Abstract
Image encryption plays a vital role in protecting digital data from unauthorized access, cyber threats, and security breaches. With the continuous evolution of attack strategies, developing highly secure encryption mechanisms becomes essential. This paper presents a novel image encryption framework that integrates Cellular Automata (CA) with a chaotic map to enhance image confidentiality and integrity. The spatial complexity of 2-D CA strengthens the key generation process, ensuring a high degree of randomness in the key image. Subsequently, a 3-D coupled logistic map enhances chaotic behavior during encryption, increasing system complexity and security. To further ensure data integrity, Reed-Solomon codes are incorporated into both the key and the encrypted image, improving resilience against transmission errors. The proposed scheme undergoes rigorous evaluation through multiple analyses, achieving high entropy values nearing 7.9989, indicating enhanced encryption randomness. Additionally, it attains an average UACI of 36.9223 and an NPCR of 99.7887, demonstrating strong resistance against differential attacks. Furthermore, the model achieves an average MSE of 88.058 and a PSNR of 29.594 dB, ensuring high-quality image reconstruction. The encryption’s robustness is further confirmed through the NIST randomness test suite, where the model achieves an average p-value of 0.6771 across 15 tests, validating the statistical randomness of the generated cipher images. Moreover, the scheme exhibits strong resilience against noise attacks, confirming its practical applicability in noisy transmission environments. Collectively, these results demonstrate the robustness, effectiveness, and superiority of the proposed image encryption framework.
Similar content being viewed by others
Introduction
In the era of pervasive digital connectivity, image encryption has become a critical necessity for securing sensitive visual data against cyber threats, unauthorized access, and data breaches. Unlike text data, securing images requires specialized encryption techniques due to their high dimensionality, redundancy, and the need for real-time processing. With the increasing exchange of images in highly sensitive domains such as medical diagnostics, satellite imaging, industrial automation, and defense, ensuring their confidentiality and integrity is paramount. The widespread use of digital images in e-commerce, telemedicine, financial transactions, and cloud-based services further underscores the urgency of robust encryption mechanisms. While cryptographic techniques play a fundamental role in securing communication by transforming image data into an unreadable format, conventional encryption methods often struggle to counter evolving security threats1,2. To address these limitations, advanced image encryption techniques that integrate computational complexity and unpredictability have become indispensable, ensuring enhanced security and resistance against modern cyberattacks.
CA, initially conceptualized by John von Neumann and Stanislaw Ulam in the 1940s3,4, were developed as mathematical models to simulate biological self-replication5. Their theoretical foundation was further refined by Stephen Wolfram in the 1980s, who demonstrated their capability to generate complex computational patterns through simple rule-based transformations6,7. The 2-D CA has gained considerable attention in cryptographic applications due to its ability to generate intricate spatial structures and highly unpredictable sequences. A prominent example of 2-D CA is John Conway’s Game of Life8,9, which demonstrates its capability to produce dynamic and evolving patterns. The spatial complexity inherent in 2-D CA plays a crucial role in enhancing image encryption by ensuring effective pixel-level diffusion and confusion–both essential properties for strengthening resistance against statistical and differential attacks10. Furthermore, the parallel processing nature of CA enhances computational efficiency, making it well-suited for large-scale image encryption while maintaining a high degree of randomness and security. Due to these characteristics, CA-based encryption methods provide a strong framework for securing image data, ensuring confidentiality, integrity, and resilience against cryptographic attacks.
Chaos theory, particularly through chaotic maps, has emerged as a powerful tool in modern encryption techniques. Chaotic maps further strengthen cryptographic security by introducing extreme sensitivity to initial conditions, resulting in highly unpredictable sequences. Despite being governed by deterministic rules, chaotic systems exhibit non-linear behavior, which makes it highly suitable for encryption applications. The logistic map, a widely studied chaotic function, is particularly effective in generating pseudo-random sequences with strong cryptographic properties. When incorporated into the encryption process, it facilitates complex non-linear transformations of pixel values, significantly enhancing diffusion and confusion11,12. This integration improves the robustness of encryption schemes, ensuring strong resistance against various forms of cryptanalysis13. The combination of 2-D CA and chaotic maps leverages the strengths of both approaches, providing a highly secure and computationally efficient framework for image encryption. By utilizing chaos-based encryption, digital images can achieve high resistance to statistical and brute-force attacks, making such techniques highly suitable for modern security applications requiring unpredictability and robustness.
This research presents a novel encryption framework that combines the computational complexity of 2-D CA with the unpredictability of the chaotic logistic map to develop a dynamic and robust image encryption scheme. The proposed model enhances resistance to cryptographic attacks by leveraging the spatial complexity of CA and the inherent non-linearity of chaotic maps. To improve its transmission reliability, Reed-Solomon codes from forward error correction techniques are integrated, reinforcing resilience against transmission errors. The security and efficiency of the proposed model are rigorously evaluated through statistical analyses, including histogram and correlation analysis, alongside comprehensive security assessments such as randomness analysis, resistance to differential attacks, and pixel disparity evaluation. The empirical findings validate the robustness of the encryption model, highlighting its potential for secure image transmission in critical domains such as medical imaging, remote sensing, and secure multimedia communications.
The rest of this paper is structured as follows: “Survey of existing work” presents a review of related studies relevant to the proposed model. “Fundamental concepts of the proposed model” outlines the foundational concepts of the study. “Proposed methodology” details the proposed image encryption scheme, providing a comprehensive explanation of its methodology. “Results and discussion” assesses the scheme’s effectiveness through various analytical evaluations. Finally, “Conclusion” concludes the paper by summarizing key findings and suggesting potential future research directions.
Survey of existing work
The subsequent review presents developments in chaotic maps and CA for image encryption techniques.
In 2011, Fu et al.14 introduced a chaos-based bit-level permutation scheme that improved diffusion through a two-stage bit-level shuffling algorithm utilizing chaotic sequence sorting and the Arnold Cat map; however, its sensitivity to noise affected robustness. In 2012, Jin15 proposed an 8-length CA-based encryption scheme with periodic boundary conditions, offering computational efficiency but relying solely on correlation analysis, making it vulnerable to predictable attacks.
In 2017, Li et al.16 designed a secure method leveraging a 5-D multi-wing hyper-chaotic system for pixel and bit-level permutation and diffusion, though the reliance on hyper-chaotic systems introduced robustness challenges. The following year, Hongjun et al.17 proposed an adaptive double encryption scheme based on a chaotic system and SHA-512, utilizing chaotic sequences and S-Boxes to enhance security, yet remaining vulnerable to error and noise interference.
In 2019, Mondal et al.18 integrated a chaotic skew tent map and CA for secure image storage, using the tent map as an initial vector to generate pseudo-random numbers, but the complexity of key space management impacted efficiency. That same year, Wu C19 proposed an encryption technique leveraging RNA molecules and genetic codes to improve security and scalability.
In 2020, Nana and Wang20 introduced chaotic image encryption by combining extended zigzag confusion and RNA operations to enhance unpredictability, though high computational complexity limited its efficiency in time-sensitive scenarios. In 2021, Roy et al.10 developed a secure and efficient image encryption technique using 2-D CA, enhancing key space and demonstrating robustness through statistical evaluations, yet scalability challenges persisted with larger images.
In 2023, Alrubaie et al.21 devised a high-security encryption scheme integrating DNA encryption and chaotic maps, though efficiency issues arose with higher-dimensional images. Additionally, Lanhangli et al.22 proposed an innovative image encoding technique combining a chaotic map with CA to enhance sensitivity, strengthening security and robustness against attacks on original images. Following this, The evolution of chaos-based image encryption across symmetric and asymmetric schemes, including block and stream ciphers, is reviewed in12, and the study also highlights how chaos properties enhance encryption strength while outlining current challenges and future research prospects.
In 2024, Kumar and Revathi23 proposed an advanced encryption framework integrating deep neural networks with a memristor-based logistic chaotic map to enhance security performance. This approach demonstrated high NPCR, UACI, and entropy values, achieving strong encryption without compromising image quality. In the same year, Paolo and Nicola24 proposed a quantitative classification method for CA based on their surface growth behavior, identifying three main classes, namely saturating, indefinitely growing, and non-growing. This approach highlights the diverse growth dynamics that CA can exhibit.
In 2025, Bin et al.25 proposed an optimization framework for deep learning-based RDH predictors by incorporating local pixel complexity, introducing a multi-scale fusion-enhanced interpolation network, and adaptively determining optimal prediction coefficients by analyzing image texture features, achieving superior prediction accuracy and embedding performance.
This survey highlights the crucial role of chaos theory and cellular automata in enhancing security and randomness in cryptographic systems. However, existing research reveals critical gaps, including limited evaluations of randomness, insufficient security analyses, inadequate performance metrics, and a lack of multilayered encryption strategies. To address these challenges, this paper proposes a novel encryption framework that integrates the 2-D CA Moore neighborhood with a 3-D coupled logistic map, thereby enhancing cryptographic strength, unpredictability, and computational efficiency. Furthermore, by incorporating forward error correction block codes, the model effectively mitigates transmission errors, ensuring robust and reliable image security. This comprehensive approach enhances encryption resilience and establishes a higher benchmark for secure and efficient digital communication.
The key features of the proposed model are outlined below.
-
1.
The proposed model introduces an encryption scheme that leverages 2-D CA and 3-D logistic map to enhance image integrity and confidentiality.
-
2.
The 2-D CA Moore neighborhood facilitate efficient key generation and effective diffusion, to increase encryption strength.
-
3.
The integration of 3-D coupled logistic map adds extensive randomness and complexity to enhance the encryption process.
-
4.
Reed-Solomon codes are incorporated to resist transmission errors and maintain data integrity in unstable channels.
-
5.
Comprehensive analyses validate the scheme’s robustness and effectiveness in securing image data.
Fundamental concepts of the proposed model
This section delves into the concepts of CA, logistic map, and forward error correction in image encryption techniques.
Cellular automata
CA are discrete mathematical systems comprising a grid of cells, with each cell having a finite set of states. The evolution of the grid occurs in discrete time steps, governed by rules that update each cell’s state based on the states of its neighbors26.
Mathematically CA can be expressed by a five tuple \((L, Q, \text {N}, \delta , I_0)\) where
L is the regular lattice of cells; Q is the finite set of states; N is the finite set of neighborhood indices;
\(\delta\) is the transition function \(\delta :Q^n \rightarrow Q\), where \(n=|\text {N}|\); \(I_0\) is the initial state.
CA can be categorized by dimensions, 1-D (linear array), 2-D (grid), and 3-D (cubic lattice), which reflect the spatial configuration of cells and significantly impact the complexity and dynamics of the automaton, influencing a wide array of applications and behaviors. In the proposed scheme, 2-D CA is essential for key generation, leveraging its diffusion properties to enhance security and strengthen encryption against potential threats. Moreover, its spatial complexity ensures effective pixel-level confusion, further reinforcing encryption robustness.
Spatial configuration of neighbors in 2-D CA
The spatial configuration of 2-D CA is defined by a neighborhood structure, typically characterized by relative coordinates such as the Moore or Von Neumann neighborhoods, as shown in Figs. 1 and 2. This structure influences local interactions and pattern evolution during discrete time steps, significantly shaping the spatial relationships among neighboring cells. The Von Neumann neighborhood comprises the central cell and its four adjacent neighbors, excluding diagonals, while the Moore neighborhood encompasses nine cells, including the central cell and its eight surrounding neighbors5. Equations 1 and 2 define the Von Neumann \((N^{V})\) and Moore neighborhoods \((N^{M})\), respectively, while Figs. 1 and 2 illustrate them with a neighborhood radius \(N_r=1\). The neighborhood radius can be expanded by extending the surrounding cells.
where \((a_0, b_0)\) represents the coordinates of the central cell, while (a, b) denotes the coordinates of a neighboring cell. The parameter \(N_r\) defines the radius of the neighborhood, determining the extent of the surrounding cells included in the neighborhood structure24.
The 2-D CA employ these neighborhood configurations to govern state transitions through deterministic rules27. These structured interactions facilitate the generation of intricate patterns and high entropy, making them ideal for secure image encryption. By leveraging their inherent parallelism and sensitivity to initial conditions, 2-D CA enhance randomness and robustness, ensuring resilience against cryptographic attacks28. The proposed model utilizes the 2-D CA Moore neighborhood to generate a key image by transforming the pixel values of the original image. It considers a central pixel and its eight surrounding pixels to update the pixel values. Periodic boundary conditions ensure the seamless inclusion of edge pixels, allowing the Moore neighborhood to be consistently applied across the entire image. The pixel values are updated by summing the neighboring values and applying the modulo operation to ensure the pixel values remain within the valid range during key generation. This transformation introduces significant randomness, further strengthening the security of the encryption process while preserving computational efficiency.
Von neighborhood [\(N_r=1\)].
Moore neighborhood [\(N_r=1\)].
Logistic map
The logistic map is a fundamental chaotic system widely employed to enhance the complexity and security of cryptographic techniques29,30. It is expressed by the recursive equation.
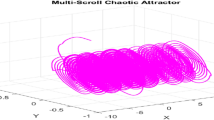
where \(a_n\) denotes the system’s state at iteration n, with \(a_n \in [0, 1]\), and r is the control parameter, typically within the range \(r \in [0, 4]\). The system exhibits bifurcation patterns characterized by distinct behaviors: fixed points occur for \(r \in (0, 3]\), periodic attractors emerge for \(r \in (3, 3.57]\), and chaotic behavior is observed for \(r > 3.57\)31. Figure 3 illustrates the bifurcation diagram of the logistic map, where \(r = 3.85\), and \(a_0 = 0.5\), with 1000 iterations, providing a visual representation of the system’s chaotic behavior.
Bifurcation diagram of 3-D coupled logistic map.
3-D coupled logistic map
The 3-D coupled logistic map extends the logistic map by incorporating three interdependent variables, leading to a more complex dynamical system
In this system, \(a_n\), \(b_n\), and \(c_n\) are the state variables, with r as the control parameter. The coupling of these variables enhances the complexity and chaotic behavior of the system. In the proposed model, \(r = 3.999\) is employed to optimize the chaotic dynamics during the encryption process. The values of \(a_n\), \(b_n\), and \(c_n\) are derived from the image size, further enhancing the chaotic dynamics during the encryption process and increasing the model’s complexity.
Forward error correction
Forward Error Correction (FEC) is a reliable error control technique that incorporates redundant error-correcting codes into transmitted data, enabling the receiver to detect and correct errors without requiring retransmission. This method improves data transmission reliability and maintains data integrity, particularly in error-prone environments32,33. FEC techniques are generally categorized into two types: Block Codes, which divide data into fixed-size blocks and add redundant bits for error correction, and Convolutional Codes, which encode data streams using memory-based methods.
In the proposed model, Reed-Solomon codes from block codes are applied to both the key image and the encrypted image to enhance their resilience against errors34. This ensures robustness during transmission or storage, protecting both images from potential corruption. Safeguarding the key image is particularly crucial, as any inaccuracies in the key could compromise the encryption and decryption processes, thereby undermining the system’s security. Therefore, the integration of Reed-Solomon codes fortifies the cryptographic scheme, maintaining the integrity and stability of both the key and encrypted images, even in the presence of errors. For instance, in the case of an RGB image, each pixel is represented by three color channels. In a \(256\times 256\) pixel image, each color channel contains 65,536 pixels, resulting in a total of 196,608 pixels across all three channels. The image is then divided into smaller blocks, each containing 255 bytes of data. Reed-Solomon encoding adds 32 redundant bytes to each block, enabling the system to detect and correct up to 16 byte errors per block, thereby ensuring the integrity of the image.
Proposed methodology
The proposed model introduces an innovative encryption scheme for encrypting images of any dimension. Initially, the sender generates the key image using the 2-D CA Moore neighborhood on the original image. This key image and the 3-D coupled logistic map are integrated into the encryption algorithm to induce chaotic behavior and enhance randomness. Reed-Solomon codes are also incorporated into both the key and encrypted images to improve resilience against transmission errors, ensuring integrity and confidentiality. Upon receiving the encrypted and key images, the recipient executes the reverse process to recover the original image. The subsequent sections provide an overview of key image generation, as well as the encryption and decryption processes. Figure 4 presents a graphical depiction of the proposed methodology.
Framework of the proposed image encryption scheme.
Key image generation process
The generation of the key image begins with an RGB image of dimensions \(M \times N\), followed by determining the number of iterations \(\texttt{i}\), which is based on the original image dimensions and ensures a minimum threshold of 10 iterations for sufficient diffusion. An empty key image is then initialized to store the final pixel values. Each pixel in the original image undergoes a transformation using a 2-D CA Moore neighborhood \(N^{M}\), facilitating diffusion across the image. This process is executed for \(\texttt{i}\) iterations to propagate pixel values and enhance randomness, ensuring that pixel relationships become increasingly complex and unpredictable. Throughout the iterations, pixel values are continually updated to optimize diffusion and increase the randomness of the generated key image, thereby enhancing its security by improving resistance to attacks. To further strengthen the resilience of the key image during transmission, Reed-Solomon codes are applied directly to blocks of the key image. This method introduces redundancy into the data, enabling the detection and correction of errors that may occur during transmission. By incorporating these codes, the key image becomes more robust, ensuring that the integrity of the data is maintained even if transmission errors occur, which ultimately increases the reliability and stability during the communication.
Image encryption process
The encryption process commences by considering both the original image and the key image, each of dimensions \(M \times N\). An XOR operation is applied to the corresponding pixels of OI and KI, resulting in an intermediate encrypted image \(\text {OI}'\), which diffuses the pixel values and enhances security. The rows of \(\text {OI}'\) are then rearranged by sorting the pixel values in ascending order, thereby reducing spatial correlation and generating the image \(\text {OI}''\). The 3-D coupled logistic map is initialized by averaging the corner pixel values of \(\text {OI}''\) to obtain \(a_0, b_0, \text {and} \ c_0,\) ensuring these values lie between 0 and 1, with a control parameter \(r = 3.999\) employed for the iteration process. The number of iterations \(\texttt{i}\), is dynamically determined based on the dimensions of OI, ensuring the encryption process is both adaptive and scalable. Using the 3-D coupled logistic map, the pixel values for each channel, represented by \(a_n\) for the red channel, \(b_n\) for the green channel, and \(c_n\) for the blue channel, are iteratively updated through non-linear transformations. After completing \(\texttt{i}\) iterations, the resulting values are rescaled to ensure they remain within the valid pixel range, producing the transformed image \(\text {OI}'''\). Finally, an XOR operation is performed between \(\text {OI}''\) and \(\text {OI}'''\) to generate the final encrypted image EI of dimension \(M \times N\), where each pixel thoroughly obfuscated to ensure secure encryption. Following this, similar to the key generation process, the reliability and integrity of the encrypted image are ensured through the incorporation of Reed-Solomon codes. These error-correcting codes effectively resist transmission errors, thereby enhancing the robustness and accuracy of the image during transmission.
Image decryption process
The decryption process is initiated upon receipt of the encrypted image and key image by the receiver. If transmission errors are detected, Reed-Solomon error-correcting codes embedded within both the encrypted and key images are employed to detect and correct any distortions, ensuring the integrity of the images. Following the error correction, the receiver extracts the initial values for the 3-D coupled logistic map from the corner pixels of EI. Specifically, the values \(a_0\), \(b_0\), and \(c_0\) are computed by averaging the corner pixel values of EI, ensuring each value is within the appropriate range. The number of iterations for the logistic map is determined dynamically based on the dimensions of EI. The receiver then executes \(\texttt{i}\) iterations of the 3-D coupled logistic map across the Red, Green, and Blue channels, to progressively update the pixel values. After completing the iterations, the resulting chaotic values are rescaled to ensure the pixel values remain within the valid range, yielding an intermediate image denoted as \(\text {OI}'''\). Then, an XOR operation is performed between \(\text {OI}'''\) and EI to generate the image \(\text {OI}''\). To further augment diffusion, the pixel values in each row of \(\text {OI}''\) are sorted, thereby generating the image \(\text {OI}'\). Finally, an XOR operation is performed between \(\text {OI}'\) and KI, thus restoring the original image. This process guarantees the accurate recovery of OI, even in the presence of transmission errors, due to the robust error correction facilitated by the Reed-Solomon codes.
Algorithms
Generation of key image.
Encryption of the data.
Decryption of the data.
Results and discussion
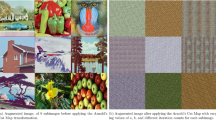
This section presents a series of rigorous experiments to evaluate and validate the effectiveness of the proposed model. Various RGB images of different dimensions, such as (a) Airplane, (b) Baboon, (c) House, (d) House1, and (e) Peppers, are sourced from the USC-SIPI Image Database35 and the University of Waterloo Image Repository36, are used for standard evaluations. Figures 5 and 6 showcase the original images processed in the proposed model, with their corresponding key, encrypted, and decrypted images.
Experimental results of various images using the proposed model.
Experimental results of the house1 image in the proposed model.
Processing time analysis
Computational efficiency constitutes a critical criterion for the practical applicability of encryption algorithms37. The proposed encryption framework was developed and executed in Python on a computational platform featuring an Intel Core i5 processor operating at 1.8 GHz, complemented by 16 GB of RAM, the Windows 11 operating system, and a 256 GB solid-state drive.
Table 1 delineates the average execution times for encryption and decryption processes applied to standard test images. The measured mean durations were 0.1745 seconds for encryption and 0.1801 seconds for decryption. These results substantiate that the proposed methodology delivers commendable computational performance, rendering it suitable for deployment in real-time environments and scenarios with constrained computational resources.
Statistical analysis
An optimal encryption technique must ensure resilience against statistical attacks, such as histogram and correlation coefficient analysis38.
Histogram analysis
A histogram is a graphical representation that illustrates the frequency distribution of pixel intensity values in an image. Examining the histogram of an encrypted image is crucial for evaluating the regularity of pixel distribution39. An ideal encryption technique produces a uniform histogram distribution, signifying effective obfuscation of the image content and enhancing security against statistical attacks. Figures 7, 8 and 9 display the histograms of the RGB color channels for the three distinct sets of original and encrypted images of the proposed model. It is evident that the histograms of the encrypted images produced by the proposed approach exhibit significantly smoother and flatter distributions, demonstrating the model’s effectiveness in achieving a uniform histogram and enhancing encryption robustness.
Correlation coefficient
Correlation quantifies the degree of resemblance between neighboring pixels, whether in a horizontal, vertical, and diagonal direction. A correlation coefficient close to 0 in a encrypted image signifies a substantial disparity between the original and encrypted images. Conversely, high correlation between neighboring pixels in any image facilitates known-plaintext attacks, making the encryption vulnerable40. Therefore, a proficient encryption algorithm must ensure minimal correlation between adjacent pixels in the encrypted image. Equation (3) is employed to precisely observe and determine the correlation coefficient of neighboring pixel values41.
Where \(C_{ij}\) represents the correlation coefficient, \(i_x\) and \(j_x\) represent the pixel values of two adjacent pixels, E(i) and E(j) denote the mean, D(i) and D(j) represent the variance, cov(i, j) represents the covariance, and S indicates total number of samples. To evaluate the correlation within the proposed model, 5000 pairs of adjacent pixels are randomly selected in each direction. Table 2 shows the average correlation coefficients of the proposed image encryption scheme, revealing a significant reduction in the correlation of adjacent pixels in the encrypted images, with values approaching zero. Similarly, Figs. 10, 11 and 12 illustrate the graphical representation of the correlation between adjacent pixels in all directions for both the original and encrypted images. These findings confirm that the proposed scheme effectively eliminates pixel correlations, thereby enhancing its robustness against statistical attacks.
Histograms of original and encrypted images of airplane and baboon.
Histograms of different channels of original and encrypted images of house and house1 using the proposed image encryption scheme.
Histograms of different channels of original and encrypted images of peppers using the proposed encryption scheme.
Correlation coefficient of original and encrypted images of airplane.
Correlation coefficient of original and encrypted images of baboon and house.
Correlation coefficient of original and encrypted images of house1 and peppers.
Information entropy analysis
Entropy quantifies the level of unpredictability and randomness of data, defined by the degree of uncertainty within a system42. The entropy of an image can be computed using Shannon’s entropy function. Consider s as the source of information, with its entropy determined using Eq. 4.
Where \(E_\text {s}\) represents the entropy of the source s, l denotes the total number of possible values for \(\text {s}_x\), and \(p(\text {s}_x)\) indicates the probability of occurrence of each \(\text {s}_x\). An entropy value close to 8 indicates a uniform pixel value distribution, signifying a robust cipher less susceptible to security breaches. The entropy of an image is directly correlated with its histogram, where flatter histograms correspond to higher entropies. Table 3 demonstrates the results of entropy analysis for the proposed model in comparison with existing methods. Evidently, the encrypted images generated by the proposed technique constantly exhibit entropy values nearing the ideal level 8, indicating uniformity and strong resistance to security attacks, thereby outperforming other models.
Differential attack analysis
Differential attacks emphasize that even slight modifications to the pixels of an original image should lead to substantial changes in the corresponding cipher image48. This resistance is evaluated using the NPCR and UACI indices, which provide both quantitative and qualitative assessments of the encrypted images, thereby determining their robustness against differential attacks. The NPCR and UACI can be obtained using Eqs. 5 and 6.
Where \(\text {EI}_1\) and \(\text {EI}'_1\) denote two distinct cipher images generated from an original image \(\text {OI}_1\), with \(\text {EI}'_1\) produced by modifying a single pixel in \(\text {OI}_1\). The value of D(i, j) is assigned as 1 if there is a difference between \(\text {EI}_1(i,j)\) and \(\text {EI}'_1(i,j)\), and 0 if they are identical. Table 4 and 5 displays the experimental outcomes for NPCR and UACI of the proposed model, demonstrating its superiority compared to existing techniques.
Pixel disparity analysis
Numerous techniques are employed to evaluate the relationship between plain and cipher images49. Among these, the PSNR and MSE are widely recognized as standard methods for assessing this relationship. These metrics, defined in Eqs. 7 and 8, provide quantitative insights into the alignment and differences between the two images.
Where, \(\text {OI}\) and \(\text {EI}\) denote the plain and cipher images, respectively, where (i, j) represents their index values. An effective encryption technique is expected to achieve a lower PSNR and a higher MSE. Table 6 and 7 summarizes the PSNR and MSE results for both the proposed and existing methods, highlighting the efficiency of the proposed model.
NIST SP 800-22 randomness test
The NIST SP 800-22 test suite comprises a rigorous set of 15 statistical tests designed to evaluate the randomness and unpredictability of binary sequences, which is a fundamental requirement for ensuring cryptographic security50. Each test produces a p-value within the range (0, 1), where a p-value exceeding the predefined significance level of 0.01 indicates that the sequence can be considered statistically random. In the context of image encryption, encrypted images are converted into binary streams to enable effective evaluation of their randomness and resistance to statistical analysis.
To validate the cryptographic robustness of the proposed encryption framework, the NIST SP 800-22 test suite was applied to encrypted outputs generated from five images (Airplane, House, House1, Baboon, and Peppers). The average p-values obtained across all 15 tests are presented in Table 8. These consistently high values confirm the model’s ability to produce highly unpredictable encrypted images, demonstrating strong resilience against statistical attacks and ensuring enhanced security.
Chi-square test
Chi-square (\(\chi ^2\)) is a statistical test employed in image encryption to evaluate the randomness and uniformity of encrypted images by comparing their histograms against the expected uniform distribution51. It quantitatively measures the deviation of the cipher image’s pixel value distribution from a uniform histogram, which is desirable for a secure encryption scheme. The \(\chi ^2\) statistic is computed as
where \(f_i\) denotes the histogram frequency at pixel intensity i, and \(M \times N\) represents the dimensions of the encrypted image. A low \(\chi ^2\) value close to zero indicates a uniform distribution, whereas higher values imply non-uniformity. The critical \(\chi ^2\) threshold depends on image size and degrees of freedom, with a significance level of 0.05.
The proposed encryption model was tested on five different images. Table 9 summarizes the computed \(\chi ^2\) values alongside their respective critical values. The results indicate that all computed values fall below their critical thresholds, demonstrating the model’s capability to produce encrypted images with statistically uniform histograms, thereby resisting histogram-based statistical attacks effectively.
Key space analysis
A robust encryption system requires a sufficiently large key space (KS) to ensure resilience against brute-force attacks52. In the proposed model, KS is determined by several independent factors, including the CA rule configurations, the number of iterations \(\texttt{i}\), the initial conditions derived from the original image, and the generated key image.
Specifically, the key space components are:
-
CA rule combinations: the 2-D CA using the Moore neighborhood offers 512 distinct rule configurations, contributing \(2^{512}\) possible combinations.
-
Iteration parameter: the number of iterations \(\texttt{i}\), computed based on the image dimensions, ranges between 10 and 255, adding approximately \(2^8\) possibilities.
-
Initial condition space: the system extracts initial conditions from the original image, contributing \(2^{M \times N \times 24}\) combinations, assuming 24-bit RGB depth.
-
Key image space: the final key image is an \(M \times N\) RGB image, where each pixel holds 24 bits (8 bits per channel), leading to \(2^{M \times N \times 24}\) combinations.
Thus, the overall key space KS can be expressed as:
For a typical \(256 \times 256\) image, this becomes:
This enormous KS far surpasses the cryptographic security benchmark of \(2^{100}\), providing strong protection against brute-force attacks. The integration of multiple chaotic parameters, pixel-derived conditions, and CA-based operations ensures the proposed encryption model delivers superior cryptographic strength.
Key sensitivity analysis
Key sensitivity is a critical security property of an encryption algorithm, reflecting the degree to which minor modifications in the secret key affect the encryption and decryption processes. An effective cryptosystem should exhibit extreme sensitivity such that even the slightest change in the key results in significantly different ciphertexts and prevents correct decryption.
In the proposed model, key sensitivity was evaluated by introducing minimal perturbations in the key parameters, such as altering the CA rule by a single unit or adjusting the initial conditions of the chaotic maps by \(10^{-15}\). The impact of these small changes was assessed by comparing the resulting encrypted images using statistical measures including correlation coefficients, NPCR, entropy, MSE, and PSNR.
The observed results demonstrate that minor key variations produce drastically different cipher images, with correlation coefficients near zero, NPCR values exceeding 99%, and entropy values close to the theoretical maximum, indicating high randomness and diffusion. Furthermore, attempts to decrypt ciphertexts with slightly altered keys failed to recover the original image, confirming the model’s robustness against key-related attacks. These findings substantiate the high key sensitivity of the proposed encryption scheme, a vital attribute for resisting brute-force and differential attacks.
Noise attack
To assess the robustness of the proposed encryption scheme against noise disturbances, additive white Gaussian noise (AWGN) was introduced to the encrypted Baboon image at varying intensities corresponding to signal-to-noise ratios (SNR) of 10 dB, 20 dB, and 30 dB. These noisy encrypted images were then decrypted to evaluate the scheme’s capability to accurately recover the original image despite noise corruption.
Figures 13a-13cillustrate the encrypted Baboon images affected by AWGN at SNR levels of 10 dB, 20 dB, and 30 dB, respectively. Figures 13d-13fpresent the corresponding decrypted images recovered using the proposed method without applying Reed-Solomon codes, and Figures 13g-13idisplay the decrypted images recovered using the proposed method with Reed-Solomon codes applied.
The experimental results demonstrate that the proposed approach, when combined with Reed-Solomon error correction, effectively withstands noise interference, maintaining image integrity and producing visually clear decrypted images even at lower SNR levels. The use of Reed-Solomon codes contributes to the recovery of corrupted data blocks, ensuring that errors introduced by the noisy channel do not propagate during decryption. This redundancy improves the reliability of the system, making it suitable for secure image transmission in noisy communication environments. Overall, these findings validate the proposed model’s robustness and practical applicability in real-world scenarios.
Encrypted and decrypted images under AWGN Noise at 10, 20 and 30 dB SNR.
Redundancy and overhead analysis
Beyond evaluating the error correction capabilities, the storage and transmission overhead introduced by the Reed-Solomon codes was examined. For a \(256 \times 256\) RGB image, where each pixel consists of three color channels, the total data size is 196,608 bytes. The image is segmented into blocks of 255 bytes, and each block is appended with 32 redundant bytes using the RS (255, 223) code, resulting in a redundancy ratio of approximately 14.1%. The Reed-Solomon code parameters (n, k) represent the total block length and the data length, respectively. Increasing the difference \(n-k\) enhances error correction strength but correspondingly increases the overhead.
In the proposed model, the selected parameters strike a well-balanced trade-off between robustness and efficiency, as demonstrated in the noise attack simulations presented earlier. Despite the added redundancy, the proposed method exhibits strong resilience against AWGN noise at varying SNR levels, validating both the theoretical and practical advantages of integrating Reed-Solomon coding within the encryption framework.
Resistance to attacks
The proposed encryption model demonstrates strong resistance to various cryptographic attacks by leveraging a large key space and high key sensitivity. Minor modifications in key parameters cause significant changes in ciphertext, preventing effective differential and related-key attacks. The combined use of CA, chaotic maps, and pixel-based key generation ensures a complex key structure that renders brute-force attacks infeasible.
Furthermore, the model’s multi-layered encryption strategy, including chaotic diffusion, pixel permutation, and XOR operations which effectively reduces statistical correlations, thereby resisting known-plaintext attacks. This is supported by experimental results showing low histogram correlation between plaintext and ciphertext, high entropy, and NPCR values exceeding 99%, indicating minimal statistical resemblance and strong diffusion. The integration of Reed-Solomon error-correcting codes enhances robustness against chosen-ciphertext attacks by detecting and correcting tampering or transmission errors, preserving data integrity and confidentiality under such attack scenarios.
Conclusion
This paper introduced an innovative image encryption scheme designed for images of arbitrary \(M \times N\) dimensions, leveraging the 2-D CA Moore neighborhood for key image generation and a 3-D coupled logistic map to enhance encryption through effective pixel scrambling. The incorporation of Reed-Solomon error correction codes enhanced the scheme’s resilience against noise and transmission errors. Extensive evaluations, including statistical, differential, and security analyses, validated the model’s superiority through various performance metrics such as entropy, correlation, differential analysis, and pixel disparity analysis. Additionally, NIST randomness tests confirmed the robustness of the encryption in generating truly random cipher images. The proposed method achieved a well-balanced trade-off between security and computational efficiency, demonstrating its suitability for secure image communication in practical and noisy environments. Future work will optimize computational efficiency for real-time encryption and extend support for multispectral and hyperspectral data using advanced processing techniques. Additionally, integration of quantum-resistant cryptographic primitives will be explored to address potential quantum computing threats.
Data availability
The datasets used and/or analyzed during the current study available from the corresponding author on reasonable request.
Change history
07 November 2025
The original online version of this Article was revised: In the original version of this Article author Venkatesan Ramasamy was incorrectly affiliated with ‘Department of Mathematics, Sri Sai Ram Engineering College, Sai Leo Nagar, West Tambaram, Chennai, Tamil Nadu, 600 044, India.’ Their correct affiliation is ‘Department of Mathematics, College of Engineering and Technology, SRM Institute of Science and Technology, Kattankulathur 603203, Tamil Nadu, India.’ The omitted affiliation has been added to the original version of this Article as Affiliation 2. As a result, the subsequent affiliations have been renumbered.
References
Kukaram, G. & Ramasamy, V. A novel approach of 1-D cellular automata in cryptosystem. Math. Model. Eng. Probl. 10(6), 2121–2126. https://doi.org/10.18280/mmep.100623 (2023).
Yasmin, A. & Venkatesan, R. An innovative RNA cryptosystem using moore machine. TWMS J. Appl. Eng. Math. 15(1), 242–255 (2025).
von Neumann, J. The Theory of Self-Reproducing Automata ( Burks, A.W. Ed.). 3–64 (University of Illinois Press, 1966).
Yasmin, A., Venkatesan, R. & Gaverchand, K. Enhancing the randomness of a symmetric cryptographic technique based on linear 1-D cellular automata. J. Discrete Math. Sci. Cryptogr. 28(1), 185–204. https://doi.org/10.47974/JDMSC-2133 (2025).
Gaverchand, K., Venkatesan, R. & Yasmin, A. Dual level strategy integrating 2-D CA and DCT technique for enhanced data protection. Math. Stat. 12(5), 428–442. https://doi.org/10.13189/ms.2024.120504 (2024).
Wolfram, S. Statistical Mechanics of Cellular Automata. Rev. Mod. Phys. 55(3), 601–644. https://doi.org/10.1103/RevModPhys.55.601 (1983).
Wolfram, S. Random sequence generation by cellular automata. Adv. Appl. Math. 7(2), 123–169. https://doi.org/10.1016/0196-8858(86)90028-X (1986).
Martin, Gardner & Games, Mathematical. The fantastic combinations of John Conway’s new solitaire game life. Sci. Am. 223, 120–123. https://doi.org/10.1038/scientificamerican1070-120 (1970).
Gardner, M. On cellular automata self-reproduction, the garden of Eden and the game of life. Sci. Am. 224, 112–117 (1971).
Roy, S. et al. IESCA: An efficient image encryption scheme using 2-D cellular automata. J. Inf. Secur. Appl. 61, 102919. https://doi.org/10.1016/j.jisa.2021.102919 (2021).
Li, L. et al. Image encryption using chaotic map and cellular automata. Multimed. Tools Appl. 81, 40755–40773. https://doi.org/10.1007/s11042-022-12621-9 (2022).
Zhang, B. & Liu, L. Chaos-based image encryption: Review. Appl. Challenges Math. 11(11), 2585. https://doi.org/10.3390/math11112585 (2023).
Kumar M. et al. Intertwining logistic map and cellular automata based color image encryption model. In 2016 International Conference on Computational Techniques in Information and Communication Technologies. 618-623 (2016). https://doi.org/10.1109/ICCTICT.2016.7514653.
Chong, Fu., Lin, Bin-bin, Miao, Yu.-sheng, Liu, Xiao & Chen, Jun-jie. A novel chaos-based bit-level permutation scheme for digital image encryption. Opt. Commun. 284(23), 5415–5423. https://doi.org/10.1016/j.optcom.2011.08.013 (2011).
Jin, J. An image encryption based on elementary cellular automata. Opt. Lasers Eng. 50(12), 1836–1843 (2012) (j.optlaseng.2012.06.002).
Li, Y., Wang, C. & Chen, H. A hyper-chaos-based image encryption algorithm using pixel-level permutation and bit-level permutation. Opt. Lasers Eng. 90, 238–246. https://doi.org/10.1016/j.optlaseng.2016.10.020 (2017).
Liu, Hongjun, Kadir, Abdurahman, Sun, Xiaobo & Li, Yanling. Chaos based adaptive double-image encryption scheme using hash function and S-boxes. Multimed. Tools Appl. 77, 1391–1407. https://doi.org/10.1007/s11042-016-4288-z (2018).
Mondal, B., Singh, S. & Kumar, P. A secure image encryption scheme based on cellular automata and chaotic skew tent map. J. Inf. Secur. Appl. 45, 117–130. https://doi.org/10.1016/j.jisa.2019.01.010 (2019).
Wu, C., Hu, K. Y., Wang, Y., Wang, J. & Wang, Q. H. Scalable asymmetric image encryption based on phase-truncation in cylindrical diffraction domain. Opt. Commun. 448, 26–32. https://doi.org/10.1016/j.optcom.2019.05.009 (2019).
Wang, X. & Guan, N. A novel chaotic image encryption algorithm based on extended Zigzag confusion and RNA operation. Opt. Laser Technol. 131, 106366. https://doi.org/10.1016/j.optlastec.2020.106366 (2020).
Alrubaie, A. H., Khodher, M. A. A. & Abdulameer, A. T. Image encryption based on 2DNA encoding and chaotic 2D logistic map. J. Eng. Appl. Sci. 70(60), 1–21. https://doi.org/10.1186/s44147-023-00228-2 (2023).
Lanhangli, L. et al. Image encryption using chaotic map and cellular automata. Multimed. Tools Appl 81(28), 40755–40773. https://doi.org/10.1007/s11042-022-12621-9 (2022).
Kumar, B. S. & Revathi, R. An efficient image encryption algorithm using a discrete memory-based logistic map with deep neural network. J. Eng. Appl. Sci. 71, 41. https://doi.org/10.1186/s44147-023-00349-8 (2024).
Lazzari, Paolo & Seriani, Nicola. Two-dimensional cellular automata-deterministic models of growth. Chaos Solit. Fract. 185, 114997. https://doi.org/10.1016/j.chaos.2024.114997 (2024).
Bin, Ma. H., Duan, R. & Ma, Y. High-performance optimization framework for reversible data hiding predictor. IEEE Signal Process. Lett. 32, 231–235. https://doi.org/10.1109/LSP.2024.3512357 (2025).
Ghosh M., Kumar R., Saha M. & Sikdar B.K., Cellular automata and its applications. In 2018 IEEE International Conference on Automatic Control and Intelligent Systems. 52–56 (2018). https://doi.org/10.1109/I2CACIS.2018.8603689.
Packard, N. H. & Wolfram, S. Two dimensional cellular automata. J. Stat. Phys. 38, 901–946. https://doi.org/10.1007/BF01010423 (1985).
Chen, R.-J. et al. Image encryption/decryption system using 2-D cellular automata. In 2006 IEEE International Symposium on Consumer Electronics. 1-6 (2006). https://doi.org/10.1109/ISCE.2006.1689421.
Alun Lloyd, L. The coupled logistic map: A simple model for the effects of spatial heterogeneity on population dynamics. J. Theor. Biol. 173(3), 217–230. https://doi.org/10.1006/jtbi.1995.0058 (1995).
Alawida, M. Enhancing logistic chaotic map for improved cryptographic security in random number generation. J. Inf. Secur. Appl. 80, 103685. https://doi.org/10.1016/j.jisa.2023.103685 (2024).
Tahmina, A.M. Observation of different behaviors of logistic map for different parameters. Int. J. Appl. Math. Theor. Phys.4, 2018. https://doi.org/10.11648/j.ijamtp.20180403.14 (2018).
Yuan Z. & Zhao X. Introduction of forward error correction and its application. In 2012 2nd International Conference on Consumer Electronics, Communications and Networks. 3288-3291 (2012). https://doi.org/10.1109/CECNet.2012.6201904.
Sathiya Narayanan, S. et al. Implementation of forward error correction for improved performance of free space optical communication channel in adverse atmospheric conditions. Results Opt.16, 100689. https://doi.org/10.1016/j.rio.2024.100689 (2024).
Reed I.S. & Chen X. Reed-solomon codes. In Error-Control Coding for Data Networks, The Springer International Series in Engineering and Computer Science. Vol. 508 (1999). https://doi.org/10.1007/978-1-4615-5005-1_6
The USC-SIPI Image Database. https://sipi.usc.edu/database/
Image Repository, University of Waterloo. https://links.uwaterloo.ca/Repository.html
Hanif, M. et al. A novel grayscale image encryption scheme based on the block-level swapping of pixels and the chaotic system. Sensors22(16), 6243 (2022). https://doi.org/10.3390/s22166243
Zhang, Y. Statistical test criteria for sensitivity indexes of image cryptosystems. Inf. Sci. 550, 313–328. https://doi.org/10.1016/j.ins.2020.10.026 (2021).
Omprakash, P., Parmeshwar, M. & Sanjeev, S. A comparative study of histogram equalization based image enhancement techniques for brightness preservation and contrast enhancement. Int. J. Signal Image Process. 4, 2013. https://doi.org/10.5121/sipij.2013.4502 (2013).
Yildirim, M. A color image encryption scheme reducing the correlations between R, G, B components. Optik 237, 166728. https://doi.org/10.1016/j.ijleo.2021.166728 (2021).
Nayak P., Nayak S. K. & Das S. A secure and efficient color image encryption scheme based on two chaotic systems and advanced encryption standard. In 2018 International Conference on Advances in Computing, Communications and Informatics. 412-418 (IEEE Access, 2018). https://doi.org/10.1109/ICACCI.2018.8554728.
Fan H., Lu H., Zhang C., Li M. & Liu Y. Cryptanalysis of an image encryption algorithm based on random walk and hyperchaotic systems. Entropy24(1), 40 (2022). https://doi.org/10.3390/e24010040.
Panwar, K. et al. Encipher GAN: An end-to-end color image encryption system using a deep generative model. Systems 11(1), 36. https://doi.org/10.3390/systems11010036 (2023).
Basha S.M., Mathivanan P. & Balaji Ganesh A. Bit level color image encryption using Logistic-Sine-Tent-Chebyshev map. Optik259, 2022. https://doi.org/10.1016/j.ijleo.2022.168956 (2022).
Wang, M., Xianping, F., Yan, X. & Teng, L. A new chaos-based image encryption algorithm based on discrete Fourier transform and improved Joseph traversal. Mathematics 12(5), 638. https://doi.org/10.3390/math12050638 (2024).
Varun, A.V. & Kumar, D. Secure chaotic image encryption method using random graph traversal and three step diffusion. Multimed. Tools Appl. 83, 46799–46824. https://doi.org/10.1007/s11042-023-17418-y (2024).
Teng, L., Wang, X. & Xian, Y. Image encryption algorithm based on a 2D-CLSS hyperchaotic map using simultaneous permutation and diffusion. Inf. Sci. 605, 71–85. https://doi.org/10.1016/j.ins.2022.05.032 (2022).
Pan, H., Lei, Y. & Jian, C. Research on digital image encryption algorithm based on double logistic chaotic map. EURASIP J. Image Video Process. 142 (2018). https://doi.org/10.1186/s13640-018-0386-3.
Chai, Xiuli, Zheng, Xiaoyu, Gan, Zhihua, Han, Daojun & Chen, Yiran. An image encryption algorithm based on chaotic system and compressive sensing. Signal Process. 148, 124–144. https://doi.org/10.1016/j.sigpro.2018.02.007 (2018).
NIST SP 800-22. A Statistical Test Suite for Random and Pseudorandom Number Generators for Cryptographic Applications. (National Institute of Standards and Technology, 2010).
Ma, S., Zhang, Y., Yang, Z., Hu, J. & Lei, X. A new plaintext-related image encryption scheme based on chaotic sequence. IEEE Access 7, 30344–30360. https://doi.org/10.1109/ACCESS.2019.2901302 (2019).
Alvarez, G. & Li, S. Some basic cryptographic requirements for chaos-based cryptosystems. Int. J. Bifurc. Chaos 16, 2129–2151. https://doi.org/10.1142/S0218127406015970 (2006).
Acknowledgements
The Researchers would like to thank the Deanship of Graduate Studies and Scientific Research at Qassim University for financial support (QU-APC2025).
Author information
Authors and Affiliations
Contributions
All authors contributed equally in this work.
Corresponding authors
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Abdul, Y., Ramasamy, V., Kukaram, G. et al. A dynamic image encryption scheme through 2-D cellular automata and chaotic logistic map. Sci Rep 15, 36116 (2025). https://doi.org/10.1038/s41598-025-21225-w
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1038/s41598-025-21225-w