Abstract
As security threats emerge, how to protect the highly-dependent infrastructure of modern society has become a great challenge. Previous studies have mostly assumed that attackers are completely rational and well-informed, and have generally considered only a single type of attacker. However, these assumptions are inconsistent with reality, where attackers often have incomplete information and irrational behavior. This paper combines network science and game theory, based on the Bayesian Stackelberg game model, studies the defense strategy under the condition of incomplete information. We especially consider the variation of rationality degree of multi-type attackers, and propose a camouflage network construction model and a strong \(\varepsilon\) equilibrium strategy. In addition, the effectiveness of the proposed method is verified by experiments. Preventive and protective measures can be taken before an attacker can launch an attack, thus greatly reducing the risk of an attack on an infrastructure network.
Similar content being viewed by others
Introduction
As the basic support of social production and operation, the failure of key infrastructure network will seriously affect people’s daily life. Since the 9/11 terrorist attacks in the United States in 2001, the frequency, scope, and severity of deliberate attacks by terrorists have increased, including the intentional sabotage of the Guri Hydroelectric Plant in Venezuela in 2019 and the explosion of the Crimean Bridge in 2023. At present, the protection of infrastructure has become the consensus and goal of the security management of countries all over the world1. This highlights the urgent need for advanced methodologies to protect critical infrastructure from various threats.
Infrastructure is a kind of infrastructure system, which is connected by pipelines and so on. A large number of connections between nodes and facilities form infrastructure network2,3. In recent years, a number of methods have been proposed for the protection of infrastructure networks such as transportation, communications and power grids, including probabilistic risk assessment4, historical data assessment5, threat modeling6 and security testing7. However, these methods need to define the failure probability of nodes as static input, and can not model the behavior of participants well. The whole process is not considered in the network attack and defense, but as a passive means of compensation. Therefore, how to protect critical infrastructure from paralysis remains a real problem that needs to be addressed. Existing methods lack the ability to dynamically adapt to changing conditions and fail to account for the complexities of real-world interactions.
Network attack and defense needs to accurately model the key factors such as multi-party interaction, non-cooperation, incomplete information and strategy optimization in the course of confrontation8. Based on this, the decision support is provided through the prediction of counteraction behavior. The complex network can provide a suitable modeling tool for describing complex systems such as infrastructure, and game theory can provide a mathematical framework for the description of counteraction process. This combination allows for a more comprehensive understanding of the dynamics involved in network attack and defense scenarios.
In the research on protecting infrastructure network, some researchers use game theory to study infrastructure networks, while others use complex network analysis. There are also numerous studies that combine network science and game theory to analyze the role of game models in infrastructure protection and explore the strategy choices of attackers and defenders in network confrontation from a network perspective. The composition of modern social infrastructure is more and more huge, and the structure is more and more complex, which presents the complex characteristics of the network. The function of the infrastructure network depends to a large extent on the topology of the node facilities and connections, and the failure of the single node facilities may have a destructive effect on the system. Therefore, it is essential to model the infrastructure as a network system to better understand its vulnerabilities and resilience. The study of games is mostly based on simultaneous games, but in order to prevent the destruction of the infrastructure, the security agencies always conduct defense measures before an attack to prevent infrastructure damage, so it is more practical to use the Stackelberg Security Game (SSG) model. Specifically, when the leader (defender) submits a mixed strategy, the follower(attacker) chooses his pure strategy by observing the leader’s strategy9. In the environment of network attack and defense, when defenders have limited resources and cannot completely protect key targets, the limited resources must be properly allocated.
The active defense is to help the defender develop a targeted defense strategy. In the research of infrastructure network protection based on network attack and defense, it is usually assumed that all the structure information is known, but the network information obtained by the attacker has the possibility of both missing information and containing false information inreal. Incomplete information and false information will interfere with the judgment of the attacker, the attack effect will be discounted, and the defense resources of the defense can be reduced accordingly. Thus, the active defense method can significantly enhance the robustness of the network by leveraging the attacker’s misjudgments and uncertainties.
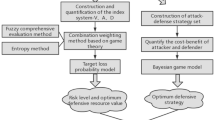
In this paper, we put forward the protection method of infrastructure network from the perspective of active defense and the advantage of game theory. The Bayesian Stackelberg game model based on false network is established. Firstly, the generation model of false network is proposed based on graph convolution network, which can overcome the limitation of network reset, the defender can take advantage of asymmetric information and gain the “first-mover advantage”; secondly, the strong \(\varepsilon\) equilibrium of Bayesian Stackelberg game is proposed for how the defender can improve the network robustness. The strong \(\varepsilon\) equilibrium is a solution that aims to deal with irrational or incomplete information situations in which an attacker acts by introducing a tolerance error \(\varepsilon\). In particular, strong \(\varepsilon\) equilibria can avoid worst-case losses and ensure the best strategy for defenders against different types of attackers. In the experiment analysis, it is proved that the proposed method can effectively transfer the attack damage, thus protecting the infrastructure network and improving the whole network.
In summary, based on reverse thinking, this paper solves three difficulties: incomplete information, multiple types of attackers and irrational attackers. Although existing research offers a variety of approaches to infrastructure protection, such as probabilistic risk assessment and threat modeling, these often rely on static network models or assume that attackers act completely rationally. Therefore, this paper proposes a more realistic game model by introducing incomplete information and multi-type attacker behavior model. The contribution are as follows: first, a false network setting method based on graph convolution network is proposed through active defense thought, which can change the key targets and fragile features of the network; second, a strong \(\varepsilon\) equilibrium is designed, and the strategic preferences of defenders and attackers under different available resources are obtained, which provides a reference for the rational allocation of the defense resources.
Related works
Since Vincent Conitzer and Tuomas Sandholm published a study on Stackelberg game in the field of security protection in 20067, Stackelberg game has provided a large number of decision-making solutions on various security issues. The research on critical infrastructure protection based on offensive and defensive game has experienced the development process from static to dynamic, from complete information to incomplete information, from complete rationality to incomplete rationality10,11. Zhou et al.12 put forward critical phase transition position monitoring index to predict network collapse, and built a network cascade fault recovery model based on system crash warning. Li et al.13,14 used static game and dynamic game to study the interaction between typical attack and defense strategies on infrastructure networks. Aiming at the problem of optimal strategy selection in network deception defense, Hu Yongjin, et al.15 constructs a multi-stage network deception game model and designs an optimal network deception defense strategy selection algorithm. Based on the attacker and defender simultaneous game model, fu et al.16 considered the effect of cascade failure on the strategy outcome. In view of the fact that the attacker chooses his own attack strategy according to the defensive strategy, Zeng et al.17 proposes an active deception defense method based on the asymmetric information of Stackelberg security game.
In addition, game-based methods have also been applied in practical application systems, such as Auxiliary Random Routing Monitor (ARMOR)18 and Intelligent Random Scheduling (IRIS)19.
Therefore, by establishing the complex network attack-defense game model and using the mathematical method to calculate the game equilibrium, we can effectively predict and get the optimal strategy of the defender, which can take the initiative in the confrontation and avoid the passivity. Through research on complex network and game theory, decision-maker can shift thinking pattern, helping defender not only consider their own factors, but also take into account the goal preferences, strategy dependence, information mastery and dynamic evolution tendency of the attacker and defender, thereby enhancing their understanding of dynamic security in the system confrontation process. This problem deserves further discussion. At present, there are still some shortcomings of network attack and defense countermeasures:
-
1.
Lack of research on information asymmetry In the process of network offensive and defensive confrontation game, the information held by both sides is symmetrical by default, and the topological structure information of infrastructure network is completely observable. However, due to opposing objectives of two sides of the network, the attacker can only obtain the local network structure. How can defenders take advantage of incomplete information conditions to actively deceive attacker and influencing his strategy through reverse thinking, so as to protect the network structure is a difficult problem, and there are few related research results.
-
2.
Inadequate study of rival types In the game of network antagonism, it is considered that the attacker makes the decision with the aim of reducing the overall capability of infrastructure, usually taking the size of network connectivity as the index of game equilibrium. However, different attackers have different motives and resources, pay attention to the vulnerability of different aspects of infrastructure network, and adjust their strategies with the change of time and environment. If only the behavior pattern of a certain type of attacker is studied, it may be difficult to effectively deal with unknown attacks, and corresponding protection strategies cannot be adopted.
-
3.
Insufficient study on the degree of opponent’s rationality In the game of network attack and defense, it is usually based on the rational assumption of the opponent, assuming that all the attackers are absolutely rational, and can accurately evaluate the information, calculate the benefit and make the best decision. However, the decision-making and behavior of the opponents in the real game situation are often influenced by their rational degree. If they fail to fully consider the irrational decision-making of the attackers, they may lead to the non-optimal deviation strategy of the defenders and cause the failure of the network nodes in a wider scope.
-
4.
Insufficient research on node interaction In the process of network offensive and defensive confrontation game, the nodes are considered as independent individuals, and the benefit of the game is the sum of all attack nodes or defense nodes, which is expressed by mathematical expression and solved by optimization method. However, cascading failure after attacking nodes may lead to exponential propagation and diffusion of attack range, and bypassing direct security measures. Without considering the relationship between nodes, the protection strategy may not effectively prevent or slow down the attack progress.
Therefore, in order to solve the above problems, it is necessary to analyze and solve the vulnerability of the defender’s network structure in the network attack and defense confrontation through game theory, establish the interaction model between the attacker and the defender, and search the strategy to protect the infrastructure network structure. Our work bridges these gaps through:
-
1.
Active deception: Unlike passive approaches, we generate false networks that actively manipulate attacker observations.
-
2.
Bayesian multi-type modeling: Extending Zeng’s asymmetric framework17, we incorporate ST/LT attacker types with prior probabilities, formalized via novel Bayesian Stackelberg equilibrium.
-
3.
Bounded rationality handling: First to integrate strong \(\varepsilon\)-equilibrium for robustness against irrational attackers.
-
4.
Cascading interactions: Explicitly modeling node interdependencies, overcoming simplification in the failure model.
Stackelberg game model based on false network
The network offensive defense model is used to analyze the strategic interaction between attackers and defenders. A defensive strategy may trigger a change in an offensive strategy, and vice versa, an offensive strategy may force the defender to adjust his strategy. The defense strategy may trigger the change of the attack strategy, and the attack strategy may force the adjustment of the defense strategy. This interaction is similar to the leader-follower interaction in the Stackelberg game, in which the follower responds to the leader’s actions. Based on Stackelberg game model, the network attack-defense game model is established, and the node interaction relationship is formally described. Considering that the cascading failure will occur after the nodes in the network are attacked, we also add this process to the game. At the same time, under the guidance of the active defense thought, the design of false network combined with the vulnerable feature can solve the problem of unknown attacker type and change of rationality degree.
False network
The infrastructure network is generally not a single network, but more or less has a coupling relationship with other networks, such as physical dependence and information exchange, and is interdependent with other networks, interact with each other, and play a role together, such as power grid and computer network, air route network and railway network. In 2003, the Italian power failure accident was due to the failure of the power grid nodes, resulting in the failure of the computer network nodes, which could not effectively regulate the power grid, resulting in a nationwide power outage20. The study of this kind of dependent network can deepen the deep understanding of the process of network offensive and defensive confrontation.
The real world is not entirely appreciable, so it is more practical to study network offensive and defensive confrontation from the angle of incomplete information. At present, many researches have optimized the original structure protection network, this kind of method will change the inherent structure of the original network, also will cause the network function to change accordingly, therefore, the rationality of the method is challenged.
In addition, the passive static defense method does not take full advantage of the attacker’s observation bias to influence the attacker itself, and it is very expensive to the defense resources, which makes the method difficult to be used in practice. In order to solve the above problems, we need a protection method which does not change the original network structure. Therefore, this paper realizes the network protection under the condition of incomplete information through false network. The false network is in the process of attack and defense, the defender adds the interference information, so that the attacker can observe the wrong network structure. Attackers observe this information and assume that the false network is the real infrastructure network, which interferes with their judgment and decision-making, and ultimately weakens the threat of the attacker. In this paper, the definition of false network is as follows:
Definition 1
(false network): In the process of network offensive and defensive confrontation under incomplete information, in order to interfere with the judgement and decision of the attacker from the observation link, the defender actively and selectively changes the structural information of the network by hiding part of information, adding false information and other means.
The false network is based on the characteristics of the real network model, so we first build the infrastructure network model. In this paper, the multi-coupling dependent network model of infrastructure network is constructed on the basis of functional factor network and organizational structure network, combined with node function and network topology21. The multi-coupling dependent network model consists of two single-layer networks A and B, including the nodes, the connected edges within the nodes and the multi-coupled edges between sub-networks, as shown in the Fig. 1.
The multi-coupling dependent network model of infrastructure network.
The nodes in the network have individual differences, and the nodes have different information processing ability. There are many-to-one multi-coupled interdependencies between sub-network A and B. Multiple nodes of sub-network A can depend on a single node of sub-network B at the same time. The coupled edge between sub-networks is directed edge, and the information is processed by the coupled edge flowing from sub-network A to B.
Based on the node set V and the edge set E of graph G, the network model adds the dependency relation between nodes to set E, and together forms the connected edge and the coupled edge between nodes of the same sub-network, and the weight of nodes is added to the edge, which is described by \(G = (V, E, W)\). The weighted edge set E and the weighted adjacency matrix W are used to represent the connections between nodes in a complex network.
In order to facilitate the theoretical analysis, the weights on both sides of the network are set to be the same. Node set \(V=V_A \cup V_B\) is a non-empty set representing the sum of \(N_A\) nodes of sub-network A and \(N_B\) nodes of sub-network B, in which the node \(V_A = \{ v_i^A | i = 1,2,\cdots ,N_A\}\), node \(V_B = \{ v_k^B | k = 1,2,\cdots ,N_B\}\). Similarly, the edge set \(E = E_{INTER} \cup E_{INTRA}\) is also a non-empty set, representing the combination of the connected edge \(E_{INTER}\) and the coupled edge \(E_{INTRA}\) in the network, in which \(E_{INTER}\) is the connected edge set in the sub-network A and B, \(E_{INTER}=\{e^A_{ij} | i,j\in V_A, k,l \in V_B\}\), and the coupled edge between sub-networks is \(E_{INTRA}=\{E_{ik}^{AB} | i \in V_A, k \in V_B\}\).
On the basis of network G, keep the nodes in the network unchanged, and construct the false network \(G_C=(V_C, E_C)\) by hiding the existing edge \(E_H\) and adding the false edge \(E_A\), in which \(V_C = V, E_C = (E - E_H) \cup E_A\). After the attacker has mastered the information of the defender’s network structure, they will make the attack strategy according to the feature of the false network structure. The purpose of false network is to make the attack target is not the fragile node or important node of the original network, and the attack strategy has little effect on the network performance. In the process of constructing the false network, there is a purposeful false information which is transmitted by the defender to the attacker, which is caused by deliberate interference and inducton. In order to ensure the credibility of false network, the false network must be able to convey the feature of the original real network, means the formation of the network depends on the real network.
Real networks generate false networks by adding false edges and deleting real edges at random or rule. A simple example illustrates the process of generating false networks, as shown in the Fig. 2. The real network in the graph contains 12 nodes and 14 edges, the nodes are marked yellow, the real edges are deleted and the false edges are marked red dotted line and red solid line respectively, and the black nodes are the nodes of the false network. Figure 2 shows the attack nodes selected by the attacker under the two strategies. The table in the upper right corner of the figure lists the attack nodes of the attacker in the real network and in the disguised network. Under the camouflage network, the attack nodes (such as nodes 3, 4, and 8) are completely different from the attack nodes in the real network, demonstrating the effectiveness of the camouflage network in protecting the real network.
False network construction process and attack nodes selection.
At present, the information of false network structure is constructed by random method and rule method can protect the origin network structure, but the controllability is too low, and it is difficult to cope with different attack strategies, and the constructed false network may not conform to the characteristics of the real infrastructure network. To make matters worse, the network contains a large number of complex relationships between functional nodes, and there are many hidden network features that have not been discovered. Therefore, in order to make the false network more confusing and reduce the attack effect by moving fewer edges, the first-order logical rule set was initially considered to build the false network, because they can be interpreted, but this method requires manual writing of rules, and the efficiency is low, while the neural network based on structural similarity can better depict the network structure characteristics, and the computational complexity is low. It could be a new way to build a false network.
Based on our previous work, this paper builds a false network22 with the of graph convolution neural network model. Firstly, the multi-coupled dependent network model of infrastructure network is established. On this basis, the ratio of target network and missing information is determined by removing and increasing the edges. Furthermore, the Logical default Attention Graph Convolution Neural Network(DA-GCN) restores the missing information of the target network, classifies the predicted edges to form false strategy, and finally obtains the false network. The steps to generate a false network are divided into four: 1) Input the adjacency matrix of the real network G; 2) Predict edge classification through the DA-GCN model (based on node feature convolution); 3) The edges with a probability greater than 0.8 are output as the false edge set (\(E_A\)), and the true edge set (\(E_H\)) with a probability less than 0.8 is hidden. This value was selected based on a trade-off between the credibility of the false network (keeping it realistic) and the effectiveness of deception (changing enough edges). Lower thresholds introduce too much noise, while higher thresholds fail to hide critical vulnerabilities; 4) Generate a false network \(G_C =(V,(E - E_H)\cup E_A)\).
Game modeling
The offensive and defensive adversarial model of infrastructure network is a model used to describe and analyze the strategic interaction and reaction relationship between attackers and defenders. The defensive strategy may trigger the change of the attack strategy, and the attack strategy may force the adjustment of the defense strategy. By analyzing the attacker’s strategy preference, the game judges its own optimal strategy, affects the defender’s protection resource allocation, and protects its own node.
This interaction is similar to the leader-follower interaction in Stackelberg games, where the attacker is the leader in the game and the defender is the follower. In the process of Stackelberg game modeling, participants, strategy sets and effect functions are generally formalized, and then the optimal strategies of defenders and attackers, as well as corresponding utility values and other related issues can be obtained by solving the game model. And the attack and defense strategy, cost constraints and benefits will be defined below.
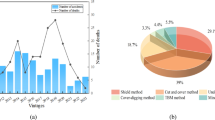
Attack and defense strategy
Based on Stackelberg game model, the defender will adopt his mixed strategy without commitment at first, and then actively reveals the strategy, forcing the attacker to choose a pure strategy. The strategy needs to satisfy the constraint of offensive and defensive resources. With the increase of the number of nodes in the network, the strategy sets also increase, and the game under the interaction of strategies results in a larger scale of the strategy return matrix, making it very difficult to solve the equilibrium23. Rational attacker and defender do not formulate strageties randomly, attacking the vulnerable part according to certain rules. In literature24, we choose degree attack, betweenness attack and vulnerable attack methods for experiments. These methods are the most widely used in current network attack strategies, and most other attack strategies are variants or combinations of the above basic strategies. And the experimental results show that the degree attack method can reduce the absolute capability of the network, and the vulnerable attack method has a relatively efficient cost ratio. Therefore, we defines three kind strategies that can be chosen in the game based on degree attack and vulnerable attack.
-
1.
Attack Strategy 1 (DA) Attack strategy one is the degree attack, which is sorted according to the node degree value in the network, and select part of nodes to attack. Attackers who choose the DA strategy usually does not consider the problem of attack resources, hoping to reduce the system capabilities to the greatest extent. In order to avoid the inconsistency of attack resource allocation, we specify the total resource setting under different attack methods. The attack resource is related to the cost of the node, and the total attack cost is the base cost according to the vulnerable attack method. The total attack resource of the selected node is greater than the base cost, but after removing one node with the least attack cost, the attack cost of the method is less than the total attack resource, and finally the node under the three attack methods can be obtained.
-
2.
Attack Strategy 2 (PA) The attack strategy two first selects the vulnerable node set in the network to attack, the vulnerable node is a suitable control matrix composed of the least number of nodes, and has the minimum control cost23. Vulnerable nodes can be obtained by using the exact controllability method proposed by Popov-Belevitch-Hautus (PBH)25. Vulnerable attack method aims to attack the vulnerable nodes of the network centrally at the same time. On this basis, the remaining resources are selected to attack some height-value nodes according to the degree value order from large to small. PA strategy combines the advantages of degree attack and vulnerable attack. The attacker who choose PA strategy is usually limited to certain attack resources, but hopes that the remaining resources can achieve better attack effect.
-
3.
Attack Strategy 3 (NA) Similar to PA strategy, attack strategy 3 also selects the vulnerable attack method first, but different from it, the strategy selects nodes with low degree values in the order of degree from small to large to attack. NA strategy is an extension of the vulnerable attack method. The attacker who chooses NA strategy attacks more nodes with the remaining resources after the vulnerable attack, hoping to achieve the maximum cost-effectiveness ratio of the attack method.
Attack and defense cost
Resource cost is generally positively correlated with the importance of nodes14, and the attack cost of nodes is the cost of failure nodes caused by attacks. Node degree value reflects the importance of nodes13 to a certain extent. Therefore, on the basis of directed network, the attack cost of nodes is measured by degree value, the greater the degree, the more the edges of nodes are connected, the wider impact on the network, and the more difficult the attack is. Similarly, the defense cost refers to the resource cost that the defender needs to deal with an attack to prevent the node from failing, and the value is same with the attack cost. Therefore, the attack cost of node \(Dv_i\) and the resource cost of defense are expressed as \(c^A_i\) and \(c_i^D\) respectively.
Among them, \(\alpha _1\in \left[ 0,1\right]\) is the eigennumber (weight), and \(\beta _1\in \left[ 0,\infty \right]\) is the characteristic phase (scaling exponent), which are adjustable parameter number sensitivity to node degree. \(k_i = k_{i_{in}} + k_{i_{out}}\) is the sum of the in-degree and out-degree of the node, and \(f[\cdot ]\) indicates that global normalization is performed.
The interaction between nodes should be considered in the game. When the attacker chooses the attack strategy \(s_j \in S^A\), the strategy set \(s_j =[a_1, a_2, \cdots , a_N]\) for the multi-coupling dependent network can be obtained. When \(a_i = 1\), the node \(v_i\) will be attacked. Otherwise, \(a_i = 0\). In the same way, we define the defensive strategy set using the mixed strategy \(s_i \in S^D\) as \(s_i =[d_1, d_2, \cdots , d_N]\), where \(d_i = 1\) means that the node \(v_i\) in the selected network is defended, otherwise, \(d_i = 0\). Attackers and defenders act according to their respective strategies and available resources, \(R^D\) and \(R^A\). When a single node is attacked and invalidated, it is necessary to remove the node and its connected edges, which may cause the cascading failure of the network. The choice of the defender strategy should consider the occurrence of cascading failures. \(C^D\) and \(C^A\) are used to represent the total cost of offensive and defensive strategy, as shown in Eqs. (2) and (3).
The attacker should take no less than the cost of node damage to attack. If the node is not a defense node, \(d_i = 1\), the attack is successful, and the node and its connected edges are removed from the network. On the contrary, if the node is a defense node, the attack fails and the node is not removed. Therefore, measuring attack success rate \(\eta _i\) based on the resource cost paied by the attacker to node \(v_i\), we define the probability of the successful attack on the non-defensive node to failure as the formula.
Among them, \(r_i^A\) is the cost of attack the node \(v_i\), \(r_i^D\) is the defense resource cost of the node \(v_i\). The total resources \(C^D\) and \(C^A\) are distributed across nodes according to the selected attack/defense strategies.
Attack and defense benefit
Considering the load redistribution process, when the attacker attacks the node, the unprotected node will fail, and at the same time the cascading failure of the network will lead to the failure of the isolated nodes. The protected node will face two situations: when the distributed defense resource is not less than the attack cost, the node will run normally but the attack fails. On the other hand, the node fails, but the network does have cascading failure. Thus, the benefit of the defender comes from 3 aspects:
-
(1)
the attacker attacks the nodes that have been defended;
-
(2)
defends the node where the cascade failed;
-
(3)
the isolated nodes are defended.
Cascades are triggered when an attacked node fails (if unprotected), leading to load redistribution. This may cause isolated nodes to fail sequentially. The payoff (Eqs. 5-6) scores the outcome by comparing the giant mutually connected component before and after the game. When the defender adopt the mixed strategy \(s_i \in S^D\) and the attackers adopt the pure strategy \(s_j \in S^A\). The calculation of the utility functions \(U_D\) and \(U_A\) is based on Eqs. (5) and (6). Among them, \(U_D\) measures the defender’s benefit (the retention rate of network hyperconnectivity components), and \(U_A\) measures the attacker’s benefit (the component failure rate). \(CP_i\) represents the capacity of node i, \(L_i\) is the load loss, and the giant mutually connected component is the largest connected subset of functional nodes.
Where \(\overset{\scriptscriptstyle \frown }{G}\) is the giant mutually connected component of the defender network after the game has reached equilibrium.
Based on the above method, the benefit matrix of the attacker and the defender under all strategy interactions \(|S^A \times S^D|\) can be obtained, as shown in Table 1. \(U_D (s_i, s_j)\) and \(U_A (s_i, s_j)\) respectively indicate that the defender and the attacker’s final benefits when the defender takes the strategy \(s_i\) and the attacker takes the strategy \(s_j\).
Strong \(\varepsilon\) equilibrium under Bayesian Stackelberg game
Bayesian game based on multi-type attacker
No matter how the antagonistic style evolves, the study of the opponent is the basic premise of winning, and different comparative advantages should be set for different types of attackers. Facing different types of attackers, defenders establish beliefs about the types of attackers based on previous experience and observation, and formulate corresponding strategies according to these beliefs. Therefore, this paper chooses Bayesian Stackelberg game to describe the network attack and defense process of the network offensive and defensive confrontation26.
The Bayesian Stackelberg game model is a Stackelberg game model in which the defenders face different types of attackers at the same time. The defenders only know the prior probability of different types of attackers, and use the incomplete information to make strategies, while the strategy of the attackers is based on the belief of the defenders. The type of the attacker is derived from the attacker’s measurement of the maximum destructive capability, and the measurement methods are divided into 2 types: 1) the giant mutually connected component of the network; 2) the sum of the maximum capacity of nodes before and after the network change. Method one corresponds to the instant type of short-term attacker ST, hoping to reduce the network’s current maximum ability, method two corresponds to the long-term type of long-term attacker LT, hoping to reduce the network’s potential capability. We use set \(H = \{ST, LT\}\) to denote the set of attacker types, \(P = \{p^S, p^L\}\) is defined as the prior probability of different types of attackers, \(p^S + p^L = 1\).
For a given attacker type \(h \in H\), the corresponding defender will takes a strategy, and the benefit function of the attacker is \(U_D^h (s_i, s_j)\). The attacker benefit function calculation method is different for different type of attackers. When the attacker take \({s_j}\) strategy, ST attacker benefit function is \(U_A^S (s_i, s_j)\), LT attacker benefit function is \(U_A^L (s_i, s_j)\), and the \(U_A^L\) calculation method is shown in the Eq. (7).
Where \(V_{remove}\) is the node set that are in a failed state and failed to redistribute the load.
Similarly, according to the above method, the benefit matrix of the defender and the two attackers under all strategy interactions can be obtained, as shown in the Fig. 3.
Payoff matrix of Bayesian Stackelberg game.
This game is non-zero-sum because the gain targets of attackers and defenders are independent. The non-zero-sum feature allows bounded rational behavior to influence strategies.
Strong \(\varepsilon\) equilibrium based on irrational attacker
The most common game equilibrium is Nash equilibrium. Nash equilibrium is a non-cooperative game equilibrium in which the defender and the attacker have no motivation to change their strategy, because neither player can change his strategy to get better results27. Stackelberg equilibrium is a special modification of Nash equilibrium in Stackelberg game. Each player chooses the optimal response under any subgame of the original game, thus eliminating the Nash equilibrium distribution supported by the non-credible threat that deviates from the equilibrium path. However, followers may not care about certain strategies, the perfect equilibrium of individual subgame does not guarantee the uniqueness of the game equilibrium. Therefore, with the support of “breaking tie”, two special Stackelberg equilibria are proposed by Litmann28 and Breton29. One is Strong Stackelberg Equilibrium(SSE), in which the followers always choose the best strategy for the leader and exist in all Stackelberg games, while the weak Stackelberg equilibrium does not necessarily exist, in which the followers choose the worst strategy for the leader30. In view of the existence of SSE and its universality in literatures31, we chooses SSE as the solution concept.
Under Stackelberg equilibrium the benefit of the defender can be guaranteed to be no less than that under the Nash equilibrium, the defender gains the so-called first advantage.The highest defender benefit is at least the same as the Nash equilibrium achieved by the game participants at this time, so this paper defines the strong Stackelberg equilibrium of network offensive and defensive confrontation on the basis of SSE.
Definition 2
(Strong Stackelberg Equilibrium): In the Stackelberg game based on network offensive and defensive confrontation, the defender induces the attacker to strictly prefer the equilibrium strategy by choosing a strategy that is close to the desired equilibrium strategy, and choose the strategy that is more favorable to the defender when there is no differences between the two strategies.
After the attacker observes the defender’s strategy \(s_i \in S^D\), selects the strategy \(s_j \in S^A\) and finally achieves the strong Stackelberg equilibrium solution \((s_i^*, s_j^*)\), which generalized a pair of strategy combinations under strong Stackelberg equilibrium. The following 3 conditions should be satisfied to achieve the equilibrium:
-
1.
The defender performs the best response: \({{U}_{D}}(s_{i}^{*},{{s}_{j}})\ge {{U}_{D}}({{s}_{i}},s_{j}^{*})\)
-
2.
The attacker performs the best response: \({{U}_{A}}({{s}_{i}},s_{j}^{*})\ge {{U}_{A}}({{s}_{i}},{{s}_{j}})\)
-
3.
The attacker chooses the strategy that is most beneficial to the defender when there is a draw: \({{U}_{D}}(s_{i}^{*},s_{j}^{*})\ge {{U}_{D}}({{s}_{i}},s_{j}^{*})\)
Among them, \(s_i^*\) and \(s_j^*\) are the best coping set for the defender and the attacker, respectively.
As one of the important factors affecting the result of confrontation, the rational degree of players is the decision making basis for the best response to the change of offensive and defensive situation. In the course of operation, rational behavior can optimize the decision and maximize their own interests. In the decision-making process, the attacker will consider various factors and choose the best action. Through rational decision-making, the risk and uncertainty can be reduced, the attack efficiency and success probability can be improved , and the attack cost can be reduced. In reality, the attacker may face some problems such as incomplete information, cognitive limitation, decision time limit, and may adopt heuristics, rules or experience to make decisions, without necessarily carrying out comprehensive and detailed calculation and analysis, leading to bounded rational decisions. In addition, the rational degree of the attacker may involve many other factors, such as politics, history, culture, morality and so on.
In the previous game modeling process, it is assumed that the attacker is rational and can make the optimal strategy. However, if the attacker takes irrational or impulsive actions and chooses strategies that is not in line with the best interest due to irrational situations caused by various reason, then the rational strategy may not be able to adapt to the attacker’s behavior patterns. If the Stackelberg game equilibrium is solved according to the rational attacker strategy, it may bring unexpected huge losses to the defender. Therefore, in order to avoid more loss in the face of irrational attackers, we need to enlarge the scope of equilibrium, reduce the change of the defender’s benefit in the face of different rational attackers, and finally find the optimal strategy combination satisfying Stackelberg’s equilibrium. In the face of possible different types of attackers, when the defender takes the strategy \(s_i \in S^D\) and the attacker takes the strategy \(s_j \in S^A\), there exists the optimal response function \(T (s_i) = \arg \max \{p^S U_A^S (s_i, s_j) + p^L U_A^L(s_i, s_j)\}\), which results in a strong equilibrium solution \((s_i^*, s_j^*)\) of the Stackelberg game:
At this point, a problem is faced, the strong SSE overestimates the rationality of the attacker. In the actual game, the rational degree of the attacker is limited, and the limited observation of the defender strategy may make the suboptimal strategy that deviates from the expected optimal response, which may lead to the serious deviation of the defender strategy and the significant decrease of the actual benefit. Therefore, in order to solve this problem, we establish the strong \(\varepsilon\) equilibrium on the basis of \(\varepsilon\) equilibrium method of synchronous moving game[20]. Strong \(\varepsilon\) equilibrium extends SSE by incorporating a tolerance parameter \(\varepsilon\) to handle bounded rationality of attackers. When \(\varepsilon =0\), it reduces to SSE, assuming full rationality. For \(\varepsilon >0\) , it allows attackers to choose any strategy within an \(\varepsilon\)-deviation from the optimal response, simulating real-world decision biases.
The strong \(\varepsilon\) equilibrium is a game equilibrium that only considers the change of the attacker’s rational degree on the basis of the defender’s complete rationality. The strong \(\varepsilon\) equilibrium is not a fixed equilibrium point, but an optimal solution set, which means that the attacker can choose any stragety response within the range of the solution set. For a given defender strategy \(s_i \in S^D\) has:
Assuming that the attacker is bounded rational, and will not necessarily fully adopt a utility-maximized response strategy,then for any \(\varepsilon \ge 0\), the strong \(\varepsilon\) equilibrium is:
On this basis, strong \(\varepsilon\) equilibrium can be obtained. When \(\varepsilon =0\), strong \(\varepsilon\) reduces to SSE. For \(\varepsilon >0\), it accommodates attacker irrationality. In the form of the strong equilibrium definition of the Stackelberg game, there are the following definitions:
Definition 3
Definition (strong \(\varepsilon\) equilibrium): For a given \(\varepsilon \ge 0\), the defender strategy \(s_i \in S^D\), the existence of an attacker’s optimal stragety set \(s_j (s_i, \varepsilon )\), the strong \(\varepsilon\) equilibrium \((s_i^*, s_j^*)\) of Bayesian Stackelberg game is obtained as follows:
The design of strong \(\varepsilon\) equilibrium is used to handle the non-optimal response of attackers caused by information asymmetry or cognitive bias. Specifically, \(\varepsilon\) tolerance simulates the decision-making bias of real attackers. Using the network offensive and defensive confrontation to protect infrastructure needs to avoid the worst result from irrational attackers, and is more in line with the best interest of defenders. Given multiple optimal responses belonging to the \(\varepsilon\) equilibrium, the strong \(\varepsilon\) equilibrium considers the strategy with the lowest benefit for the defender and can prevent the worst result.
Strong \(\varepsilon\) equilibrium of game
After the attacker and the defender have chosen their respective strategies, based on the cascading failure model we designed in our previous work24, we can get the revenue matrix of the defender and two types of attackers, and then use an efficient and accurate method, DOBSS (Decomposed Optimal Bayesian Stackelberg Solver), to calculate the strong \(\varepsilon\) equilibrium of Bayesian Stackelberg game. Compared with the original model, the MILP adds descriptions of multiple types of attackers and introduces \(\varepsilon\) constraints to handle the irrational responses of attackers.
The game is defined as four-element group (\(S^A\), \(S^D\), \(U_A^h\), \(U_D\)), in which \(S^A\) is the strategy set of the attacker, \(S^D\) is the strategy set of the defender, \(U_A^h: S^A \times S^D \rightarrow R\) is the benefit function of the attacker of the h type, \(U_D: S^A \times S^D \rightarrow R\) is the benefit function of the defender. H is a collection of possible attacker types, and P is the prior probability that different types of attackers may appear.
In order to eliminate the nonlinearity of the function, the quadratic programming problem is linearized by the variable \(\delta _{ij}^h = d_{s_i} a^h_{s_j}\), and the strong \(\varepsilon\) equilibrium of Bayesian Stackelberg game is solved by the mixed integer linear programming problem. \(a^h_{s_j}\) is the probability of optimal strategies with an attacker of type h, variable \(b^h_{s_j}\) is the probability of using the best strategy \(s_j\) with an attacker of type h, \(C^A\) and \(C^D\) are the total amount of resources available to the attacker and the defender, respectively. \(r_j^A\) is the amount of resources that the node \(v_j\) required to be distributed to other nodes in strategy \(s_j\), and \(r_i^D\) is the amount of resources that the node \(v_i\) in the defender’s strategy \(s_i\) needs to allocate. The prior probability of a defender facing an h type attacker is \(p^h\). At this point, the defender’s minimum benefit \(\delta\) is maximized, and the strong \(\varepsilon\) equilibrium of Bayesian Stackelberg game is solved:
We have added Table 2, which provides a comprehensive summary of all key variables used in the MILP model. The core variables were previously introduced and explained in the text surrounding the model formulation. However, the new table serves as a convenient reference that collects these definitions in one place, providing a clear overview for the reader.
Equation 14 and 17 ensure the \(\varepsilon\) optimal stragety is not less than 1. In Eq. 17, when \(a^h_j = 1\), Ph can be obtained to \(m^h-\sum \limits _{s_i\in S^D} U_A^h d_{s_i} \le \varepsilon\), which is consistent with the definition. Equation 15 and 16 ensure that \(b^l_j = 1\) can be obtained only if the stragety j is the optimal stragety of the type l attacker. Equation 16 is the optimal condition for all different types of attackers to solve linear programming problems, and two inequalities ensure that \(b_{s_j}^h = 1\) can be obtained only when the stragety \(s_j\) is the optimal stragety of the type h attacker. The left side of the inequality in Eq. 16 ensures that \(m^h \ge \sum \limits _{s_i\in S^D}U_A^h d_{s_i}\), which means that \(m^h\) is the upper bound of the benefit that the type h attacker can get in the defensive strategy distribution. On the right side of the inequality, it always holds when \(a^h_{s_j} = 0\), because M is a large positive number. And for \(b^h_{s_j} = 1\), \(m_h \le \sum \limits _{s_i\in S^D}U_A^h d_{s_i}\) can be obtained. Combined with the previous inequalities, it shows that the current strategy is optimal for h type attackers. Equation 16–18 enforce the \(\varepsilon\)-optimal response set. Specifically, Eq. 16 ensures that the attacker’s strategy is within \(\varepsilon\) of the optimal payoff, while Eq. 18 selects the response that minimizes the defender’s benefit when ties occur. Finally, Eq. 19 is central to the defender’s objective, as it defines \(\delta ^h\) as the minimum defender utility over the attacker’s \(\varepsilon\) optimal responses, which is then maximized in the objective Eq. 12. This constraint mapping clarifies how the mathematical formulation implements the theoretical game model. This implements the tie-breaking rule where the defender prepares for the worst-case scenario. Equation 20 and 21 define the maximum resources for the attacker and defenders. In addition, the defender is rational, each optimal strategy for the attacker produces an optimal defense strategy, and Eq. 18 defines \(\delta ^h\) as the smallest of benefit in the defender’s alternative strategy.
Experimental analysis
In this section, based on Stackelberg game model, we first analyze and verify the effectiveness of strong \(\varepsilon\) equilibrium. Furthermore, we obtain the setting method of defense strategy under the Bayesian probability framework. Finally, based on the game model, we analyze the validity of the false network construction algorithm. Combined with the above game model and algorithm, we set up a detailed simulation experiment to verify the effectiveness of false network in offensive and defensive confrontation. The experimental environment is set up as a multi-coupling dependent network consisting of 500 nodes described in Section False network. Simulate the different types of attack patterns described in Section Attack and defense strategy and dynamically adjust defense strategies based on Bayesian probabilities. The experimental steps include initializing the network, simulating the attack, analyzing the game strategy, and recording the return.
Verification and analysis of game model
The multi-coupling dependent network have 500 nodes. Based on the game model, the change of the attacker’s strong \(\varepsilon\) equilibrium and strategy to the player benefit is analyzed through 1000 independent repeated experiments.
Analysis the influence of strong \(\varepsilon\) equilibrium
When \(\varepsilon\) is 0, the strong \(\varepsilon\) equilibrium is equal to Nash equilibrium. Therefore, the advantage of strong \(\varepsilon\) equilibrium is demonstrated by comparing the benefits of the defenders under Nash equilibrium and strong \(\varepsilon\) equilibrium. In addition, by setting different \(\varepsilon > 0\), the influence of \(\varepsilon\) value on the strong \(\varepsilon\) equilibrium is analyzed by observing the change of the defender’s benefit in rational and irrational situations.
(1) Comparison of Nash Equilibrium Results
The dynamic \(\varepsilon\) value is set in the experiment, and \(f_n (\varepsilon )\) is used to indicate that the number of strategies included under the \(\varepsilon\) value is n.
In the face of different types of attackers, \(f_n (\varepsilon )\) and the change of the available resources are used to compare and analyze the benefits under Nash equilibrium and strong \(\varepsilon\) equilibrium. The experiment results are shown in the Fig. 4, where available resources refer to the proportion of the current available resources in the total cost of all nodes.
Comparison of defender benefits with available resources and \(\varepsilon\) under two equilibria.
Figures 4a and 4b show the minimum benefits of the defenders under two equilibrium strategies as the available resources and \(f_n (\varepsilon )\) change against the irrational attackers of type ST and LT. With the increase of available resources, the defender’s benefit decreases first and then increases in the overall trend, and the minimum value of strong \(\varepsilon\) equilibrium is higher than that of Nash equilibrium.
(2) Confronting Rational Attacker Results
In the face of two types of attackers in the completely rational situations, ST and LT type, with the change of \(f_n (\varepsilon )\) and the available resources, the benefit value of the defender changes as shown in the Fig. 5.
The result of the defender benefits against the rational attacker varying with available resources and \(\varepsilon\).
In the case of ST type attacker, with the increase of available resources, the change of defender’s benefit decreases first and then increases.
In the case of LT type attacker, the change of the defender’s benefit is more moderate, especially when the available resources are between 0.3 and 0.7, the difference decreases rapidly, perhaps because the change of attack strategy has no significant effect on the overall benefit. Horizontal comparison shows that with the increase of \(f_n (\varepsilon )\) in the same amount of available resources, the benefits of the defender decrease, indicating that the benefits are negatively correlated with the values of \(\varepsilon\).
(3) Confronted with irrational Attacker Results
The strong \(\varepsilon\) equilibrium of the game is designed to avoid the huge loss of the defender benefit caused by the irrational attacker. By changing the rationality of the attacker, the experiment analyzes the change of the defender benefit, as shown in the Fig. 6.
The result of benefits change and benefits stability of the defender with \(\varepsilon\) and the attacker rationality.
Figures 6a and 6c are the highest and lowest benefit averages obtained by the defenders under all available resources. With the increase of \(f_n (\varepsilon )\), the maximum and minimum benefits of the defender are increased first and then decreased with different degree of rationality. At the same time, continue to observe the difference between the highest and lowest benefits, as shown in Figs. 6b and 6d . With the increase of \(f_n (\varepsilon )\) and the rationality degree, the difference decreases, especially after \(f_n (\varepsilon )> 3\), which indicates that the larger \(f_n (\varepsilon )\) can bring the higher stability of benefit.
Compared with the Nash equilibrium, the strong \(\varepsilon\) equilibrium can effectively increase the minimum benefit of the defender and prevent the irrational attacker from bringing huge loss to the defender’s benefit. The appropriate \(\varepsilon\) value is a strategy to balance the competitive relationship between the defender and the attacker. With the decrease of the defender’s maximum benefit, exchange the increase of the minimum benefit and the stability of the overall benefit, to ensure higher security and defense effect.
Strong \(\varepsilon\) equilibrium under bayesian probability
In the face of different available resources, the defender sets the pretest probability of the attacker’s rational degree to 0.1, calculates the benefit matrix of the defender and two types of attackers, then obtains the mixed strategy of the defender and the pure strategy of the two types attackers under strong \(\varepsilon\) equilibrium by the quadratic programming problem.
In order to comprehensively evaluate the effect of defense strategies under different information distributions and reduce the amount of computation, we choose three Bayesian probability scenarios for analysis. Use \(p^S = 0.5, p^L = 0.5\) symmetric information for benchmarking, the defender’s equilibrium strategy against different types of attackers is basically the same as with single type of attacker. Furthermore, the strong \(\varepsilon\) equilibrium of Bayesian dynamic game under two types of attacker is obtained by setting the pretest probability \(p^S = 0.1, p^L = 0.9\), and \(p^S = 0.9, p^L = 0.1\), represent the information distribution in which the attacker and the defender have obvious advantages, and the performance of the defense strategy under such asymmetric information is evaluated. Based on the analysis results of the influence of the upper section on the \(\varepsilon\) value, the appropriate dynamic \(\varepsilon\) value is selected to make \(f_n (\varepsilon )=4\).
When \(p^S = 0.1, p^L = 0.9\), the probability of ST type attacker is small, while the probability of LT type attacker is large. With the increase of available resources, the mixed strategy (DA, PA, NA) of the defender is obtained, as shown in the figure. When \(p^S = 0.9, p^L = 0.1\), ST type attacker have a high probability of occurrence, while LT type attacker have a low probability of occurrence, and the defense’s mixed strategy is shown in the Fig. 8.
The result of the defender’s mixed strategy changing with available resources under \({{p}^{S}}=0.1,{{p}^{L}}=0.9\).
The result of the defender’s mixed strategy changing with available resources under \({{p}^{S}}=0.9,{{p}^{L}}=0.1\).
By comparing the Fig. 7a and Fig. 8a , Fig. 7b and Fig. 8b , Fig. 7c and Fig. 8c , the probability of adopting DA strategy is higher when the ratio of available resources is within 0.3 to 0.7, and the probability value is above 0.7. When the ratio of available resources is not in the range of 0.3-0.7, Fig. 7c shows that the probability of a defender choosing a NA strategy is greater, and the probability of choosing NA strategy is above 0.5 in 24/56, and that of choosing PA strategy is above 0.5 in 24/56 in Fig. 7b . At this point, the defender’s expected benefits are at a minimum of 0.663, with a maximum of 0.679. In contrast, under the condition of \(p^S = 0.9, p^L = 0.1\), the defender has a greater probability of choosing PA strategy as shown in Fig. 8b , and 27/56 of the defenders choose PA strategy above 0.5, and only 12/56 of the defenders choose NA strategy over 0.5 in Fig. 8c . Defender’s benefit expectation minimum is 0.683, the maximum is 0.698.
ST type and LT type attackers choose their respective attack strategies after mastering the mixed strategy promised by the defender, and then achieve the strong \(\varepsilon\) equilibrium. Under the condition that the prior probability of the two types of attackers is fixed, the attacker adopts the strategy as shown in the Fig. 9.
The pure strategy result of ST and LT attackers changing with the available resources.
In Fig. 9a , when the available resources of both attacker and the defender are generally within the range of 0.3-0.7, the ST type attacker mainly chooses the NA strategy. When the available resources of the attacker are less than 0.3 and the available resources of the defender are less than 0.7, the attack strategy of the ST type attacker is mainly PA strategy. And in other cases, the DA strategy is the main one. Figure 9b shows that the attack strategy of LT type attackers can also be divided into three categories according to the available resources: the available resources are less than 0.3, the LT type attackers mainly adopt PA strategy. When the attack resources are 0.3, the basic all adopt NA strategy. And the attack resources are more than 0.7, the LT type attackers mainly use DA strategy. Compared with Fig. 9a and Fig. 9b , when the attack resource is greater than 0.3, the defense resource is less than 0.3 or the attack resource is less than 0.7, and the defense resource is greater than 0.7, the ST type attackers mainly adopt DA strategy, the LT type attackers choose DA strategy, and different attackers adopt different strategies.
In the face of irrational attackers, when the defenders adopt a mixed strategy, they can improve the benefit expectation and benefit stability of the defenders through strong \(\varepsilon\) equilibrium, and prevent the worst benefit from happening. It is necessary to adopt Bayesian Stackelberg game model when the defense and attack resources are not equal. At the same time, the strageties that different types of attackers and defenders may adopt under different available offensive and defensive resources are also obtained, which is of reference significance for the defenders to distribute limited defense resources.
Verification and analysis of false network
Based on the random method, the rule integration method and the method of this paper, we get the false network and carry out the game.
Based on the logical default attention graph convolution neural network model, the real network can be input into the trained network model, and then all nodes pairs can be output to form a false network. The output edges include two types, existing edges and non-existent edges. By comparing with the real network, the classification of edges can be easily completed, and the edges need to be deleted and added in the original network can be obtained.
In order to illustrate the advantages of the false network construction method, the experimental results are compared with those obtained by random and degree methods. Based on the Bayesian Stackelberg game model, the attacker observed that the false network designed the attack strategy, and the defender designed the defense strategy based on the real network, and got the result of the attack-defense game.
The strong \(\varepsilon\) equilibrium of Bayesian Stackelberg game with long-term and instant types is obtained by setting the pretest probability \(p^S = 0.1, p^L = 0.9\); \(p^S = 0.5, p^L = 0.5\) and \(p^S = 0.9, p^L = 0.1\). The Fig. 10 is the benefit of the defender facing two types of fully rational attackers under different available resources.
A comparison of the defender benefits with available resources under different false network generate methods.
In general, as the resources available to the attacker and the defender increase, compared with the other two methods, the defender gains the most from this chapter’s false network-building approach. In addition, the average number of moving edges is 700, 657 and 630 when the random method, the method and the degree method are used to construct the false network. The cost of adjusting the structure of the method is between the other two methods. Compared with the random method, the cost can be reduced by about 6.14%, and the average gain can be increased by 3.96%, although the cost is increased by 4.28% compared with the degree method. But the average gain of 5.43% indicates that the cost-effectiveness ratio of the method in this paper is the highest.
Compared with the results of the non-false network, the maximum benefit of the defender increased by 32.52% when the available resources were between 0.3 and 0.7. At the same time, in the face of different battle architecture defense strategies, this method can effectively improve the use efficiency of limited network defense resources, and the cost-effectiveness ratio can be increased by 37.44%. The false network based on logical default attention map convolution network can improve the defender’s benefit and reduce the network’s vulnerability at lower false cost.
Conclusion
In the network attack and defense confrontation, how to reduce the frailty of their own architecture and gain more benefits is a challenging practical problem. Based on the advantage of game theory, this paper solves the problems of incomplete information, more types of attackers and less rational degree, and provides decision-making support for the active protection of infrastructure network.
Based on the Stackelberg game model, a Bayesian Stackelberg game model based on false network is constructed. Construct false network based on logical default attention map convolution network, break the limitation problem of network reset, so that the defender can take advantage of asymmetric information and gain “first-mover advantage” at the same time. Based on Bayesian prior probability game, the case of multi-type attackers is considered, and the worst result of non-rational attackers is avoided by strong \(\varepsilon\) equilibrium solution. Finally, the strategy preference of the defenders and attackers under different available resources is obtained by solving the game model, which provides reference for the resource allocation of the defenders. The simulation experiment shows that this method can effectively transfer the attack damage, thus protecting the infrastructure network and improving the overall defense capability of the network.
The defense department releases false information about the infrastructure network to the terrorists, allowing them to choose the target of attack in the false network, while releasing some false defense plans to strengthen the protection of key nodes. Although false networks have significant defensive advantages in theory, in practice, defenders may face the challenge of attackers analyzing disinformation through deep learning techniques or large-scale computing. Future research should focus on how to improve the dynamic adaptability and anti-jamming ability of false networks to cope with more complex attack strategies.
Data availability
The datasets used and/or analysed during the current study available from the corresponding author on reasonable request.
References
Dekker, A.H. & Colbert, B. D. Scale-free networks and robustness of critical infrastructure networks, in: 7th Asia-Pacific Conference on Complex Systems, p. 685–699. (2004)
Li, J. et al. Recent progress on cascading failures and recovery in interdependent networks. Int. J. Disaster Risk Reduct. 40, 101266 (2019).
Ezell, B. C., Bennett, S. P. & Von Winterfeldt, D. Probabilistic risk analysis and terrorism risk. Risk Anal.: Int. J. 30(4), 575–589 (2010).
Golany, B., Kaplan, E. H. & Marmur, A. Nature plays with dice-terrorists do not: Allocating resources to counter strategic versus probabilistic risks. Eur. J. Oper. Res. 192(1), 198–208 (2009).
Tweneboah-Koduah, S. & Buchanan, W. Security risk assessment of critical infrastructure systems: A comparative study. Comput. J. 61, 1–10 (2018).
Sochor, H., Ferrarotti, F. & Ramler, R. An architecture for automated security test case generation for mqtt systems. in: Database and Expert Systems Applications, pp. 48–62. (Cham, 2020)
Conitzer, M. & Sandholm, T. Computing the optimal strategy to commit to. In: Proceedings of the 7th ACM conference on Electronic commerce, pp. 82–90. (2006)
Iaiani, M., Sorichetti, R., Tugnoli, A. & Cozzani, V. Modelling standoff distances to prevent escalation in shooting attacks to tanks storing hazardous materials. Reliab. Eng. Syst. Saf. 241, 109689 (2024).
Zhou, J. et al. Three-layer and robust planning models to evaluate the strategies of defense layer, attack layer, and operation layer for optimal protection in natural gas pipeline network. Reliab. Eng. Syst. Saf. 249, 110196 (2024).
Zhang, W. Y. Game theory and information economics (Gezhi publishing house, Shanghai, 2012).
Li, Y. et al. Joint optimization of structure and protection of interdependent infrastructure networks. Reliab. Eng. Syst. Saf. 218, 108163 (2022).
Zhou, D. & Elmokashfi, A. Network recovery based on system crash early warning in a cascading failure model. Sci. Rep. 8(1), 7443 (2018).
Li, Y. P., Tan, S. Y. & Deng, Y. Attacker-defender game from a network science perspective. Chaos: Interdiscip. J. Nonlinear Sci. 28(5), 051102 (2018).
Li, Y., Qiao, S., Deng, Y. & Wu, J. Stackelberg game in critical infrastructures from a network science perspective. Phys. A: Stat. Mech. Appl. 521, 705–714 (2019).
Hu, Y., Ma, J., Guo, Y. & Zhang, H. Research on active defense based on multi-stage cyber deception game. J. Commun. 41(8), 32–42 (2020).
Fu, C. et al. Attack-defense game for critical infrastructure considering the cascade effect. Reliab. Eng. Syst. Saf. 216, 107958 (2021).
Zeng, C., Ren, B., Li, M., Liu, H. & Chen, J. Stackelberg game under asymmetric information in critical infrastructure system: From a complex network perspective. Chaos: Interdiscip. J. Nonlinear Sci. 29(8), 083129 (2019).
Pita, J., Jain, M. & Marecki, J. Deployed armor protection: The application of a game theoretic model for security at the los angeles international airport. In: Proceedings of the 7th international joint conference on Autonomous agents and multiagent systems: industrial track, pp. 125–132. (2008)
Tsai, J., Kiekintveld, C. & Ordonez, F. Iris-a tool for strategic security allocation in transportation networks. In: Proceedings of the Eighth International Conference on Autonomous Agents and Multiagent Systems, pp. 7–44. (2009)
Rinaldi, S., Peerenboom, J. & Kelly, T. Identifying, understanding, and analyzing critical infrastructure interdependencies. IEEE Control Syst. Mag. 21(6), 11–25 (2001).
Kammouh, O., Fecarotti, C. & Marandi, A. A scalable optimization approach to the intervention planning of complex interconnected infrastructures. Reliab. Eng. Syst. Saf. 250, 110281 (2024).
Zhang, J., Huang, J., Gao, J., Han, R. & Zhou, C. Knowledge graph embedding by logical-default attention graph convolution neural network for link prediction. Inf. Sci. 593, 201–215 (2022).
Yuan, Z., Zhao, C., Di, Z., Wang, W.-X. & Lai, Y.-C. Exact controllability of complex networks. Nat. Commun. 4(1), 2447. https://doi.org/10.1038/ncomms3447 (2013).
Zhang, J., Huang, J. & Zhang, Z. Analysis of the effect of node attack method on cascading failures in multi-layer directed networks. Chaos, Solitons & Fractals 168, 113156 (2023).
Zhang, J., Tang, B., Duan, Y. & Huang, J. Percolation phase transition in the heterogeneous multi-coupled interdependent network. Chaos, Solitons & Fractals 174, 113851 (2023).
Dong, M. et al. Playing bayesian stackelberg game model for optimizing the vulnerability level of security incident system in petrochemical plants. Reliab. Eng. Syst. Saf. 235, 109237 (2023).
Qi, G., Li, J., Xu, X., Chen, G. & Yang, K. An attack-defense game model in infrastructure networks under link hiding. Chaos: Interdiscip. J. Nonlinear Sci. 32(11), 113109 (2022).
Guo, Q., An, B. & Bosansky, B. Comparing strategic secrecy and stackelberg. In: Proceedings of the 26th International Joint Conference on Artificial Intelligence (IJCAI17), Melbourne Australia, p. 3691–3699. (2017)
Zeng, C., Ren, B. & Li, M. LI, On generalized stackelberg strategies. J. Optim. Theory Appl. 26(4), 637–643 (1978).
Breton, M., Alj, A. & Haurie, A. Sequential stackelberg equilibria in two-person games. J. Optim. Theory Appl. 59(1), 71–97 (1988).
Basar, T. & Olsder, G. J. Dynamic noncooperative game theory, Siam, (1999).
Acknowledgements
This work was supported by the National Natural Science Foundation of China No.72501224.
Author information
Authors and Affiliations
Contributions
Jiarui Zhang conducted the investigation and prepared the manuscript draft. Yinjun Gao was responsible for supervision. Weijie Kang and Yueer Li carried out validation and formal analysis. Wenli Tian prepared the visualizations. All authors reviewed and approved the final manuscript.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Zhang, J., Gao, Y., Kang, W. et al. Research on infrastructure network protection strategy based on bayesian stackelberg game under asymmetric conditions. Sci Rep 16, 7045 (2026). https://doi.org/10.1038/s41598-026-37843-x
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1038/s41598-026-37843-x