Abstract
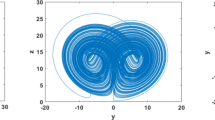
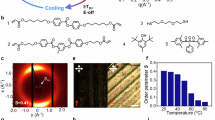
Data forgery and manipulation can undermine trust in areas ranging from science to journalism. Artificial intelligence will probably exacerbate this problem, degrading our ability to distinguish between artificially created data and real recordings (such as those taken with a video camera). Here we report a recording device technology that establishes a cryptographic link between a physical process (the act of recording) and an immutable digital entity (such as an entry in a public blockchain). Our approach relies on a monolithic cryptographic sensor that integrates a sensor device with a hashing unit (that continuously hashes pieces of recorded data) and a cryptographic signature unit (that signs the hashes using a public key encryption scheme). The system then uploads the signed hashes to a trusted public repository. We provide a proof-of-concept implementation with a voltage sensor for extracellular recording of cardiac myocyte field potentials that is fabricated using 180-nm complementary metal–oxide–semiconductor technology.
This is a preview of subscription content, access via your institution
Access options
Access Nature and 54 other Nature Portfolio journals
Get Nature+, our best-value online-access subscription
$32.99 / 30 days
cancel any time
Subscribe to this journal
Receive 12 digital issues and online access to articles
$119.00 per year
only $9.92 per issue
Buy this article
- Purchase on SpringerLink
- Instant access to the full article PDF.
USD 39.95
Prices may be subject to local taxes which are calculated during checkout


Similar content being viewed by others
Data availability
Links to the data uploaded to the Sokol blockchain during the proof-of-concept (PoC) implementation can be found in Supplementary Section 3. Other data that support the findings of this study (including the electrophysiological recordings) are available from the corresponding authors upon reasonable request.
References
Rini, R. Deepfakes and the epistemic backstop. Philos. Impr. 20, 1–16 (2020).
Westerlund, M. The emergence of deepfake technology: a review. Technol. Innov. Manag. Rev. 9, 39–52 (2019).
Ienca, M. On artificial intelligence and manipulation. Topoi 42, 833–842 (2023).
Shumailov, I. et al. AI models collapse when trained on recursively generated data. Nature 631, 755–759 (2024).
Naveh, A. & Tromer, E. PhotoProof: cryptographic image authentication for any set of permissible transformations. In 2016 IEEE Symposium on Security and Privacy (SP) 255–271 (IEEE, 2016).
Sedlmeir, J., Rieger, A., Roth, T. & Fridgen, G. Battling disinformation with cryptography. Nat. Mach. Intell. 5, 1056–1057 (2023).
C2PA technical specification. C2PA https://c2pa.org/specifications/specifications/2.0/specs/_attachments/C2PA_Specification.pdf (2024).
Igarashi, T., Kazuhiko, T., Kobayashi, Y., Kuno, H. & Diehl, E. Photrace: a blockchain-based traceability system for photographs on the internet. In 2021 IEEE International Conference on Blockchain (Blockchain) 590–596 (IEEE, 2021).
Garrison, C. & Sorensen, D. Apparatus for authenticated recording and method therefor. US patent 20030204736A1 (2003).
Ghoreishizadeh, S. S. et al. A lightweight cryptographic system for implantable biosensors. In 2014 IEEE Biomedical Circuits and Systems Conference (BioCAS) Proceedings 472–475 (IEEE, 2014).
Myers, C. C. Imaging systems with data encryption and embedding capabilities. US patent 20180097636A1 (2018).
Shao, B. et al. Highly trustworthy in-sensor cryptography for image encryption and authentication. ACS Nano 17, 10291–10299 (2023).
Suh, G.E. & Devadas, S. Physical unclonable functions for device authentication and secret key generation. In 2007 44th ACM/IEEE Design Automation Conference 9–14 (IEEE, 2007).
Cardes, F., Baladari, N., Lee, J. & Hierlemann, A. A low-power opamp-less second-order delta-sigma modulator for bioelectrical signals in 0.18 µm CMOS. Sensors 21, 6456 (2021).
Munjal, K. & Bhatia, R. A systematic review of homomorphic encryption and its contributions in healthcare industry. Complex Intell. Syst. 9, 3759–3786 (2023).
Aad, I. in Trends in Data Protection and Encryption Technologies (eds Mulder, V. et al.) 25–30 (Springer Nature, 2023).
Acknowledgements
This research was supported by ETH Zurich (ETH Postdoctoral Fellowship to F.C.); the Swiss National Science Foundation (SNSF) through project no. 205320_188910 (to A.H.); the State Secretariat for Education, Research and Innovation (SBFI) through the SwissChips initiative (to A.H.); the Swiss National Science Foundation (SNSF) Eccellenza Grant (grant no. PCEFP3_187001 to F.F.); Projects in Life Sciences Grant (grant no. 310030_220209 to F.F.); and an SNSF Spark Grant (grant no. CRSK-3_220987 to F.F.). We thank N. Baladari (ETH Zurich and TU Delft) for help with analogue-to-digital converter (ADC) design, P. Rimpf (Cleanroom Facility Basel, ETH Zurich) for assistance with chip packaging and F.K. Gürkaynak and B. Muheim Bachl (Microelectronics Design Center, ETH Zurich) for valuable discussions.
Author information
Authors and Affiliations
Contributions
F.C., S.B. and F.F. conceived the project. F.F. and A.H. supervised the project. F.F., F.C. and X.Y. developed the algorithm and implemented the software. F.C., X.Y., R.B. and V.V. built the prototype. F.C. and J.L. performed the experiments. Q.Y. and S.B. implemented the verification software in Solidity. A.R. performed the power, area and overhead estimation analysis. F.F. and F.C. wrote the paper. A.H., A.R. and S.B. edited the paper.
Corresponding authors
Ethics declarations
Competing interests
F.C., X.Y., R.B. and F.F. are inventors in a European patent application filed by ETH Zurich (application no. EP25164337.5). The patent application covers certain possible implementations of the monolithic cryptographic sensor discussed in the manuscript. The other authors declare no competing interests.
Peer review
Peer review information
Nature Electronics thanks Soumyajit Mandal and Fei Zhuge for their contribution to the peer review of this work.
Additional information
Publisher’s note Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary information
Supplementary Information (download PDF )
Supplementary Sections 1–4, Figs. 1 and 2 and Tables 1 and 2.
Rights and permissions
Springer Nature or its licensor (e.g. a society or other partner) holds exclusive rights to this article under a publishing agreement with the author(s) or other rightsholder(s); author self-archiving of the accepted manuscript version of this article is solely governed by the terms of such publishing agreement and applicable law.
About this article
Cite this article
Cardes, F., Bürgel, S., Yuan, X. et al. In-sensor cryptographic signature generation to link a physical process and an immutable digital entity. Nat Electron (2026). https://doi.org/10.1038/s41928-026-01593-5
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1038/s41928-026-01593-5