Abstract
Biometric authentication is essential for securing Internet of Things (IoT) devices, yet the vulnerability of biometric data to breaches underscores the necessity for improved security measures. Cancelable biometric sysems, which convert original biometric data into non-reversible templates, offer a strong solution for user privacy preservation. This paper presents an innovative method for creating cancelable biometric templates by integrating Empirical Mode Decomposition (EMD) and quaternion mathematics. The EMD disaggregates biometric data into Intrinsic Mode Functions (IMFs), whereas quaternion transformations guarantee the safety and non-reproducibility characteristics of the templates. The proposed method ensures template diversity and IoT systems’ efficiency. Experimental assessments indicate the method robustness against possible attacks, attaining an Area under the Receiver Operating Characteristic curve (AROC) of 0.9997 and an almost negligible Equal Error Rate (EER). Moreover, the system has a minimal computational cost, rendering it appropriate for resource-limited IoT settings. These findings highlight the method capacity to tackle significant security issues, while ensuring optimal performance in practical applications.
Similar content being viewed by others
Introduction
With developments in electronic device capabilities and communication technologies, biometrics has become a pivotal tool to authenticate and identify individuals1. Biometric characteristics can be classified into physical qualities, such as fingerprints, palm prints, facial features, or behavioral patterns, including voice and stride. These particular biometric traits are unique to individuals, facilitating reliable differentiation between users2. As a result, biometrics has emerged as a very efficient substitute for conventional password-based authentication solutions. Integrating biometric technologies with IoT systems is a possible answer to security challenges in IoT contexts3,4.
Biometric authentication systems have two fundamental phases: enrollment and evaluation. Biometric data are collected and preserved during enrollment for subsequent comparisons with future biometric samples5,6,7. In contrast to conventional passwords, biometric data cannot be substituted if compromised. To mitigate this issue, it is essential to protect biometric data or replace them with cancelable templates produced via non-reversible methods7. New methodologies are utilized to protect biometrics: biometric cryptography and cancelable biometrics. In biometric cryptography, biometric information is preserved in an encrypted form. During authentication, the encrypted data is decrypted for comparison with the decoded query sample; nevertheless, this procedure creates possible weaknesses during the decryption phase. Alternatively, cancelable biometrics allows authentication directly on altered, non-reversible templates, reducing security risks8.
While creating secure biometric templates, four fundamental requirements must be evaluated: non-inevitability, diversity, reusability, and high performance. The principle of non-inevitability guarantees that safeguarded templates may be rescinded and substituted with newly modified versions following a security violation. Diversity requires that templates are distinct across various applications to avoid redundancy. In addition, protected templates must provide sufficient security to prevent reconstruction of original biometric data, while maintaining high recognition accuracy to facilitate successful biometric authentication9.
Various techniques for safeguarding biometric templates have been suggested. Specific methodologies depend on a singular biometric modality for the verification process, with the so-called unimodal biometrics. Fingerprint, iris, and facial recognition are among unimodal verification systems9. However, unimodal biometrics frequently demonstrate constrained dependability. Various biometric modalities for a single individual can be integrated to improve verification accuracy and system resilience, creating multimodal biometric systems10. Multimodal biometrics substantially diminish the probability of unauthorized access, thereby enhancing security. Frequent combinations in multimodal systems consist of fingerprints with iris patterns, facial images with fingerprints, and more pairings5.
In the light of the security issues posed by password-based identity systems, our research demonstrates biometric recognition as a formidable option. We deploy the cancelable biometric generation method to preserve original biometric data from potential database breaches. This study introduces an innovative approach for producing cancelable biometric templates employing EMD in conjunction with quaternion mathematics. This technology improves security by converting biometric data into irreversible templates appropriate for real-time IoT applications. The verification technique employs template correlation and thresholding to provide precise identification without reconstructing the original biometrics.
The fundamental contribution of this research work is developing a face-based biometric verification framework tailored for IoT systems. The key characteristics of the suggested methodology are as follows:
-
The algorithm solely uses facial images to create secure biometric templates, concentrating on a singular biometric modality. The EMD is utilized to deconstruct the facial image into its fundamental components, facilitating improved feature extraction.
-
Quaternion mathematics is utilized to encrypt the decomposed facial data, offering a solid technique for template protection.
-
The encrypted biometric template is safely maintained in the database, obviating the necessity to preserve the original facial image, substantially augmenting both privacy and security.
This framework protects biometric data, while preserving its verification functionality, making it ideal for IoT-based real-time applications.
The simulation outcomes indicate that the suggested system satisfactorily fulfills the requirements of non-invertibility, diversity, reusability, and high performance. The effectiveness of the system is confirmed by evaluation using the Olivetti Research Laboratory (ORL) face images and Labeled Faces in the Wild (LFW), a database for studying face recognition in unconstrained environments 11,12.
Related work
Cancelable biometric systems depend on intentionally altering biometric data using techniques like biometric salting or non-invertible transformations. These systems maintain databases that contain only altered versions of biometric data, as opposed to the original biometric information. The verification method depends on these altered templates, safeguarding the original biometric data from recovery, thus augmenting security and privacy.
Cancelable biometric templates are altered or distorted forms of biometric data intended to facilitate elimination or replacement of utilized templates instead of changing the biometric data itself. These modified templates preserve the effectiveness of identification systems, reconciling the need for security with enhanced identification precision. This equilibrium requires a meticulous management of trade-offs1. Diverse algorithms have been formulated to tackle these issues, including encryption, transformations, compression, and data-hiding strategies, which are frequently utilized to create cancelable templates. Certain algorithms employ a singular biometric modality, whereas others use many biometric modalities to generate the secure templates13,14.
Fingerprints are extensively utilized in identification systems owing to their distinctive minutiae features. Jing et al.15 devised a cancelable biometric blueprint based on these minutiae, combining numerous single-line codes with fingerprint characteristics to generate multi-line codes. These codes represent the modified templates, tackling the problem of layout invariance between molds. The algorithm exhibited an Equal Error Rate (EER) of 4.69%. In another technique, Jin et al.16 leveraged Minutiae Proximity Decomposition (MVD) to construct a cancelable fingerprint identification system, attaining a considerably low EER of 1.77%.
Gowthami et al.13 utilized zone-based linear binary patterns for fingerprint recognition, segmenting each fingerprint image into nine uniformly sized sectors, with each sector designating its own linear pattern for identification. This technique achieved an average recognition accuracy of 94.28%. Likewise, Sandhaya and Parased17 created a cancelable fingerprint recognition method using spiral patterns and fuzzy logic processing. The fuzzy commitment method was used to encrypt minutiae features, yielding an EER of 1.17%.
Qiu et al. 18 devised a cancelable template generation method employing Gabor filters and a look-up table for palmprint recognition. The Gabor filter extracts features from palmprint images, which are then encoded using a lookup table. This system exhibited an exceptional detection rate of 99.92%, while efficiently protecting palmprint templates from cracker attempts.
Another method for cancelable biometric identity recognition systems involves employing features derived from the iris region of ocular images for personal identification. This procedure begins with the localization and normalization of the iris region, followed by feature extraction. Cancelable iris recognition primarily emphasizes the concealment of iris features by encryption or irreversible modifications before storage or verification. Ali and Tahir19 proposed a cancelable iris identification technique that successfully combines encryption with non-reversible changes to conceal iris characteristics. This technique achieved an identification rate of 99.9%.
Although unimodal biometric templates perform satisfactorily, they have distinct limits in particular contexts. For example, in fingerprint identification, difficulties, such as the scanner failure to obtain correct fingerprints, may lead to erroneous acceptances or rejections. Factors such as fingerprint degradation impede the capturing of precise images. Likewise, poor conditions during data acquisition might alter biometric characteristics in facial recognition. Fluctuations in illumination and facial emotions influence the quality and dependability of facial data. Multimodal biometrics offer a comprehensive method to eliminate these constraints by merging different biometric modalities, thus increasing recognition accuracy and system dependability20.
The amalgamation of many biometric modalities into a singular template for an individual is a burgeoning concept that improves verification reliability, while streamlining storage needs. This multi-biometric recognition method enables the generation of templates that can be easily revoked and substituted if necessary5. Sree and Radha developed a multimodal biometric system that integrates facial and fingerprint data. Their system utilizes the number of crossings concept to derive minutiae characteristics from fingerprints and the Local Binary Pattern (LBP) algorithm to obtain facial features. The features are integrated at the feature level, and a fuzzy vault technique is utilized to augment the security of the created templates14.
Tarek et al. introduced a multimodal biometric recognition algorithm incorporating encryption to boost security21. This algorithm depends on the Double Random Phase Encoding (DRPE) technology to encrypt fingerprint images, using the palmprint image as a secret key in the enrolment phase. Successful decryption during authentication is contingent upon providing the correct palmprint of the same user to confirm the individual identification. The decrypted fingerprint image is then compared against a newly obtained fingerprint image for validation.
Likewise, Soliman et al.22 presented an alternative encryption-based approach using DRPE for multimodal biometric recognition that incorporates iris and facial features. This approach involves extracting face features with the Scale-Invariant Feature Transform (SIFT) algorithm, and subsequently encrypting them using DRPE. Features are retrieved from two iris images of the same person for iris recognition. One iris image is encrypted using DRPE, while the other is used to create the second phase mask necessary for DRPE decryption.
Tarif et al.23 presented a multimodal cancelable biometric recognition system utilizing digital encryption and concealment methods. The technology seeks to guarantee the secure transmission of multimodal biometric data in identification systems. It integrates fingerprint, facial, and iris modalities, with fingerprint and iris images processed independently before embedding into a host facial image utilizing the Slantlet Transform with Singular Values (SLT-SVs).
Yang et al.24 devised a biometric access control system for critical infrastructures, employing fingerprint and facial recognition technologies. Their solution includes a cascaded encryption system containing core and disposable encryption layers. Furthermore, a fuzzy commitment strategy is employed to amalgamate the irreversible transformation key with the retrieved facial feature set, hence augmenting the system security and resilience.
Nasr et al.25 introduced an innovative method for enhancing the security of biometric systems via quaternion DRPE. The biometric data, including facial images, is first converted into quaternion representation. The data is expanded into four-dimensional space using quaternion mathematics, thereby substantially augmenting its complexity and security. The subsequent stage entails the implementation of DRPE on the quaternion-based data. DRPE depends on random phase masks to conceal biometric traits, enhancing data security. The result is a revocable biometric template that can substitute the original data if compromised, safeguarding sensitive biometric information. This procedure enables the system to modify the stored template without altering the user intrinsic biometric characteristics. The presented method exhibits exceptional accuracy and efficiency, as robust performance metrics indicate, including the area under the ROC curve and the EER. This method provides a robust and efficient solution for preserving privacy in biometric identification systems, tackling common security issues through quaternion mathematics26.
Khalaf et al.27 offered two sophisticated cancellable biometric recognition techniques that utilize quaternion mathematics to enhance security. The initial technique combines quaternion mathematics with the Fractional Fourier Transform (FRFT), deliberately adding distortions to biometric data to thwart unauthorized access. The second technique depends on quaternion rotation to create comparable distortions, hence enhancing the protection of biometric templates. Encoding biometric templates in quaternion form expands the data into four-dimensional space, hence augmenting its complexity and resistance against attacks. The performance assessment through metrics like EER and AROC underscores the efficacy of these techniques. Both of them exhibit remarkable reliability, attaining EER values around zero and AROC levels close to one. This study presents a comprehensive framework for privacy-preserving biometric authentication, delivering an effective solution to significant security concerns in biometric systems.
Andrew et al. introduced a two-factor authentication technique that integrates fingerprint biometrics with tokenized random integers to provide each user with a distinctive, concise code. The BioHashing approach improves security by necessitating both the token and the fingerprint for authentication, rendering it very resistant to biometric forgery and spoofing. This approach provides substantial benefits compared to conventional biometric systems, including a 0% EER and distinct differentiation between authentic and fraudulent populations, thus enhancing biometric authentication systems’ overall security and dependability28.
Dong et al. introduced an IoT-compatible biometric hashing network named PalmCohashNet. This network utilises palm print and palm vein data to produce distinctive, compact hash codes for each user. The technique enhances security by integrating two cooperatively-taught hashing sub-networks, ensuring that hash codes from the same identity are consistent and proximate. This technique markedly enhances authentication precision and security in IoT applications, rendering it exceptionally resilient to biometric spoofing and fabrication. PalmCohashNet versatility enables deployment in multiple operational modes, guaranteeing strong and dependable biometric authentication for IoT devices29.
Basic concepts
Empirical mode decomposition
A non-stationary signal is defined by its time-varying mean and variance, complicating analysis with traditional methods. EMD is an efficient technique for partitioning signals into a collection IMFs and a residual component (\(r_n\)). In contrast to conventional methods, EMD functions directly inside the time domain, maintaining the essential characteristics of the original signal, while decomposing it into significant components30. The first IMF encompasses the signal highest frequencies and energy levels, whereas the following IMFs denote progressively lower frequencies and energies, until they are reduced in the residual. A one-dimensional signal s(t) is decomposed into n IMFs and a residual, enabling the reconstruction of the signal through the summation of these components as shown in Fig. 1. This decomposition can be mathematically represented as follows31:
EMD can be an effective tool for extracting unique features from facial images in facial image processing to create cancelable biometric templates. Utilizing the adaptive and data-driven characteristics of EMD, the derived components can be modified to guarantee privacy and security, rendering the resultant templates both non-invertible and efficient for biometric identification.
An illustration of EMD decomposition for an input biometric.
The sifting process is an essential phase in EMD. It is employed to derive IMFs and a residual component from a signal. To qualify as an IMF, a component must meet two fundamental criteria: (1) the numbers of zero crossings and extrema must be either identical or different by no more than one, (2) the average of the upper and lower envelopes must equal zero.
In the sifting process, the envelope mean, denoted as m(t), is computed as follows:
where u(t) and l(t) represent the upper and lower envelopes, respectively. The initial IMF, denoted as h(t), is then formulated as:
where s(t) denotes the original signal. The two IMF criteria are subsequently evaluated for h(t). If the conditions are unmet, the sifting process is reiterated, considering h(t) as the new signal. This iterative process persists until a component meets the IMF criteria. Upon extraction of all IMFs, the original signal, s(t), can be rebuilt as follows:
where \(r_n\) is the ultimate residual. The sifting procedure is thereafter done recursively to the residual, r(t), until it comprises solely a single extremum.
Quaternion mathematics
Quaternions are a numerical system that expands complex numbers into four dimensions. Quaternions, first introduced by Sir William Rowan Hamilton in 1843, are essential in various domains, including 3D computer graphics, robotics, and physics, owing to their efficient representation of rotations and orientations32,33.
A quaternion is generally represented in the following format33:
where \(w, x, y,\) and \(z\) are real numbers, and \(i, j,\) and \(k\) represent the fundamental quaternion units. The units \(i, j,\) and \(k\) adhere to defined multiplication rules33.
These laws indicate that quaternion multiplication is non-commutative; thus, the multiplication sequence is significant. For example33:
Basic operations with quaternions
Let \(q_1\) and \(q_2\) be two quaternions expressed as33:
and
where \(w_1, w_2, x_1, x_2, y_1, y_2, z_1, z_2\) are real numbers, and \(i\), \(j\), and \(k\) are the fundamental quaternion units.
Addition and Subtraction: Quaternions can be added and subtracted component-wise33:
Multiplication: The product of two quaternions is given by33:
Conjugation: The conjugate of a quaternion \(q = w + xi + yj + zk\) is defined as33:
Norm: The norm of a quaternion \(q = w + xi + yj + zk\) is given by33:
Inverse: The inverse of a non-zero quaternion \(q = w + xi + yj + zk\) is calculated as33:
Unit quaternions and rotations
Unit quaternions, or normalized quaternions, have a norm equal to one and are essential in representing rotations in a three-dimensional space. A unit quaternion \(q = w + xi + yj + zk\) satisfies the condition33:
To depict rotation utilizing a quaternion, the quaternion must be a unit quaternion. Rotations can be readily combined by multiplying the respective unit quaternions. This attribute renders quaternions exceptionally efficient and stable for computations related to 3D rotations, circumventing the issues of gimbal lock linked to Euler angles and facilitating smooth interpolations25,34,35.
The proposed cancelable biometric system
Methodology
The suggested system is an unimodal identification system that depends solely on one biometric modality: face images. The system depends on the EMD to analyze input images by breaking them down into a sequence of IMFs. The initial IMF encapsulates the high-frequency and high-energy content of the original image, while the following IMFs denote lower-frequency components with diminishing energy levels as in Fig. 1.
The biometric system functions in two separate stages: the enrolment stage and the verification stage. The user biometric data is collected during the enrolment step to create a cancelable template. A query biometric is obtained during the verification step, and an identical procedure is employed to generate a cancelable template for matching. User verification is accomplished by comparing the enrolled template with the query template. The procedures for enrollment and verification are depicted in Fig. 2.
Enrollment and the verification phases of the biometric identification system.
The suggested method begins with the acquisition of facial biometric data, which is then processed by EMD to produce a sequence of IMFs. The IMFs are expressed in quaternion form, as depicted in Fig. 3 for explaining the proposed method for generating the cancelable template. The non-commutative multiplication property of quaternion mathematics is then applied. The output is normalized to yield a unit value retained as a cancelable template in the application database.
The quaternions are represented as follows:
The utilization of quaternions for generating cancelable biometric templates is represented in 3 steps as follows:
Step 1: Compute \(q_1 \cdot q_2\)
Using quaternion multiplication, the result is:
Let this result be denoted as \(q_{12}\).
Step 2: Multiply \(q_{12}\) by \(q_3\)
Let \(q_{12} = a + bi + cj + dk\), where:
Now, compute \(q_{12} \cdot q_3\):
Let the result of this multiplication be denoted as \(q_{123}\), where:
Step 3: Compute the unit quaternion. The unit quaternion is obtained by normalizing \(q_{123}\). The norm of \(q_{123}\) is given by:
The unit quaternion is then calculated as:
Ultimately, the \(q_{\text {unit}}\) is preserved as the produced biometric template, as depicted in Fig. 3.
Illustration of the proposed biometric template generation process.
Template revocation and replacement mechanism
The suggested method depends on the intrinsic characteristics of quaternion mathematics and the biometric data transformation process for template revocation and replacement. The essential steps are as follows:
Template Revocation: Each biometric input is subjected to EMD to derive IMFs, which are subsequently encoded using quaternion transformations. Should a template be compromised, its security can be nullified by eliminating the pertinent transformation parameters and quaternion mappings linked to it. Without specific criteria, the compromised template becomes inoperative, safeguarding system security.
Template Replacement: A novel template can be produced by utilizing an alternative set of transformation parameters on the original biometric data. The quaternion mappings and transformation rules are contingent on the key. They are not reliant on the compromised template, ensuring that the new template remains unlinkable to the previous one. This attribute maintains the biometric system cancelability and reusability without compromising its recognition efficacy.
Utilization of quaternion mathematics guarantees that the changed templates are not directly reversible, obstructing unauthorized access or reconstruction of the original biometric information. The system depends on this technique to preserve template diversity and avert cross-matching between revoked and substituted templates.
Simulation results
The suggested method employs data-hiding techniques to safeguard biometric templates. EMD initially decomposes the biometric input, yielding a sequence of IMFs. Quaternion mathematics is subsequently employed on these IMFs, converting them into a secure template. This procedure guarantees the security of biometric data by integrating it within a non-commutative mathematical structure.
This section delineates the outcomes of the suggested method. The simulation studies depend on a MacBook with 32 GB of memory, using MATLAB 2023b. The datasets utilized in the experiments comprise the Olivetti Research Laboratory (ORL) for facial images and Labeled Faces in the Wild (LFW): a database for studying face recognition in unconstrained environments11,12. All cancelable templates have dimensions of 128 \(\times\) 128, with face images resized to this resolution. The average processing time of the enrollment and verification process is 0.7035 s.
The proposed method depends on EMD and quaternion mathematical methods to generate cancelable biometric templates. To evaluate the relationship between the original and the cancelable biometric templates, the correlation coefficient \(c_r\) is used. A diminished value of \(c_r\) signifies an elevated degree of robustness of the cancelable template.
The verification procedure is assessed using two metrics: EER and AROC36. The EER functions as a metric of system precision, where diminished values signify enhanced accuracy. Conversely, the AROC is used to assess system efficiency, with a value approaching one signifying enhanced efficiency. The authentic and fraudulent score distributions, together with the ROC curve, are obtained using simulation studies.
Figures 4 and 6 display representative images from the ORL and LFW face datasets alongside their histograms. Figures 5 and 7 illustrate cancelable templates and their corresponding histograms using the proposed encryption-like methodology. The correlation coefficient (\(c_r\)) between the original and cancelable templates approaches zero, signifying the robustness and great efficacy of the template generation process.
Samples from ORL dataset (a) original face images and (b) image histograms.
Cancelable templates based on EMD and quaternion mathematics for ORL dataset (a) cancelable templates and (b) histograms of cancelable templates.
Samples from LFW dataset (a) original face images and (b) image histograms.
Cancelable templates based on EMD and quaternion mathematics for LFW dataset (a) cancelable templates and (b) histograms of cancelable templates.
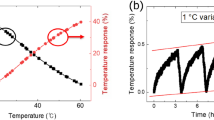
Figures 8 and 9 represent the distributions of authentic and fraudulent scores, as well as the ROC curves in different cases. Table 1 presents the numerical values of EER and AROC. The data in the table indicates that the proposed cancelable biometric recognition algorithm exhibits high performance in the verification process, as reflected by AROC values approaching 1. Furthermore, the EER approaches 0, signifying the system great accuracy.
Simulation results for ORL dataset (a) Verification results of genuine and impostor distribution curves. (b) Verification results of AROC curve.
Simulation results for LFW dataset (a) Verification results of genuine and impostor distribution curves. (b) Verification results of AROC curve.
The little discrepancy between the EER of 0.00 and the AROC of 0.9997 might be ascribed to the granularity and distribution of the underlying data. The EER metric denotes the precise juncture at which the False Accept Rate (FAR) matches the False Reject Rate (FRR), with a value of approximately 0.00, signifying an impeccably distinguishing system for the assessed dataset. Nonetheless, the AROC is a comprehensive metric derived from the integral of the ROC curve over all threshold values, offering an overarching perspective on system performance. The result of 0.9997 indicates an almost perfect separation of templates, although it may slightly differ from 1 due to the aggregate effect of thresholds. Hence, the system performance is virtually flawless but not entirely absolute. This disparity frequently arises in practical systems as a result of interpolation techniques or minor flaws in the dataset.
The simulation results indicate that the suggested cancelable biometric recognition algorithm successfully reconciles the four essential criteria of cancelable biometric systems. By integrating EMD and randomly produced quaternions, the approach guarantees the generation of a unique cancelable template for each user. This method facilitates the creation of several cancelable templates from identical facial images without undermining the system efficiency or performance. Simulation outcomes across multiple areas validate the superior efficacy of the suggested system. Table 2 demonstrates that the system surpasses current state-of-the-art techniques15,22,23,26,27. The analysis of the EER and FAR underscores the enhanced efficacy of the proposed system.
Conclusion
This research work introduced an innovative method for constructing a cancelable biometric recognition system for IoT applications by integrating EMD and quaternion mathematics. The suggested method creates cancelable biometric templates by converting deconstructed biometric features into a quaternion format. This transformation expands the data into four-dimensional space, augmenting complexity and security.
In contrast to conventional methods, this method does not depend directly on the user’s initial biometric data, facilitating template updates, while preserving user privacy. The proposed system effectiveness was confirmed by simulations and comparison trials, revealing low EER values and high AROC scores, underscoring its high performance. An extensive complexity analysis encompassing computational time assessment validated its feasibility for real-time applications.
This system depends on developing techniques like EMD and quaternion mathematics to substantially improve the security and adaptability of access control in IoT systems, rendering it a good solution for privacy-preserving biometric authentication in contemporary cyber-physical contexts.
References
Jain, A., Ross, A. & Prabhakar, S. An introduction to biometric recognition. IEEE Trans. Circuits Syst. Video Technol. 14, 4–20. https://doi.org/10.1109/TCSVT.2003.818349 (2004).
Choudhury, B., Then, P., Issac, B., Raman, V. & Haldar, M. K. A survey on biometrics and cancelable biometrics systems. Int. J. Image Graph. 18, 1850006 (2018).
Yang, W. et al. Biometrics for internet-of-things security: A review. Sensors 21, 6163 (2021).
Hussein, A. F., AlZubaidi, A. K., Al-Bayaty, A. & Habash, Q. A. An iot real-time biometric authentication system based on ecg fiducial extracted features using discrete cosine transform. arXiv preprint[SPACE]arXiv:1708.08189 (2017).
Bedad, F. & Réda, A. Multi-biometric template protection: An overview. In International Conference in Artificial Intelligence in Renewable Energetic Systems, 62–79 (Springer, 2018).
El-Hameed, H. et al. Cancelable biometric security system based on advanced chaotic maps. Visual Comput. 38, 2171–2187. https://doi.org/10.1007/s00371-022-02167-w (2022).
Chung, Y., Moon, D., Moon, K. & Pan, S. A hybrid encryption/hiding method for secure transmission of biometric data in multimodal authentication system. Multimed. Tools Appl. 77, 16477–16493. https://doi.org/10.1007/s11042-018-6583-1 (2018).
Manzoor, S. & Selwal, A. An analysis of biometric based security systems. In IEEE Fifth International Conference on Parallel, Distributed and Grid Computing (PDGC), 306–311 (2018).
Sarkar, A. & Singh, B. K. A review on performance security and various biometric template protection schemes for biometric authentication systems. Multimed. Tools Appl. 79, 27721–27776. https://doi.org/10.1007/s11042-020-08762-x (2020).
Jin, Z., Teoh, A., Goi, B. & Tay, Y. Biometric cryptosystems: A new biometric key binding and its implementation for fingerprint minutiae-based representation. Pattern Recogn. 56, 50–62. https://doi.org/10.1016/j.patcog.2016.01.002 (2016).
ORL Database. Orl database (n.d.). (accessed 03 Dec 2024).
Huang, G. B., Ramesh, M., Berg, T. & Learned-Miller, E. Labeled faces in the wild: A database for studying face recognition in unconstrained environments. typeTech. Rep. number 07-49, University of Massachusetts, Amherst (2007).
Gowthamim, A. & Mamatha, H. Fingerprint recognition using zone based linear binary patterns. Proc. Comput. Sci. 58, 552–557. https://doi.org/10.1016/j.procs.2015.08.074 (2015).
Sree, S. & Radha, N. Cancelable multimodal biometric user authentication system with fuzzy vault. In IEEE International Conference on Computer Communication and Informatics (ICCCI), 1–6 (2016).
Gupta, K., Walia, G. & Sharma, K. Novel approach for multimodal feature fusion to generate cancelable biometric. Visual Comput. 37, 1401–1413. https://doi.org/10.1007/s00371-021-01989-1 (2021).
Jin, Z., Lim, M., Beng, A., Teoh, J. & Goi, B. A non-invertible randomized graph-based hamming embedding for generating cancelable fingerprint template. Pattern Recogn. Lett. 42, 137–147. https://doi.org/10.1016/j.patrec.2014.03.006 (2014).
Sandhya, M. & Prasad, M. Cancelable fingerprint cryptosystem using multiple spiral curves and fuzzy commitment scheme. Int. J. Pattern Recogn. Artif. Intell. 31, 1756004. https://doi.org/10.1142/S0218001417560046 (2017).
Qiu, J., Li, H. & Dong, J. Design of cancelable palm print templates based on look up table. In IOP Conference Series: Materials Science and Engineering, 60–70. https://doi.org/10.1088/1757-899X/402/1/012051 (2018).
Ali, M. & Tahir, N. Cancelable biometric technique for iris recognition. In 2018 IEEE Symposium on Computer Applications & Industrial Electronics (ISCAIE), 434 (2018).
Krishnakumari, Y. & Savitha, G. A review on unimodal and multimodal biometric systems. Int. J. Innov. Sci. Res. Technol. 2 (2017).
Tarek, E., Ouda, O. & Atwan, A. Image-based multimodal biometric authentication using double random phase encoding. Int. J. Netw. Secur. 20, 1163–1174. https://doi.org/10.6633/IJNS.201811_20(6).07 (2018).
Soliman, R. et al. Double random phase encoding for cancelable face and iris recognition. Appl. Opt. 57, 10305–10316. https://doi.org/10.1364/AO.57.010305 (2018).
Tarif, E., Wibowo, S., Wasimi, S. & Tareef, A. A hybrid encryption/hiding method for secure transmission of biometric data in multimodal authentication system. Multimed. Tools Appl. 77, 2485–2503. https://doi.org/10.1007/s11042-018-6005-7 (2018).
Yang, W., Wang, S., Zheng, G., Chaudhry, J. & Valli, C. Ecb4ci: An enhanced cancelable biometric system for securing critical infrastructures. J. Supercomput. 74, 4893–4909. https://doi.org/10.1007/s11227-018-2475-9 (2018).
Nasr, M., Piórkowski, A., El-Samie, A. & Fathi, E. Quaternion double random phase encoding for privacy-preserving cancelable biometrics. Multimed. Tools Appl. 1–14 (2024).
Nasr, M., Piórkowski, A., Mah, P. M. & Abd El-Samie, F. E. Cancelable biometrics based on quaternion adaptive filter optimization for security applications. In 2024 6th International Conference on Computing and Informatics (ICCI), 490–498 (IEEE, 2024).
Khallaf, F. et al. Implementation of quaternion mathematics for biometric security. Multimed. Tools Appl. 1–28 (2024).
Teoh, A. B. J., Ling, D. N. C. & Goh, A. Biohashing: Two factor authentication featuring fingerprint data and tokenised random number. Pattern Recogn. 37, 2245–2255 (2004).
Dong, X., Khan, M. K., Leng, L. & Teoh, A. B. J. Co-learning to hash palm biometrics for flexible iot deployment. IEEE Internet Things J. 9, 23786–23794 (2022).
Hadiyoso, S., Wijayanto, I., Rizal, A. & Aulia, S. Biometric systems based on ecg using ensemble empirical mode decomposition and variational mode decomposition. J. Appl. Eng. Sci. 18, 181–191 (2020).
Abd El-Moneim, S., Dessouky, M. I., Abd El-Samie, F. E., Nassar, M. & Abd El-Naby, M. Hybrid speech enhancement with empirical mode decomposition and spectral subtraction for efficient speaker identification. Int. J. Speech Technol. 18, 555–564 (2015).
Kuipers, J. B. Quaternions and Rotation Sequences: A Primer with Applications to Orbits, Aerospace, and Virtual Reality (Princeton University Press, 1999).
Voight, J. Quaternion Algebras (Springer Nature, 2021).
Zhu, X., Xu, Y., Xu, H. & Chen, C. Quaternion convolutional neural networks. In Proceedings of the European Conference on Computer Vision (ECCV), 631–647 (2018).
Huang, C., Li, J. & Gao, G. Review of quaternion-based color image processing methods. Mathematics 11, 2056 (2023).
Bae, G., Lee, H., Son, S., Hwang, D. & Kim, J. Secure and robust user authentication using partial fingerprint matching. In 2018 IEEE International Conference on Consumer Electronics (ICCE), 1–6 (2018).
Acknowledgements
This research project supported/partly supported by program “Excellence initiative – research university” for the University of Krakow. This project has received funding from the European Union’s Horizon 2020 research and innovation programme under Grant agreement No 857533 and from the International Research Agendas Programme of the Foundation for Polish Science No MAB PLUS/2019/13. The publication was created within the project of the Minister of Science and Higher Education “Support for the activity of Centers of Excellence established in Poland under Horizon 2020” on the basis of the contract number MEiN/2023/DIR/3796.
Author information
Authors and Affiliations
Contributions
M.N.: Writing—original draft, software, methodology, conceptualization. A.P., K.B., F.E.: Writing—review and editing, software, methodology, conceptualization. F.E.: Software, data curation. A.P.: Validation, software. K.B.: Validation, software. F.E.: Visualization. A.P., F.E.: Investigation.
Corresponding author
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Nasr, M., Brzostowski, K., Piórkowski, A. et al. Cancelable biometric authentication leveraging empirical mode decomposition and quaternion representations for IoT security. Sci Rep 15, 10997 (2025). https://doi.org/10.1038/s41598-025-89491-2
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1038/s41598-025-89491-2
This article is cited by
-
Securing biometric authentication: a hybrid approach with non-invertible wavelet scattering transform and RSA encryption for speech signal protection
Multimedia Tools and Applications (2026)