Abstract
Lithium niobate materials, which have the potential to fabricate lasers, modulation devices, and photodetectors, are widely used in quantum information processing due to their exceptional optical and electro-optical properties. However, the photorefractive effect in lithium niobate materials may cause the quantum device to deviate from its ideal operation model, which is an important assumption for the security of quantum key distribution. Here, we demonstrate the practical security of the continuous-variable quantum key distribution protocol under the photorefractive effect, where the eavesdropper Eve injects a 488 nm visible light into the source-side variable optical attenuator and excites the photorefractive effect phenomenon in a lithium-niobate-based dual-waveguide. In particular, we derive the photorefractive-effect-induced intensity change of a variable optical attenuator and then the corresponding parameter estimation process, showing the effectiveness of this attack for various irradiation powers and waveguide technologies (including proton-exchanged and annealed-proton-exchanged waveguides). To show its effect on practical continuous-variable quantum key distribution systems, we present the composable finite-size security of one-way continuous-variable quantum key distribution and continuous-variable measurement-device-independent quantum key distribution protocols. Numerical results show that this induced-photorefraction attack can break the security even with a low irradiation power, such as 3 \(\textrm{W}/\textrm{cm}^2\) (or about 0.21 \(\mathrm {\mu W}\)). In addition, we find that Eve’s optimal attack strategy against continuous-variable measurement-device-independent quantum key distribution is related to the information reconciliation process by comparing three different attack strategies. Finally, we discuss some possible countermeasures to resist induced-photorefraction attacks to enhance the security of the system.
Similar content being viewed by others
Introduction
Quantum key distribution (QKD) enables distant legitimate users to extract secure keys with theoretically unconditional security based on the fundamental principles of quantum mechanics1. Generally, QKD can be implemented by two schemes: discrete-variable (DV) QKD and continuous-variable (CV) QKD2. In detail, DV-QKD usually encodes the information on the polarization of a single photon, while CV-QKD encodes the information on the regular component of the optical field and detects the quantum state by coherent detection. Due to the advantages of a simple realization, high key-generation rate, and compatibility with current optical networks, CV-QKD has developed considerably in both security proof and experimental implementation recently3.
When performing security proof, some assumptions should be imposed on systems to ensure that the proof of protocol is valid4. For example, one of the most critical assumptions is that all devices of the two users should operate according to the ideal model. Otherwise, once one device deviates from its ideal model, a side channel is created, which can result in security loopholes. A well-known example is the security loopholes caused by tampering with the intensity or shape of the transmitted local oscillator (LO), such as saturation attack5, LO fluctuation attack6, etc. To resist these attacks, a real-time shot-noise measurement (RTSNM) scheme is proposed, where the signal is randomly applied strong attenuation7. However, even with RTSNM, the eavesdropper Eve can use the sensitivity of the beam splitter (BS) split ratio to the wavelength to tamper with shot-noise measurements without being detected8. After that, the local LO (LLO) scheme, which generates LO at the receiver, is proposed to close all the security loopholes related to the transmitted LO but needs additional phase reference pulse and thus has large phase noise9,10. Moreover, Ref.11 has shown that Eve can also tamperer the additional phase reference pulse of the LLO scheme for her attack. Note that device-independent (DI) QKD is the final solution to solve the side channel completely12. However, the construction of CV-DI-QKD requires the introduction of non-Gaussian operation, which increases the realization difficulty, and there is no relevant experimental research so far1,13. Another promising approach is the CV measurement-device-independent (MDI) QKD, which closes all the security loopholes related to the detectors14. The composable security of CV-MDI-QKD has been verified, and the complete experiment and data-processing have been realized in recent years15,16.
As the CV-MDI-QKD protocol closes all the detector-side loopholes, the attacks at the source side or side channel become the last piece that needs to be solved for practical security. A common method to create a source-side side channel is to inject light to cause the device to deviate from its ideal model. For example, Stiller et al.17 demonstrated that Eve can inject light pulses to the source side and then analyze the reflected light pulse signals for key information, i.e., the Trojan-horse attack. Huang et al. proposed laser damage attack and laser seeding attack, both of which inject light to the source side and open source-side loophole by changing modulation variance18,19. In detail, the laser damage attack changes the modulation variance by reducing the attenuation of the variable optical attenuator (VOA), while the laser seeding attack increases the intensity of the laser diode. More recently, Ye et al. proposed that injecting light and the photorefractive effect (PE) in Lithium niobate (LiNbO\(\vphantom{0}_3\), LN) device can be exploited as a source-side loophole to attack one-way DV-QKD and DV-MDI-QKD, which is called induced-photorefraction attack (IPA)20,21. Since PE is an intrinsic nature of LN material, this phenomenon occurs in all LN-based devices at the CV-QKD source, including amplitude modulators (AMs), phase modulators (PMs), polarization controllers (PCs), VOAs, etc. In addition to the devices above, recent studies have shown that LN materials also have the potential to fabricate lasers and photodetectors even if they belong to wide bandgap materials22,23. In other words, LN materials may appear throughout the CV-QKD system in the future.
Motivated by the findings above, this paper investigates the practical security of CV-QKD under the PE in LN material. Here, we select the LN-based VOA as an example because, from Eve’s perspective, VOA is the first device she accesses if she passes the isolator3. In detail, the LN waveguide of VOA is based on proton-exchanged or annealed-proton-exchanged fabrication technique, while the wavelength of Eve’s injected light is 488 nm, which belongs to the visible light region. Note that the waveguides based on the Ti-diffused, proton-exchanged and annealed-proton-exchanged technology are commonly used in QKD, while the case of Ti-diffused is discussed in Ref.20. We first reveal the mechanism of PE affecting VOA and then show its induced source-side loophole on both one-way CV-QKD and CV-MDI-QKD. Security analysis shows that combining the induced loophole with intercept-resend attacks can break security without being detected. Finally, we discuss some possible countermeasures to resist IPA to enhance the security of the system.
This paper is organized as follows. We first describe the details of PE and then show its effect on LN-based VOA. Next, the practical security of one-way CV-QKD and CV-MDI-QKD under the IPA is investigated. Then, we discuss the possible countermeasures to resist the IPA. Finally, the conclusion is presented.
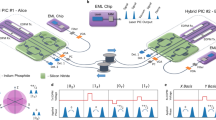
Schematic diagram of the IPA. (a) A typical source-side structure in CV-QKD under IPA. The yellow blocks of the VOA denote LN waveguides. IQmod: in-phase and quadrature electro-optic modulator; MBC: modulator bias controller; BS: beam splitter; PD: photo-diode; VOA: variable optical attenuator; \(I_{\textrm{in}}\): input intensity of the optical signals; \(I_{\textrm{out}}\): output intensity without irradiation; \(I^{\prime }_{\textrm{out}}\): output intensity under irradiation. (b) Schematic diagram of PE procedure in MZI. \(E_{\textrm{in}}\): amplitude of the input optical signals; \(E_{\textrm{out}}\): amplitude of the output optical signals; \(\theta _{\textrm{L}}\) and \(\theta _{\textrm{R}}\): phase shifts of the upper and lower waveguides, respectively.
The scheme
Fig. 1a shows a typical source-side structure in CV-QKD under IPA. In detail, the key information generated by Alice’s quantum random number generator is encoded in the initial light (generated by Laser 1) by an in-phase and quadrature electro-optic modulator (IQmod). Then, the encoded signal is split by a 99:1 BS, 1 % of the output is measured by a photo-diode (PD) and the result is returned to the modulator bias controller (MBC) to adjust the bias DC voltage of IQmod; 99 % of the output is transmitted to a LN-based VOA with a Mach-Zehnder interferometer (MZI) structure to attenuate the modulation variance to an expected value. Finally, the adjusted signal is transferred to Bob’s side for detection. To perform IPA, Eve uses a continuous-wave laser (Laser 2) to inject light into the VOA through a circulator. Under the irradiation of injected light, the VOA deviates from its ideal model due to PE, thus inducing a security loophole. In what follows, we first show the mechanism of PE and then reveal how it affects LN-based VOA.
The mechanism of PE
PE is the change in refractive index in the LN waveguide owing to the photoinduced redistribution of electrons and holes, as shown in Fig. 1b. Then, these excited charges move out of the waveguide through processes such as the photovoltaic effect, causing a photoinduced space-charge field. Finally, this space-charge field changes the refractive index of the waveguide by the so-called Pockels effect. In reality, the photoinduced index change does not occur immediately but requires a buildup time. Mathematically, the relation between the photoinduced index change and the irradiation time t is given by24
where \(\tau\) is the buildup time constant, \(\varDelta n_{\textrm{s}}\) denotes the saturated photorefractive index change, i.e., the photorefractive index change \(\Delta n( t)\) with \(t \rightarrow \infty\), which can be expressed as
where n is the waveguide refractive index at the signal wavelength, \(r_{33}\) is the Pockels coefficient, and \(E_{\textrm{s}}\) is the saturated space-charge field. Similarly, the saturated space-charge field \(E_{\textrm{s}}\) denotes the case that the space-charge field E(t) with \(t \rightarrow \infty\), which is given by25
where \(I_{\textrm{ir}}\) is the irradiation power, \(\sigma = \sigma _{\textrm{d}} + \sigma _{\textrm{ph}}\) with the dark conductivity \(\sigma _{\textrm{d}}\) and the photoconductivity \(\sigma _{\textrm{ph}}\), \(E_{\textrm{app}}\) is the applied electric field, \(\kappa\) is the Glass constant, and \(\alpha\) is the absorption coefficient of the donor or acceptor centers. When \(t \rightarrow \infty\), Eq. (3) evolves into the saturated space-charge field given by
Combining Eq. (4) and Eq.(2), the saturated photoinduced index change finally becomes
As shown in Eq. (5), beside the waveguide parameters and the constants, \(\Delta {n_\mathrm{{s}}}\) is affected by the irradiation power \(I_{\textrm{ir}}\) and the applied electric field \(E_\mathrm{{app}}\).
Let us further discuss the saturated photoinduced index change related to the irradiation power, which is controlled by Eve. When there is no applied electric field i.e., \(E_\mathrm{{app}}=0\), the saturated photoinduced index change evolves from Eq. (5) to
However, Eq. (6) fails to give an exact relationship between the saturated photoinduced index change and \(I_{\textrm{ir}}\). This is because the photoconductivity \(\sigma _{\textrm{ph}}\) is also related to the value of \(I_{\textrm{ir}}\)26. In detail, \(\sigma _{\textrm{ph}}\) and \(I_{\textrm{ir}}\) show a linear relationship with low irradiation power (lower than 100 \(\textrm{W}/\textrm{cm}^2\) or about 7 \(\mu \textrm{W}\)) while becoming a sub-linear relationship when the irradiation power is higher. In our manuscript, we consider the former case with the linear relationship because the less power Eve uses, the less likely it is to be detected or defended. We directly read Ref.27 for the higher irradiation case with the sub-linear relationship. Under a low irradiation power, the photoconductivity can be expressed as27
where a is a constant. Thus, Eq. (6) can be rewritten as
where \(A=n^{3}r_{33} \kappa \alpha /2 \sigma _{\textrm{d}}\), \(B=a\alpha /\sigma _{\textrm{d}}\). Note that the values of A and B are related to the fabrication techniques of optical waveguides. Generally, Ti-diffused, proton-exchanged, and annealed-proton-exchanged are the most commonly used techniques for fabricating optical waveguides in LN. Table 1, which comes from Ref.27, shows the values of A and B with various fabrication techniques and irradiation wavelength \(\lambda _\textrm{ir}\).
The PE of VOA
As shown in Fig. 1b, MZI is an optical interferometer formed with the incoming light split, experiencing phase shifts \(\theta _L\) and \(\theta _R\) through the upper and lower waveguides, respectively, and then recombined. After the MZI, the amplitude of the output optical signal is given by
where \(E_{\textrm{in}}\) is the amplitude of the input optical signal, \(\varDelta \theta =\theta _R- \theta _L\) is the phase difference between the two waveguides, and \(\varphi =(\theta _R+\theta _L)/2\). The derivation of Eq. (9) is shown in the supplementary material. We find that MZI can be considered AM when \(\theta _R=- \theta _L\), and PM when \(\theta _R= \theta _L\). Here, we set \(\theta _R=-\theta _L\) because our manuscript considers the MZI for attenuation. For such a MZI, the output intensity is given by
In the ideal case, the phase difference \(\varDelta \theta\) only comes from the electro-optic modulation process on the waveguide. In detail, the values of \(\theta _R\) and \(\theta _L\) are determined by the applied voltage of the corresponding waveguide, i.e., \(V_R\) and \(V_L\), respectively. Since \(\theta _R=-\theta _L\), the two voltages follow \(V_R=-V_L=V_\textrm{app}\). Then, the ideal relationship between \(\varDelta \theta\) and the applied voltages is given by
where \(V_{\pi }\) is the driving voltage required for the phase modulator to provide the \(\pi\) phase.
However, when Eve radiates the two waveguides, the phase difference between them comes from not only the electro-optic modulation process but also the PE. In detail, the PE-induced phase on each waveguide is given by20
where \(\lambda _0\) is the signal wavelength, \(L_{\textrm{E}}\) refers to the effective interaction length. In practice, the effective interaction length of each waveguide is the same; thus, the PE-induced phase difference between the two waveguides is only related to \(\varDelta n_{\textrm{s}}\). As shown in Eq. (5), beside the waveguide parameters and the constants, \(\Delta {n_\mathrm{{s}}}\) is affected by the irradiation power \(I_{\textrm{ir}}\) and the applied electric field \(E_\mathrm{{app}}\). Since the applied electric field \(E_{\textrm{app}}\) on the upper and lower waveguide are different, the \(\theta _{\textrm{PE}}\) of the two waveguides are inconsistent and cannot cancel each other out. Additionally, if the irradiation wavelength deviates from the signal wavelength, the split light ratio of MZI for irradiation light will deviate from 0.5, so that the upper and lower waveguides have different irradiance power8. Therefore, the PE-induced phase difference between two waveguides can be expressed as
where d is the distance of applied electric field, \(\Delta n_{\mathrm{{s}},\mathrm{{0}}}^ \pm = \Delta {n_{\mathrm{{s}},\mathrm{{0}}}}(I_{\mathrm{{ir}}}^L) \pm \Delta {n_\mathrm{{s},0}}(I_{\mathrm{{ir}}}^R)\) with the upper waveguide irradiation power \(I_{\mathrm{{ir}}}^L\) and the lower waveguide irradiation power \(I_{\mathrm{{ir}}}^R\). The derivation of Eq. (13) is shown in the supplementary material. Finally, the total phase difference between the upper and lower waveguides is \(\Delta \theta ' = \Delta \theta + \Delta {\theta _{\mathrm{{PE}}}}\). Note that the result \(\Delta \theta '\) assumes a perfectly fabricated MZI, as the phase difference can also come from the structural difference due to the fabrication error. Then, the output intensity under irradiation becomes
To characterize the output intensity change after irradiation, we can define a parameter in terms of Eqs. (10) and (14) given by
The waveguide fabrication technique of Ref.20 is based on Ti-diffused. Besides Ti-diffused, the waveguides based on the proton-exchanged and annealed-proton-exchanged technology are also commonly used in QKD. Generally, proton-exchanged waveguide has the lowest fabrication cost among the three technologies, while annealed-proton-exchanged has fewer problems of index instability and deterioration of the electrooptic effect28. Therefore, we study the effect of PE on the VOA using different fabrication techniques (proton-exchanged or annealed-proton-exchanged). Fig. 2 shows the relationship between the output intensity change parameter k and the irradiation power \(I_\textrm{ir}\) with various fabrication techniques. The simulation parameters are shown in Tables 1 and 2. Here, we set the applied voltage \({V_{\textrm{app}}}\) to 2.386 V, for example, so that the MZI reaches a 10 dB attenuation with a 6 V half-wave voltage. Moreover, the range of \(I_\textrm{ir}\) is set to 0 to 50 \(\textrm{W}/\textrm{cm}^2\) (or about 3.5 \(\mu\)W) to meet a low irradiation power20,26. Since the irradiation wavelength deviates from the signal wavelength, the split light ratio of MZI for irradiation light will deviate from 0.5. In terms of the test data in Ref.20, a 405 nm irradiation wavelength has an 88:12 split light ratio when the signal wavelength of MZI is 1550 nm. Combining this result with Eq. (4) of Ref.8, we calculated that the split light ratio is about 87:13 when the irradiation wavelength is changed to 488 nm. Therefore, we set \(I_{\mathrm{{ir}}}^L:I_{\mathrm{{ir}}}^R = 87:13\) with \(I_{\mathrm{{ir}}}=I_{\mathrm{{ir}}}^L+I_{\mathrm{{ir}}}^R\). We find that the output intensity change parameter k of the proton-exchanged waveguide is significantly lower than that of the annealed-proton-exchanged waveguide, which can be attributed to a smaller dark conductivity of annealed-proton-exchanged waveguide in comparison with the proton-exchanged because of the annealing, and therefore, a higher photoinduced index change, as shown in Eq. (5). Note that the difference of dark conductivity \(\sigma _{\textrm{d}}\) between various fabrication techniques can be seen from the value of A in Table 1 as \(A=n^{3}r_{33} \kappa \alpha /2 \sigma _{\textrm{d}}\).
Security analysis
The relationship between the output intensity change parameter and the irradiation power with various fabrication techniques.
In this section, we show the practical security of one-way CV-QKD and CV-MDI-QKD under the IPA. Both cases use the Gaussian-modulation coherent state (GMCS) scheme, which has been proven secure against coherent attacks29. Finally, since secret key not proven to be composable is thus practically useless, the composable finite-size secret key rate is used for security analysis, which allows specifying the security requirements for combining different cryptographic applications in a unified and systematic way3.
One-way CV-QKD
The steps of the one-way GMCS scheme are as follows. First, Alice generates a sequence of coherent state \(|\alpha _{\textrm{A}}\rangle\) based on the Gaussian-modulated data, which can be expressed in phase space as
where \(x_{\textrm{A}}=|\alpha _{\textrm{A}}|\cos \theta\), \(p_{\textrm{A}}=|\alpha _{\textrm{A}}|\sin \theta\) are the Gaussian-modulated data, or equivalently, the so-called quadratures with the amplitude \(|\alpha _{\textrm{A}}|\) and phase \(\theta\). In detail, both \(x_{\textrm{A}}\) and \(p_{\textrm{A}}\) follow a zero mean Gaussian distribution with variance \(V_{\textrm{A}}\). Next, Alice uses VOA to attenuate the initial coherent state, adjusting the variance of the quadratures to an expected value, i.e., the modulation variance \(V_{\textrm{A}_0}\). The attenuated coherent state can be expressed as \(|\alpha _{\textrm{A}_0}\rangle = x_{\textrm{A}_0}+ip_{\textrm{A}_0}\) with adjusted quadratures \(x_{\textrm{A}_0}\) and \(p_{\textrm{A}_0}\). Then, Alice transfers the attenuated coherent state \(|\alpha _{\textrm{A}_0} \rangle\) to Bob through the thermal-loss channel, which is characterized by the transmittance T and the excess noise \(\xi\). When Bob receives the transmitted coherent state, he measures either one of the two quadratures randomly (by the homodyne detector) or both quadratures simultaneously (by the heterodyne detector). In terms of the measurement results, Alice and Bob perform the parameter estimation by disclosing part of the data, and calculate the secret key rate according to the method in the Supplemental Material. If their estimation shows that no secret keys can be generated, then they stop the key distribution. Otherwise, they proceed with information reconciliation and privacy amplification, and finally, the secret keys.
In our manuscript, we select the homodyne detector, for example, so that Bob gets either \(x_{\textrm{B}}\) or \(p_{\textrm{B}}\) randomly. A practical homodyne detector is characterized by its detection efficiency \(\eta\) and electronic noise \(V_{\textrm{el}}\). Generally, the thermal-loss channels can be modeled as a standard linear model; thus the relationship between the transmitted quadratures \(x_{\textrm{A}_0}\) and detection result \(x_{\textrm{B}}\) is given by
where z is a noise variable following a Gaussian distribution with variance \(\sigma ^2 =\eta T \xi + N_0 + V_{\textrm{el}}\). Here, \(N_0\) is the variance of shot noise. Note that Eq. (17) shows the case of quadrature x for example, while the quadrature p follow the same relationship i.e., \(p_{\textrm{B}}=\sqrt{\eta T}p_{\textrm{A}_0}+z\). In what follows, we only discuss the case of quadrature x. After the N-round detection, the statistics of \(x_{\textrm{A}_0}\) and \(x_{\textrm{B}}\) are as follows:
The next step after N-round detection is parameter estimation. In detail, Alice and Bob randomly select m \((m < N )\) round data to estimate the channel parameters T and \(\xi\) in practical implementation. The maximum-likelihood estimators \(\hat{t}\) and \(\hat{\sigma }^2\) are given by30
Here, \(\hat{t}\) and \(\hat{\sigma }^2\) are independent estimators and follow the distributions
(a) Secret key rate versus transmission distance under different irradiation power (\(I_\textrm{ir}=10, 30\) \(\textrm{W}/\textrm{cm}^2\)) when VOA uses the annealed-proton-exchanged fabrication technique. (b) Secret key rate versus transmission distance under different irradiation power (\(I_\textrm{ir}=2, 30, 50\) \(\textrm{W}/\textrm{cm}^2\)) when VOA uses the proton-exchanged fabrication techniques. \(K_{e}\) and \(K_{p}\) denote the overestimated and practical secret key rates, respectively. The fiber loss is 0.2 dB/km.
where \(\mathcal {N}\) denotes the Gaussian distribution, t and \(\sigma ^2\) represent the true values of parameters \(\hat{t}\) and \(\hat{\sigma }^2\), respectively. When m is large enough (e.g., \(m > 10^6\)), the chi-square distribution \(\chi ^2\) converges to a Gaussian distribution. Thus, the confidence intervals for the estimators \(\hat{t}\) and \(\hat{\sigma }^2\) are
with
where \(\epsilon _{\textrm{PE}}\) is the probability that the estimated parameter doesn’t belong to the confidence interval, \(z_{\epsilon _{\textrm{PE}}/2}\) is a coefficient which satisfies \(1-\frac{1}{2} \textrm{erf}(z_{\epsilon _{\textrm{PE}}/2}/ \sqrt{2})=\frac{1}{2}\epsilon _{\textrm{PE}}\) with the error function \(\textrm{erf}(x) = \frac{2}{\sqrt{\pi }} \int ^{x}_0 e^{-t^2} dt\). Finally, the estimators of transmittance and excess noise are given by
Based on the estimators \(\hat{T}\) and \(\hat{\xi }\), Alice and Bob can estimate the composable finite-size secret key rate \(K(V_{\textrm{A}_0}, \hat{T}, \hat{\xi } )\), as shown in the supplementary material.
However, when Eve radiates the waveguides, the attenuation of Alice’s VOA may decrease due to the influence of the PE (see Fig. 2); thus \(x_{\textrm{A}_0}\) and \(V_{\textrm{A}_0}\) deviate from the ideal values. The deviations of \(x_{\textrm{A}_0}\) and \(V_{\textrm{A}_0}\) can be characterized by the output intensity change parameter k in Eq. (15) given by
Correspondingly, Bob’s detection result will deviate from \(x _{B}\) to \(x^{\prime }_{\textrm{B}}\) given by
If Alice doesn’t monitor the deviation of modulation variance \(V_{\textrm{A}_0}\) and continues to use the original quadrature \(x_{\textrm{A}_0}\) for statistic calculation, the results will deviate from Eq. (18) to
Since the detection efficiency \(\eta\) and electronic noise \(V_{\textrm{el}}\) can be determined by Bob, the deviation of statistics caused by k will be incorrectly attributed to the change of T and \(\xi\). In other words, Alice and Bob consider the statistics still follow Eq. (18) with \(T \rightarrow T'\) and \(\xi \rightarrow \xi '\), which is given by
Combining Eqs. (27) and (26), we get
After the parameter estimation, Alice and Bob will get two deviated estimators \(\hat{T'}\) and \(\hat{\xi '}\) so that the estimated secret key rate becomes \(K(V_{\textrm{A}_0}, \hat{T'}, \hat{\xi '} )\). Because \(k>1\), Alice and Bob will overestimate the transmittance and underestimate the excess noise so that \(K(V_{\textrm{A}_0}, \hat{T'}, \hat{\xi '} )\) can be considered as an overestimate secret key rate, which introduces security loophole.
Fidelity of the mixture of Gaussian-modulation coherent states versus irradiation power with different waveguides.
Figure 3 shows the composable finite-size secret key rate when VOA uses different waveguides in one-way CV-QKD. The modulation variance is set to 4, while other protocol parameters are listed in Table 3. Note that we set the parameter estimation signals to 0.1 N in terms of Ref.31, which can be larger for more accurate estimation (but reducing the number of signals available for key generation). Here we use \(K_{e}=K(V_{\textrm{A}_0}, \hat{T^{\prime }}, \hat{\xi ^{\prime }})\) to denote overestimated secret key rate, while \(K_{p}=K(V_{\textrm{A}_0}^{\prime }, \hat{T}, \hat{\xi })\) represent the practical secret key rate with deviated modulation variance. Therefore, the gap between \(K_{\textrm{e}}\) and \(K_{\textrm{p}}\) reveals the key information that Eve can steal thro ugh the PE without being detected. Fig. 3a shows the composable finite-size secret key rate when VOA uses annealed-proton-exchanged waveguide. We find that the leakage of the secret key information increases with the irradiation power. Moreover, the PE had no significant effect on the practical secret key rate \(K_p\). Fig. 3b shows the composable finite-size secret key rate when VOA uses the proton-exchanged waveguide. We find that the proton-exchanged waveguide shows more robustness to PE than the annealed-proton-exchanged waveguide. This result is consistent with previous works, which suggest that proton-exchanged waveguides exhibit the highest robustness to PE20,27. We find that when the attack light power is less than 2 \(\textrm{W}/\textrm{cm}^2\), the leakage of the secret key information is almost zero. When the irradiation power is above 2 \(\textrm{W}/\textrm{cm}^2\), CV-QKD systems still cannot avoid the impact of PE on its security by using proton-exchanged VOA and need other countermeasures to defend against IPA. When the irradiation power increases from 2 to 50 \(\textrm{W}/\textrm{cm}^2\), the secret key information leakage, or equivalently, the gap between \(K_e\) and \(K_p\) increases and cannot be ignored.
To further discuss these results, we plot the fidelity F with different waveguides between the (total) transmitted quantum state with and without irradiation in Fig. 4. Here, the total quantum state represents the mixture of Gaussian-modulation coherent states, i.e., a thermal state with variance \(V_{\textrm{A}0} + 1\). In detail, the fidelity of two thermal states is \(F(\hat{\rho }_0,\hat{\rho }_1)=[\textrm{Tr}(\sqrt{\sqrt{\hat{\rho }_0}\hat{\rho }_1\sqrt{\hat{\rho }_0}})]\), which ranges from 0 (for orthogonal states) to 1 (for identical states)32. Here, \(\hat{\rho }_0\) and \(\hat{\rho }_1\) are the density matrices of the thermal state without and with irradiation. We find that the fidelity with the proton-exchanged waveguide is higher than that of annealed-proton-exchanged waveguide. In addition, the fidelity of the annealed-proton-exchanged waveguide case only decreases from 0.985 to 0.918 when the irradiation increases from 10 to 30 \(\textrm{W}/\textrm{cm}^2\). However, even having a fidelity of 0.985 (when \(I_\textrm{ir}\)= 10 \(\textrm{W}/\textrm{cm}^2\)), the parameter estimation has changed, which creates an obvious gap between \(K_{\textrm{e}}\) and \(K_{\textrm{p}}\). In summary, the PE mainly affects the parameter estimation process.
CV-MDI-QKD
Prepare-measure scheme of the CV-MDI-QKD protocols. QM quantum memory; LO local oscillator; PM phase modulation.
Secret key rate versus transmission distance when Eve performs different attack strategies in CV-MDI-QKD protocol. (a) Secret key rate versus transmission distance \({L_{\mathrm{{BC}}}}\) in the asymmetric configuration (\(\tau _A=0.9\)) based on RR. (b) Secret key rate versus transmission distance \({L_{\mathrm{{AC}}}}\) in the asymmetric configuration (\(\tau _B=0.9\)) based on RR. (c) Secret key rate versus one-side transmission distance (\({L_{\mathrm{{AC}}}}\) or \({L_{\mathrm{{BC}}}}\)) in the symmetric configuration based on RR. (d) Secret key rate versus one-side transmission distance (\({L_{\mathrm{{AC}}}}\) or \({L_{\mathrm{{BC}}}}\)) in the symmetric configuration based on DR. The irradiation power is \(I_{\textrm{ir}}\) = 3 W/cm\(\vphantom{0}^2\). The fiber loss is 0.2 dB/km. The solid and dashed lines denote \(K_p\) and \(K_e\), respectively.
CV-MDI-QKD protocol closes all the detector-side loopholes, but Eve may use the IPA to attack Alice’s and Bob’s VOA to create a source-side side channel. Fig. 5 shows the prepare-measure scheme of the CV-MDI-QKD protocol. First, Alice and Bob prepare coherent states independently, characterized by the variances \(V_\textrm{A} + 1\) and \(V_\textrm{B} + 1\), respectively. Then, they transfer their coherent states to Charlie (i.e., an untrusted third party) through two thermal-loss channels after the attenuation of their VOA. The traveling mode A (B) is subsequently combined with the ancillary mode \(E_1\) (\(E_2\)), through the BS with transmittance \(\tau _\textrm{A}\) (\(\tau _\textrm{B}\)), introducing thermal noise characterized by variance \(\omega _\textrm{A}\) (\(\omega _\textrm{B}\)). Next, Charlie performs a CV Bell detection on the received modes by mixing them in a balanced BS, with output ports conjugately homodyned. This detection process corresponds to the measurement of the quadrature operators \(\hat{q}_\textrm{C}=(\hat{q}_\textrm{A}-\hat{q}_\textrm{B})/ \sqrt{2}\) and \(\hat{p}_\textrm{D}=(\hat{p}_\textrm{A}+\hat{p}_\textrm{B})/ \sqrt{2}\), whose classical outcomes are combined in a complex variable \(\gamma =(q_\textrm{C}+ip_\textrm{D})/ \sqrt{2}\) with probability \(p(\gamma )\). The outcome \(\gamma\) is relayed to Alice and Bob through a classical public channel, where the relay functions as a correlator. The outcome \(\gamma\) establishes a posteriori correlation between Alice and Bob. Finally, Alice and Bob use information reconciliation and privacy amplification techniques to generate secret keys.
Figure 6 shows the composable finite-size secret key rate versus the transmission distance under different attack strategies in CV-MDI-QKD. The calculation details are shown in the supplementary material. Here, we consider the secret key rate under the two independent entangling-cloner attacks, i.e., \(g=g^{\prime }=0\), where g and \(g^{\prime }\) are correlation parameters14. In addition, the waveguide fabrication technology is annealed-proton-exchanged, and an example of such an MZI can be found in Ref.33. The parameter estimation method used in our manuscript is shown in Ref.34, and the irradiation power is set to \(I_\textrm{ir}=3\) \(\textrm{W}/\textrm{cm}^2\). Note that the parameter estimation results of each channel also follow Eq. (28) in CV-MDI-QKD protocol when \(g=0\). Similarly, the estimated secret key rate is \(K_{e}\), while the practical secret key rate is \(K_{p}\). The modulation variance is set to \(V_{\textrm{A}_0}=V_{\textrm{B}_0}\)=20, while other protocol parameters are listed in Table 3.
We first analyze the secret key rate when Alice and Bob use the asymmetric configuration, i.e., \({L_{\mathrm{{AC}}}} \ne {L_{\mathrm{{BC}}}}\). Note that, unlike the one-way protocol, CV-MDI-QKD has two source sides, so there are different attack strategies, i.e., attack Alice, attack Bob, attack both Alice and Bob. Fig. 6a shows the secret key rate versus transmission distance \({L_{\mathrm{{BC}}}}\) in the asymmetric configuration (\(\tau _A=0.9\)) based on reverse reconciliation (RR). We find that the biggest gap between \(K_e\) and \(K_p\) appears when Eve attacks both Alice and Bob. In this strategy, only a 3 \(\textrm{W}/\textrm{cm}^2\) irradiation power can reach a 14.29 km maximum transmission distance difference between \(K_{e}\) and \(K_{p}\). In addition, if Eve can only attack one side, attacking Alice yields more key information than attacking Bob. This result is related to the information reconciliation; attacking the non-reference side yields more key information than the reference side as the key rate benefits more from the improved channel quality between non-reference side and Charlie35. Fig. 6b shows the secret key rate versus transmission distance \({L_{\mathrm{{AC}}}}\) in the asymmetric configuration (\(\tau _B=0.9\)) based on RR. We find that attacking both Alice and Bob is also optimal for Eve, while only attacking Alice is better than only attacking Bob. Moreover, the transmission distance when Charlie is close to Bob is shorter than when Charlie is close to Alice.
Then, we analyze the secret key rate when Alice and Bob use the symmetric configuration (\({L_{\mathrm{{AC}}}} = {L_{\mathrm{{BC}}}}\)) based on RR, as shown in Fig. 6c. Here the transmission distance denotes one-side distance (\({L_{\mathrm{{AC}}}}\) or \({L_{\mathrm{{BC}}}}\)) so the total transmission distance of CV-MDI-QKD protocol is double. Similar to Fig. 6a and b, we find that only attacking Alice is better than only attacking Bob. This can be attributed to the RR we used above, where we fixed Bob’s data and corrected Alice’s data for error correctin. Consequently, attacks on Alice directly reduce the correlations most relevant for key extraction and increase Eve’s information more than attacks on Bob, even when Charlie is closer to Alice. If we change the reconciliation process and fix Alice’s data, i.e., direct reconciliation (DR), only attacking Alice is better than only attacking Bob, as shown in Fig. 6d.
The structure of the real-time monitoring scheme against the IPA in Alice’s apparatus for the one-way CV-QKD systems. IQmod in-phase and quadrature electro-optic modulator; MBC modulator bias controller; BS beam splitter; PD photo-diode; VOA variable optical attenuator.
Countermeasures
The research above reveals that the IPA threatens the practical security of the CV-QKD and CV-MDI-QKD systems based on LN waveguide devices. Therefore, countermeasures need to be developed to close this security loophole. Filter, isolator, and monitoring are the three most common ways to defend against attacks using injected light. However, commercial filters behind the VOA usually operate over a limited bandwidth, while the IPA works over a wide range of wavelengths (from ultraviolet to even 1549 nm36). For example, our manuscript uses a 488 nm irradiation wavelength, which is located in the visible light region and significantly deviates from the 1550 nm signal wavelength. In addition, when deploying quantum networks, the dense wavelength division multiplexing (DWDM) device behind the VOA can be considered as a filter because it adds loss to the light deviating from the commonly used communication wavelength. However, the loss of some DWDM channels may not be enough to filter out the injected visible light. The test data in Ref.20 shows that the loss of the C33 channel (or 1550.92 nm channel) is only 33 dB when the irradiation wavelength is 405 nm. Since IPA can attack Alice with several nW levels of injected light, the 33 dB loss may not be enough.
The isolator or circulator, which is also behind the VOA, is commonly used to protect the QKD system from the injected light. Unfortunately, a recent study shows that the loss on the injected light provided by the optical isolator can be reduced to 17.2 dB at minimum when a high-power light is injected into it in the reverse direction37. In addition, Tan et al. demonstrate that the loss of the isolator on the injected light can decrease from 70.3 dB to 10.9 dB when an external magnetic field with a magnetic induction of 1129.9 Gs is applied38. An alternative method of isolator to control the energy of injected light is the optical-power limiter (OPL) device, which is based on the thermo-optical defocusing effect of an acrylic prism and does not compromise quantum communication signals39. More recently, Peng et al. have proposed an improved OPL device, which adds a temperature monitor module near the acrylic prism to monitor real-time temperature fluctuations for improving the security of the system40. However, in terms of Ref.40, when Eve injects a 40 mW light with 1550 nm wavelength, the output optical power after passing the improved OPL device is -7 dBm or about 0.2 mW. As shown in Fig. 2, IPA can attack Alice with several nW of optical power.
A direct monitoring method is to detect the reverse injected light from Eve. However, if one wants to detect the reverse injection light, a wide response wavelength of the detector is required to meet the broadband characteristics of PE. Motivated by Ref.41, one can also monitor the intensity of the output signal in real-time to regain security. Fig. 7 shows the structure of a possible real-time monitoring scheme against the IPA in Alice’s apparatus for the one-way CV-QKD systems. In detail, Alice adds another 99:1 BS after VOA to split the attenuated signal, where 1 % of the output is measured by an additional PD for real-time signal intensity \(I_p\). Note that Alice can get the ideal intensity of the 1 % signal \(I_0\) before communication. Therefore, the intensity fluctuation values are calculated by \(k = {{{I_\mathrm{{P}}}} / {{I_0}}}\). Next, Alice can revise her corresponding data from \({x_{{A_0}}}\) to \(\sqrt{k} {x_{{A_0}}}\). Based on the revised data, Alice can get the true modulation variance \(V_{{\mathrm{{A}}_0}}^\prime \mathrm{{ = }}k{V_{{\mathrm{{A}}_\mathrm{{0}}}}}\), and then get two non-deviated estimators \(\hat{T}\) and \(\hat{\xi }\) by the parameter estimation. Finally, the new estimated key rate becomes \({K_e} = K(V_{{\mathrm{{A}}_0}}^\prime ,\hat{T},\hat{\xi }) = {K_p}\), which regain security. Note that this real-time monitoring scheme can also be used for the CV-MDI-QKD system. Beyond the discussion above, some other methods may enhance resistance to IPA, such as the bias feedback control and stabilization technology of Mach-Zehnder structures, doping engineering, and restorative process.
Conclusion
We have investigated the practical security of the CV-QKD protocols under the IPA using numerical simulations. In this attack, Eve has injected visible light with 488 nm wavelength into an LN-based VOA, where the LN waveguide uses a proton-exchanged or annealed-proton-exchanged fabrication technique. We have presented the relationship between the output intensity change of the VOA and the irradiation power of Eve, and then shown the change in output intensity affects the parameter estimation results that induce loopholes. We have established the composable finite-size security of both one-way and CV-MDI-QKD protocols. The results illustrate that the proposed attack combining the induced loopholes with intercept-resend attacks can break the security even with a low irradiation power. We have investigated that Eve’s optimal attack strategy for CV-MDI-QKD is related to the information reconciliation process. Filters, monitoring, and isolators may enhance the system security in response to the IPA, but these schemes have shortcomings, so the relevant countermeasures need further research. Our results provide guidance for future experiments on IPA and corresponding countermeasures in practical CV-QKD systems.
Data availability
All the data used in this study can be obtained from the corresponding author upon a reasonable request (e-mail: xxywyj@sina.com).
References
Pirandola, S. et al. Advances in quantum cryptography. Adv. Opt. Photon. 12, 1012–1236. https://doi.org/10.1364/AOP.361502 (2020).
Xu, F., Ma, X., Zhang, Q., Lo, H.-K. & Pan, J.-W. Secure quantum key distribution with realistic devices. Rev. Mod. Phys. 92, 025002. https://doi.org/10.1103/RevModPhys.92.025002 (2020).
Jain, N. et al. Practical continuous-variable quantum key distribution with composable security. Nat. Commun. 13, 4740. https://doi.org/10.1038/s41467-022-32161-y (2022).
Scarani, V. et al. The security of practical quantum key distribution. Rev. Mod. Phys. 81, 1301–1350. https://doi.org/10.1103/RevModPhys.81.1301 (2009).
Qin, H., Kumar, R. & Alléaume, R. Quantum hacking: Saturation attack on practical continuous-variable quantum key distribution. Phys. Rev. A 94, 012325. https://doi.org/10.1103/PhysRevA.94.012325 (2016).
Ma, X.-C., Sun, S.-H., Jiang, M.-S. & Liang, L.-M. Local oscillator fluctuation opens a loophole for eve in practical continuous-variable quantum-key-distribution systems. Phys. Rev. A 88, 022339. https://doi.org/10.1103/PhysRevA.88.022339 (2013).
Jouguet, P., Kunz-Jacques, S. & Diamanti, E. Preventing calibration attacks on the local oscillator in continuous-variable quantum key distribution. Phys. Rev. A 87, 062313. https://doi.org/10.1103/PhysRevA.87.062313 (2013).
Huang, J.-Z. et al. Quantum hacking of a continuous-variable quantum-key-distribution system using a wavelength attack. Phys. Rev. A. 87, 062329. https://doi.org/10.1103/PhysRevA.87.062329 (2013).
Qi, B., Lougovski, P., Pooser, R., Grice, W. & Bobrek, M. Generating the local oscillator “locally’’ in continuous-variable quantum key distribution based on coherent detection. Phys. Rev. X 5, 041009. https://doi.org/10.1103/PhysRevX.5.041009 (2015).
Soh, D. B. S. et al. Self-referenced continuous-variable quantum key distribution protocol. Phys. Rev. X 5, 041010. https://doi.org/10.1103/PhysRevX.5.041010 (2015).
Shao, Y. et al. Phase-reference-intensity attack on continuous-variable quantum key distribution with a local local oscillator. Phys. Rev. A 105, 032601. https://doi.org/10.1103/PhysRevA.105.032601 (2022).
Primaatmaja, I. W. et al. Security of device-independent quantum key distribution protocols: A review. Quantum 7, 932 (2023).
Marshall, K. & Weedbrook, C. Device-independent quantum cryptography for continuous variables. Phys. Rev. A 90, 042311. https://doi.org/10.1103/PhysRevA.90.042311 (2014).
Pirandola, S. et al. High-rate measurement-device-independent quantum cryptography. Nature Photon. 9, 397–402. https://doi.org/10.1038/nphoton.2015.83 (2015).
Papanastasiou, P., Mountogiannakis, A. G. & Pirandola, S. Composable security of cv-mdi-qkd with secret key rate and data processing. Sci. Rep. 13, 11636. https://doi.org/10.1038/s41598-023-37699-5 (2023).
Hajomer, A. A., Andersen, U. L. & Gehring, T. High-rate continuous-variable measurement device-independent quantum key distribution with finite-size security. Quantum Sci. Technol. 10, 025032. https://doi.org/10.1088/2058-9565/adb2be (2025).
Stiller, B. et al. Quantum hacking of continuous-variable quantum key distribution systems: realtime trojan-horse attacks. In 2015 Conference on Lasers and Electro-Optics (CLEO), 1–2, 2015, https://doi.org/10.1364/CLEO_QELS.2015.FF1A.7 (IEEE.
Huang, A. et al. Laser-seeding attack in quantum key distribution. Phys. Rev. Appl. 12, 064043. https://doi.org/10.1103/PhysRevApplied.12.064043 (2019).
Huang, A. et al. Laser-damage attack against optical attenuators in quantum key distribution. Phys. Rev. Appl. 13, 034017. https://doi.org/10.1103/PhysRevApplied.13.034017 (2020).
Ye, P. et al. Induced-photorefraction attack against quantum key distribution. Phys. Rev. Appl. 19, 054052. https://doi.org/10.1103/PhysRevApplied.19.054052 (2023).
Lu, F.-Y. et al. Hacking measurement-device-independent quantum key distribution. Optica 10, 520–527. https://doi.org/10.1364/OPTICA.485389 (2023).
Zhu, S. et al. Waveguide-integrated two-dimensional material photodetectors in thin-film lithium niobate. Adv. Photonics Res. 4, 2300045. https://doi.org/10.1002/adpr.202300045 (2023).
Cai, M. et al. Monolithic tunable dual-wavelength laser utilizing erbium-doped lithium niobate on an insulator. Opt. Lett. 49, 3018–3021. https://doi.org/10.1364/OL.522774 (2024).
Fujiwara, T., Mori, H. & Fujii, Y. Evolution and decay behavior of the photorefractive effect in ti: Linbo3 optical waveguides. Ferroelectrics 95, 133–137. https://doi.org/10.1080/00150198908245191 (1989).
Becker, R. & Williamson, R. Photorefractive effects in linbo3 channel waveguides: Model and experimental verification. Appl. Phys. Lett. 47, 1024–1026. https://doi.org/10.1063/1.96365 (1985).
Fujiwara, T., Cao, X., Srivastava, R. & Ramaswamy, R. V. Photorefractive effect in annealed proton-exchanged linbo3 waveguides. Appl. Phys. Lett. 61, 743–745. https://doi.org/10.1063/1.107784 (1992).
Fujiwara, T., Srivastava, R., Cao, X. & Ramaswamy, R. V. Comparison of photorefractive index change in proton-exchanged and ti-diffused linbo 3 waveguides. Opt. Lett. 18, 346–348. https://doi.org/10.1364/OL.18.000346 (1993).
Kuneva, M. Rare-earth doped optical waveguides in linbo3. Bulgarian Chem. Commun. 98 (2012).
Renner, R. & de Cirac, J. I. finetti representation theorem for infinite-dimensional quantum systems and applications to quantum cryptography. Phys. Rev. Lett. 102, 110504. https://doi.org/10.1103/PhysRevLett.102.110504 (2009).
Leverrier, A., Grosshans, F. & Grangier, P. Finite-size analysis of a continuous-variable quantum key distribution. Phys. Rev. A 81, 062343. https://doi.org/10.1103/PhysRevA.81.062343 (2010).
Wang, T., Huang, P., Li, L., Zhou, Y. & Zeng, G. High key rate continuous-variable quantum key distribution using telecom optical components. New J. Phys. 26, 023002. https://doi.org/10.1088/1367-2630/ad1b7e (2024).
Weedbrook, C. et al. Gaussian quantum information. Rev. Mod. Phys. 84, 621–669. https://doi.org/10.1103/RevModPhys.84.621 (2012).
Papanastasiou, P., Ottaviani, C. & Pirandola, S. Finite-size analysis of measurement-device-independent quantum cryptography with continuous variables. Phys. Rev. A 96, 042332. https://doi.org/10.1103/PhysRevA.96.042332 (2017).
Fletcher, A. et al. An overview of cv-mdi-qkd. Reports on Progress in Physics (2025).
Kostritskii, S. Photorefractive effect in linbo3-based integrated-optical circuits at wavelengths of third telecom window. Appl. Phys. B 95, 421–428. https://doi.org/10.1007/s00340-009-3501-4 (2009).
Ponosova, A. et al. Protecting fiber-optic quantum key distribution sources against light-injection attacks. PRX Quantum 3, 040307. https://doi.org/10.1103/PRXQuantum.3.040307 (2022).
Tan, H. et al. External magnetic effect for the security of practical quantum key distribution. Quantum Sci. Technol. 7, 045008. https://doi.org/10.1088/2058-9565/ac7d07 (2022).
Zhang, G. et al. Securing practical quantum communication systems with optical power limiters. PRX Quantum 2, 030304. https://doi.org/10.1103/PRXQuantum.2.030304 (2021).
Peng, Q. et al. Defending against a laser-seeding attack on continuous-variable quantum key distribution using an improved optical power limiter. Phys. Rev. A 108, 052616. https://doi.org/10.1103/PhysRevA.108.052616 (2023).
Li, C., Qian, L. & Lo, H.-K. Simple security proofs for continuous variable quantum key distribution with intensity fluctuating sources. npj Quantum Inf. 7, 150, https://doi.org/10.1038/s41534-021-00482-3 (2021).
Acknowledgements
We would like to thank Jingzheng Huang, Yuehuan Xu, and Qinquan Peng for helpful discussions.
Funding
This work was supported by the Innovation Program for Quantum Science and Technology (Grant No. 2021ZD0300703). The National Natural Science Foundation of China (Project Number: 62501084).
Author information
Authors and Affiliations
Contributions
N.Y.M. performed the security analysis and wrote the manuscript. H.Z., Y.J.W and Y.G. established attack strategies and countermeasures. Z.Z.Y. conceptualizing thesis framework and revised the main manuscript text. Y.Y.M. checked the full text formula. All authors reviewed the manuscript.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary Information
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Mao, N., Zhang, H., Zuo, Z. et al. Hacking continuous-variable quantum key distribution using the photorefractive effect on proton-exchanged/annealed-proton-exchanged waveguide. Sci Rep 16, 8934 (2026). https://doi.org/10.1038/s41598-026-42620-x
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1038/s41598-026-42620-x