Abstract
Graph theory has emerged as an influential tool for communication network design and analysis, especially for designing hybrid network topologies for local area networks (LANs). LAN topologies often face challenges related to scalability, data traffic optimization, and security. Designing reliable and efficient hybrid LAN structures remains a critical problem in communication networks. This paper addresses the issue by proposing the application of graph labeling techniques, particularly H-irregularity strength, as a mathematical framework to model and optimize hybrid network topologies. The results illustrate the way theoretical graph labeling and practical network technology interact, offering a novel solution to LAN design problems. This study adds to the expanding field of graph theory applications in communication networks by relating graph theoretical ideas to actual network topologies. With an emphasis on the irregularity strength of particular graph families, the role of graph labeling in optimizing these topologies is explored in this study. The labeling methods that are given offer valuable insights into improving communication efficiency, guaranteeing LAN scalability, and optimizing network architecture. The theoretical underpinnings of the application of graph theory to communication network modelling are strengthened by these discoveries. Labeling methods are introduced in this study to capture topological irregularities and labeling constraints through the use of specialized graphs, such as the Dutch Windmill and Corona product graphs as they both have special labeling characteristics that can be used to improve network performance. In order to secure data and prevent network failures, a three-unit organization structure with a shared administrator is used in network design and optimization. A model of hybrid ring topology of a local area network is considered in this paper and different models are presented which are originated from Dutch Windmill and corona product of graphs. The contribution of this paper is it includes results about a special version of irregularity strength in which the subgraphs used are Dutch windmill graphs and cycle graphs. The edge, vertex and total H-irregularity strength of Dutch Windmill graph and Corona product graph are calculated, offering fresh perspectives on the way they could represent hybrid LAN topologies. The irregularity strength metric is particularly useful even though it measures the imbalance in vertex degrees, which is essential for optimizing communication flow and load balancing within a network. Our theoretical findings illustrate how these labeling schemes can model network behavior, improve resource allocation, and trace data flow effectively. Although the study is primarily theoretical, it offers groundwork for practical network simulation and real-world implementation. Future work will focus on validating the models through simulations and assessing performance metrics such as latency, throughput, and fault recovery. A key limitation of the current study is the absence of empirical performance validation, which is identified as an important direction for further research.
Similar content being viewed by others
Introduction
Graph theory relates mathematical models with graphs to visualize and understand them with ease. The foundation of this field was laid when Konigsberg bridge problem arose, Euler studied it in mid-18th century1. In 19th century a mathematician, Kirchhoff proposed electric circuits with the help of graphs2. In 1936 the first book on graph theory was published by K\(\ddot{\textrm{o}}\)nig3. In same era, graphs were used to develop four colored theorem4,5. Researchers Erd\(\ddot{\textrm{o}}\)s and Tutte gave the idea of graph coloring and planner graphs respectively6,7. In current era, it is a vital field of research along its applications in computer science, information technology, biology and many fields.
Graph labeling is an approach used in graph theory in which vertices and/or edges are given labels are usually positive integers, frequently in accordance with specific rules or patterns. Alexander Rosa introduced vertex, edge, and total labeling in 19678,9. Gallian analyzed these labels in further detail in10. Graph labels have a wide range of applications in several disciplines where links and dependencies between things are modeled using graph structures. In the design and analysis of algorithms for a range of graph problems, including network flow, shortest path, graph coloring and labeling are playing a vital role. Graph labeling methods are being used in bio-informatics to examine biological information represented as graphs, including phylogenetic trees, DNA sequences, protein structures, and metabolic pathways11. By analyzing social networks, graph labeling methods can be used to find important nodes, communities, and patterns of interaction between people or organizations. In communication networks, graph labeling is used to manage traffic, routing and quality of service12. Graph labeling is a tool used in game theory to represent and analyze player-to-player strategic interactions in network-based games13.
Ahmad, Bača, and Siddiqui studied the exact values for irregularity strebgth of generalized graphs of grids and prisms14. The strength for edge irregularity under \(C_{4}\) covering was examined in14. Bača, Javed, Hinding, Semaničová-Feňovčíková examined the mappings between edge-face and vertex-face planer connected graphs15. Grid-covering has been utilized by Tilukay16 to identify three features for grid graphs. Three novel properties of a graph with graphical representations of edge, vertex and total irregularity strength respectively17 are examined by taking distinct families of graphs. Ashraf, Bača, Kimáková, and Semaničová-Feňovčíková investigated ladder graph labeling and irregularity strength by using subgraphs \(C _8\) and \(C _{10}\)18, moreover provided new characteristics and computed exact values for path, ladder, and fan graphs, respectively. Several findings about the total irregularity of graphs are discussed in14,19. Edge amalgamation of cycles is used to build new graphs20. Nisviasari, Dafik, and Agustin21 used \({\dot{H}}\)-covering to investigate grid graph and triangular ladder properties. Joedo, Kristiana, Agustin and Nisviasari22 examined total irregularity strength for shackle and amalgamation of several graph families and suggested some limitations for these.
Relationship between local metric dimension and integer linear programming of corona product graph is investigated23, Energies of 2-corona product graph24, Generalized signed corona product of graphs and their applications are discussed in25. Rahmadani, Fauziah, Nusantara and Muksar used the Dutch windmill graphs26 to investigate the lower and upper bounds of rainbow connection numbers rc(G) and strong rainbow connection numbers src(G). Irene, Mahmudi, and Nurmaleni27 examined if super \((a,d)-C_3\)-antimagic total labeling of the Dutch windmill graph \(D_{3}^{m}\) exists. Ghanbari28 studied super domination number and sharp bounds for Dutch windmill graph and other classes of graphs. He proposed an exact solution for Dutch windmill graph. Various aspects and properties of the Dutch windmill graph are studied and exact values of graph parameters are suggested based on their findings29,30,31,32,33,34,35.
This paper introduces a novel application of H-irregularity strength in modeling and optimizing hybrid LAN topologies. Unlike traditional graph-based network models, our approach integrates vertex, edge, and total labeling techniques derived from Dutch Windmill and Corona product graphs to simulate and improve key network attributes such as load balancing, fault tolerance, and security. To the best of our knowledge, this is the first study that leverages H-irregular graph labeling specifically for designing LAN architectures with a focus on structural irregularities and topological resilience.
The article is structured as follows: “Overview on irregularity strength” illustrates the background of terms related to irregularity strength, “Formulation of problem” gives formulation of problem and linking it with real life application of hybrid ring topology in network design and optimization. “Generalized Dutch windmill graph” explains labeling methodology applied on generalized Dutch windmill graph. “Corona product structure of graph” contains model of corona product of graphs. The concluding remarks and future work are given in the last section.
Overview on irregularity strength
Chartrand et al. proposed an edge k-labeling which is a mapping \(\beta : E(G)\rightarrow \{1,2,\dots ,k\}\) in a simple connected graph G19 in the way that each vertex in G has a unique sum of the labels of the edges connected with it. This labeling is referred as irregular assignment. In a graph G, the maximal number k that is minimized over all irregular assignments is called irregularity strength s(G). If G contains at most one isolated vertex and no isolated edge, then the \(s(G)\le \infty\). In the similar manner vetex k-labeling \(\alpha : V(G)\rightarrow \{1,2,\dots ,k\}\) and total k-labeling \(\gamma : E(G) \cup V(G) \rightarrow \{1,2,\dots ,k\}\) were introduced. There are several variations in graph irregularity strength. Vertex irregularity strength36, edge irregularity strength14 and modular edge irregularity strength37,38,39 are a few examples.
The \({\dot{H}}\)-irregularity strength is a new form of irregularity strength that was introduced by Ashraf, Bača, Kimáková, and Semaničová-Feňovčíková40. As an expansion of the irregularity strength, it is a novel concept that originated in recent years. Each subgraph in a graph is isomorphic to the given subgraph \({\dot{H}}\), as demonstrated by the extension and generalisation of the weight of an edge in a graph40. A subgraph \({\dot{H}}\) has a total \({\dot{H}}\)-weight associated to it, which is the sum of all the labeled edges and vertices in \({\dot{H}}\)41. If the \({\dot{H}}\)-weights in total labeling are different, then graph exhibits total \({\dot{H}}\)-irregularity strength. Total \({\dot{H}}\)-irregularity strength is kept as low as feasible and is the lowest positive integer k for which vertex and edge labels are used to reduce \({\dot{H}}\)-weights42. The collection of subgraphs that cover the graph is represented by the following: \({\dot{H}}_1, {\dot{H}}_2,\dots ,{\dot{H}}_t\). In a graph if a vertex, edge or total labeled set has at least one subgraph \({\dot{H}}_i\) for a positive integer i, where \(i = 1,2, \dots ,t\), then G contains (\({\dot{H}}_1\)), (\({\dot{H}}_2),\dots ,({\dot{H}}_t\))-vertex, edge, or total covering respectively. If any two arbitrary distinct, and isomorphic subgraphs of \({\dot{H}}\), \({\dot{H}}_{a}\) and Ȟb are labeled and they satisfy the following condition: \(wt_{\gamma }({\dot{H}}_{b}) \ne wt_{\gamma }({\dot{H}}_{b})\), then G is irregular with respect to the given labeling. Furthermore, if a total k-labeling is achievable with considering k, as suggested by ths(G\(, {\dot{H}})\), the \({\dot{H}}\)-irregular total k-labeling preserves it for the least positive integer k. Similarly, one may define the strengths of vertex \({\dot{H}}\)-irregularity and edge \({\dot{H}}\)-irregularity respectively. H-irregularity strength cannot be easily calculated using a single formula.
The edge \({\dot{H}}\)-weight incorporating \({\dot{H}}\)-covering of subgraphs under edge k-labeling \(\gamma\) is:
Under vertex k-labeling, the equivalent vertex \({\dot{H}}\)-weight is:
Likewise, under total k-labeling, the equivalent edge \({\dot{H}}\)-weight is:
Formulation of problem
Graph theory serves as a mathematical basis for assessing and improving communication network structures. Network administrators could enhance network efficiency, performance, and privacy by illustrating networks as graphs and leveraging multiple graph theoretic concepts such as irregular labelings, irregular wights and irregularity strength. This strategy can result in more effective and extensible network designs. H-irregular labeling can be applied to the hybrid LAN topology by assigning separate labels to interconnections (edges) and devices (vertices) in such a way that no two labels are identical.This is the novel idea that for security and authentication reasons, distinct irregularity strength methods can be employed. In order to identify and monitor devices within the network and aid discover abnormalities or unauthorised access, nodes are given unique ”signatures” based on edge labels. Similarly the idea can be used while creating protocols for communication. It can be used, for instance, to create routing algorithms that ensure dependable and effective delivery by directing data packets according to the distinct IDs of nodes. H-irregularity strength in data networks can be applied to pattern identification and data analysis. Clusters, anomalies, and other intriguing patterns in the network data can be found by examining the distribution of labels and node sums.
Consider cycle graph \(C_{n}\) and path graph \(P_{m}\) as two connected and simple graphs having order n and m respectively. The corona product graph with vertex set \(V(C_{n}\odot P_m)\) and edge set \(E(C_{n}\odot P_m)\) is denoted by \(C_{n}\odot P_m\) can be obtained by taking one copy \(C_{n}\) and n copies of \(P_{m}\), and then each vertex of the \(i-th\) copy of \(P_{m}\) is attached to the \(i-th\) vertex of \(C_{n}\), where \(1 \le i \le m\)43. An important feature of this graph is that hierarchical structures or systems with interconnected parts, each with its own internal structure, can potentially be modelled using this graph.
A Dutch windmill graph is a form of graph that is created by taking t copies of the cycle \(C_{p}^{j}\), with \(6 \le p,~ 2 \le j \le m,\) having a shared vertex x, resulting in a ”windmill” structure. Here i, j shows the coordinates of vertices and \(\sigma , m\) are the coordinates size of \(D_{n}^{m}\). In other words, the Dutch windmill graph \(D_{n}^{m}\), \(n \ge 2, m \ge 3\), is formed by joining t copies of the cycle graph \(C_{p}^{j}\) at a common universal vertex. It contains \(m \sigma\) edges and \(m(n-1)+1\) vertices. The cycle subgraphs in \(D_{n}^{m}\) that is \(C_{p}^{j}\), shared a vertex denoted by x, and the vertices of \(C_{p}^{j}\) by \(w_{1}^{j}, w_{2}^{j}, \dots , w_{n-1}^{j}, x.\)The special structure of Dutch windmill graph can emulate scenarios in which several entities are linked to a central hub, such as processes linked to a central server or friendships in a social network.44.
A hybrid multi-ring topology integrates different ring topologies into a single, continuous network. This configuration takes advantage of the benefits of ring topology, such as security and fault tolerance, while simultaneously offering the flexibility and scalability of hybrid topology. A router comprises of a device utilized to link two or more subnetworks. Its key functions include managing traffic among such networks by routing data packets towards their intended network addresses and enabling several devices to utilize the same Internet connection. A physical firewall is a specially designed device that protects a network by filtering and regulating both inbound and outbound traffic according to predetermined security rules. A personal computer (Pc) is used by a single user at a time. It is frequently utilized for graphic design, email, data entry, and data analysis. A multi-function printer (MFP) is a device which may function as both a printer and a scanner. It often comes with extra functionality such as copying, scanning and faxing, resulting in handy instrument for professional use. A Network Storage Device (NSD) is a customized device that enables centralized data storage and access via a network. Network segmentation is the division of a network into smaller, isolated networks. This method improves network efficiency as well as safety by managing traffic flow and restricting access within the network.
In network design and optimization, there is a structure of a three-unit organization with a common administrator to prevent network failures and secure data. A hybrid ring topology of local area network (LAN) in this case includes a networking administrator, a physical firewall, router, personal computer, printing and scanning machine, and a network storage device that responds to administrator inquiries in each unit. To boost network speed, every appliance in each unit is connected. In Fig. 1, a hybrid ring topology network is shown. \(Pf_{i}, 1 \le i \le 3\) represents the physical firewall in units 1, 2 and 3 respectively. \(R_{i}, 1 \le i \le 3\) represents the routers in units 1, 2 and 3 respectively. \(Pc_{i}, 1 \le i \le 3\) represents the personal computer in units 1, 2 and 3 respectively. \(Ps_{i}, 1 \le i \le 3\) represents the printer with scanner in units 1, 2 and 3 respectively. \(NSD_{i}, 1 \le i \le 3\) represents the network storage device in units 1, 2 and 3 respectively.
Illustration of a hybrid ring topology of local area network.
In this topology, each device functions as a repeater, reviving the signal and transmitting it to the next device. This enables that data can be transmitted over long distances without deterioration. If any device in the ring fails, the entire network might be disrupted, making ring topology an important concern. The Network Administrator supervises all units and sends and receives responses to his queries. Each unit has its own NSD, and the administrator has access to each NSD to obtain any type of data linked to each unit. The administrator also sets rules at each unit to prevent vulnerable data from entering via a physical firewall, which filters irrelevant data flow and protects each unit’s network.
Each unit has a supervisor who may analyze data using the unit’s own computer. Each unit’s personal computer also performs data entry. There are peripheral devices attached to each network supervisor. They have access to their respective unit’s peripheral devices, as well as their NSD, and can send any request to obtain the necessary information about their unit’s data. The network administrator has access to all peripheral devices in each unit. The network administrator monitors the data flow in each unit and is in charge of ensuring that the network is operational at all times. If each devive is represented by a vertex and the connection between these devices is represented by an edge then the graph derived from local network hybrid topology is illustrated in Fig. 2. It would utilize to guarantee that a network performs smoothly, consistently and securely. This includes planning, configuring, and maintaining network devices to achieve specified goals such as improved performance, reliability and safety as well as making sure the network is capable of adapting to changing needs and expectations while remaining cost-effective.
Derived graph from hybrid topology of local area network.
Organizations can improve their general effectiveness and competitive advantages by effectively designing and optimizing networks. This includes assisting company operations and communication within companies providing access and structures for storage devices, servers, and other information technology telecommunications networks, and delivering internet connectivity to users by using graph labeling.
Model of vertex irregular labeling for hybrid LAN topology
Vertex irregular labeling is an effective approach for network optimization. To build a graph model for a local area network, the issue arises: what are the benefits of using vertex labeling to monitor local area network performance? Simply it will assign unique identifiers to each device. This enables extensive monitoring of device performance, usage trends and potential concerns. In a hybrid local network design, this can aid in swiftly identifying and fixing underperforming devices to ensure optimal network performance. It is essential for network virtualization because it assigns unique identifiers to virtual devices and connections. This can assist manage virtual networks by ensuring that each virtual device and connection is correctly separated and controlled, as well as enhancing the overall efficiency and security of the visualized environment.
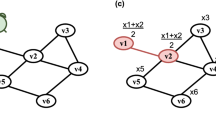
Vertex labeling serves as labels to the vertices nodes of a graph based on resource allocation. Labels correspond to various types of devices or their abilities, allowing for more efficient resource distribution. Similarly, a distinct vertex label can improve security by making simpler to monitor and regulate access to various areas of the local area network. The minimum case is two ring topologies represented by organizational units that are linked by a common network administrator x. To extend each unit in this model, \(w_{i}^{j}\) for \(2 \le n, m\) play a vital role to increase number of devices with a unique code in a sequence: \(\langle i, i, i, i, i, i \rangle , \langle i, i, i, i, i, i+1 \rangle , \langle i, i, i, i, i+1, i+1 \rangle , \langle i, i, i, i+1, i+1, i+1 \rangle\), ..., \(\langle n-1, n-1, n-1, n-1, n-1, n-1 \rangle\) for \(1\le i\le n-1\), where \(w_{i}^{j}\) represents a vertex in the graph. This sequence is critical for protecting the visualized environment of the local area network and tracing under performing devices in each unit that is connected to the network via a wired ring topology to maximize data transfer speed. If a device loses connection, every operation will be halted until the network administrator notifies the maintenance staff, who will then address the issue. This enhancement will enable small enterprises to have faultless security in their local area networks. Figure [3] provides a hybrid ring topology for local area networks. A specific derivative graph model with network administrator x is presented, having devices designated by \(w_{i}^{j}\), \(2 \le n, m\), and here \(1 \le i \le 6, m = 6\).
Vertex and edge irregular labeling of \(D_{n}^{m}\) graph via local network topology.
Model of total irregular labeling with irregularity strength for hybrid LAN topology
In total labeling, the third model consists of both edges and vertices labels which illustrate local area network capacity planning by giving a complete picture of the resources available in the network and connections. This can assist detect difficulties, plan for future modifications and ensure that the network can handle additional traffic without degrading performance. Total labeling can also improve network availability via offering an in-depth analysis of all connections and devices, allowing critical paths and probable failure locations to be identified. By ensuring that alternative pathways and devices are correctly labeled and controlled, network administrators strengthen the ability of the network to tolerate failures and operate continuously. Total labeling can be utilized to optimize both connections and devices, resulting in a more productive and evenly distributed network. This model \((x, w_{i}^{j}, w_{i}^{j} w_{i+1}^{j}, xw_{i}^{j} xw_{n-1}^{j})\) for \(1 \le j, 1\le i \le n-1, x=1\) plays a vital role in increasing the quantity of connections. In Fig. 4 a specific case of an enterprise is illustrated. The labeled map is given to monitor the data flow and devices activities through total labeling, in this specific case of total labeling in local network topology there are five units in it with six devices attached with the network in each unit excluding the network administrator x. In order to ensure unquestionable security in the model organization, x has complete control over networking in every unit and serves as an internet service provider.
An illustration of total irregular labeling of \(D_{n}^{m}\) in local area network which shows both vertex and edge labels.
Generalized Dutch windmill graph
This section includes a brief analysis with precise results for the total \(C_{p}^{j}\)-irregularity strength of the derived Dutch Windmill graph, represented by \(D_{n}^{m}, p \ge 3\). It contains labeled vertices and edges. \(C_{p}^{j}\) covering constructs a family of isomorphic subgraphs for \(3 \le p\) \(C_{p}^{j,\Re } = (C_{3}^{2,1}, C_{3}^{2,2}, C_{3}^{2,3} ,\dots , C_{3}^{2,\Re }, $$\) \(C_{4}^{3,1}, C_{4}^{3,2}, C_{4}^{3,3} ,\ldots , C_{4}^{3,\Re }, \ldots , $$\) \(C_{\sigma -1}^{m,1}, C_{\sigma -1}^{m,2}, C_{\sigma -1}^{m,3} ,\dots , C_{\sigma -1}^{m,t-1}, C_{\sigma -1}^{m,t})\), where \(3 \le p\) and \(2 \le j \le m, 1 \le \Re \le t\). Total \(C_{p}^{j}\)-weight for a specific \(C_{p}^{j}\), \(1 \le \Re \le t\), is the sum of each labeled vertex and edge in the given \(C_{p}^{j}\). The formula used for total \(C_{p}^{j}\)-weight labeling is \(wt_{\gamma }(C_{p}^{j})=\sum _{w_{i}^{j}\in V(C_{p}^{j,\Re }} \gamma (w_{i}^{j}) + \sum _{e_{i}^{j} \in E(C_{p}^{j,\Re })} \gamma (e_{i}^{j})\). Here \(\gamma\) provides the total \(C_{p}^{j}\)-labeling for \(C_{p}^{j} \subseteq D_{n}^{m}\). For total \(C_{p}^{j}\)-irregularity strength, each \(C_{p}^{j}\)-weight has a distinct value in \(C_{p}^{j}\) and satisfies \(wt_{\gamma }(C_{p}^{j})\ne wt_{\gamma }(C_{p}^{j+1})\). This condition illustrates an irregular \(C_{p}^{j}\)-labeling in \(D_{n}^{m}\). Total irregularity strength exists when there is at least one positive integer k for which total irregular labeling is conceivable. The total irregularity under \(C_{p}^{j}\) labeling is written as \(ths(D_{n}^{m}, C_{p}^{j})\).
Lemma 1, 2 and 3 explain the exact solutions for upper bounds of total, vertex and edge \({\dot{H}}\) -irregularity strengths respectively. These are deduced from results given in45. Lemma 1 establishes lower bounds of edge \(C_{p}^{j}\)-irregularity strength of \(D_{n}^{m}\) graph.
Lemma 1
Consider the \(C_{p}^{j}\)-covering of \(D_{n}^{m}\) graph given by t sub-graphs with \(p \ge 6\), \(j \ge 2\) and \(1 \le \Re \le t\). Then edge \(C_{p}^{j}\)-irregularity strength
This result shows that as the number of cycle subgraphs increases, the minimum number of distinct edge labels needed also grows. In real-world LANs, this implies that larger or more complex network segments require more diverse connection identifiers, helping to uniquely trace data flows and reduce routing conflicts. The Dutch Windmill graph additionally indicate the strength of vertex \(C_{p}^{j}\)-irregularity. The lower bounds of the vertex \(C_{p}^{j}\)-irregularity strength of graph \(D_{n}^{m}\) have been provided by Lemma 2.
Lemma 2
Consider the \(C_{p}^{j}\)-covering of \(D_{n}^{m}\) graph given by t sub-graphs with \(p\ge 6\) and \(j \ge 2\) and \(1 \le \Re \le t\). Then vertex \(C_{p}^{j}\)-irregularity strength
This lemma gives a lower bound on the number of unique device identifiers (i.e., vertex labels) needed. In a LAN setting, this means that to reliably identify and monitor devices, particularly in layered or hybrid structures, each must have a sufficiently distinct signature – aiding in fault detection and device tracking. The lower bounds of total \(C_{p}^{j}\)-irregularity strength of \(D_{n}^{m}\) are ensured by Lemma 3.
Lemma 3
Consider that \(C_{p}^{j}\)-covering of \(D_{n}^{m}\) graph given by t sub-graphs with \(p\ge 6\) and \(j \ge 2\) and \(1 \le \Re \le t\). Then total \(C_{p}^{j}\)-irregularity strength
This bound combines both vertex and edge labeling complexity. For network administrators, it indicates the minimum label set size necessary for complete traceability of both devices and connections—essential for maintaining data integrity, auditing, and security in a large-scale hybrid LAN. Using Lemma 3, \(ths(D_{n}^{m}, C_{p}^{j})\) is computed based on the generalized model of \(D_{n}^{m}\) with \(C_{p}^{j}\)-labeling. The objective is to determine the least k at which unique sums with labels (ranging from 1 to k) can be accomplished by using above defined weights and lemmas.
The following results measures the edge, vertex and total \(C_{p}^{j}\)-irregularity strength of the Dutch Windmill graphs.
Theorem 1
Suppose \(D_{n}^{m}\), for \(m, n \ge 2\), be a Dutch Windmill graph preserving \(C_{p}^{j}\)-covering with \(p \ge 6, 2\le j \le m\). Then
Proof
The Dutch Windmill graph contains \(t = n +1\) isomorphic copies of \(C_{p}^{j}\). The edge set is represented by \(E(D^{m}_n)\), that is \(\{xw_{i}^{j}, w_{i}^{j}w_{i+1}^{j}: 1\le i \le n-1, 2 \le j \le m\}\). The generalized Dutch Windmill graph contains precisely \(t = n +1\) copies of \(C_{p}^{j}\).
For \(3 \le m, n\), Lemma1 states the lower bound of this strength. Suppose \(k = 1+ \Big \lceil \frac{n}{n(m+1)} \Big \rceil\). To ensure that k is the upper boundary of \(ehs(D^{m }_n, C_{p}^{j })\) for \(2 \le m,2 \le n\). The edge \(C_{p}^{j}-\)irregular labeling is defined through the following manner:
The given result shows that all edge labelings are no more than k. For edge labeling \(\beta\), the weight \(C_{p}^{j}\)-weight in cyclic graph \(C_{p}^{j},\) where \(2 \le j \le m\) and \(p \ge 6\) is expressed as, \(wt(\beta (C_{p}^{j}))= \sum _{ e_{j}^{i} \in E(C_{p}^{j})} \beta (e_{j}^{i})\).
Consider the difference of the weights of subgraphs \(C_{p}^{j}\) and \(C_{i+1}^{j}\), which illustrates the weights difference of \(C_{p}^{j}\) and \(C_{i+1}^{j}\) subgraphs for \(i = 1,2,3,\dots ,n-1\). Therefore, \(ehs (D_{n}^{m}, C_{p}^{j}) \le k,\) and this completes the proof. \(\square\)
Theorem 2
Assume \(D_{n}^{m}\), for \(2 \le m, n\), as a generalized Dutch Windmill graph with \(C_{p}^{j}\)-covering with \(p \ge 6\). Then
Proof
For \(2 \le n,m\), the generalized Dutch Windmill \(D_{n}^{m}\) has \(mn + 1\) vertices and \(n(m+1)\) edges. The vertex set is represented by \(V(D_{n}^{m})= \{ w_{i}^{j}, 1 \le i \le n-1, 2 \le j \le m \}\). The graph \(D_{n}^{m}\) contains precisely \(t = n +1\) copies of \(C_{p}^{j}\). Lemma 2 states the lower bound of this strength. Now put \(k = \Big \lceil 1+ \frac{n}{nm+1 } \Big \rceil\), such that the vertex \(C_{p}^{j,\Re }-irregular\) labeling is set up in this manner:
The preceding result shows that all vertex labelings are not more than k. Under the vertex labeling \(\alpha\), the weight \(C_{p}^{j}-\)weight of the cyclic graph \(C_{p}^{j}\), with \(6 \le p \le t\) is represented as \(wt (\alpha (C_{p}^{j}))= \sum _{ w_{i}^{j} \in V(C_{p}^{j})} \alpha (w_{i}^{j})\).
For each \(i = 1,2,3,\dots , n-1\) note the difference in weights between the subgraphs \(C_{p}^{j}\) and \(C_{p+1}^{j}\). This represents the difference in weights between the subgraphs \(C_{p}^{j}\) and \(C_{i+1}^{j}\) for that particular \(j = 2,3,\dots , m\). Thus, \(vhs (D^m_n, C_{p}^{j}) \le k,\) which is the desired result. \(\square\)
Theorem 3
Let \(D_{n}^{m}\) be the generalized Windmill graph having order \(mn + 1\) and size \(n(m+1)\) respectively. \(D_{n}^{m}\) is admitting \(C_{p}^{j}\)-covering having \(n +1\) copies of \(C_{p}^{j}\) with \(p \ge 6\). Then
Proof
A Dutch Windmill graph \(D_{n}^{m}, m,n \ge 2\) contains \(mn + 1\) vertices and \(n(m+1)\) edges. The given sets \(\{w_{i}^{j}, x : i = 1,2,3,\dots , n-1, 2\le j\le m \}\) and \(\{ xw_{i}^{j}, w_{i}^{j}w_{i+1}^{j}: 1\le i \le n-1, 2 \le j \le m \}\) characterize the vertex and edge set of \(D_{n}^{m}\), respectively. The Dutch Windmill graph has precisely \(t = n +1\) copies of \(C_{p}^{j}\)-covering. Lemma 3 states the lower bound of this strength. Put \(k = \Big \lceil 1 +\frac{n}{2mn+n+1} \Big \rceil\) for the total \(C_{p}^{j}-\) irregularity strength of \(D_{n}^{m}\). Consider the total \(C_{p}^{j}-\) irregular labeling for \(m \ge 3, n = 3\) as follows:
According to the preceding findings, all vertex and edge labelings comprises no more than k of the total graph labeling. For total labeling, \(\gamma\), the weight \(C_{p}^{j}\)-weight of the cyclic graph \(C_{p}^{j,\Re }, p \ge 3\) is represented as:
Furthermore, the difference of the weights of subgraphs \(C_{p}^{j, \Re }\) and \(C_{p+1}^{j,\Re }\) for \(p \ge 3\).
Case-1: By taking first exact value of \(\gamma (xw_{i}^{j})\)
Case-2: By taking second value of \(\gamma (xw_{i}^{j})\)
Hence, \(ths (D_{n}^{m}, C_{p}^{j,\Re }) \le k,\) that accomplishes the proof. \(\square\)
This formula directly relates the size of the network (through n and m) to the complexity of labeling. The result implies that as network redundancy increases (larger windmill with more arms), we can maintain irregularity with a modest number of labels—making the design both scalable and efficient.
Significance of weights and H-irregularity strength of generalized Dutch windmill graph
\(C_{p}^{j}\)-irregular weights are unique which are allocated to the edges as well as vertices of a graph in an \(C_{p}^{j}\)-irregular labeling. These weights reflect a variety of network structure criteria, including speed, delay, and priority. By making sure that these weights are unique, network administrators can improve resource routing and allocation, resulting in a more efficient and dependable network. \(C_{p}^{j}\)-irregular weights can be distributed among connections and devices according to their importance or significance. In a hybrid ring local network topology, such weights can be utilized to allocate resources to vital data flows, guaranteeing that high-priority traffic gets transmitted quickly. This is especially important in situations when certain apps or services require consistent speed and low delay.
The \(C_{p}^{j}\)-irregularity strength of a graph is defined as the least positive integer \(k\) that allows for \(C_{p}^{j}\)-irregular labeling. This property is critical for network optimization because it ensures that the weights allocated to edges or vertices are unique, thereby reducing conflicts and improving data flow efficiency. \(C_{p}^{j}\)-irregularity strength influences network durability by guaranteeing that each route and device has a distinct label, which can aid in dispute resolution and fault tolerance. In a hybrid local network design, this can result in a more durable networks that can endure failures while still operating effectively. \(C_{p}^{j}\)-irregularity strength can improve the security of networks through guaranteeing that each interconnection (edge) and machine (vertex) have its own identity. This distinguishing feature is useful in tracking and handling network activity, which makes it easier to discover irregularities and possible violations of security.
Corona product structure of graph
Corona product of two graphs \(C_{p}\) and \(P_m\) is denoted as \(C_{p}\odot P_m\). It is basically a graph operation which combines \(C_{p}\) and \(P_m\) in a unique way. There are three steps to perform this operation: Firstly, a copy of \(C_{p}\) and number of copies of \(P_m\) equivalent to the vertex set of given graph \(C_{p}\) are considered. In next step, each vertex \(v_i\) of \(C_{p}\) is joined to the each vertex in the i-th copy of \(P_m\). Finally, after this operation a new graph is generated that has structure of \(C_{p}\) with each of its vertices expanded into a copy of \(P_m\) attached to it. In this paper, there is a brief study of edge, vertex and total labeling of a generalized model for the \(C_{p}\odot P_m\) and the exact solutions are investigated with the help of certain parameters. For the exact solutions that admits \(C_{p}\)-covering with respect to edge, vertex and total labeling Lemmas 4, 5, 6 play a vital role. After defining these lemmas, \(C_p\)-irregularity strength of \(C_{p}\odot P_m\) will be calculated.
Lemma 4 establishes lower bounds for edge \(C_{3}\)-irregularity strength.
Lemma 4
Let \(C_{3}\odot P_m\) graph admitting the \(C_{3}\)-covering given by t sub-graphs isomorphic to \(C_3\). Then
The Lemma 5 establishes the lower bounds for the vertex \(C_{3}\)-irregularity strength.
Lemma 5
Let \(C_{3}\odot P_m\) graph admitting the \(C_{3}\)-covering given by t sub-graphs isomorphic to \(C_3\). Then
The lower bounds of total \(C_{3}\)-irregularity strength are given by Lemma 6.
Lemma 6
Let \(C_{3}\odot P_m\) graph admitting the \(C_{3}\)-covering given by t sub-graphs isomorphic to \(C_3\). Then
Total \(C_{3}^{\Re (j)}\)-irregularity strength of corona product of \(C_{3}^{\Re (j)}\) with path graph
In “Introduction”, detailed construction of \(C_{3}\odot P_m\) has been provided. Isomorphic \(C_3\) covering generates a family of subgraphs written as \(C_{3}^{\Re (j)} = (C_{3}^{\Re (1)}, C_{3}^{\Re (2)}, C_{3}^{\Re (3)},\dots , C_{3}^{\Re (t)})\), here \(\Re (i)=i\) is a function to distinguish total covering. Total \(C_{3}^{\Re (j)}\)-weight for one of the given \(C_{3}^{\Re (j)}\), \(j = 1, 2,\dots , t\) is the sum of each labeled vertex and edge in the provided \(C_{3}^{\Re (j)}\). Total \(C_{3}^{\Re (j)}\)-weight labeling for an arbitrary \(C_{3}^{\Re (j)}\) is defined as, \(wt_{\gamma }(C_{3}^{\Re (j)})=\sum _{v\in V ( C_{3}^{\Re (j)})} \gamma (v) + \sum _{e\in E(C_{3}^{\Re (j)})} \gamma (e).\) Here \(\gamma\) specifies the total \(C_{3}^{\Re (j)}\)-labeling for the subgraph such that \(C_{3}^{\Re (j)} \subseteq C_{3}\odot P_m\). For total \(C_{3}^{\Re (j)}\)-irregularity strength each \(C_{3}^{\Re (j)}\)-weight has a different weights in \(C_{3}^{\Re (j)}\) and satisfy \(wt_{\gamma }(C_{3}^{\Re (j)})\ne wt_{\gamma }(C_{3}^{\Re (j+1)})\), here \(1 \le j \le t\). This condition proves total \(C_{3}^{\Re (j)}\)-irregular \(C_{3}^{\Re (j)}\)-labeling in \(C_{3}\odot P_m\). Total irregularity strength exists if there exist a least positive integer k for which total irregular labeling is possible. Forthwith, \(C_{3}^{\Re (j)}\)-irregularity under \(C_{3}^{\Re (j)}\)-labeling is expressed as \(ths(C_{3}\odot P_m, C_{3})\). Symbol of \(ths(C_{3}\odot P_m,C_{3})\) is defined first time in41.
Now we are going to calculate \(ths(C_{3}\odot P_m, C_{3})\) for the generalized structure of \(C_{3}\odot P_m\) under \(C_{3}^{\Re (j)}\)-labeling with the help of Lemma 6.
Theorem 4
Let \(C_{3}\odot P_m\) be the corona product of cycle graph and path graph \(P_m\). The graph \(C_{3}\odot P_m\) is admitting \(C_{3}-covering\) generating a family of \(~3\sigma -2\) isomorphic copies of \(C_{3}^{\Re (j)}\) as \(\left( C_{3}^{\Re (1)}, C_{3}^{\Re (2)}, C_{3}^{\Re (3)},\dots , C_{3}^{\Re (3\sigma -2)}\right)\) with a parameter \(3 \le \sigma\). Then
Proof
Consider \(C_{3}\odot P_m (x, y, z, u_{i}, w_{i}, w_{i})\) be a \(C_{3}\odot P_m\) for a positive integer \(3 \le \sigma\). \(C_{3}\odot P_m\) has order \(3(m +2)\) and size \(6(m +1)\) such that \(k \le ths(C_{3}\odot P_m)\) for the all following cases, where k is the least positive integer for which \(C_{3}\odot P_m\) admitting \(C_{3}^{\Re (j)}\)-irregular total \(C_{3}^{\Re (j)}\)-labeling.
The vertex set and the edge set of \(C_{3}\odot P_m\) are defined as follows:
and
Total labeling of \(C_{3}\odot P_m\) is defined as,
. The generalized solutions of total labeling in \(C_{3}\odot P_m\) for \(3 \le \sigma , 1 \le i \le \sigma -1\) are defined as,
It is easily evident that all total labels in \(C_{3}\odot P_m\) with \(C_{3}^{\Re (j)}\)-labeling are at most t. We get the following relations for \(1\le i \le \sigma -1\);
The weights of \(C_{3}\odot P_m\) after calculating and summarizing are listed below for \(1\le i \le \sigma -1\):
For two arbitrary subgraphs \(C_{3}^{j+1}\) and \(C_{3}^{j}\) which have an isomorphism with \(C_{3}^{\Re (j)}\) under the labeling \(\gamma\), for \(1\le j \le t\). It is simple to verify that all weights are consecutive, such as \(wt_\gamma (C_{3}^{j}) \ne wt_\gamma (C_{3}^{j+1})\). Furthermore, \(wt_\gamma (C_{3}^{j}) - wt_\gamma (C_{3}^{j+1}) = 1\). At this point \(1 \le j \le t\) is a parameter. This concludes the proof. \(\square\)
This result provides a bound for labeling corona-style subnetworks where devices (paths) are clustered around a main cycle (core router). It shows that even as subnet sizes grow, the labeling remains manageable, which is ideal for extending LANs by adding new departments or remote clusters. Figure 5 demonstrates a total labeled graph of \(C_{3}\odot P_{36}\) with 109 isomorphic copies of \(C_{3}^{\Re (j)}\).
Total \(C_{3}^{\Re (j)}\)-irregular labeling of a \(C_{3}\odot P_{36}\).
Edge \(C_{3}^{\Re (j)}\)-irregularity strength of \(C_{3}\odot P_m\)
Edge-covering in \(C_{3}\odot P_m\) is the collection of subgraphs which originate a set as \(C_{3}^{\Re (j)} = C_{3}^{\Re (1)}, C_{3}^{\Re (2)},\ldots , C_{3}^{\Re (t)}\), with the condition that every edge of \(C_{3}\odot P_m\) is present in at least one subgraph \(C_{3}^{\Re (j)} \subset C_{3}\odot P_m\), here \(\Re (j)=i\) and \(j = 1, 2,\dots , t\). At that instant it is said that \(C_{3}\odot P_m\) admits a (\(C_{3}^{\Re (1)}, C_{3}^{\Re (2)},\dots , C_{3}^{\Re (t)}\))-(edge) covering. A \(C_{3}^{\Re (j)}\)-covering exists when every subgraph \(C_{3}^{\Re (j)}\) has an isomorphism to the specified subgraph \(C_{3} \subset C_{3}\odot P_m\). Every isomorphic subgraph of \(C_{3}^{\Re (j)}\) is contained in \(C_{3}^{\Re (j)}\)-covering. The associated weight of \(C_{3}^{\Re (j)}\) with edge \(C_{3}^{\Re (j)}\)-labeling \(\beta\) is stated as,
Here, \(\beta\) defines the edge \(C_{3}\)-labeling in \(C_{3} \odot P_m\). For two arbitrary subgraphs \(1 \le a\), \(C_{3}^{\Re (a)}\) and \(C_{3}^{\Re (a+1)}\) if the following inequality is satisfied, \(wt(C_{3}^{\Re (a)}) \ne wt(C_{3}^{\Re (a+1)}).\) then irregular \(C_{3}^{\Re (j)}\)-labeling in \(C_{3}\odot P_m\) exists. Ultimately, \(C_{3}^{\Re (j)}\)-irregularity for edges under \(C_{3}^{\Re (j)}\)-labeling is represented as \(ehs(C_{3} \odot P_m, C_{3}),\) which was proposed initially in40. Edge irregularity strength is acquired when there exists a k with \(0 \le k, k \subset Z\), for which \(ehs(C_{3}\odot P_m, C_{3})\) is achievable under \(C_{3}^{\Re (j)}\) labeling. Now, we are going to determine \(ehs(C_{3} \odot P_m, C_{3})\) for the modified structure of \(C_{3} \odot P_m\) under \(C_{3}^{\Re (j)}\)-covering with the help of Lemma 4.
Theorem 5
Let \(C_{3}\odot P_m\) be the corona product of cycle graph and path graph \(P_m\). The graph \(C_{3}\odot P_m\) is admitting \(C_{3}-covering\) generating a family of \(~3\sigma -2\) isomorphic copies of \(C_{3}^{\Re (j)}\) as \(\left( C_{3}^{\Re (1)}, C_{3}^{\Re (2)}, C_{3}^{\Re (3)},\dots , C_{3}^{\Re (3\sigma -2)}\right)\) with a parameter \(3 \le \sigma\). Then
Proof
Let \(C_{3}\odot P_m = C_{3}\odot P_m\) be the corona product of graphs with a positive integer \(\sigma\), where \(3 \le \sigma\). Furthermore, k is the least positive integer for which \(C_{3}\odot P_m\) admits \(C_{3}^{\Re (j)}\)-irregular edge \(C_{3}^{\Re (j)}\)-labeling. Edge set for \(C_{3}\odot P_m\) is defined as:
From lemma 4, \(\mathrm{{ehs}}(C_{3}\odot P_m,C_{3}) \ge \sigma\). Take \(k=\sigma\) to check that k represents the upper boundary of \(\mathrm{{ehs}}(C_{3}\odot P_m,C_{3})\) with given constraints \(1 \le i \le \sigma\), \(3 \le \sigma\). Edge labeling for \(C_{3}\odot P_m\) is set up as follows:
\(C_{3}^{\Re (j)}\) - irregular edge labeling \(\beta\) for \(C_{3}\odot P_m\) is provided below:
It is easily evident that all labels of edge in \(C_{3}\odot P_m\) with \(C_{3}^{\Re (j)}\)-labeling are at most k. The weight of all subgraphs in \(C_{3}\odot P_m\) generate the following results for \(1 \le i \le \sigma -1\),
The weights in \(C_{3}\odot P_m\) after computing and summarizing are provided below for \(1\le i \le \sigma -1\):
It is simple to verify that for two arbitrary subgraphs, \(C_{3}^{\Re (a)}\) and \(C_{3}^{\Re (a+1)}\) for \(1\le a\) under edge labeling \(\beta\), the following connection between their weights exist. \(wt(C_{3}^{\Re (a)}) \ne wt(C_{3}^{\Re (a+1)})\). Here, \(3\le i\le \sigma -1\). We get,
This completes the proof. \(\square\)
In figure 6, \(C_{3}\odot P_m\) illustrates an edge irregular \(C_{3}^{\Re (j)}\)-labeling under t isomorphic copies of \(C_{3}^{\Re (j)}\), where \(0 \le t = 3\sigma -2\).
Edge \(C_{3}^{\Re (j)}\)-irregular labeling of a \(C_{3}\odot P_m\) \(= C_{3}\odot P_m (u_i, v_i, w_i)\) for a positive integer i, where \(1\le i \le 35\).
Vertex \(C_{3}^{\Re (j)}\)-irregularity strength of \(C_{3}\odot P_m\)
For vertex irregularity strength, there exist covering \(C_{3}\odot P_m\) which is described as a collection of subgraphs given by \(C_{3}^{\Re (1)}, C_{3}^{\Re (2)},\dots , C_{3}^{\Re (t)}\), on the condition that every vertex of \(C_{3}\odot P_m\) appears in at least one subgraph which is predefined in the preceding family of subgraphs \(C_{3}^{\Re (j)}\), here \(\Re (j)=j\) and \(j = 1, 2,\dots , t\). At this point, it is stated that \(C_{3}\odot P_m\) admits a (\(C_{3}^{\Re (1)}, C_{3}^{\Re (2)},\dots , C_{3}^{\Re (t)}\))-(vertex) covering. \(C_{3}^{\Re (j)}\)-covering occurs if each subgraph \(C_{3}^{\Re (j)}\) has an isomorphism corresponding to the specified subgraph. Under vertex \(C_{3}^{\Re (j)}\)-labeling \(\alpha\), the associated weight of \(C_{3}^{\Re (j)}\) is,
Here, \(\alpha\) represents the \(C_{3}^{\Re (j)}\) vertex labeling associated with subgraph and \(C_{3}^{\Re (j)}\subseteq C_{3}\odot P_m\). If two arbitrary subgraphs \(C_{3}^{\Re (j)}\) and \(C_{3}^{\Re (j+1)}\) have an isomorphism with the provided subgraph \(C_{3}^{\Re (j)}\), the required requirements need to be proved, i.e., \(wt(C_{3}^{\Re (j)}) \ne wt(C_{3}^{\Re (j+1)})\) and their weight difference is one. This situation demonstrates vertex \(C_{3}^{\Re (j)}\)-irregular labeling in \(C_{3}\odot P_m\). For a least positive integer k if there exist irregularity in \(C_{3}\odot P_m\). under \(C_{3}^{\Re (j)}\) covering then vertex irregularity strength exist. It is written as \(vhs(C_{3}\odot P_m, C_{3}).\) Using Lemma 5, the general form of \(C_{3}\odot P_m\) for \(C_{3}^{\Re (j)}\) covering will be computed. Figure 7 illustrates a \(C_{3}^{\Re (j)}\)-irregular vertex structure of a graph.
Vertex \(C_{3}^{\Re (j)}\)-irregular labeling of a \(C_{3}\odot P_m\) \(C_{3}^{184} = (u_i, v_i, w_i)\) for a positive integer i, where \(1\le i\le 60\).
Theorem 6
Let \(C_{3}\odot P_m\) be the corona product of cycle graph and path graph \(P_m\). The graph \(C_{3}\odot P_m\) is admitting \(C_{3}-covering\) generating a family of \(~3\sigma -2\) isomorphic copies of \(C_{3}^{\Re (j)}\) as \(C_{3}^{\Re (j)} = (C_{3}^{\Re (1)}, C_{3}^{\Re (2)}, C_{3}^{\Re (3)},\ldots , C_{3}^{\Re (3\sigma -2)})\) with a parameter \(3 \le \sigma\). Then
Proof
Assume \(C_{3}\odot P_m (u_{i}, w_{i}, w_{i})\) is the corona product of cyclic and path graphs of order 3 and m, respectively, for a positive integer \(\sigma\), for \(3 \le \sigma -1\). \(C_{3}\odot P_m\) has order \(3(m +2)\) and size \(6(m +1)\). Furthermore, k is the minimum positive integer that ensures \(C_{3}\odot P_m\) admits \(C_{3}^{\Re (j)}\)-irregular vertex labeling. The vertex set for \(C_{3}\odot P_m\) is given as,
Based on Lemma 5, \(\mathrm{{vhs}}(C_{3}\odot P_m,C_{3}) \ge \sigma\). Vertex labeling for \(C_{3}\odot P_m\) is described as
\(\alpha\) for \(C_{3}\odot P_m\) with order m along with size \(m-1\), for \(1 \le i \le \sigma -1, 3\le \sigma\), as follows:
It is easily evident that each of the label for vertices in \(C_{3}\odot P_m\) with \(C_{3}^{\Re (j)}\)-labeling are limited to k. The weight of t isomorphic subgraphs in \(C_{3}\odot P_m\) leads to the following relations:
The weights for the mathematical model of \(C_{3}\odot P_m\) after simplifying are provided below for \(1\le i \le \sigma -1\),
Any two arbitrary subgraphs \(C_{3}^{\Re (a)}\) and \(C_{3}^{\Re (a+1)}\) for \(1\le a \le j\) are isomorphic to \(C_{3}^{\Re (j)}\) under the labeling \(\alpha\). It is simple to check that \(wt(C_{3}^{\Re (a)}) \ne wt_(C_{3}^{\Re (a+1)})\) and \(wt_(C_{3}^{\Re (a)}) - wt_(C_{3}^{\Re (a+1)}) = 1\). In this case, \(s\ge 1\), and \(3\le j \le \sigma -1\) represents the \(C_{3}^{\Re (j)}\) labeling parameter. It concludes the proof. \(\square\)
Performance evaluation
Graph labeling is an effective method for resolving a variety of network optimisation issues. By assigning labels to the vertices or edges of a graph intricate networks can be modeled and analyzed which help to solve issues like resource allocation, routing, and network design. Graph labeling in large-scale networks, however, is fraught with difficulties.The number of potential label assignments rises exponentially with network growth. Even for modestly big networks, it becomes computationally costly to find the best labeling that meets the optimisation problem’s criteria. Long processing durations and the impossibility of real-time solutions are the main consequences. It is a challenging issue to create effective distributed graph labeling algorithms that can avoid communication bottlenecks and coordinate label assignments across several processors.
The efficiency of the suggested hybrid network topologies in optimising local area network (LAN) designs is evaluated through performance assessment. These topologies are generated from the Dutch Windmill graph and the corona product of graphs. The assessment focusses on important parameters that are essential for guaranteeing dependable and effective network topologies, such as load balancing, fault tolerance, scalability, and communication efficiency. The average path length and network latency of the suggested hybrid topologies are examined in order to assess their communication effectiveness. Compared to conventional ring and star topologies, the Dutch Windmill graph and corona product-based topologies show shorter average path lengths, which results in lower latency and quicker data transfer. The optimised edge and vertex labeling systems, which reduce superfluous connections and promote direct communication channels between nodes, are responsible for this improvement. Because of their modular design, which enables the smooth integration of more nodes, the suggested topologies demonstrate exceptional scalability. Specifically, the corona product graph offers a hierarchical structure that facilitates gradual growth while preserving effective channels of communication. Robust fault tolerance is ensured by the Dutch Windmill graph which has three-unit organizational structure with a shared administrator. These topologies’ built-in redundancy makes other routing pathways possible, reducing the impact of failures and improving network dependability. An important factor in assessing load balancing throughout the network is the irregularity strength indicator. This metric, which measures the imbalance in vertex degrees, makes sure that no node is overburdened, maximising resource use and avoiding bottlenecks. The computed edge, vertex, and total H-irregularity strengths of the Dutch Windmill and corona product graphs demonstrate how well the suggested labeling techniques disperse communication burdens throughout the network. The performance evaluation highlights the interaction between real-world network technology and theoretical graph labeling. The results show that the irregularity strength metric gives practical insights for creating effective and scalable LANs in addition to a theoretical framework for examining network topologies. The study opens the door for more research into graph-based solutions in communication networks by bridging the gap between graph theory and network engineering.
Conclusion
With a particular focus on the implementation of graph labeling methods in hybrid network topologies deployed in local area networks (LANs), the relationship between graph theory and communication networks is investigated in this study. The applicability of these theoretical ideas to practical network design is illustrated by analysing the H-irregularity strength of many graph topologies, including the Dutch Windmill graph and the corona product of graphs. Edge, vertex and total labeling are calculated to generalize the graphical model of \(C_{p}\odot P_m\) and \(D_{n}^{m}\). \(C_{3}^{\Re (j)}\)-covering and \(C_{p}^{j, \Re }\)-covering are used to cover \(C_{p}\odot P_m\) and \(D_{n}^{m}\) derived from provided parameters. In addition, the generalized model of \(C_{3}\odot P_m\) and \(D_{n}^{m}\) is used to investigate certain graph features.
To determine edge, vertex, and total \(C_{3}^{\Re (j)}\)-weights and \(C_{p}^{j, \Re }\)-weights, specified graph models are utilized and labeled accordingly. Furthermore, it is examined that for edge, vertex, and total labeling under \(C_{3}^{\Re (j)}\) covering or \(C_{p}^{j, \Re }\)-covering, there exists a least positive integer k for which edge, vertex, and total irregularity strength endures. The exact results for \(ths(D^m_n, C_{p}^{j,\Re })\), \(ehs(D^ m_\sigma , C_{p}^{j,\Re })\) and \(vhs(D^ m_\sigma , C_{p}^{j,\Re })\) are natural extensions of the irregularity strength of a graph. The results are obtained for a family of the Dutch Windmill structure of graphs. It also investigates the exact values for \(ths(C_{3}\odot P_m, C_{3})\), \(ehs(C_{3}\odot P_m, C_{3})\), and \(vhs(C_{3}\odot P_m, C_{3})\).
Our findings demonstrate that irregularity strength is essential for maximizing network performance by correcting vertex degree imbalances, which have a direct effect on load distribution and communication flow in hybrid LANs. The results demonstrate how graph labeling can potentially used as a tool to improve network designs’ scalability, resilience, and performance. This work can be extended further by taking variation in model or using different types of irregularity strengths. Through the integration of graph-theoretical ideas with real-world communication network applications, this study advances our knowledge of how mathematical models might enhance the functioning and design of contemporary LAN systems. In order to better integrate graph theory into network engineering, future studies can apply similar labeling approaches to increasingly intricate network topologies.
SDAC-DA may be useful for analysing irregularity in clustered graphs or as a preprocessing step. These relationships need to be investigated further in order to create efficient methods for combining SDAC-DA with irregularity strength analysis46.Although identifying spreaders in social networks is the main goal of ranking measure, it may also be used to determine which nodes affect irregularity strength, examine the connection between irregularity and spreading influence, create spreading strategies that take irregularity into account, and estimate irregularity strength in large networks47. These relationships need to be investigated further in order to provide practical strategies for combining irregularity strength analysis with this ranking metric. It might be feasible to affect traffic distribution and the degree of irregularity in the underlying network by strategically controlling data flow inside the network. In order to obtain the necessary irregularity features, this may need carefully routing flows to certain nodes or connections48.
While this study provides valuable theoretical insights into the application of H-irregularity strength for optimizing hybrid LAN topologies, it is important to acknowledge certain limitations. The proposed models have not yet been validated using real-world network data or assessed through empirical performance metrics such as latency, throughput, or fault recovery. Additionally, the labeling schemes are based on idealized and deterministic graph structures, which may not fully capture the complexity, dynamism, or failure-prone nature of practical communication networks.
Despite these limitations, the results have significant implications for network design. The derived bounds and labeling strategies offer a novel framework for distinguishing devices, managing connections, and optimizing communication within hybrid topologies. These theoretical foundations can inform the development of more efficient, secure, and scalable LAN architectures. By embedding mathematical structure into the modeling of network behavior, this work contributes to the broader integration of discrete mathematics in network optimization.
Future work will focus on implementing and testing the proposed models in simulated and real-world environments, with particular attention to quantifiable network performance. There is also strong potential for extending the labeling techniques to dynamic or stochastic network models, where topologies evolve over time or include uncertainties. Furthermore, the integration of machine learning algorithms for adaptive labeling strategies presents an exciting avenue for enhancing flexibility and robustness in real-time network applications. Finally, exploring multi-layer or software-defined network architectures may uncover new roles for graph irregularity labeling in managing virtual and physical topologies simultaneously.
Abbreviation
The abbreviations utilized in this study are presented in the following Table 1.
Data availability
The datasets used and/or analysed during the current study available from the corresponding author on reasonable request.
References
Venkataraman, G. The Königsberg Bridges Problem and Euler’s Solution. 5–12 (Bulletin of the Mathematics Teachers’ Association (India), 2024).
Kadowaki, M., Katayama, H. & Yamamoto, M. Galvanic current analysis of AA6016/SM490 couple using experimental and numerical simulation data in various NaCl solutions. Corros. Sci. 211, 110918 (2023).
Kőnig, D. Theorie der Endlichen und Unendlichen Graphen (Akadémiai Kiadó, 1936).
Asif, M. A. et al. An application on edge irregular reflexive labeling for m t-graph of cycle graph. AIMS Math. 10(1), 1300–1321 (2025).
Soifer, A. The Four-Color Theorem. In The New Mathematical Coloring Book: Mathematics of Coloring and the Colorful Life of Its Creators (Springer US, 2024).
Maus, Y. Distributed graph coloring made easy. ACM Trans. Parallel Comput. 10(4), 1–21 (2023).
Jungić, V. The never-ending happiness of Paul Erdős’s mathematics. Math. Intell. 46(1), 33–41 (2024).
Ganati, G. A., Repalle, V. S. R. & Ashebo, M. A. Social network analysis by Turiyam graphs. BMC Res. Notes 16(1), 170 (2023).
Farrell, L. K. m-Colored Exchange Graphs and Associated Combinatorial Objects (Master’s Thesis, University of Minnesota, 2022).
Gallian, J. A dynamic survey of graph labelings, 1996–2023. Electron. J. Combin. https://doi.org/10.37236/27 (2023).
Yi, H. C., You, Z. H., Huang, D. S., & Kwoh, C. K. Graph representation learning in bioinformatics: Trends, methods and applications. Brief. Bioinform. 23(1), bbab340 (2022).
Bhatt, H., & Bhatt, V. Cordial Labeling Technique Applications on Various Standard Graphs. Available at SSRN 5112211 (2025).
Asim, M. A., Hasni, R., Ahmad, A., Assiri, B. & Semanicová-Fenovcíková, A. Irregularity strength of circulant graphs using algorithmic approach. IEEE Access 9, 54401-54406 (2021). https://doi.org/10.1109/ACCESS.2021.3058786.
Zalsa, T. M., Indriati, D., & Martini, T. S. Edge irregular reflexive labeling of dumbbell graph, corona of open ladder, and null graph. Barekeng J. Ilmu Mat. Terapan 18(4), 2767-2778 (2024).
Bača, M., Hinding, N., Javed, A. & Semaničová-Feňovčíková, A. H-irregularity strengths of plane graphs. Symmetry 13(2), 229 (2021).
Tilukay, M. I. On H-Irregularity Strength of Grid Graphs. arXiv preprint arXiv:2110.10883 (2021).
Ashraf, F., Bača, M., Semaničová-Feňovčíková, A., & Shabbir, A. On H-irregularity strengths of G-amalgamation of graphs. Electron. J. Graph Theory Appl. 5(2) (2017).
Ashraf, F., Bača, M., Semaničová-Feňovčíková, A. & Siddiqui, M. K. On-irregularity strength of ladders and fan graphs. AKCE Int. J. Graph. Combin. 17(1), 213–219 (2020).
Sainsbury-Dale, M. & Zammit-Mangion, A. Neural Bayes estimators for irregular spatial data using graph neural networks. J. Comput. Graph. Stat. 4, 1–16 (2025).
Nurvazly, D. E. & Sugeng, K. A. Graceful labeling of edge amalgamation of cycle graph. J. Phys. Conf. Ser. IOP Publishing 1108(1), 012047 (2018).
Nisviasari, R. & Agustin, I. H. The total H-irregularity strength of triangular ladder and grid graphs. J. Phys. Conf. Ser. IOP Publishing 1211(1), 012005 (2019).
Joedo, J. C., Kristiana, A. I., Agustin, I. H. & Nisviasari, R. On the rainbow antimagic coloring of vertex amalgamation of graphs. J. Phys. Conf. Ser. IOP Publishing 2157(1), 012014 (2022).
Amini, F., Henning, M. A., & Tavakoli, M. Local edge metric dimensions via corona products and integer linear programming. Comput. Appl. Math. 43, 358. https://doi.org/10.1007/s40314-024-02879-0 (2024).
Energy of 2-Corona of Graphs. SpringerLink. https://link.springer.com/chapter/10.1007/978-981-16-5952-2_7 (2021).
Adhikari, B., Singh, A., & Yadav, S. K. Corona product of signed graphs and its application to signed network modelling. arXiv:1908.10018 (2019).
Rahmadani, D., Fauziah, G. R., Nusantara, T., & Muksar, M. A rainbow and strong rainbow connection numbers on pleated of the Dutch windmill graphs. In AIP Conference Proceedings. Vol. 3176(1). (AIP Publishing, 2024).
Irene, Y., Mahmudi, M., & Nurmaleni, N. On super \((a, d)\)-antimagic total labeling of Dutch windmill graph. Mathline J. Mat. Pendidikan Mat. 9(1), 189-204 (2024).
Ghanbari, N. Some results on the super domination number of a graph. Discrete Math. Algorithms Appl. 16(04), 2350044 (2024).
Zhang, Y., Wang, F. & Yang, C. Monitoring edge-geodetic numbers of some networks. J. Interconnect. Netw. 24(1), 2450001 (2024).
Zainiyah, Z., Kristiana, A. I., Slamin, S., Dafik, D., & Mursyidah, I. L. On time series forecasting on NPK and pH concentration of hydroponic plants by means of resolving efficient domination set of graph. In AIP Conference Proceedings. Vol. 3176(1). (AIP Publishing, 2024).
Batiha, I. M., Anakira, N., Hashim, A., & Mohamed, B. A special graph for the connected metric dimension of graphs. Math. Models Eng. (2024).
Akhter, S., Muhiuddin, G., Hameed, S. & Ahmad, U. A new family of graphs and strong antireciprocal eigenvalue property. J. Math. 2024(1), 8849362 (2024).
Hathi, Y. M., Javia, P. S., Jariya, M. M., Shukla, M., Acharya, B., Shah, M. A., & Mallik, S. Harmonic Mean Cordial Labeling of Some Special Graphs and Some Graphs Related to H-Graph (2024).
Waheed, M., Bashir, M. F., Jamil, M. K., Javed, A., & Naci Cangul, I. Edge corona product and its topological descriptors with applications in complex molecular structures. In Communications in Combinatorics and Optimization (2024).
Sethukkarasi, A., & Vidyanandini, S. Graph composite labeling techniques and practical applications. In 2024 International Conference on Emerging Systems and Intelligent Computing (ESIC). 526–532. (IEEE, 2024).
Imran, M., Ahmad, A., Siddiqui, M. K. & Mehmood, T. Total vertex irregularity strength of generalized prism graphs. J. Discrete Math. Sci. Cryptogr. 25, 1855–1865 (2021).
Koam, A. N. A., Ahmad, A., Bača, M., & Semaničová-Feňovčíková, A. Modular edge irregularity strength of graphs. AIMS Math. https://api.semanticscholar.org/CorpusID:253065791 (2022).
Almazaydeh, A. I. Edge and modular edge irregularity strength of some path related graphs. J. Algebra Appl. Math. 22(1) (2024).
Susanto, F., Simanjuntak, R. & Baskoro, E. T. D-irregularity strength of a graph. Utilitas Math. 121(69), 90 (2024).
Maryati, T. K. & Hadiputra, F. F. On H-irregularity strength of comb and edge comb product of graphs. J. Combin. Math. Combin. Comput. 125(255), 269 (2025).
Ashraf, F., Bača, M., Lascśaková, M. & Semaničová-Feňovčíková, A. On H-irregularity strength of graphs. Discuss. Math. Graph Theory 37(4), 1067–1078 (2017).
Ashraf, F., Bača, M., Semaničová-Feňovčíková, A., & Saputro, S. W. On cycle-irregularity strength of ladders and fan graphs. Electron. J. Graph Theory Appl. 8(1) (2020).
Pegua, J., Singha, K. R., Kumaria, P. & Mishrab, V. N. Decomposition of corona graph. Filomat 39(10), 3321–3328 (2025).
Singh, P., Sharma, S., Sharma, S. K. & Bhat, V. K. Metric dimension and edge metric dimension of windmill graphs. AIMS Math. 6(5), 531–548. https://doi.org/10.3934/math.2021531 (2021).
Ashraf, F. et al. On total-irregularity strength of the disjoint union of graphs. Discuss. Math. Graph Theory 40(1), 181–194 (2020).
Berahmand, K., Bahadori, S., Abadeh, M. N., Li, Y., & Xu, Y. SDAC-DA: Semi-supervised deep attributed clustering using dual autoencoder. In IEEE Transactions on Knowledge and Data Engineering (2024).
Berahmand, K., Bouyer, A. & Samadi, N. A new local and multidimensional ranking measure to detect spreaders in social networks. Computing 101, 1711–1733 (2019).
Abdollahi, S., Deldari, A., Asadi, H., Montazerolghaem, A. & Mazinani, S. M. Flow-aware forwarding in SDN datacenters using a knapsack-PSO-based solution. IEEE Trans. Netw. Serv. Manag. 18(3), 2902–2914 (2021).
Author information
Authors and Affiliations
Contributions
All the authors equally contributed towards this work.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Naqvi, S.A.A., Ashraf, F., Ovais, A. et al. Optimizing hybrid network topologies in communication networks through irregularity strength. Sci Rep 15, 29330 (2025). https://doi.org/10.1038/s41598-025-05631-8
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1038/s41598-025-05631-8