Abstract
Bipolar complex fuzzy set (BCFS) theory is a newly developed framework for addressing real-world decision-making (DM) problems that involve ambiguous, uncertain, and dual-valued information. The theory is based on bipolar fuzzy set (BFS) and complex fuzzy set (CFS), which enable the association of both positive membership degree (PMD) and negative membership degrees (Ne-MD) within the unit square of the complex plane. This paper considers the use of Aczel-Alsina (AA) operational laws in the BCFS setting to introduce two new aggregation operators (AOs): bipolar complex fuzzy Choquet integral Aczel-Alsina averaging (BCFCIAAA) and order averaging (BCFCIAAOA). These operators are studied analytically in terms of essential properties, such as idempotency, monotonicity, and boundedness. To demonstrate the superiority of the proposed approach, we develop a hybrid DM model that combines the decision-making trial and evaluation laboratory (DEMATEL) method with the Choquet integral (CI) within the BCFS framework. This model is applied to a real-world case study focused on prioritizing critical factors influencing the integration of image processing and big data analytics (IP-BDA) into software development. The causal effects indicate that feature extraction, automation and efficiency, as well as object detection, are critical causal factors, whereas image enhancement, security, and segmentation are dependent effects. These findings offer actionable insights for decision-makers (DMKs), emphasizing the importance of intelligent feature handling and scalable analytics workflows in designing adaptive and high-performance software systems.
Similar content being viewed by others
Introduction
In everyday life, one must deal with obscure and complicated information to reach a firm conclusion. The crisp set theory only deals with the MD of an element in the form of \(0\) or \(1,\) but falls short when dealing with MD somewhere between 0 and \(1\). Keeping this in view, Zadeh1 introduced the notion of a Fuzzy Set (FS): a generalization of crisp set theory to cope with such situations. In FS, the membership of an element lies in the unit interval \(\left[\text{0,1}\right]\). Later on, various researchers investigated the concepts of FS and fuzzy logic to address real-world issues involving vague and ambiguous environments. Real-world scenarios involve the existence as well as absence of certain traits/elements, and the fuzzy set theory lacks in such scenarios because it only involves MD. Atanassov2 appeared with the concept of an intuitionistic fuzzy set (IFS) as which involves MD as well as the non-membership degree (n-MD) of an element. In IFS, the MD and n-MD belong to the unit interval \(\left[\text{0,1}\right]\) with a given condition such that the sum of MD and n-MD should be less than \(1\). IFS proved to be a significant step for the generalization of the FS. Atanassov and Gargov3 proposed an interval-valued intuitionistic fuzzy set (IV-IFS) to handle ambiguous and complex data. The MD and n-MD are expressed in the form of intervals, and the values lie in the unit interval \(\left[\text{0,1}\right]\). Later, researchers observed that a larger portion of DM relies on dual aspects or bipolar judgmental thinking, which involves considering both positive and negative perspectives. For instance, decisions often involve both direct effects and unintended consequences, as well as personal preferences and dislikes. This observation led Zhang4 to propose the notion of a BFS: An extension of FS. BFS involved positive membership (P-MD) and negative membership degree (Ne-MD). A variety of natural scenarios are complex and cannot be represented using one-dimensional variables. For example, the objects are characterized by a set of measurements in pattern recognition, forming a vector in a multidimensional space. It is often impractical to explain this multidimensional data through a simple combination of one-dimensional variables and operators, particularly when considering a collection of values where each value is a fuzzy number. Due to the advanced approach of BFSs in handling uncertainty and vagueness in DM processes, Akram et al.5 discussed MCDM methods with BCFSs, explored MCGDM for green supplier selection under the BFS PROMETHEE process6, and applied TOPSIS and ELECTRE-I methods for BCFSs7. In contrast, Ramot et al.8 proposed a unique concept of a complex fuzzy set (CFS) by extending the P-MD function to the unit circle in the complex plane. He onboarded an additional phase term to handle complex issues that facilitate the translation of human language into complex-valued functions and vice versa. Alkouri and Salleh9 extended the idea of CFS to Complex IFS (CIFS). Furthermore, the issues and problems in mathematics and real life are often ambiguous and uncertain. In the case of CFS, there are significant challenges in handling uncertain and noisy data. In response, Mahmood and Rehman10 introduced the most widely known BCFS theory to analyze real-world issues by employing positive and negative singular values (SGs) in the structure of complex numbers. The distinction between these grades lies in their definitions: The positive SG is mapped from the universal set to \(\left[\text{0,1}\right]+i\left[\text{0,1},\right]\) while the negative SG is mapped to \(\left[-\text{1,0}\right]+i\left[-\text{1,0}\right]\). BCFSs have many distinct advantages over the previously established FSs, BFSs, and CFSs due to the negative SG in their structure.
Triangular norms (TNs) and triangular conorms (TCNs) play a crucial role in fuzzy logic for modeling conjunction (AND) and disjunction (OR) operations, respectively. These norms serve as the foundational basis for aggregating fuzzy values while preserving properties such as associativity, commutativity, and monotonicity. In 1942, TN was first defined by Menger11 as a part of his theory of probabilistic metric spaces. Later on, Aczél and Alsina12 defined the Aczél-Alsina triangular norm (AA-TN) and conorm (AA-TCN) that are characterized by parameter flexibility. Liu13 proposed the Einstein TN and TCN, as well as several new atomic orbitals (AOs). Although there are various TNs and TCNs but AA-TN and AA-TCN show greater flexibility in complex environments. Moreover, aggregation operators (AOs) are tools that are used to take multiple values or factors as input and provide an optimal resultant outcome based on the given data. AOs attracted the attention of researchers due to their vital role in different DM processes. Various AOs have been developed by utilizing AA-TNs and AA-TCNs. Hussain et al.14 structured picture fuzzy set Aczel-Alsina (PFSAA) AOs and provided an application to DM. Mahmood et al.15 developed AOs based on BCFS by utilizing the AA-TN and AA-TCN. Later on, Zulqarnain et al.16 studied aggregation strategies that have enabled us to realize the strength of interval-valued Pythagorean fuzzy soft sets in multi-attribute group decision-making problems (MAGDM), prompting us to utilize equally robust mechanisms for uncertainty modeling. Similarly, the interval-valued neutrosophic hypersoft sets17 and their application in decision analysis contexts18, including the evaluation of COVID-19 sanitizers, underscore the growing importance of fine grained data modeling in complex systems. The feedback-driven DM structures we have been working on within the framework of T-spherical fuzzy environments19 enable contextual prioritization, which is central to our analysis of software development factors. Additionally, some approaches based on Pythagorean fuzzy hypersoft aggregation20, q-rung orthopair fuzzy soft set-based cloud service provider selection21, and neutrosophic hypersoft matrices22 have highlighted the need for flexible and adaptive decision models in high-dimensional settings. We are also inspired by the medical diagnosis methods based on Q-rung orthopair fuzzy soft sets23 and by the algorithms developing multipolar neutrosophic soft sets in24, which highlights the essentiality of credible and explainable co-calculation in uncertainty-ridden decisions. Lastly, the interactive aggregation schemes in25 mirror a design philosophy that we follow in our BCF model, which incorporates feedback loops and models dependencies among decision factors. Combining these pertinent results, the model we propose fits in rather well within the emerging landscape of fuzzy multi-criteria decision-making (MCDM) models.
Choquet26introduced the theory of the CI in 1954. One of the most essential features of these operators is that they can model the interactions between preferences or criteria. Thus, the resultant outcome is reflected in the formula of the CI operator as a mathematical expression. Moreover, it is possible to determine the correlative dependencies of sets of criteria with the help of fuzzy measures. These fuzzy measures generalize the concept of weights because, unlike the case of the fuzzy measure of the whole set that must be one, the sum of fuzzy measures of sets of criteria may be greater than one. Due to the assumption of criterion independence, previously discussed BCF AOs have been developed. Criteria are dependent on the MCDM problem. In such cases, the assessments cannot be aggregated using the weighted AOs, and the importance of the requirements is represented by a fuzzy measure instead of weights, which provides greater flexibility. CI can be used as a method of aggregating assessments under conditions of dependence between criteria. Many researchers worked on the advancement and applications of the CI. For instance, Murofushi et al.27, discussed the CI in terms of the non-monotonic fuzzy measures with an example to show that this integral is helpful in the case of non-monotonic fuzzy measures as well as in ordinary fuzzy measures. Wang and Yan28 elaborated on a few applications of the CI in a fuzzy environment. Tan and Chen29proposed the intuitionistic fuzzy CI (IFCI) operator, which incorporated the CI into the IF setting. To provide a deeper analysis of the project matching issues in public–private partnerships, Wang et al.30, used the IFCI to integrate the IFSs. Further, the CI is used in solving real-life problems. For example, Büyüközkan and Göçer31 proposed methodologies derived from IF information to select smart medical devices in a DM context. Garg et al. introduced new approaches with interval-valued IF information with the help of AA aggregation tools and the CI operator. To establish the reliable properties of the CI operator, Jia and Wang32 introduced some CI AOs within the IF landscape and proposed an application to MCDM. Sha and Shao33 explained the Fermatean fuzzy sets combined with the CI operator.
In 1971, Gabus and Fontela developed the DEMATEL method to clarify the mutual relationships and interdependencies between various criteria. This technique generates a cause-and-effect diagram that visually presents the mutual relationships and influences among criteria. DEMATEL can analyze comprehensive relationships among the sets of variables to establish logical and direct impact connections. This method is particularly effective when it becomes necessary to enhance the evaluation of one criterion by introducing new ones, even if the number of criteria is quite large. In other DM approaches, such as AHP or TOPSIS, the use of an unrestricted number of criteria can lead to increased decision complexity and decreased decision quality. In contrast, DEMATEL manages large sets of criteria by categorizing them into two groups — cause and effect —and visualizing their causal relationships. DEMATEL is helpful in various DM processes that involve a wide range of criteria, often with potentially incomplete and inconsistent information that needs to be considered. Wu and Tsai34 explored DEMATEL and proposed its application in the auto spare parts industry. Wu and Lee35 developed an efficient method that combines fuzzy logic and DEMATEL to identify and organize key competencies, supporting the growth of global managers. Seker and Zavadskas36 utilized DEMATEL to assess the causal relation of accidents on construction sites. Govindan et al.37 illustrated the DEMATEL method, based on IFS, for developing green practices at the corporate level within the supply chain management system. Govindan and Chaudhuri38 proposed a detailed analysis based on DEMATEL and discussed interrelationships between risks faced by third-party logistics service providers (3PLs) about their customers.
The evolution of software development has become increasingly inclined towards state-of-the-art technologies, such as IP-BDA, to cater to the growing need for intelligent, adaptive, and high-performance systems. IP has formed the foundation for sectors like computer vision, pattern recognition, and visual automation. According to Gonzalez39 and Szeliski40, this method is instrumental in enabling machines to derive usable information from visual input, thereby framing applications such as facial recognition, optical character recognition (OCR), and medical diagnostics. The incorporation of IP into software systems facilitates improved human–computer interaction, automatic monitoring, and visual DM capabilities. At the same time, BDA has become a vital component in data-driven software systems. The capacity to analyze large-scale, high-velocity, and high-variety data, as noted by Brown et al.41 and Hashem et al.42, enables the development of software that is not only reactive but also predictive and prescriptive. BDA technology, including data mining, machine learning, and stream analytics, enables software to discover previously undetected patterns, optimize processes, and provide a tailored experience. These abilities are particularly needed in sectors such as healthcare, e-commerce, smart cities, and finance. The synergy between IP-BDA has been highlighted by recent research. For instance, in healthcare systems, image-based diagnostics can be combined with the analytics of patient history and demographic data to enhance the accuracy of diagnostics and treatment recommendations43. In industrial automation, the combination of real-time image inspection with predictive analytics is practical for fault detection and preventive maintenance44. In addition, integration of IP and BDA plays a key role in enhancing intelligent software systems such as autonomous vehicles, surveillance platforms, and adaptive user interfaces. Moreover, the contributions of IP-BDA in software development are shown in Fig. 1.
Contributions of image processing and big data analytics in software development.
The past few years have witnessed the intersection of IP-BDA, which has become a significant factor in shaping contemporary software development. IP provides a means to extract meaningful information in visual data, whereas BDA offers the means to analyze and interpret very large, heterogeneous, and changing datasets. The combination enables intelligent automation, enhances system flexibility, and facilitates real-time DM in areas such as healthcare, surveillance, smart cities, and autonomous systems. Nonetheless, it is pretty challenging to incorporate those technologies to the creation of software. The complexity of both the technical and contextual factors involved in it makes the DM process in such environments full of uncertainty, ambiguity, and conflicting information. Central challenges include handling heterogeneous data sources, ensuring the scalability of algorithms, maintaining security, achieving real-time capabilities, and scaling system functionality to meet the evolving needs of users.
Problem statement
Despite the growing relevance of IP-BDA in software engineering, there is a lack of robust DM frameworks capable of evaluating and prioritizing critical factors under conditions of ambiguity, uncertainty, and dual-valued reasoning. Existing approaches often fall short in modelling interdependencies among factors, fail to capture both positive and negative contributions, and lack the flexibility to handle complex-valued information effectively.
Motivation
The study is driven by the desire to provide developers, system architects, and managers in software development with a more expressive and trustworthy instrument for evaluating key factors related to IP and BDA integration. To achieve the effectiveness of a software solution for data-intensive and image-driven applications, a method is needed that can capture the subtle interactions of multiple criteria and consider uncertainties.
Research gap
Despite the similar contexts of fuzzy set theories and multi-criteria MCDM methods, the majority of available models are either specialized in single-valued uncertainties or do not consider the bipolar nature of the decision space. Moreover, CI and sophisticated aggregation techniques are rarely used in the context of BCF information, especially in the field of software engineering.
Novelty and objectives
The proposed paper will bridge this gap by introducing a new hybrid structure that utilizes DEMATEL-CI within the BCFS landscape and the AA AOs for aggregation purposes. The primary contributions are:
-
We developed BCFCIAAA and BCFCIAAOA AOs in this article and discussed their authenticity.
-
The combination of these operators with DEMATEL under a BCFS environment to model interdependencies.
-
The model was applied to a real-world case study aimed at identifying and prioritizing key factors that impact on integration of IP and BDA in software development.
-
This integrated framework enables the modeling of complex interrelationships, uncertain information, and conflicting perspectives among the criteria. Furthermore, the cause-effect relationships provide practical recommendations to developers.
The structure of this manuscript is as follows: Section 2 discusses the fundamental concepts of TNs, AA aggregation tools, BCFSs, and their basic operations. Section3 illustrates some reliable operations of AA-TNs under BCFSs. Section 4 presents the developed BCFCIAAA and BCFCIAAOA AO along with their fundamental properties. Section 5 presents the algorithm for the DEMATEL-CI within the BCF environment. Section 6 contains a case study on IP-BDA in Software Development. Section 7 comprises of sensitivity analysis of the said AOs and methodology. Section 8 involves a comparison of the proposed methodology and AOs with previously well-known methods and AOs. Section 9 concludes the article, outlining future research directions.
Preliminaries
In this section, the concepts of TN, TCN, AA-TN, and AA-TCN are discussed. Furthermore, the theory of BCFSs and the algebraic operational laws governing BCFSs are provided. The purpose of this section is to develop a better understanding of further developments made in this article.
Definition 1
11A function \({\rm T}:\left[\text{0,1}\right]\times \left[\text{0,1}\right]\to \left[\text{0,1}\right]\) is known as T-N if it satisfies the following axiom11:
-
1.
\({\rm T}\left(\varsigma ,\varepsilon \right)={\rm T}\left(\varepsilon ,\varsigma \right)\)
-
2.
If \(\varepsilon \le \vartheta\) , then \({\rm T}\left(\varsigma ,\varepsilon \right)\le {\rm T}\left(\varsigma ,\vartheta \right)\)
-
3.
\({\rm T}\left(\varsigma ,\varepsilon \right)\le {\rm T}\left(\varsigma ,\vartheta \right)\)
-
4.
\({\rm T}\left(\varsigma ,1\right)=\varsigma\)
Where \(\varsigma ,\varepsilon , \vartheta \in \left[\text{0,1}\right].\)
Definition 2
A function \({\rm{S}}:\left[\text{0,1}\right]\times \left[\text{0,1}\right]\to \left[\text{0,1}\right]\) is known as T-CN if it satisfies the following axiom11:
-
1.
\({\rm{S}}\left(\varsigma ,\varepsilon \right)= {\rm{S}}\left(\varepsilon ,\varsigma \right)\)
-
2.
If \(\varepsilon \le \vartheta\), then\({\rm{S}}\left(\varsigma ,\varepsilon \right)\le {\rm{S}}\left(\varsigma ,\vartheta \right)\)
-
3.
\({\rm{S}}\left(\varsigma , {\rm{S}}\left(\varepsilon ,\vartheta \right)\right)= {\rm{S}}\left( {\rm{S}}\left(\varsigma ,\varepsilon \right),\vartheta \right)\)
-
4.
\({\rm{S}}\left(\varsigma ,0\right)=\varsigma\)
Where \(\varsigma ,\varepsilon , \vartheta \in \left[\text{0,1}\right]\).
Definition 3
Aczel-Alsina provided an interpretation of the T-N and T-CN within the context of functional equations that are characterized as follows12:
And
where \(\Gamma>1.\) \({{\rm T}}^{D}, { {\rm{S}}}^{D}\) represent discrete T-N and discrete T-CN respectively.
Definition 4
A BCF information associated to the universal set X is characterized as10:
Clearly,
\({\xi }_{P-\mathcal{L}}\left(\mathcal{x}\right)={\xi }_{RP-\mathcal{L}}\left(\mathcal{x}\right)+{l\xi }_{IP-\mathcal{L}}\left(\mathcal{x}\right)\) and \({\xi }_{N-\mathcal{L}}\left(\mathcal{x}\right)={\xi }_{RN-\mathcal{L}}\left(\mathcal{x}\right)+{l\xi }_{IN-\mathcal{L}}\left(\mathcal{x}\right)\), found as the supporting and supporting against terms with \({\xi }_{RP-\mathcal{L}}\left(\mathcal{x}\right), {\xi }_{IP-\mathcal{L}}\left(\mathcal{x}\right)\in \left[\text{0,1}\right]\) and \({\xi }_{RN-\mathcal{L}}\left(\mathcal{x}\right), {\xi }_{IN-\mathcal{L}}\left(\mathcal{x}\right)\in \left[\text{0,1}\right]\). The term \(\mathcal{L}=\left({\xi }_{P-\mathcal{L}}\left(\mathcal{x}\right),{\xi }_{N-\mathcal{L}}\left(\mathcal{x}\right)\right)=\left({\xi }_{RP-\mathcal{L}}\left(\mathcal{x}\right)+{l\xi }_{IP-\mathcal{L}}\left(\mathcal{x}\right),{\xi }_{RN-\mathcal{L}}\left(\mathcal{x}\right)+{l\xi }_{IN-\mathcal{L}}\left(\mathcal{x}\right)\right)\), simplified the BCF numbers (BCFNs).
Definition 5
The score value of a BCFN is characterized as10:
Definition 6
The accuracy value of a BCFN is characterized as10:
Theorem 1
Let\({ \mathcal{L}}_{1}=\left({\xi }_{P-{\mathcal{L}}_{1}}\left(\mathcal{x}\right),{\xi }_{N-{\mathcal{L}}_{1}}\left(\mathcal{x}\right)\right)=\) \(\left({\xi }_{RP-{\mathcal{L}}_{1}}\left(\mathcal{x}\right)+{l\xi }_{IP-{\mathcal{L}}_{1}}\left(\mathcal{x}\right),{\xi }_{RN-{\mathcal{L}}_{1}}\left(\mathcal{x}\right)+{l\xi }_{IN-{\mathcal{L}}_{1}}\left(\mathcal{x}\right)\right)\) and \({\mathcal{L}}_{2}=\left({\xi }_{P-{\mathcal{L}}_{2}}\left(\mathcal{x}\right),{\xi }_{N-{\mathcal{L}}_{2}}\left(\mathcal{x}\right)\right)=\) \(\left({\xi }_{RP-{\mathcal{L}}_{2}}\left(\mathcal{x}\right)+{l\xi }_{IP-{\mathcal{L}}_{2}}\left(\mathcal{x}\right),{\xi }_{RN-{\mathcal{L}}_{2}}\left(\mathcal{x}\right)+{l\xi }_{IN-{\mathcal{L}}_{2}}\left(\mathcal{x}\right)\right)\) are given two BCFNs. Basic operations for BCFNs are given as10:
-
1.
\({\mathcal{L}}_{1}\oplus{\mathcal{L}}_{2}={\mathcal{L}}_{2}\oplus{\mathcal{L}}_{1}\)
-
2.
\({\mathcal{L}}_{1}\oplus{\mathcal{L}}_{2}={\mathcal{L}}_{2}\oplus{\mathcal{L}}_{1}\)
-
3.
\(\left({\mathcal{L}}_{1}\oplus{\mathcal{L}}_{2}\right)={\mathcal{}\mathcal{L}}_{2}\oplus{\mathcal{}\mathcal{L}}_{1}\)
-
4.
\({\left({\mathcal{L}}_{1}\oplus{\mathcal{L}}_{2}\right)}^{}={{\mathcal{L}}_{1}}^{} \oplus{{\mathcal{L}}_{2}}^{}\)
-
5.
\({{}_{1}\mathcal{L}}_{1}\oplus{}_{2}{\mathcal{L}}_{1}=\left({}_{1}\oplus{}_{2}\right){\mathcal{L}}_{1}\)
-
6.
\({{\mathcal{L}}_{1}}^{{}_{1}}\oplus{{\mathcal{L}}_{1}}^{{}_{2}}={{\mathcal{L}}_{1}}^{{}_{1}\oplus{}_{2}}\)
-
7.
\({\left({{\mathcal{L}}_{1}}^{{}_{1}}\right)}^{{}_{2}}={{\mathcal{L}}_{1}}^{{}_{1}{}_{2}}\)
Where \(,{}_{1},{}_{2}>0\).
Aczel-Alsina operational laws utilizing BCFNs.
This section focuses on the AA operational laws defined for the BCFSs along with their proofs. The AA-TNs play a vital role in establishing the AA operational laws within the BCFS framework and provide a foundational base for the development of AOs. These operations are responsible for fusing and interacting with the BCF information, which enables the model to effectively handle non-linear dependencies and uncertain dual-valued data. Further, the theory of fuzzy measure and CI is also explored for further use in the proposed work.
Definition 7
Let \({\mathcal{L}}_{1}=\left({\xi }_{P-{\mathcal{L}}_{1}}\left(\mathcal{x}\right),{\xi }_{N-{\mathcal{L}}_{1}}\left(\mathcal{x}\right)\right)=\left({\xi }_{RP-{\mathcal{L}}_{1}}\left(\mathcal{x}\right)+{l\xi }_{IP-{\mathcal{L}}_{1}}\left(\mathcal{x}\right),{\xi }_{RN-{\mathcal{L}}_{1}}\left(\mathcal{x}\right)+{l\xi }_{IN-{\mathcal{L}}_{1}}\left(\mathcal{x}\right)\right)\) and \({\mathcal{L}}_{2}=\left({\xi }_{P-{\mathcal{L}}_{2}}\left(\mathcal{x}\right),{\xi }_{N-{\mathcal{L}}_{2}}\left(\mathcal{x}\right)\right)=\left({\xi }_{RP-{\mathcal{L}}_{2}}\left(\mathcal{x}\right)+{l\xi }_{IP-{\mathcal{L}}_{2}}\left(\mathcal{x}\right),{\xi }_{RN-{\mathcal{L}}_{2}}\left(\mathcal{x}\right)+{l\xi }_{IN-{\mathcal{L}}_{2}}\left(\mathcal{x}\right)\right)\) are given two BCFNs. AA operational laws based on AA-TN and AA-TCN utilizing BCFNs are characterized as:
-
1.
\(\begin{aligned} &{ \mathcal{L}}_{1}\oplus{\mathcal{L}}_{2}= \\ & \left(\begin{array}{c}1-{e}^{-{\left({\left(-\text{log}\left(1-{\xi }_{RP-{\mathcal{L}}_{1}}\right)\right)}^{\varrho }+{\left(-\text{log}\left(1-{\xi }_{RP-{\mathcal{L}}_{2}}\right)\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}\\ +l\left(1-{e}^{-{\left({\left(-\text{log}\left(1-{\xi }_{IP-{\mathcal{L}}_{1}}\right)\right)}^{\varrho }+{\left(-\text{log}\left(1-{\xi }_{IP-{\mathcal{L}}_{2}}\right)\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}\right)\\ -\left({e}^{-{\left({\left(-\text{log}\left|{\xi }_{RN-{\mathcal{L}}_{1}}\right|\right)}^{\varrho }+{\left(-\text{log}\left|{\xi }_{RN-{\mathcal{L}}_{2}}\right|\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}\right)+l\left(-\left({e}^{-{\left({\left(-\text{log}\left|{\xi }_{IN-{\mathcal{L}}_{1}}\right|\right)}^{\varrho }+{\left(-\text{log}\left|{\xi }_{IN-{\mathcal{L}}_{2}}\right|\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}\right)\right)\end{array}\right) \end{aligned}\)
-
2.
\(\begin{aligned} &{ \mathcal{L}}_{1}\oplus{\mathcal{L}}_{2}= \\ &\left(\begin{array}{c}{e}^{-{\left({\left(-\text{log}\left({\xi }_{RP-{\mathcal{L}}_{1}}\right)\right)}^{\varrho }+{\left(-\text{log}\left({\xi }_{RP-{\mathcal{L}}_{2}}\right)\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}+l\left({e}^{-{\left({\left(-\text{log}\left({\xi }_{IP-{\mathcal{L}}_{1}}\right)\right)}^{\varrho }+{\left(-\text{log}{\xi }_{IP-{\mathcal{L}}_{2}}\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}\right)\\ -1+{e}^{-{\left({\left(-\text{log}\left(1+{\xi }_{RN-{\mathcal{L}}_{1}}\right)\right)}^{\varrho }+{\left(-\text{log}\left(1+{\xi }_{RN-{\mathcal{L}}_{2}}\right)\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}\\ +l\left(-1+{e}^{-{\left({\left(-\text{log}\left(1+{\xi }_{IN-{\mathcal{L}}_{1}}\right)\right)}^{\varrho }+{\left(-\text{log}\left(1+{\xi }_{IN-{\mathcal{L}}_{2}}\right)\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}\right)\end{array}\right)\end{aligned}\)
-
3.
\(\begin{aligned} &{ \mathcal{L}}_{1}=\\ &\left(\begin{array}{c}1-{e}^{-{\left({\left(-\text{log}\left(1-{\xi }_{RP-{\mathcal{L}}_{1}}\right)\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}+l\left(1-{e}^{-{\left({ \left(-\text{log}\left(1-{\xi }_{IP-{\mathcal{L}}_{1}}\right)\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}\right),\\ -\left({e}^{-{\left({ \left(-\text{log}\left|{\xi }_{RN-{\mathcal{L}}_{1}}\right|\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}\right)+l\left(-\left({e}^{-{\left({ \left(-\text{log}\left|{\xi }_{IN-{\mathcal{L}}_{1}}\right|\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}\right)\right)\end{array}\right)\end{aligned}\)
-
4.
\(\begin{aligned} &{{ \mathcal{L}}_{1}}^{ }= \\&\left(\begin{array}{c}{e}^{-{\left({ \left(-\text{log}\left|{\xi }_{RP-{\mathcal{L}}_{1}}\right|\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}+l\left({e}^{-{\left({ \left(-\text{log}\left|{\xi }_{IP-{\mathcal{L}}_{1}}\right|\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}\right),\\ -1+{e}^{-{\left({ \left(-\text{log}\left(1+{\xi }_{RN-{\mathcal{L}}_{1}}\right)\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}+l\left(-1+{e}^{-{\left({ \left(-\text{log}\left(1+{\xi }_{IN-{\mathcal{L}}_{1}}\right)\right)}^{\varrho }\right)}^{\frac{1}{\varrho }}}\right)\end{array}\right)\end{aligned}\)
Theorem 2
Let \({\mathcal{L}}_{1}=\left({\xi }_{P-{\mathcal{L}}_{1}}\left(\mathcal{x}\right),{\xi }_{N-{\mathcal{L}}_{1}}\left(\mathcal{x}\right)\right)=\left({\xi }_{RP-{\mathcal{L}}_{1}}\left(\mathcal{x}\right)+{l\xi }_{IP-{\mathcal{L}}_{1}}\left(\mathcal{x}\right),{\xi }_{RN-{\mathcal{L}}_{1}}\left(\mathcal{x}\right)+{l\xi }_{IN-{\mathcal{L}}_{1}}\left(\mathcal{x}\right)\right)\) and \({\mathcal{L}}_{2}=\left({\xi }_{P-{\mathcal{L}}_{2}}\left(\mathcal{x}\right),{\xi }_{N-{\mathcal{L}}_{2}}\left(\mathcal{x}\right)\right)=\left({\xi }_{RP-{\mathcal{L}}_{2}}\left(\mathcal{x}\right)+{l\xi }_{IP-{\mathcal{L}}_{2}}\left(\mathcal{x}\right),{\xi }_{RN-{\mathcal{L}}_{2}}\left(\mathcal{x}\right)+{l\xi }_{IN-{\mathcal{L}}_{2}}\left(\mathcal{x}\right)\right)\) are given two BCFNs with \(,{ }_{1},{}_{2}>0\). Then:
-
1.
\({\mathcal{L}}_{1}\oplus{\mathcal{L}}_{2}={\mathcal{L}}_{2}\oplus{\mathcal{L}}_{1}\)
-
2.
\({\mathcal{L}}_{1}\oplus{\mathcal{L}}_{2}={\mathcal{L}}_{2}\oplus{\mathcal{L}}_{1}\)
-
3.
\(\left({\mathcal{L}}_{1}\oplus{\mathcal{L}}_{2}\right)={\mathcal{ }\mathcal{L}}_{2}\oplus{\mathcal{ }\mathcal{L}}_{1}\)
-
4.
\({\left({\mathcal{L}}_{1}\oplus{\mathcal{L}}_{2}\right)}^{ }={{\mathcal{L}}_{1}}^{} \oplus{{\mathcal{L}}_{2}}^{ }\)
-
5.
\(\left({ }_{1}\oplus{ }_{2}\right){\mathcal{L}}_{1}={{ }_{1}\mathcal{L}}_{1}\oplus{ }_{2}{\mathcal{L}}_{1}\)
-
6.
\({{\mathcal{L}}_{1}}^{{ }_{1}}\oplus{{\mathcal{L}}_{1}}^{{ }_{2}}={{\mathcal{L}}_{1}}^{{ }_{1}\oplus{ }_{2}}\)
Proof.
See appendix section, appendix A.
Definition 8
A function \(\wp :\mathcal{P}\left(V\right)\to \left[\text{0,1}\right]\) on a given set \(V\) is termed a fuzzy measure if it satisfies the below two conditions:
-
1.
\(\wp \left(\varnothing \right)=0, \wp \left(\varnothing \right)=1\)
-
2.
If \(\mathfrak{L},\mathfrak{P}\in \mathcal{P}\left(V\right)\) and \(\mathfrak{L}\subseteq \mathfrak{P}\), then \(\wp \left(\mathfrak{L}\right)=\wp \left(\mathfrak{P}\right)\)
Definition 9
For any non-negative real-valued function \({\mathbb{F}}\) and a fuzzy measure \(\wp\) on \(V\). The CI \(\mathcal{C}\) of \({\mathbb{F}}\) is defined as:
where \(\left(\mathcal{j}\right)\) is a collection of permutations on \(V\), such that \({\mathbb{F}}_{\left(1\right)}\ge {\mathbb{F}}_{\left(2\right)}\ge ,\dots ,\ge {\mathbb{F}}_{\left(\mathcal{n}\right)}\) and \({\mathfrak{L}}_{\left(\mathcal{j}\right)}=\left\{\mathcal{j}=\text{1,2},\dots ,\mathcal{n}\right\},{\mathfrak{L}}_{\left(\mathcal{j}+1\right)}=\phi .\)
Aczel-Alsina aggregation averaging operators using BCF information
In this segment, we proposed new averaging AOs within the BCF environment utilizing the CI and AA operational laws. The proposed methodologies include BCFCIAAA and BCFCIAAOA operators. Further, the fundamental properties of these AOs are also verified here to check the authenticity of the proposed work.
Let \({\mathcal{L}}_{\mathcal{j}}=\left({\xi }_{P-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right),{\xi }_{N-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right)\right)=\) \(\left({\xi }_{RP-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right)+{l\xi }_{IP-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right),{\xi }_{RN-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right)+{l\xi }_{IN-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right)\right),\mathcal{j}=\text{1,2},\dots ,\mathcal{n}\) be a collection of BCFNs and \(\mathcal{w}={\mathcal{w}}_{1},{\mathcal{w}}_{2},\dots ,{\mathcal{w}}_{\mathcal{n}}\) represents weight vector of \({\mathcal{L}}_{\mathcal{j}},\mathcal{j}=\text{1,2},\dots , \mathcal{n}\).
Definition 10
The BCFCIAAA operator is characterized as:
Theorem 3
The aggregated value of BCFN by utilizing the \(BCFCIAAA\) operator is also a BCFN and given as:
Proof.
See appendix section, appendix B.
Theorem 4
Let \({\mathcal{L}}_{\mathcal{j}}=\left({\xi }_{P-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right),{\xi }_{N-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right)\right)=\left({\xi }_{RP-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right)+l{\xi }_{IP-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right),{\xi }_{RN-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right)+l{\xi }_{IN-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right)\right),\mathcal{j}=\text{1,2},\dots ,\mathcal{n}\) be a collection of BCFNs. Then:
Proof.
See appendix section, appendix C.
Theorem 5
For given \({\mathcal{L}}_{\mathcal{j}}\le {\mathcal{L}}_{\mathcal{j}}^{*}\forall \mathcal{j}\) i.e., \({\xi }_{RP-{\mathcal{L}}_{\mathcal{j}}}\le {\xi }_{RP-{\mathcal{L}}_{\mathcal{j}}^{*}}\),\({\xi }_{IP-{\mathcal{L}}_{\mathcal{j}}}\le {\xi }_{IP-{\mathcal{L}}_{\mathcal{j}}^{*}}\),\({\xi }_{RN-{\mathcal{L}}_{\mathcal{j}}}\le {\xi }_{RN-{\mathcal{L}}_{\mathcal{j}}^{*}}\) and \({\xi }_{IN-{\mathcal{L}}_{\mathcal{j}}}\le {\xi }_{IN-{\mathcal{L}}_{\mathcal{j}}^{*}}\), it is provided that:
Proof.
See appendix section, appendix D.
Theorem 6
For given \({\mathcal{L}}^{L}=\text{min}\left({\mathcal{L}}_{1},{\mathcal{L}}_{2},\dots ,{\mathcal{L}}_{\mathcal{n}}\right)\) and \({\mathcal{L}}^{U}=\text{max}\left({\mathcal{L}}_{1},{\mathcal{L}}_{2},\dots ,{\mathcal{L}}_{\mathcal{n}}\right).\) We may write.
Proof.
See appendix section, appendix E.
Definition 11
The BCFCIAAOA operator is characterized as:
where \(\left(\Xi \left(1\right),\Xi \left(2\right),\dots ,\Xi \left(\mathcal{n}\right)\right)\) denotes the permutation of \(\mathcal{j}=\text{1,2},\dots ,\mathcal{n}\) for which \({\mathcal{L}}_{\Xi \left(\mathcal{j}-1\right)}\ge {\mathcal{L}}_{\Xi \left(\mathcal{j}\right)}\forall \mathcal{j}\).
Theorem 7
The aggregated value of BCFNs utilizing the BCFCIAAOA operator is again a BCFN and is given as:
Proof.
The proof of Theorem 7 is the same as the proof of Theorem 3.
Theorem 8
Let \({\mathcal{L}}_{\mathcal{j}}=\left({\xi }_{P-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right),{\xi }_{N-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right)\right)\) \(=\left({\xi }_{RP-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right)+l{\xi }_{IP-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right),{\xi }_{RN-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right)+l{\xi }_{IN-{\mathcal{L}}_{\mathcal{j}}}\left(\mathcal{x}\right)\right),\mathcal{j}=\text{1,2},\dots ,\mathcal{n}\) be a collection of BCFNs. Then:
Proof.
The proof of Theorem 8 is the same as the proof of Theorem 4.
Theorem 9
For given \({\mathcal{L}}_{\mathcal{j}}\le {\mathcal{L}}_{\mathcal{j}}^{*}\forall \mathcal{j}\) i.e., \({\xi }_{RP-{\mathcal{L}}_{\mathcal{j}}}\le {\xi }_{RP-{\mathcal{L}}_{\mathcal{j}}^{*}}\),\({\xi }_{IP-{\mathcal{L}}_{\mathcal{j}}}\le {\xi }_{IP-{\mathcal{L}}_{\mathcal{j}}^{*}}\),\({\xi }_{RN-{\mathcal{L}}_{\mathcal{j}}}\le {\xi }_{RN-{\mathcal{L}}_{\mathcal{j}}^{*}}\) and \({\xi }_{IN-{\mathcal{L}}_{\mathcal{j}}}\le {\xi }_{IN-{\mathcal{L}}_{\mathcal{j}}^{*}}\), it is provided that:
Proof.
The proof of Theorem 9 is the same as the proof of Theorem 5.
Theorem 10
For given \({\mathcal{L}}^{L}=\text{min}\left({\mathcal{L}}_{1},{\mathcal{L}}_{2},\dots ,{\mathcal{L}}_{\mathcal{n}}\right)\) and \({\mathcal{L}}^{U}=\text{max}\left({\mathcal{L}}_{1},{\mathcal{L}}_{2},\dots ,{\mathcal{L}}_{\mathcal{n}}\right)\). We may write.
Proof.
The proof of Theorem 10 is the same as the proof of Theorem 6.
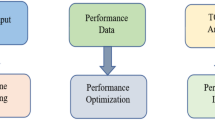
Proposed DEMATEL method infused with Choquet integral within BCF landscape
This article involves the integration of BCFSs and CI into the DEMATEL methodology. It presents a novel preference scale for DEMATEL and assigns weights to DMKs in terms of BCFNs, which encompass P-MD, Ne-MD, and HD. The aggregation of DMK’s preferences is achieved by using the BCFCIAA operator. Additionally, the proposed method employs a BCF entropy measure for normalization. The involvement of the CI in structural correlation analysis addresses the issues of interrelationships between the sum of rows and columns in the proposed method. The distinct advantages of the proposed DEMATEL-CI method within the BCF environment are discussed below:
-
By integrating BCFNs, the proposed method captures the P-MD, Ne-MD, and HD, offering a richer and more nuanced modeling of uncertainty in DMK’s judgments compared to traditional crisp or fuzzy DEMATEL approaches.
-
By taking into consideration the BCF preferences of numerous DMKs, which is not taken into account by traditional aggregation techniques, the BCFCIAA operator allows for more accurate aggregation of their inputs.
-
The introduction of a BCF entropy-based normalization method ensures a more objective and consistent standardization of data, enhancing the reliability of the causal relationship analysis within the DEMATEL process.
-
A known drawback of conventional DEMATEL approaches is the imbalance between the sum of rows and columns, which is fixed by integrating CI in the analysis of structural correlations. As a result, causal links are represented more accurately and in a more structured manner.
Consider \({\Pi }_{i},i=\text{1,2},\dots ,\beta\) be the criteria to be assessed using the proposed methodology, and \({\mathfrak{w}}_{\boldsymbol{\vartheta }},\vartheta =\text{1,2},\dots , \delta\) represent the weights assigned to DMKs. The proposed DEMATEL-CI method within the BCF environment involves below given steps:
Step 1. In the first step, the preferences of DMKs are collected in the form of linguistic terms.
Step 2. In this step, the DMK’s preferences are converted into BCFNs by using the linguistic preference scale set.
Step 3. The multiple DMK’s preferences are then aggregated using the proposed BCFCIAAA operator given below:
Step 4. Here, the crisp values for the initial direct relation matrix are computed using the BCF entropy/score function given by:
Step 5. The initial direct relation matrix is normalized by dividing each entry \({\Pi }_{ij}\) with the \(\text{\rm M}=\frac{1}{\text{max}\sum_{j=1}^{n}{\Pi }_{ij}},1\le i\le n\). denotes the resultant normalized matrix.
Step 6. Here, in this step, the total relation matrix is calculated using the following expression:
Step 7. Compute \({\Pi }_{R}\) and \({\Pi }_{C}\), which is the sum of each row and column, respectively, in the total relation matrix \({\text T}.\) Further, the value of \({\Pi }_{R}+{\Pi }_{C}\) indicates the relative significance of each criterion, while \({\Pi }_{R}-{\Pi }_{C}\) reveals its role within the system. Specifically, \({\Pi }_{R}-{\Pi }_{C}\) is positive, the criterion is classified as part of the cause group; if negative, it falls into the effect group.
Step 8. The causal diagram is plotted with prominence on the horizontal axis and relation on the vertical axis, enabling the classification of criteria into the cause-and-effect groups.
The flowchart for the proposed DEMATEL-CI algorithm within the BCF environment is presented in Fig. 2.
Algorithm for the DEMATEL method combined with the Choquet integral.
Prioritizing critical factors in image processing and big data analytics for software development using DEMATEL and bipolar complex fuzzy choquet integral
IP-BDA are critical in contemporary software development, enabling intelligent and data-driven solutions across various domains. IP enables software to understand and manipulate visual information used in applications such as facial recognition, medical diagnostics, autonomous vehicles, and augmented reality. On the contrary, the capability of BDA to conduct analysis of large quantities of structured and unstructured data and derive valuable insights, thereby facilitating data mining, performance optimization, and personalization based on user preferences, is enhanced. When combined, these technologies enable developers to build competitive, responsive, and intelligent systems, which are capable of promoting innovation not only in healthcare but also in security, e-commerce, and smart cities, among other fields. Combined, they make a strong base for developing the next generation of contextual and highly adaptive software solutions.
A panel of domain experts is carefully selected to ensure a balanced representation of perspectives. The opinion of each expert is taken into account with a certain weight, which is based on their relative experience and expertise. In this study, we onboarded four domain-experts/DMKs with distinct and complementary backgrounds in software development, BDA, and IP. Purposive sampling was used to select these specialists, ensuring high-level, pertinent insights for ranking the most critical factors. The BCF CI aggregates these weights into the process, and we are able to pick up the individual and collective impact of the experts on the decision matrix. The backgrounds of the experts, the selection criteria, and the weights assigned are outlined in Table 1.
After a thorough review of the literature, the relevant criteria and factors are selected. Image enhancement is one of the essential critical factors in IP, which enhances the visual quality of images, resulting in the usability of images for future analysis45; feature extraction, critical in the reduction of dimensionality with the retention of meaningful information46; segmentation, which selects an area of interest to focus on for individualized DM47; and object detection/recognition is imperative for work in surveillance, autonomous vehicles, and diagnostics in medicine48. Similarly, for BDA, there are improved automation and efficiency, which make the data workflow less complex and ensure real-time insights49; more intelligent and adaptive systems that enable software to learn from patterns and adapt to changes in conditions50; individualized user experiences, based on behavior and preference analysis for better satisfaction and engagement51; and security and fraud detection, which are essential for the protection of sensitive data and the integrity of the system, represent50. All these components contribute to the creation of a landscape in the field of software development, dictate the course of the design functionality, and user outcomes. Based on experts’ recommendations and strategic plan analysis, six priority factors from these domains will be selected for further consideration in DM. The chosen factors/criteria are feature extraction \({\Pi }_{1}\), image enhancement \({\Pi }_{2}\), security and fraud detection \({\Pi }_{3}\), improved automation and efficiency \({\Pi }_{4}\), \(\text{segmentation}\) \({\Pi }_{5}\), and object detection/recognition \({\Pi }_{6}\). The data utilized in the study was gathered through structured expert input, where these experts evaluated and rated the critical factors influencing the integration of IP-BDA into software development. Their evaluations were modeled using the linguistic preference scale presented in Table 2.
Step 1. In the first step, the preferences of DMKs are collected in the form of linguistic terms. These preferences are provided in Table 3,4,5,6. These linguistic preferences are transformed further in the form of BCFNs as per the linguistic preference scale defined in Table 2.
Step 2. The DMK’s preferences are converted into BCFNs by using the linguistic preference scale defined in Table 2. The converted DMK’s preferences are provided in Table 7,8,9,10. Moreover, after conversion, it is ensured that the consensus threshold of DMKs is met by using a distance measure or any other available technique to safeguard a combined meaningful group perspective.
Step 3. The multiple DMK’s preferences are then aggregated using the proposed BCFCIAAA operator given below, and the aggregated decision matrix of combined DMK’s preferences is shown in Table 11.
Step 4. Here, the crisp values for the initial direct relation matrix are computed using the BCF entropy/score function given by:
The decision matrix for crisp values is presented below in Table 12.
Step 5. The initial direct relation matrix is normalized by dividing each entry \({\Pi }_{ij}\) with the \(\text{\rm M}=\frac{1}{\text{max}\sum_{j=1}^{n}{\Pi }_{ij}},1\le i\le n\). The resultant normalized matrix is denoted by \(\mathcal{n}\) and provided in Table 13.
Step 6. Now, we compute the total relation matrix using below given expression:
The Total relation matrix \({\text T}\) is shown in Table 14.
Step 7. Compute \({\Pi }_{R}\) and \({\Pi }_{C}\), which are the sum of each row and column, respectively, in the total relation matrix \({\text T}.\) Further, the value of \({\Pi }_{R}+{\Pi }_{C}\) indicates the relative significance of each criterion, while \({\Pi }_{R}-{\Pi }_{C}\) reveals its role within the system. Specifically, \({\Pi }_{R}-{\Pi }_{C}\) is positive, the criterion is classified as part of the cause group; if negative, it falls into the effect group. \({\Pi }_{R},{\Pi }_{C},{\Pi }_{R}+{\Pi }_{C,}\) and \({\Pi }_{R}-{\Pi }_{C}\) are computed in Table 15.
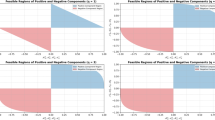
Step 8. In this step, the ranking of the criteria is done based on \({\Pi }_{\text{r}}-{\Pi }_{\text{c}}\) and provided in Table 16. Furthermore, the causal diagram is plotted with \({\Pi }_{\text{r}}+{\Pi }_{\text{c}}\) on the x-axis and \({\Pi }_{\text{r}}-{\Pi }_{\text{c}}\) on the y-axis. As illustrated in Fig. 3, this visual representation facilitates a clearer understanding of the interrelationships among the criteria.
Causal diagram.
The use of the proposed BCFS-based hybrid DM methodology enables the release of a holistic analysis of the key factors that affect the integration of IP-BDA into software development. The study found feature extraction \({\Pi }_{1}\), enhanced automation and efficiency \({\Pi }_{4}\), and object detection/recognition \({\Pi }_{6}\) to be significant cause factors that influence core development functionalities and directly affect system performance and design outcomes. Conversely, image enhancement \({\Pi }_{2}\), security and fraud detection \({\Pi }_{3,}\) and segmentation \({\Pi }_{5}\) were specified as effect factors dependent upon the former product. Such results imply that prioritizing intelligent feature handling, workflow automation, and object-level analysis is crucial for developing adaptive and efficient software solutions, which should be accompanied by visual clarity, system security, and precise data segmentation as consequential benefits.
Sensitivity analysis
A sensitivity analysis was conducted to assess the robustness and stability of the causal relationships derived from the proposed DEMATEL-CI methodology within the BCF landscape. This analysis aims to determine the effect of different expert weights on the classification of factors in cause-and-effect groups. Baseline experts were given a weight vector of \({\left\{\text{0.2,0.2,0.3,0.3}\right\}}^{T}\). The methodology was then reapplied using other weight vectors \({\left\{\text{0.25,0.2,0.3,0.25}\right\}}^{T}\) and \({\left\{\text{0.3,0.3,0.2,0.2}\right\}}^{T}\). Through both sub-alternative scenarios, the classification remained static with feature extraction \({\Pi }_{1}\), improved automation and efficiency \({\Pi }_{4}\), and object detection/recognition \({\Pi }_{6}\) all assessed as cause factors. However, there had been minor movements in the ordering of the effect group factors \(\left({\Pi }_{5},{\Pi }_{3},{\Pi }_{2}\right)\). The DM structure remained the same. Table 17 gives an integrated view of the results.
These results demonstrate that the robustness of the DEMATEL-CI within the BCF landscape is high, particularly with respect to various expert coefficients and varying degrees of uncertainty. The recurrent attribution of fundamental causal factors strengthens the credibility and practical applicability of the model to scenarios in the field of badminton instruction.
Comparative analysis
This comparative study aims to assess the performance of the newly proposed procedure against established state-of-the-art methods, specifically in terms of efficiency, accuracy, and reliability. To determine the effectiveness and improvements of the proposed DEMATEL extension, it is compared against the previously recognized IF DEMATEL method52 and the best–worst method using the fuzzy DEMATEL method53. The analysis includes a comparison of relative significance, uncertainty handling, sensitivity analysis, error detection mechanism, and novelty of study. The results of the comparative analysis of relative significance are presented in Table 18, and the causal diagram associated with the analysis is illustrated in Fig. 4.
Causal diagram illustrating the relative significance through the proposed DEMATEL, IF DEMATEL, and fuzzy best–worst DEMATEL method.
Furthermore, Table 19 presents a comprehensive comparison of the proposed methodology with existing well-known methods.
The above analysis shows that the DEMATEL-CI method within the BCF landscape outperforms other current methods by providing an efficient and resilient DM framework. Its main strengths are the involvement of various DMKs, integration with the CI, and integration with BCFSs, which significantly reduce bias and promote objectivity in DM. These integrations make the outcomes more reliable. This approach to integration makes the proposed method suitable for handling complex DM problems and enhancing the effectiveness and credibility of the DM process.
Validations of results
To verify the soundness and integrity of the proposed BCFS-based hybrid DM approach, a layered validation strategy was employed, comprising sensitivity analysis, comparative model benchmarking, and alignment with expert opinion. To evaluate the stability of the causal relationships obtained using the DEMATEL-CI model, a sensitivity analysis was conducted concerning the weights assigned by the experts. First of all, specialists were given a baseline weight vector of \({\left\{\text{0.2,0.2,0.3,0.3}\right\}}^{T}\). To assess stability, the model was reassessed with different weight distributions \({\left\{\text{0.25,0.2,0.3,0.25}\right\}}^{T}\), and \({\left\{\text{0.3,0.3,0.2,0.2}\right\}}^{T}\). Overall, critical cause factor classifications were consistent across all scenarios, where \({\Pi }_{6}\), \({\Pi }_{1}\), and \({\Pi }_{4}\) continue to be classified as dominant cause factors. However, the positional changes between the factors of the effect group \({\Pi }_{5}\), \({\Pi }_{3}\), and \({\Pi }_{2}\) were minor. The entire cause-and-effect structure proved to be consistent, which again testifies to the robustness of the method in the face of variations in expert weighting. Moreover, to demonstrate the methodological superiority, the proposed framework was compared with two standard MCDM methods: the IF DEMATEL approach and the Fuzzy Best–Worst DEMATEL method. The comparative analysis indicated that our proposed model produced a more detailed set of interdependencies, better prioritization, and improved correspondence with expert judgment, and thus was superior to traditional methods in terms of interpretability and support for DM. Last but not least, the ranking outcomes of our model were close to those of expert consensus, which demonstrated additional verification of its validity and practical relevance. All these validation steps indicate that the proposed hybrid methodology is robust, sound, and practically applicable to modeling the complex DM problem in software development, specifically in IP-BDA.
Discussion
The results obtained in this paper reinforce the suitability of using BCFSs for the DEMATEL and CI-based framework in the realm of complex and uncertain DM. The suggested methodology enables the model to capture the magnitude and polarity of expert opinion in a nuanced manner, serving as a partial means of establishing the causal interrelationships among criteria in the software development setting, which involves IP-BDA. Application results demonstrated Feature extraction, automation and efficiency, and object detection/recognition to be not only core technical issues of interest but also strategic handles to overall performance improvement of a system. AA-TNs in BCFSs enabled the robust aggregation of criteria under ambiguity, and the CI enabled the interaction between criteria, which is omitted in additive models. The comparison with other MCDM methods also confirmed the superior interpretability and realism of the suggested method. This discussion demonstrates how sophisticated fuzzy modeling methods, particularly in the BCFS approach, can be utilized to make more informed and practical decisions, especially when the criteria involved exhibit interdependencies and coincidences in two-valued uncertainty.
The prioritization and the classification of criteria as cause and effect groups were instrumental in making informed strategic decisions in developing software enabled by IP-BDA in the proposed case study. It was found that feature extraction \({\Pi }_{1}\), improved automation and efficiency \({\Pi }_{4}\) and object detection/recognition \({\Pi }_{6}\) were the key cause factors, i.e. they have a strong influence on other criteria. Their high scores indicated that these factors are enablers at the bottom of the development pipeline, implying that investing in and optimizing these factors would yield a system-wide improvement. On the other hand, image improvement \({\Pi }_{2}\), security and fraud identification \({\Pi }_{3,}\) as well as segmentation \({\Pi }_{5}\) were found to be effect factors, that is, depending on the performance of the cause group. This categorization assisted developers and experts in realizing that quality results in more application-driven modules \(\left({\Pi }_{2},{\Pi }_{3},{\Pi }_{5}\right)\) are only achievable with enhancements in the fundamental technical processes \(\left({\Pi }_{1},{\Pi }_{4},{\Pi }_{6}\right)\). In this way, the suggested ranking not only eased the prioritization of developmental work but also allowed distributing the resources more sensibly, targeting the most impactful parts of the system, resulting in stronger, more efficient, and scalable software solutions.
Practical implications
The suggested methodology can have the following practical benefits to the participants of software development:
-
The model assists developers and project managers in focusing on features and functionalities that create the most significant upstream impact on system architecture and performance.
-
The framework provides a clear explanation of why resources are allocated transparently, allowing experts to give structured input and map the causes, which is essential in high-budget or high-stakes software development.
-
With the extension of CI, it is possible to consider interaction effects between criteria, thereby designing systems more coherently and adaptively in settings with multifaceted dependencies, such as IP pipelines and big data frameworks.
-
The methodology is not restrictive and could be applied to other high-dimensional, complex areas, including cybersecurity, healthcare systems, or intelligent transport systems.
Limitations
Although the suggested methodology provides a comprehensive and nuanced DM process in software development, it is not immune to flaws. The first issue is its reliance on expert opinion, which, despite the use of structured weighting and normalization procedures, can still introduce subjectivity and potential bias into the analysis. Due to the relatively small group of domain experts involved in the evaluation, the results may be limited in their generalizability to broader software development contexts. Second, the application of sophisticated fuzzy mathematical machinery, such as BCFSs and the CI, involves greater computational complexity, which can be a practical limitation in real-time or resource-constrained settings. The verification of the model was primarily based on expert judgment and comparative evaluation with other MCDM methods, rather than empirical data or live system performance measures, thus constraining its scope of empirical generalizability. Furthermore, the case study was explicitly focused on the field of IP-BDA in software development. Although the framework is theoretically adaptable, its application to completely different domains may require additional customization and validation.
Conclusion
This paper proposes and validates two new AOs: BCFCIAAA and BCFCIAAOA in the context of the BCFS using AA-TNs. These operators are mathematically demonstrated to meet essential properties, including idempotency, monotonicity, and boundedness, which enhances their credibility in uncertain, bipolar-valued DM situations. We integrated these AOs into a hybrid DM approach by combining the DEMATEL technique with the CI, enabling the model to efficiently handle interdependent criteria and imprecision in expert judgments. Using this integrated model to develop a case study of software development, specifically in the areas of IP-BDA integration, has demonstrated its pragmatic value. The outcomes determined that object detection/recognition \({\Pi }_{6}\), feature extraction \({\Pi }_{1}\), and improved automation and efficiency \({\Pi }_{4}\) are causal factors that have direct effects on performance and innovation in software systems. Image enhancement \({\Pi }_{2}\), security and fraud detection \({\Pi }_{3}\), and segmentation \({\Pi }_{5}\) were identified as effect factors that the causal group influenced. The outcomes of the proposed methodology were verified through sensitivity analysis and comparative performance tests, demonstrating its stability, adherence to expert judgment, and superiority over conventional fuzzy DM models. In general, this research not only advances theoretical developments in fuzzy aggregation and modeling but also provides an evidence-based, practical approach to prioritizing key technological variables in high-dimensional complex contexts, such as software engineering.
The proposed methodology not only pushes the theoretical limits in DM but also provides a structured and explainable approach toward modeling complex interdependencies in high-dimensional settings, which are particularly relevant in software development. Future research will focus on real-life applications, as well as daily tests in agile software development environments. Based on recent developments, such as the application of UAV selection in precision agriculture using interval-valued q-rung orthopair fuzzy information and Einstein AOs54, we will consider introducing the same type of interval-valued and hypersoft set structures into our approach to handle higher-order uncertainties in software selection more adequately. Additionally, based on the group DM method applied to cloud storage selection in interval-valued probabilistic linguistic T-spherical fuzzy environments55, further research will enhance the model with mechanisms for linguistic uncertainty and group consensus. Finally, we also wish to generalize interaction AOs, as was done in the study of the cryptocurrency market using q-rung orthopair fuzzy hypersoft sets56, to model the interactivity of attributes and dynamic relations in complex data ecosystems, such as software analytics, to a greater degree. These improvements will result in increased flexibility and real-time decision support for the framework in areas such as intelligent systems engineering and the design of adaptive software architecture.
Data availability
The datasets used and/or analyzed during the current study are available from the corresponding author upon reasonable request.
References
Zadeh, L. A. Fuzzy sets. Inf. Control. 8, 338–353. https://doi.org/10.1016/S0019-9958(65)90241-X (1965).
Atanassov, K. T. Intuitionistic fuzzy sets. Fuzzy Set. Syst. 20, 87–96. https://doi.org/10.1016/S0165-0114(86)80034-3 (1986).
Atanassov, K. & Gargov, G. Interval valued intuitionistic fuzzy sets. Fuzzy Set. Syst. 31, 343–349. https://doi.org/10.1016/0165-0114(89)90205-4 (1989).
Zhang, W.-R. Bipolar fuzzy sets and relations: A computational framework for cognitive modeling and multiagent decision analysis. In Proc. NAFIPS/IFIS/NASA’94. Proceedings of the First International Joint Conference of The North American Fuzzy Information Processing Society Biannual Conference. The Industrial Fuzzy Control and Intellige. 305–309 (IEEE 1994).
Akram, M., Shumaiza, & Al-Kenani, A. N. Multi-criteria group decision-making for selection of green suppliers under bipolar fuzzy PROMETHEE process. Symmetry 12, 77 (2020).
Akram, M., Shumaiza, & Arshad, M. Bipolar fuzzy TOPSIS and bipolar fuzzy ELECTRE-I methods to diagnosis. Comp. Appl. Math. 39, 7. https://doi.org/10.1007/s40314-019-0980-8 (2020).
Akram, M., Shumaiza, Rodríguez Alcantud, J.C. Multi-criteria decision making methods with bipolar fuzzy sets; forum for interdisciplinary mathematics Springer Nature Singapore 978–981–99–0568–3 (Singapore, ISBN, 2023).
Ramot, D., Milo, R., Friedman, M. & Kandel, A. Complex fuzzy sets. Fuzzy Syst. IEEE Trans. 10, 171–186. https://doi.org/10.1109/91.995119 (2002).
Alkouri, A., Moh’d, J. S. & Salleh, A. R. Complex Intuitionistic fuzzy sets. AIP Conf. Proc. 1482, 464–470. https://doi.org/10.1063/1.4757515 (2012).
Mahmood, T. & Rehman, U. A novel approach towards bipolar complex fuzzy sets and their applications in generalized similarity measures. Int. J. Intell. Syst. 37, 535–567. https://doi.org/10.1002/int.22639 (2022).
Menger, K. Statistical metrics. Proc. Natl. Acad. Sci. U.S.A. 28, 535 (1942).
Aczél, J. & Alsina, C. Characterizations of some classes of quasilinear functions with applications to triangular norms and to synthesizing judgements. Aeq. Math. 25, 313–315. https://doi.org/10.1007/BF02189626 (1982).
Wang, W. & Liu, X. Intuitionistic fuzzy information aggregation using einstein operations. IEEE Trans. Fuzzy Syst. 20, 923–938 (2012).
Hussain, A., Liu, Y., Ullah, K., Rashid, M., Senapati, T., Moslem, S. Decision algorithm for picture fuzzy sets and aczel alsina aggregation operators based on unknown degree of wights. Heliyon 10 (2024).
Mahmood, T., ur Rehman, U. & Ali, Z. Analysis and application of Aczel-Alsina aggregation operators based on bipolar complex fuzzy information in multiple attribute decision making. Inf. Sci. 619, 817–833 (2023).
Zulqarnain, R. M., Siddique, I., Iampan, A. & Baleanu, D. Aggregation operators for interval-valued pythagorean fuzzy soft set with their application to solve multi-attribute group decision making problem. Comput. Model. Eng. Sci. 2, 1–34 (2022).
Zulqarnain, R. M. et al. Some fundamental operations on interval valued neutrosophic hypersoft set with their properties. Neutrosophic. Set. Syst. 40, 8 (2021).
Samad, A. et al. Selection of an effective hand sanitizer to reduce COVID-19 effects and extension of TOPSIS technique based on correlation coefficient under neutrosophic hypersoft set. Complexity 2021, 5531830. https://doi.org/10.1155/2021/5531830 (2021).
Gurmani, S. H., Zhang, Z., Zulqarnain, R. M. & Askar, S. An interaction and feedback mechanism-based group decision-making for emergency medical supplies supplier selection using T-spherical fuzzy information. Sci. Rep. 13, 8726 (2023).
Siddique, I., Zulqarnain, R. M., Ali, R., Jarad, F. & Iampan, A. Multicriteria decision-making approach for aggregation operators of pythagorean fuzzy hypersoft sets. Comput. Intell. Neurosci. 2021, 2036506. https://doi.org/10.1155/2021/2036506 (2021).
Zulqarnain, R. M., Garg, H., Ma, W.-X. & Siddique, I. Optimal cloud service provider selection: An MADM framework on correlation-based TOPSIS with interval-valued q-Rung orthopair fuzzy soft set. Eng. Appl. Artif. Intell. 129, 107578. https://doi.org/10.1016/j.engappai.2023.107578 (2024).
Zulqarnain, R. M. et al. Neutrosophic hypersoft matrices with application to solve multiattributive decision-making problems. Complexity 2021, 5589874. https://doi.org/10.1155/2021/5589874 (2021).
Zulqarnain, R. M. et al. Extension of einstein average aggregation operators to medical diagnostic approach under Q-Rung orthopair fuzzy soft set. IEEE Access 10, 87923–87949. https://doi.org/10.1109/ACCESS.2022.3199069 (2022).
Zulqarnain, R. M. et al. Algorithms for a generalized multipolar neutrosophic soft set with information measures to solve medical diagnoses and decision-making problems. J. Math. 2021, 1–30. https://doi.org/10.1155/2021/6654657 (2021).
Zulqarnain, R. M. et al. Novel multicriteria decision making approach for interactive aggregation operators of Q-Rung orthopair fuzzy soft set. IEEE Access 10, 59640–59660. https://doi.org/10.1109/ACCESS.2022.3178595 (2022).
Choquet, G. Theory of capacities. Proc. Ann. de l’institut Fourier 5, 131–295 (1954).
Murofushi, T., Sugeno, M. & Machida, M. Non-monotonic fuzzy measures and the choquet integral. Fuzzy Set. Syst. 64, 73–86 (1994).
Wang, Z., Yan, J. Choquet Integral and Its Applications: A Survey. Acad. Math. Syst. Sci. (2006).
Tan, C. & Chen, X. Intuitionistic fuzzy choquet integral operator for multi-criteria decision making. Expert. Syst. Appl. 37, 149–157 (2010).
Wang, P., Shen, J. & Zhang, B. A new method for two-sided matching decision making of PPP projects based on intuitionistic fuzzy choquet integral. J. Intell. Fuzzy syst. 31, 2221–2230 (2016).
Büyüközkan, G. & Göçer, F. Smart medical device selection based on intuitionistic fuzzy choquet integral. Soft. Comput. 23, 10085–10103 (2019).
Jia, X. & Wang, Y. Choquet integral-based intuitionistic fuzzy arithmetic aggregation operators in multi-criteria decision-making. Expert Syst. Appl. 191, 116242. https://doi.org/10.1016/j.eswa.2021.116242 (2022).
Sha, L., Shao, Y. Fermatean hestitant fuzzy choquet integral aggregation operators. IEEE Access (2023).
Wu, H.-H. & Tsai, Y.-N. A DEMATEL method to evaluate the causal relations among the criteria in auto spare parts industry. Appl. Math. Comput. 218, 2334–2342 (2011).
Wu, W.-W. & Lee, Y.-T. Developing global managers’ competencies using the fuzzy DEMATEL method. Expert Syst. Appl. 32, 499–507 (2007).
Seker, S. & Zavadskas, E. K. Application of fuzzy DEMATEL method for analyzing occupational risks on construction sites. Sustainability 9, 2083 (2017).
Govindan, K., Khodaverdi, R. & Vafadarnikjoo, A. Intuitionistic fuzzy based DEMATEL method for developing green practices and performances in a green supply chain. Expert Syst. Appl. 42, 7207–7220 (2015).
Govindan, K. & Chaudhuri, A. Interrelationships of risks faced by third party logistics service providers: A DEMATEL based approach. Transp. Res. Part E: Logist. Transp. Rev. 90, 177–195 (2016).
Gonzalez, R.C. Digital image processing. Pearson education (India, 2009).
Szeliski, R. Image processing. In Computer Vision, Texts in Computer Science, 87–180 ISBN 978–1–84882–934–3 (Springer, London, 2011).
Brown, B., Chui, M. & Manyika, J. Are you ready for the era of ‘big data’. McKinsey Q. 4, 24–35 (2011).
Hashem, I. A. T. et al. The rise of “big data” on cloud computing: Review and open research issues. Inf. Syst. 47, 98–115 (2015).
Ristevski, B. & Chen, M. Big data analytics in medicine and healthcare. J. Integr. Bioinform. 15, 20170030. https://doi.org/10.1515/jib-2017-0030 (2018).
Lee, J., Kao, H.-A. & Yang, S. Service innovation and smart analytics for industry 4.0 and big data environment. Proced. cirp 16, 3–8 (2014).
Maini, R., Aggarwal, H. A. Comprehensive review of image enhancement techniques (2010).
Jia, W., Sun, M., Lian, J. & Hou, S. Feature dimensionality reduction: A review. Complex Intell. Syst. 8, 2663–2693. https://doi.org/10.1007/s40747-021-00637-x (2022).
Aruna Kumar, S. V. & Harish, B. S. A. Modified intuitionistic fuzzy clustering algorithm for medical image segmentation. J. Intell. Syst. 27, 593–607. https://doi.org/10.1515/jisys-2016-0241 (2018).
Xiao, Y. et al. A review of object detection based on deep learning. Multimed. Tool. Appl. 79, 23729–23791. https://doi.org/10.1007/s11042-020-08976-6 (2020).
Himeur, Y. et al. AI-big data analytics for building automation and management systems: A survey, actual challenges and future perspectives. Artif. Intell. Rev. 56, 4929–5021. https://doi.org/10.1007/s10462-022-10286-2 (2023).
Marriott, N. Using computerized business simulations and spreadsheet models in accounting education: A case study. Account. Educ. 13, 55–70. https://doi.org/10.1080/0963928042000310797 (2004).
Liang, T.-P., Lai, H.-J. & Ku, Y.-C. Personalized content recommendation and user satisfaction: Theoretical synthesis and empirical findings. J. Manag. Inf. Syst. 23, 45–70. https://doi.org/10.2753/MIS0742-1222230303 (2006).
Abdullah, L., Mohd Pouzi, H. & Awang, N. A. Intuitionistic fuzzy DEMATEL for developing causal relationship of water security. IJICC 16, 520–544. https://doi.org/10.1108/IJICC-11-2022-0296 (2023).
Govindan, K., Nasr, A. K., Karimi, F. & Mina, H. Circular economy adoption barriers: An extended fuzzy best-worst method using fuzzy DEMATEL and supermatrix structure. Bus. Strat. Env. 31, 1566–1586. https://doi.org/10.1002/bse.2970 (2022).
Gurmani, S. H., Garg, H., Zulqarnain, R. M. & Siddique, I. Selection of unmanned aerial vehicles for precision agriculture using interval-valued q-Rung orthopair fuzzy information based TOPSIS method. Int. J. Fuzzy Syst. 25, 2939–2953. https://doi.org/10.1007/s40815-023-01568-0 (2023).
Gurmani, S. H., Zhang, Z. & Zulqarnain, R. M. An integrated group decision-making technique under interval-valued probabilistic linguistic T-Spherical fuzzy information and its application to the selection of cloud storage provider. Aim. Math. 8, 20223–20253 (2023).
Zulqarnain, R. M., Siddique, I., Eldin, S. M. & Gurmani, S. H. Extension of interaction aggregation operators for the analysis of cryptocurrency market under Q-Rung orthopair fuzzy hypersoft set. IEEE Access 10, 126627–126650 (2022).
Author information
Authors and Affiliations
Contributions
Ruimin Ma contributed fully.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Supplementary Information
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Ma, R. Prioritizing image processing and big data analytics factors for software development using DEMATEL-choquet method in bipolar complex fuzzy context. Sci Rep 15, 30347 (2025). https://doi.org/10.1038/s41598-025-13536-9
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1038/s41598-025-13536-9