and overload parameter \(\delta = 0.5\) to focus specifically on the impact of attack intensity P on network performance.
This experiment aims to further study the impact of different attack intensities on network performance, particularly how to assess the resilience and stability of the network under various attack intensities. The experiment simulates different levels of network attack scenarios by gradually increasing the attack intensity (P), observing the network’s response and performance changes under these attack conditions. The main output result of the experiment is the B-value of the network performance after it stabilizes. This value is used to measure the network’s stability and resilience under a specific attack intensity. The experimental results are visually presented in Figs. 10 and 11, illustrating the changes in network performance under different attack intensities and types.
Figure 10 shows the performance changes of the Information and Communication (IC) Network under different attack types and intensities. The red curve represents the network performance change under random attacks, and the blue curve represents the performance change under intentional attacks. As the attack intensity increases, the network shows a gradual linear performance decline under random attack conditions, indicating a certain level of resilience. However, under intentional attacks, when the attack intensity reaches a certain threshold, the network performance drops sharply, indicating that the network’s robustness is significantly reduced when critical nodes are targeted.
Impact of Attack intensity on network performance under different attack types.
Figure 11 displays the performance of the Command and Control (C2) Network under different attack types, similar to the Information and Communication (IC) Network’s situation. The network performance decline caused by random attacks is relatively slow and stable, while intentional attacks lead to a sharp drop in performance once a certain critical point is reached. However, intentional attacks cause far more damage to the Information and Communication (IC) Network than to the Command and Control (C2) Network, suggesting that the critical nodes in the Information and Communication (IC) Network play a more significant role in maintaining network stability.
Impact of attack intensity on command and control (C2) network performance.
Overall, among the four load redistribution strategies, the Comprehensive Redistribution Strategy (CR) performs the best, significantly improving the resilience of the Command and Control (C2) Network. This is because the CR strategy effectively combines factors such as node similarity, centrality, and remaining capacity, enabling the network to better adapt to various attack modes. However, even with the optimal strategy, the network still exhibits a mix of robustness and vulnerability when facing intentional attacks, highlighting the persistent threat posed by directed attacks to the network.
Figure 12 further validates the vulnerability of the Information and Communication (IC) Network when facing attacks. The experimental results show that the number of initial node failures in the Information and Communication (IC) Network caused by attacks is approximately 1.66 times that of the Command and Control (C2) Network. This indicates that the Information and Communication (IC) Network is more prone to cascading failures, especially as the attack intensity increases, with the number of failed nodes rising significantly.
Curve of the impact of overload parameter \(\delta\) on network performance under random attacks.
To better illustrate the network’s response to initial failures, we examine the average number of initially failed nodes across various attack scenarios in detail below.
Average Number of Initial Failed Nodes Under Different Attacks
Comprehensive analysis shows that, under a certain attack intensity, especially when intentional attacks exceed a certain threshold, network performance declines significantly, exposing the network’s high vulnerability to concentrated attacks. Attacks on the Information and Communication (IC) Network lead to more severe cascading failures. By adopting the Comprehensive Allocation Strategy (CR), the network’s resilience is significantly improved, demonstrating its superiority over other strategies in handling various attack scenarios.
Resilience experiments with different parameters
This experiment investigates the impact of network overload parameter \(\delta\) and recovery coefficient \(\eta\) on network resilience.
Variation of overload parameter \(\varvec{\delta }\)
First, the experiment analyzes the effect of the overload parameter \(\delta\) on network resilience. The overload parameter \(\delta\) reflects the tolerance of a node when handling additional load beyond its capacity. The results show that as \(\delta\) increases, the node’s tolerance to additional load improves, leading to a reduced failure probability and consequently enhancing the network’s resilience. Figures 13 and 14 demonstrate that as \(\delta\) increases, network resilience gradually improves under both random and intentional attacks, with a more pronounced effect under intentional attacks. However, when \(\delta \ge 0.7\), the improvement in network resilience levels off, indicating diminishing returns in parameter adjustment.
Curve of the impact of overload parameter \(\delta\) on network performance under intentional attacks.
Curve of the impact of overload parameter \(\delta\) on network performance under random attacks.
Variation of recovery coefficient \(\varvec{\eta }\)
Next, the experiment investigated the impact of the recovery coefficient \(\eta\) on network performance. The recovery coefficient \(\eta\) determines the ability of failed nodes to recover and return to normal operation. Figures 15 and 16 show that as \(\eta\) increases, the network’s resilience significantly improves under both random and intentional attacks, with the effect being particularly noticeable when \(\eta\) is higher. However, when \(\eta\) exceeds 0.6, the effect of further increasing its value diminishes. Relying solely on enhancing the recovery ability of nodes cannot continuously and effectively improve network resilience. While recovery ability can enhance network stability in the short term, without considering other important performance parameters and reasonable load redistribution strategies, the network may still fail under complex scenarios or high load pressure. Therefore, to achieve better resilience, node recovery ability must be combined with other key factors, such as optimizing node capacity configuration, improving load balance, and dynamically adjusting load redistribution strategies. Only through multi-faceted collaboration can the network’s robustness and stability be significantly improved when responding to cascading failures and other emergencies.
Curve of network performance changes under different attack intensities in Command and Control (C2) Networks.
Curve of network performance changes under different attack intensities in Information and Communication (IC) Networks.
Overall, the experimental results show that adjusting the overload parameter \(\delta\) and recovery coefficient \(\eta\) can improve network resilience to a certain extent, but their effects have limitations and specific applicability. In the face of large-scale attacks, especially intentional attacks on logical layer networks, relying solely on adjustments to \(\delta\) and \(\eta\) is limited and cannot fully prevent abrupt changes in network performance. Therefore, when optimizing network resilience, other factors and strategies must be comprehensively considered to address network challenges in complex attack scenarios.
Comparison with baseline methods
To further validate the effectiveness of the proposed Comprehensive Redistribution Strategy (CR), we conducted a comparative analysis with two baseline strategies: the traditional Weight Redistribution (WR) strategy and the Average Redistribution (AR) strategy. These baseline methods are widely used in network robustness studies but lack the ability to dynamically adapt to both local and global network attributes.
Table 1 summarizes the resilience performance (B-values) of different strategies under intentional attacks with varying attack intensities (\(P = 2\), \(4\), \(6\)). The results demonstrate that CR consistently outperforms WR and AR across all scenarios, achieving a 15%–20% average improvement in resilience.
These findings confirm that the CR strategy, which integrates node similarity, residual capacity, and two-layer centrality, delivers superior performance under targeted network disruptions. It effectively mitigates cascading failures and preserves functional connectivity more robustly than traditional methods.
Conclusion
This study aims to analyze the resilience characteristics of Command and Control (C2) Networks under different types of attacks, with a particular focus on how attack intensity and network parameters affect their stability and robustness. The research examines the specific vulnerabilities of these networks when exposed to random and intentional attacks and evaluates the effectiveness of different strategies in enhancing network resilience.
The study found that Command and Control (C2) Networks exhibit strong robustness when facing random attacks, maintaining overall stability. However, under intentional attacks, once the attack intensity exceeds a critical threshold, the network’s resilience rapidly declines, potentially leading to widespread collapse. The network’s defense capabilities against directed attacks are relatively weak, highlighting the importance of protecting critical nodes. Additionally, the Comprehensive Redistribution Strategy (CR) significantly enhances the network’s robustness and recovery ability compared to traditional strategies. Moderately increasing the overload parameter and recovery coefficient helps improve resilience, though their effects become less pronounced once they exceed certain thresholds.
This study provides valuable insights into the vulnerabilities and defense mechanisms of Command and Control (C2) Networks, particularly when responding to directed and random attacks. The proposed Comprehensive Redistribution Strategy (CR) effectively enhances the network’s stability and recovery ability, emphasizing the need for a balanced approach in improving resilience. This approach should combine factors such as node physical capacity, recovery abilities, and optimized load distribution. The findings provide a theoretical foundation for the design and protection of Command and Control (C2) Networks.
Despite the valuable insights provided by this research, there are some limitations. The study mainly focuses on specific attack scenarios and network parameters, which may not cover all potential threats faced by Command and Control (C2) Networks in real-world applications. Additionally, while the research analyzes the effectiveness of different strategies, it does not fully consider the influence of real-time environmental changes and network dynamics. Human factors, such as decision-making processes during attacks, are also not addressed in the study.
While this study provides valuable insights into C2 network resilience, several limitations should be acknowledged: 1. The model assumes idealized communication without considering real-world constraints such as bandwidth limitations and transmission delays. 2. Human factors in decision-making processes during attacks are not incorporated. 3. The study focuses on specific network topologies (BA model) and may not generalize to all real-world C2 networks.
Future research should address these limitations by incorporating more realistic operational constraints and exploring adaptive strategies for dynamic network environments.
Data availability
The original data and experimental results of this study are included in the supplementary files. For detailed data, please refer to the supplementary files section.
References
Martinez-Mares, A. & Fuerte-Esquivel, C. R. A unified gas and power flow analysis in natural gas and electricity coupled networks. IEEE Trans. Power Syst. 27, 2156–2166 (2012).
Liu, R.-R., Li, M. & Jia, C.-X. Cascading failures in coupled networks: The critical role of node-coupling strength across networks. Sci. Rep. 6, 1–6 (2016).
Qiao, Z. et al. An interval gas flow analysis in natural gas and electricity coupled networks considering the uncertainty of wind power. Appl. Energy 201, 343–353 (2017).
Zhang, L., Su, C., Jin, Y., Goh, M. & Wu, Z. Cross-network dissemination model of public opinion in coupled networks. Inform. Sci. 451, 240–252 (2018).
Gong, M., Ma, L., Cai, Q. & Jiao, L. Enhancing robustness of coupled networks under targeted recoveries. Sci. Rep. 5, 8439 (2015).
Li, T. et al. Evaluation and optimization of a command and control system based on complex networks theory. Electronics 12, 1180 (2023).
Valdez, L. D. et al. Cascading failures in complex networks. J. Complex Netw. 8, cnaa013 (2020).
Xing, L. Cascading failures in internet of things: Review and perspectives on reliability and resilience. IEEE Internet Things J. 8, 44–64 (2020).
Liu, N., Hu, X., Ma, L. & Yu, X. Vulnerability assessment for coupled network consisting of power grid and ev traffic network. IEEE Trans. Smart Grid 13, 589–598 (2021).
Wang, Y.-M., Chen, B., Chen, X.-S. & Gao, X.-E. Cascading failure model for command and control networks based on an m-order adjacency matrix. Mobile Inform. Syst. 2018, 6404136 (2018).
Zhao, B., Wang, M., Zhang, Q., Lin, W. & Zhou, D. Research on the robustness of command and control networks under cascading failures. Electronics 13, 3992 (2024).
Gao, X., Zhang, D., Li, K. & Chen, B. A cascading failure model for command and control networks with hierarchy structure. Security Commun. Netw. 2018, 6063837 (2018).
Cai, Y., Cao, Y., Li, Y., Huang, T. & Zhou, B. Cascading failure analysis considering interaction between power grids and communication networks. IEEE Trans. Smart Grid 7, 530–538 (2015).
Chen, B., Pang, G., Xiang, Z., Tao, H. & Chen, Y. Load allocation strategy for command and control networks based on interdependence strength. KSII Trans. Internet Inform. Syst. (TIIS) 17, 2419–2435 (2023).
Li, M., Liu, R.-R., Jia, C.-X. & Wang, B.-H. Cascading failures on networks with asymmetric dependence. Europhys. Lett. 108, 56002 (2014).
Liu, R.-R., Jia, C.-X. & Lai, Y.-C. Asymmetry in interdependence makes a multilayer system more robust against cascading failures. Phys. Rev. E 100, 052306 (2019).
Chen, M., Song, M., Zhang, M., Jin, L. & Gong, X. Cascading failure in multilayer network with asymmetric dependence group. Int. J. Modern Phys. C 30, 1950043 (2019).
Song, X., Zhang, S. & Shi, X. Measurement of network complexity and capability in command and control system. J. Stat. Comput. Simulat. 84, 1232–1248 (2014).
Khazaei, M. & Mozayani, N. A dynamic distributed overload control mechanism in sip networks with holonic multi-agent systems. Telecommun. Syst. 63, 437–455 (2016).
Matiuzzi Stocchero, J., Dexheimer Carneiro, A., Zacarias, I. & Pignaton de Freitas, E. Combining information centric and software defined networking to support command and control agility in military mobile networks. Peer-to-Peer Netw. Appl. 16, 765–784 (2023).
Acknowledgements
Acknowledgements should be brief, and should not include thanks to anonymous referees and editors, or effusive comments. Grant or contribution numbers may be acknowledged.
Author information
Authors and Affiliations
Contributions
B.Z. conceived and designed the experiments, providing the overall framework and research direction for the study. M.W. and W.L. conducted the experiments, including data collection, processing, and initial analysis. Q.Z.Z. contributed to the development of the methodology and assisted in refining the experimental design. W.L. and Q.Z.Z. performed detailed data analysis and interpreted the results in collaboration with B.Z. All authors contributed to the writing and editing of the manuscript, ensuring its scientific rigor and accuracy. Additionally, all authors reviewed and approved the final version of the manuscript.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Zhao, B., Wang, M., Lin, W. et al. Study on the resilience of command and control networks to cascading failures based on asymmetric group dependencies. Sci Rep 15, 29487 (2025). https://doi.org/10.1038/s41598-025-14921-0
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1038/s41598-025-14921-0