Abstract
This paper introduces an enhancement to the Chen chaotic system by incorporating a constant perturbation term \(d\) to one of the state variables, aiming to improve the performance of pseudo-random number generators (PRNGs). The perturbation significantly enhances the system's chaotic properties, resulting in superior randomness and increased security. An FPGA-based realization of a perturbed Chen oscillator (PCO)-derived PRNG is presented, tailored for embedded cryptosystems and implemented on a Nexys 4 FPGA card featuring the XILINX Artix-7 XC7A100T-1CSG324C integrated chip. The Xilinx-based system generator (XSG) tool is utilized to generate a digital version of the new oscillator, minimizing resource utilization. Experimental results demonstrate that the PCO-generated data successfully passes the NIST and TestU01 test suites. Additionally, statistical tests with key sensitivity are performed, validating the suitability of the designed PRNG for cryptographic applications. This establishes the PCO as a straightforward and efficient tool for multimedia security.
Similar content being viewed by others
Introduction
The exploration of deterministic chaos in dissipative systems has marked a significant milestone in scientific inquiry since E. N. Lorenz's pioneering demonstration in 19631. Chaos is prevalent in nature and has been observed across various scientific disciplines, including forced pendulums2, nonlinear optical devices3, classical many-body systems (such as the three-body problem) and particle accelerators4, chemical reactions5, fluids near turbulence onset6, and biological models for population dynamics7. Notably, recent advancements in modeling physical systems have yielded remarkable results, exemplified by systems like Sprott8, Chen-Lu9, Chua10, Lorenz11, Roosler12, Van der Pol, Duffing13, Genesio14, and others.
The Chen system, in particular, has been extensively studied in engineering and RNG applications. Han Ping et al. developed an algorithm15 for generating binary sequences and normalizing data distribution produced by the Chen oscillator (CO). Ozturk I and Kinc R16 proposed a novel method for generating pseudo-random numbers from Lü-like chaotic systems capable of exhibiting both Lorenz-like and Chen-like chaotic behaviors. Their FPGA experiment based on this method was effective and passed all NIST SP 800-22 statistical randomness tests.
Recent developments include: (i) Hamza R17 proposed an algorithm for generating PRNG based on CCO samples, particularly for cryptographic keys in digital images. Statistical tests, such as the Diehard battery test and NIST TEST version SP 800-22 rev1.a, confirm the good statistical properties of sequences generated by the proposed scheme. (ii) Gupta M D and Chauhan RK18 conducted an FPGA experiment for a PRNG using the CCO system. The generated sequences successfully passed all 15 statistical tests of NIST, demonstrating the generation of pseudo-random numbers at a uniform clock rate with minimal hardware complexity. Consequently, the Chen chaotic attractor emerges as a simple yet promising candidate with potential applications in cryptosystems.
Over the past decade, the research community has shown considerable interest in exploring fundamental pseudo-random number generators (PRNGs) rooted in simple yet captivating chaotic systems. Various applications, including the implementation of cryptosystems in network communication19, derive significant benefits from PRNGs. With growing concerns about security threats20, the statistical quality of PRNGs has become more crucial than ever.
However, despite the wealth of contributions in reputable journals mentioned earlier, there is still a gap in the literature regarding the study of an oscillator considering its real-life behavior concerning voltage perturbation and its digital implementation on an FPGA. It's noteworthy that FPGAs serve as a primary tool for implementing high-performance systems, particularly in applications like image processing and digital signal processing. Furthermore, FPGAs excel in executing signal processing tasks with high efficiency. XSG extends FPGA capabilities and provides essential tools for developing image encryption models21. In this context, we propose a new Chen oscillator that accounts for the real-world behavior of the oscillator when subjected to disturbed voltages in practical scenarios. The main contributions of this paper could be summarized in the following points:
-
The presentation of the renowned Chen oscillator within a real-world environment, showcasing its intriguing dynamics under external disturbances.
-
The successful FPGA-embedded experiment of the oscillator, reproducing these dynamic behaviors with minimal resource utilization.
-
The generation of pseudo-random numbers (PRNs) from the embedded oscillator, which pass the NIST SP800-22 test and TestU01 test.
-
Despite the challenges involved in constructing and evaluating random number generators (RNGs), we have accomplished the generation of PRNs from the perturbed Chen oscillator, paving the way for applications in embedded systems for cryptography.
The rest of this paper is structured as follows: Sect. "The perturbed CHEN chaotic oscillator (PCO)" outlines the development of the Perturbed Chen oscillator. Section "Dynamical analysis: effect of external term on the oscillator" examines basic properties derived from the mathematical model of the oscillator. The implementation of the system in an FPGA hardware device using the XSG method is explicated in Sect. "PCO in FPGA". Section "PRNG and encryption scheme" delves into PRN generation and an encryption scheme, providing presentation and discussion. Section "Results and discussion" presents and discusses the results, and finally, Sect. "Conclusion" offers a summary of the work presented in this paper.
The perturbed CHEN chaotic oscillator (PCO)
Chaotic systems, such as the Chen system, are widely employed in the design of PRNGs due to their inherent unpredictability and sensitivity to initial conditions. The Chen oscillator was introduced by Chen and Ueta in the literature22. Chaotic behavior is observed by configuring the oscillator parameters as follows: a = 35, b = 3, and c = 28, with the initial condition set at (0, 0, 0).
This paper introduces a perturbation term to simulate the real-world behavior of the oscillator in engineering systems. As shown in Fig. 1, which depicts a circuit diagram with an external constant voltage for op-amp 3, this perturbation term can represent an offset voltage produced by op-amp 3 in an analog implementation. For a digital implementation, this term accounts for variations in the coefficients from the mathematical model and the reduced accuracy of the numerical method used to discretize Eq. (1). Acknowledging the imperfect environment in which the numerically controlled oscillator (NCO) operates, this paper incorporates a perturbed oscillator by adding an extra voltage bias term that models an externally applied excited voltage and evaluates its impact on the system's dynamics.
Circuit diagram of the perturbed Chen oscillator with constant external voltage.
We can see that Vd acts as a perturbated signal to the electronic behavior of the entire oscillator.
By using the KVL23, the PCO oscillator can be described by the following set of 3-D differential equations.
As Vd = 0, the original Chen oscillator is obtained. In the set of Eq. (2), Vx, Vy and Vz stand for the voltages across capacitors Cx, Cy and Cz respectively. \(\dot{x} = \frac{{dV_{x} }}{d\tau };\dot{y} = \frac{{dV_{y} }}{d\tau };\dot{z} = \frac{{dV_{z} }}{d\tau };\tau = \frac{t}{RC}\) By choosing Cx = Cy = Cz = C and by setting the following dimensionless variable as follows, a = R/Ra, b = R/Rb, c = R/Rc, d = R/Rd,Vd = Vref = 1V, the previous equations are written as follows.
Mathematical equations
The mathematical equations of the PCO are defined as follows:
where a, b, c and d are the previous defined parameters and Eq. (3) shows that the PCO bridges the gap between the original one and takes into consideration some real external force and perturbations. We will see that the extra term induced new dynamics and can be seen as unknown behavior unobserved by the literature24.
Dissipation and symmetry analyses
The divergence \(\nabla\) of the vector field helps us classify the system in two groups. The first group concerns when the divergence is negative, the trajectories of the vector field are confined and evolved in a limited volume. In the second group, the divergence equals to zero, the system is conservative. Hence:
The later equation demonstrates that \(\nabla < 0\) and all the trajectories are asymptotically convergent to a specific subset of volume zero. The PCO is not symmetric meanwhile the original one is symmetric. The perturbed term, when equal to zero induces symmetric long-term behaviors.
Equilibrium points: EP
The overall behavior of the oscillator, as described by Eq. (3), is established through a local examination within the vicinity of the equilibrium point, following the recommendation in Ref.25. Accordingly, we set all the derivatives to zero. Let \(X_{0} \left( {x_{0} \,\,,\,\,y_{0} \,\,,\,\,z_{0} } \right) \in {\mathbb{R}}\) the EP \(\left( {\dot{x}_{0} ;\,\,\dot{y}_{0} ;\,\,\dot{z}_{0} } \right) = \left( {0;\,\,0;\,\,0} \right).\)
As we can see the system (3) has tree equilibrium points EP,
The perturbation of the system around the EP is set by the Jacobian matrix MJ as follows:
And the following characteristic equation are deduced as:\(\det \left( {MJ - \lambda I_{3} } \right) = 0\); where λ is the eigenvalue, hence:
By using the Routh-Hurwitz criteria, we plot the sign of the real part of λ in the (c, d) space to discover the values for which the EP are stable or unstable.
The stability nature of the EP, Po changes from S to U for c in the interval4,5. The stable area of the EP is greater than the one for instability. The parameter d does not influence the behavior of Po. In the other hand, P \(\pm\) is reversed behaviour from Po, that is stable region for P \(\pm\) is unstable for Po and vice versa. This description opens up the possibility of Pitchfork bifurcation of Po and P \(\pm\) (not demonstrated here for the simplicity of the paper) as shown in Fig. 2.
Stability diagram for the equilibrium point drawn by varying simultaneously the parameters \(c{\text{ and }}d\): (a) for EP \(P_{0}\), (b) for EP \(\,P_{ \pm }\). The red region corresponds to the unstable (U) area while the black one represents the stable zone (S).
Dynamical analysis: effect of external term on the oscillator
This section centers on the dynamic analysis of how the bias term influences the behavior of the oscillator. The system is resolved utilizing the RK4 algorithm26, employing a discrete time step of 0.005. Solely the steady-state data of the resolved system is documented, and several established plots are included to scrutinize the system's behavior. These plots encompass the 1-D bifurcation diagram, phase portrait, Lyapunov spectrum plot, and the largest Lyapunov exponent (LLE) plot. Utilizing these tools aids in illustrating the coexistence of attractor systems, multistability, and chaotic bubbles.
One-parameter bifurcation plots
In this subsection, we observe the oscillator's response to variations in the offset term. To achieve this, we generate a bifurcation diagram by recording the peaks of the state variable (xmax) after the system (3) has run for an extended duration. The control parameter undergoes both increments and decrements to facilitate hysteresis scanning. Consequently, two curves, represented by black and blue, are plotted.
Examining the diagram presented in Fig. 3 reveals a hysteresis phenomenon within the scanning parameter range of [− 60, − 20], where the black curve and the blue curve exhibit non-overlapping behavior. To provide a detailed representation of this phenomenon, a zoom into this interval is performed, resulting in the bifurcation diagram depicted in Fig. 4.
Bifurcation diagrams at the top (a) and the corresponding Lyapunov spectra at the bottom (b) showing route to chaos with respect to increasing and deceasing parameter d ranging between − 60 and 59.4 the other system parameters are \(a\, = \,35\,\,;\,\,b\, = \,3\,{\text{ et }}c\, = \,28\,\) the blue curve is plotted by drawing with positive starting point \(\left( {x_{0} \,;\,y_{0} \,;\,z_{0} } \right) = + \left( {1\,;\,1\,;\,1} \right)\) while the black is drawn by stating the curve with negative ones \(\left( {x_{0} \,;\,y_{0} \,;\,z_{0} } \right) = - \left( {1\,;\,1\,;\,1} \right)\).
(a) Zoom in the curves in Fig. 3 from − 60 to − 10 interval for the screening parameter d \(- 60\,\,\,{\text{to }} - {10}\) while \(a\, = \,35\,\,;\,\,b\, = \,3\,{\text{ et }}c\, = \,28\,\). (b) Zoom in the curves in Fig. 3(b).
The highlighted zone shows that some coexistence of attractors occur as follows:
-
a-
Coexistence of P-2 with P-1 attractors.
-
b-
Coexistence of chaotic attractors for d = − 25.
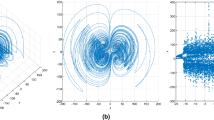
Figure 5 displays the phase portraits showing these multistability dynamics.
Phase portraits drawn for \(d = - 60\) focusing to the coexistence of different kind of attractors (period-3 and period-1) with the same system parameters \(a\, = \,35\,\,;\,\,b\, = \,3\,{\text{ et }}c\, = \,28\,\) just by changing starting points: \(\left( {x_{0} \,;\,y_{0} \,;\,z_{0} } \right) = \left( {1\,;\,1\,;\,1} \right)\,\) for blue curves and \(\left( {x_{0} \,;\,y_{0} \,;\,z_{0} } \right) = \left( { - 1\,;\, - 1\,;\, - 1} \right)\,\) for red ones.
In the light of the phase portraits drawn in the above Figs. 5 and 6, one can see that different steady state coexists for the additional parameter d, showing that in the real oscillator the dissymmetric parameter induces some interesting dynamics.
Phase portraits drawn for \(d = 5\).
Route to chaos
The bifurcation diagram shows p1 → p2 → p4 and so on to chaos. For the increasing parameter d, some period-3 limit cycles are sandwiched inside chaos zones. The deeper inside the behavior, some sample phased portraits are drawn by choosing the screening parameter showing these transitions in the plane \(\left( {y - z} \right)\). The rest of the system parameters are \(a\, = \,35\,\,;\,\,b\, = \,3\,{\text{ et }}c\, = \,28\,\) and the initial conditions are: \(\left( {x_{0} \,;\,y_{0} \,;\,z_{0} } \right) = \left( {1\,;\,1\,;\,1} \right)\,\) for the blue phased portrait and \(\left( {x_{0} \,;\,y_{0} \,;\,z_{0} } \right) = \left( { - 1\,;\, - 1\,;\, - 1} \right)\,\) for the red ones (see Figs. 5, 6 and 7).
Sample phase portraits (y–z) of the long-term running of the system illustrating period doubling dynamics when varying the d parameter and experimentally with the Nexys 4 board (a) \(d=-60\); (b) \(d=-45\); (c) \(d=-35\); (d) \(d=-28\); (e) \(d=-22\) and (f) \(d=-5\). The initial conditions are: \(\left({x}_{0};{y}_{0};{z}_{0}\right)=(1;1;1)\) (blue) and \(\left({x}_{0};{y}_{0};{z}_{0}\right)=(-1;-1;-1)\) (red) presenting the asymmetry of the modified Chen system on its route to chaos. Corresponding oscilloscope photos in green confirming the numerical results.
PCO in FPGA
Conducting FPGA experiments for electronic systems is remarkably straightforward, offering rapid prototyping, easy programming, and reconfigurability. The exploration of new chaotic systems in electronic experiments to validate analytical findings holds paramount significance and remains a challenging endeavor. This approach allows for flexible control parameter adjustments and precise initialization conditions, overcoming limitations faced by most analog realizations. Additionally, it incurs no cost when undergoing reconfigurations, thereby enhancing the prospects for realizing dynamical circuits27,28. Since the FPGA card processes data in digital form, it becomes essential to discretize the numerical form of system (3). We opt for the RK4 method, adjusting the time step to prevent computation errors26. The electronic experiment is depicted in Fig. 8 as follows:
Experimental setup of the new Chen oscillator embedded in the Artix 7 FPGA board with the Pmod DA2 converter.
The FPGA experiment of the system (3) is composed of an Artix-7 XC7A100T-1CSG324CFPGA card, which was previously designed in Vivado software (Xilinx Vivado Design Suite, Version 2021.2; URL Link: https://www.xilinx.com/developer/products/vivado.html). An analogue oscilloscope displays the chaotic attractor produced by the FPGA via the digital-to-analog converter PmodDA2.
The discrete transformation of the PCO
Regarding numerical algorithms for solving nonlinear differential equations, three primary methods exist, each characterized by distinct levels of accuracy and complexity: the Euler method, the RK4 algorithm, and the Midpoint algorithm29. Despite having a lengthier calculation path and requiring more resources, RK4 methods stand out as the superior choice for discretizing and approximating simultaneous nonlinear equations due to their minimal computational errors and high accuracy30. Despite their longer calculation path and increased resource usage, the RK4 methods outperform others in discretizing and approximating simultaneous nonlinear equations, providing superior accuracy with fewer computational errors30. Through the implementation of the RK4 method, the discrete version of the system is expressed as follows:
The primitive parameters k1, k2, k3, and k4 of Eqs. (9a), (9b), (9c) are calculated as follows:
where \(h\) is the discrete step size and has been set to the value \(h={2}^{-8}\) to minimise the hardware resources by replacing the multiplication by h with 8 right shifts. The next system state (xn+1, yn+1, zn+1) is then evaluated using the previous system state (xn, yn, zn). Now that the script to solve Eqs. (9a), (9b), (9c) form of the perturbed Chen oscillator is set, the next section focused on the environment software to implement the system.
Vivado environment
Xilinx's System Generator serves as a DSP design tool, enabling the utilization of the model-based Simulink design environment developed by MathWorks for FPGA design. No prior familiarity with Xilinx FPGAs or RTL design methods is necessary when using system generator. Xilinx designs are depicted in Simulink's DSP-friendly modeling environment through a distinct block set tailored for Xilinx. The process of generating an FPGA programming file, encompassing downstream procedures such as synthesis and place-and-route, is automated31. Each block in the XSG toolkit employed for creating system (3) is configured with a fixed-point representation in the 32Q20 format, and the latency is set to zero, facilitating the design of system (3).
Schematic diagram for the PCO
Figure 9 illustrates the schematic diagram of the PCO implementation. In this diagram, the register block labeled "REG" is utilized to store the initial values of the state variables (x 0, y0, z0), as well as the system state at the nth time step (xn, yn, zn) when the control unit (CU) generates an active "Rdy" signal. The MUX unit functions as a multiplexer, responsible for routing the data during the calculation of the parameters k1, k2, k3, and k4 for the primitives, based on the "cmd" signal generated by the CU. These primitive parameters are then computed using the PCO unit and stored in the Memory unit, which consists of four registers enabled by the "cmd" and "NRdy" signals, as depicted in Figs. 10a,b and 11. The computed values of the primitive parameters are subsequently utilized to calculate the next system state (xn + 1, yn + 1, zn + 1), which is stored in the "REG" block when the "Rdy" signal is active, following Eq. (6). To minimize the use of FPGA resources, all multiplication and division operations involving powers of 2 have been replaced by shifts.
Schematic diagram of the proposed Runge Kutta implementation of the PCO for one state variable.
XSG design of (a) the system control unit and (b) the memory unit.
XSG design of the perturbed Chen system.
The counter block of the CU ranges from 0 to \(N ={ 2}^{n-1}\), where n represents the number of bits. The maximum operating frequency (FOmax) is achieved when n equals 3 bits and N equals 4, resulting in a latency of five clock cycles. In order to display the phase portraits through the oscilloscope while reducing the operating frequency, we can increase the value of n. For this implementation, we have utilized n = 9 bits and N = 256.
Experimental setup
This subsection describes the deployment of the experimental setup using the Nexys 4 FPGA board and the PmodDA2 converter, as illustrated in Fig. 8. The VHDL script for the DAC Pmod controller can be referenced in Ref.32. The "Rdy" signal from the control unit is utilized to synchronize with the "dac_tx_ena" input of the DAC Pmod controller. Additionally, the "busy" signal is employed to enable the counter block in the control unit, ensuring that each state variable is fully converted before proceeding to the next one.
To accommodate the converter's representation format, the system's state variables are resized to 12 bits in 12Q9 fixed-point format. The selected variables are then transmitted to the "dac_data_a" and "dac_data_b" inputs of the Pmod controller. The controller's outputs are configured on the Pmod JB ports of the Nexys 4 board, which includes the XILINX Artix-7 XC7A100T-1CSG324C chip. Subsequently, the PmodDA2, is connected. This converter incorporates two channels of 12-bit Digital-to-Analog conversion powered by the Texas Instruments DAC121S10133, and is connected to the Pmod JB port of the FPGA board. The resulting signals are then visualized using an oscilloscope.
Figure 12 depicts the flow chart of our experimental setup, along with its circuit diagram. It is worth noting that the experimental results in Fig. 7 align perfectly with the numerical outcomes.
Schematic diagram of the experimental flow chart32.
PRNG and encryption scheme
RNG find applications in various domains like encryption, secure communication, authentication, game programming, and more. Chaotic systems are favored for RNGs due to their non-periodic nature, sensitivity to initial conditions and parameters, and the inability to predict long-term outcomes34. To produce our PRNG we set the initials values of perturbed Chen system at \(\left({x}_{0};{y}_{0};{z}_{0}\right)=(-1;-1;-1)\) with the perturbed term \(d=-5.\)
The architecture
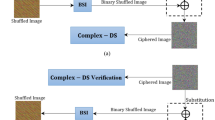
To generate random bits from chaotic signals, the full data-width is not fully utilized due to the presence of low self-oscillators. In this scheme, we truncate the 8 least significant bits (LSBs) from the original 32-bit chaotic signals and concatenate them to form a random number consisting of 24 bits, which is then employed for image encryption. Previous works, such as35 and34, have mentioned and implemented this truncation process. However, a clear justification for selecting the truncation position was not provided. The preference for using the LSBs lies in their higher fluctuation compared to the other bits36. The architecture obtained for this process is illustrated in Fig. 13. The down sample block is configured with a sample rate of 5 when the system is operating at its maximum frequency. The value of the sample rate should be set in accordance with the output latency of the state variables.
XSG design of PRNG.
Chaotic image encryption
The binary sequence generated earlier can serve as a pseudo-random number generator (PRNG) and be utilized to construct a secure communication system based on chaos for image encryption, as depicted in Fig. 14. In this study, we employed the peppers and Baboon images with respective dimensions of \(384x512\), and \(512x512\) to evaluate the performance of the PRNG within the image encryption scheme. The outcomes of this encryption process will be presented in the subsequent section.
Flowchart a chaotic secure communication diagram.
Results and discussion
This section begins by comparing our work with other FPGA implementations of the XSG KK algorithm for chaotic systems. Next, we provide an evaluation of the randomness performance of our pseudo-random number generator (PRNG) using the NIST and TestU01 tests. Finally, we present some statistical analysis of the encryption results, like the histogram analysis, the correlation coefficient analysis, the global Shannon entropy analysis, and the key sensitivity.
Implementation performances
Our implementation of the RK4 algorithm, as depicted in Table 1, strikes a balance between resource utilization, power consumption, and maximum operating frequency. Reference37 co-simulated the RK4 implementation of the new Chen system using active-HDL in Matlab/Simulink, utilizing 5615 Luts and 144 registers. In the study38, the resource utilization of Luts and flip-flops was reduced to 711 and 202, respectively, using a vhdl code to implement the fourth-order Runge–Kutta resolution of the hyperjerk. But the power consumption was not mentioned. Reference39 achieved resource utilization in Luts and flip-flops up to 2236 and 573, respectively, for the RK4 implementation of the Chen system. However, the maximum operating frequency (FOmax) was limited to 6.649 MHz, while requiring 200 DSPs. In Ref.36, the implementation showcased a reduction in Luts to 2017, achieving a maximum frequency of 113MHz with only 8 DSPs. However, it incurred the highest usage of flip-flops, with a value of 3458 and a power consumption of 73 mW. Meanwhile, in study40 the RK4 implementation of a Hopfield Neural Network oscillator (HNNO) was performed with 37,977 Luts and 47,195 FF.
Our design outperforms some others in terms of resource utilization, with 1527 Luts and 468 flip-flops while operating at a FOmax of 51 MHz. Additionally, it only requires 8 DSP multipliers and consumes 112 mW of power. By introducing delay blocks and adjusting the latency in the perturbed Chen system unit, we can further enhance the FOmax of our design. When setting the latency to 1, the FOmax can reach up to 75 MHz. However, this would result in more clock cycles needed to complete the state variable computation. As a result, our design strikes a balance between resource utilization, power consumption, and maximum operating frequency.
NIST statistical tests and TestU01
To ensure the suitability of the proposed pseudo-random number generator (PRNG) for cryptographic applications, it is essential to evaluate the randomness of the generated sequence. We used two statistical test suites for this purpose. Firstly, the 15 tests of the NIST (National Institute of Standards and Technology) statistical test suite, a widely employed tool commonly utilized for testing pseudo-random number generators41. Secondly, two tests of the TestU01 suite: Rabbit and Alphabit. These tests were designed for binary files. Rabbit and Alphabit apply 40 and 17 different statistical tests, respectively42.
For this research, the tested PRNG produced N = 100 sequences of 1 million bits each for three different values of perturbed term \({\varvec{d}}\), with initial values \(\left(-1\boldsymbol{ },-1,-1\right)\) and \(\left(1\boldsymbol{ },1,1\right),\) and control parameter values \(a=35\), \(b=3\) and \(c=28\). When \({\varvec{d}}=0\), the system is equivalent to the original Chen chaotic system. The value \({\varvec{d}}=1.61\) correspond to the highest amplitude value of the Lyapunov exponent spectra. We also generated a set of 100 sequences for the value \({\varvec{d}}=5\).
In this study, the NIST SP 800–22 standard software package (NIST Statistical Test Suite (STS) for Random and Pseudorandom Number Generators for Cryptographic Applications, Version 2.1.2; URL Link: https://csrc.nist.gov/projects/random-bit-generation/documentation-and-software) was used, employing the standard test parameters with the P_value α set to 0.01, with the TestU01 tests Rabbit and Alphabit. The proportion of successful sequences that passed the sub-tests is presented in Table 2. For the tests that provide multiple result values, we present the lowest one. In this table, the proportions corresponding to tests where the sequences have a perfect score are formatted in bold. Those corresponding to tests where the results indicated that the sequence did not meet the randomness criteria are followed by an asterisk (*). An overview of the table shows that all the sequences built with the initial condition \((\text{1,1},1)\) have an issue with the non-overlapping template NIST test. They did not meet the randomness criteria. Among the other sequences, the first one with initial conditions \((-1, -1, -1)\) and perturbed term value \(d=-5\) has the highest number of perfect scores. The value \(d=-5\), will be used to perform all the other statistical tests in this study.
Histogram analysis
The pixel distribution, which illustrates the number of pixels at various levels of color intensity, is visualized through the image histogram. Figures 15a,b, 16a and b present a comparison of the histogram results for both the encrypted and original images. The histograms of the encrypted images display a uniform distribution of pixel values for the red, green, and blue channels compared to the histograms of the original images. This makes it difficult for an attacker to deduce any information from the encrypted image about the original image.
Histogram of (a) original and (b) of encrypted peppers image for red, green and blue channel.
Histogram of (a) original and (b) of encrypted Baboon image for red, green and blue channel.
Correlation coefficient analysis
Correlation coefficient analysis compares neighboring pixels in plaintext and ciphered images. In the plaintext image, adjacent pixels correlate horizontally, vertically, and diagonally. In contrast, the ciphered image should have no association between pixels. A high correlation between pixels \((closed to+1 or -1)\) shows statistical attack susceptibility. Thus, good encryption reduces this coefficient \((closed to 0)\). Equation (11) can be used for correlation coefficient computation.
where \(C(x,y)\) is the covariance between the values of two adjacent pixel in the image x and y; \(D(x)\) and \(D(y)\) are the variance of x and y respectively, with:
where \(E(x)\) is the mean value of x and N is the number of observations or pairs of data points.
The correlation coefficient is calculated by randomly selecting 5000 pairs of adjacent pixels from the original and encrypted images. The correlation coefficient in horizontal, vertical, and diagonal orientations is estimated using Eq. (11) next. Figure 17 shows the selected adjacent pixels of the original Baboon image in horizontal, vertical, and diagonal orientations for the red, blue, and green color components. Figure 18 shows the horizontal, vertical, and diagonal distribution of selected adjacent pixels of the encrypted Baboon picture for the red, blue, and green color components. The results show that the original image has a linear pixel distribution, indicating a significant correlation between adjacent pixels. In contrast, the encrypted image has a random pixel distribution. Thus, the encrypted image has uncorrelated pixels, suggesting no significant association. Table 3 shows encrypted picture correlation coefficients near zero. Thus, predicting encrypted image pixel values is challenging. These results show that the proposed PRNG generated sequence for the image encryption scheme has good performance in fighting against attacks based on the correlation properties of the images.
Distribution of 5000 pairs of randomly selected (a) Horizontal adjacent pixels, (b) Vertical adjacent pixels, (c) Diagonal adjacent pixels for the original Baboon image with \(d=-5\) and initial values \((-1,-1,-1)\).
Distribution of 5000 pairs of randomly selected (a) Horizontal adjacent pixels, (b) Vertical adjacent pixels, (c) Diagonal adjacent pixels for the encrypted Baboon image with \(d=-5\) and initial values \((-1,-1,-1)\).
Global Shannon entropy analysis
An image's Shannon entropy measures its randomness by measuring its average information per bit. Entropy should be around 8 bits per pixel for an 8-bit encoded image for optimal encryption. Equation (13) calculates information entropy for an 8-bit image.
where \(H(S)\) is the Shannon entropy of the image, \(P(s_{i} )\) is the probability of occurrence of a pixel having a value \(s_{i} .\) The summation runs over all possible values \(s\) in the image source \(S.\)
Equation (13) quantifies image-wide Shannon entropy. Encrypted image global Shannon entropies are shown in Table 4. In conclusion, encrypted images have an average global entropy of 7.9992, close to 8. From those results, we infer that the encrypted image has no statistical information that may be exploited to obtain the original image. Table 5 shows that the suggested PRNG generate sequence for image encryption performs equally to recent studies proposed in the literature.
Many chaos-based encryption techniques are used in the literature to secure image transmission using embedded devices. In study43, a chaotic fractional order encryption scheme implemented in an FPGA was proposed. Likewise, the authors in Ref.38 designed a chaotic hyperjerk-based encryption scheme in integer order embedded in an FPGA. In studies44 and45, a chaos-based encryption embedded in a microcontroller was designed using a jerk system and a Modified Hénon Chaotic Map (MHCM), respectively. Moreover, a Raspberry Pi implementation of many chaotic systems, including the Chen system, was used to design an encryption scheme in the study46. In references47 and40, an image encryption algorithm based on a chaotic neural network was designed on an FPGA. Table 5 presents a comparative study of the global entropy for encrypted images between our work and those papers. We obtained an average global entropy value that was similar to the other study. Therefore, we can use the sequences generated with our PRNG for image encryption, as their statistical properties are comparable to those of other recent and diverse encryption schemes.
Key sensitivity
Cryptography requires a secret parameter to be sensitive enough to assure the "avalanche property": any little change in the parameter will modify the ciphertext. This ensures strong parameter mismatch sensitivity48.
Table 6 presents the keys used to achieve the key sensitivity tests. Key1 is the original key used in the above results. Keys 2–4 are used to verify initial condition sensitivity, and Keys 5–7 are used for control parameter sensitivity. Since we represent data with a fixed-point format of 32Q20, there is a difference of one bit with the slightest difference value between Key1 and all the other keys.
At the decryption phase, the decrypted image must be completely different from the original image when using the wrong key. Figure 19 presents the decrypted images with Keys 1–7 for an image encrypted using Key1. The results show that only the right key can decipher the encrypted image. As a consequence, we can attest to the key sensitivity of our design for both initial values and control parameters.
Decrypted Baboon image by (a) Key1, (b) Key2, (c) Key3, (d) Key4, (e) Key5, (f) Key6, (g) Key7.
All those results show that the introduction of a simple constant perturbation term d in the Chen system significantly enhances the chaotic properties of the system, resulting in superior randomness quality in the PRNG produced and increased security.
Conclusion
This paper has introduced a modified Chen system and demonstrated its application on an FPGA. The approach reduces device resource utilization by implementing the fourth-order RK4 numerical method to solve system differential equations using XSG, embedded in the Nexys 4 FPGA card. Experimental results validate the efficiency of this implementation, with the generated pseudo-random number generator (PRNG) successfully passing the NIST and TestU01 tests. Statistical analysis, including histogram, correlation coefficient, entropy, and key sensitivity, confirms the PRNG scheme's potential for integration into image cryptosystems, comparable to recent encryption schemes. This contribution highlights the PCO as a versatile and effective tool for enhancing multimedia security.
Future research should extend the application of the perturbed Chen system on an FPGA to real-world scenarios, exploring its practical utility in secure communication, image encryption, and signal processing. Optimization of the FPGA implementation is recommended to enhance computational efficiency and reduce resource utilization. A comprehensive security analysis of the implemented PRNG is essential, evaluating its robustness against differential and brute force attacks. Additionally, expanding the scope of multimedia security applications, considering integration with emerging technologies like machine learning or edge computing, is suggested. Evaluating the implementation on different FPGA platforms, exploring parallel processing techniques, and investigating alternative numerical methods for solving differential equations will enhance the system's versatility and performance across diverse hardware environments.
Data availability
The datasets generated and/or analyzed during the current study are not publicly available due to their involvement in an ongoing research project, as public release may compromise the integrity and novelty of subsequent analyses, but are available from the corresponding author on reasonable request.
References
Lorenz, E. N. A new approach to linear filtering and prediction problems. Determ. Nonperiod. Flow 20, 130–141 (1963).
Xu, X., Wiercigroch, M. & Cartmell, M. Rotating orbits of a parametrically-excited pendulum. Chaos Solitons Fractals 23(5), 1537–1548 (2005).
Lynch, S. & Steele, A. Controlling chaos in nonlinear optical resonators. Chaos Solitons Fractals 11(5), 721–728 (2000).
Schuster, H. G. & Just, W. Deterministic Chaos: An Introduction (Wiley, 2006).
Li, Q. S. & Zhu, R. Chaos to periodicity and periodicity to chaos by periodic perturbations in the Belousov-Zhabotinsky reaction. Chaos Solitons Fractals 19(1), 195–201 (2004).
Swinney, H. L. & Gollub, J. P. Hydrodynamic Instabilities and the Transition to Turbulence (Springer Berlin Heidelberg, 1981).
May, R. M. Simple Mathematical Models with Very Complicated Dynamics, in The Theory of Chaotic Attractors 85–93 (Springer, 2004).
Daszkiewicz, M. Noncommutative Sprott systems and their jerk dynamics. Mod. Phys. Lett. A 33(18), 1850100 (2018).
Selvam, A. G. M. & Vianny, D. A. Bifurcation and dynamical behaviour of a fractional order Lorenz-Chen-Lu like chaotic system with discretization. J. Phys. Conf. Ser. 1377, 012002 (2019).
Elwakil, A. S. & Kennedy, M. P. Improved implementation of Chua’s chaotic oscillator using current feedback op amp. IEEE Trans. Circuits Syst. I Fund. Theory Appl. 47(1), 76–79 (2000).
Pehlivan, I. & Uyaroğlu, Y. Simplified chaotic diffusionless Lorentz attractor and its application to secure communication systems. IET Commun. 1(5), 1015–1022 (2007).
Osipov, G. V. et al. Phase synchronization effects in a lattice of nonidentical Rössler oscillators. Phys. Rev. E 55(3), 2353 (1997).
Murali, K. & Lakshmanan, M. Transmission of signals by synchronization in a chaotic Van der Pol-Duffing oscillator. Phys. Rev. E 48(3), R1624 (1993).
Nguenjou, L. N. et al. A window of multistability in Genesio-Tesi chaotic system, synchronization and application for securing information. AEU-Int. J. Electron. Commun. 99, 201–214 (2019).
Hu, H., Liu, L. & Ding, N. Pseudorandom sequence generator based on the Chen chaotic system. Comput. Phys. Commun. 184(3), 765–768 (2013).
Öztürk, I. & Kılıç, R. A novel method for producing pseudo random numbers from differential equation-based chaotic systems. Nonlinear Dyn. 80(3), 1147–1157 (2015).
Hamza, R. A novel pseudo random sequence generator for image-cryptographic applications. J. Inf. Secur. Appl. 35, 119–127 (2017).
Gupta, M. D. & Chauhan, R. K. Hardware efficient pseudo-random number generator using chen chaotic system on FPGA. J. Circuits Syst. Comput. 31(03), 2250043 (2022).
Lei, W., Fu-Ping, W. & Zan-Ji, W. A novel chaos-based pseudo-random number generator. Acta Phys. Sin. 55(8), 3964–3968 (2006).
Ergün, S. A. S. Ö. Truly random number generators based on a non-autonomous chaotic oscillator. AEU-Int. J. Electron. Commun. 61(4), 235–242 (2007).
Al-Musawi, W. A., Wali, W. A. & Al-Ibadi, M. A. A. Field-programmable gate array design of image encryption and decryption using Chua’s chaotic masking. Int. J. Electr. Comput. Eng. (IJECE) 12(3), 2414 (2022).
Chen, G. & Ueta, T. Yet another chaotic attractor. Int. J. Bifurc. chaos 9(07), 1465–1466 (1999).
Malvino, A. P., Bates, D. J. & Hoppe, P. E. Electronic Principles (Glencoe, 1993).
Sprott, J. C. A proposed standard for the publication of new chaotic systems. Int. J. Bifurc. Chaos 21(09), 2391–2394 (2011).
Strogatz, S. H. Nonlinear Dynamics and Chaos: With Applications to Physics, Biology, Chemistry, and Engineering (C. press, 2018).
Press, W. H. et al. Numerical Recipes 3rd Edition: The Art of Scientific Computing (Cambridge University Press, 2007).
Soliman, N. S. et al. Fractional X-shape controllable multi-scroll attractor with parameter effect and FPGA automatic design tool software. Chaos Solitons Fractals 126, 292–307 (2019).
Ramakrishnan, B. et al. Image encryption with a Josephson junction model embedded in FPGA. Multimed. Tools Appl. 81, 1–25 (2022).
Press, W. H. et al. Numerical Recipes 3rd Edition: The Art of Scientific Computing (C.u. Press, 2007).
Koyuncu, I. The design and realization of a new high speed FPGA-based chaotic true random number generator. Comput. Electr. Eng. 58, 203–214 (2017).
xilinx, Vivado Design Suite Tutorial Model-Based DSP Design Using System Generator. UG948 (v2020.1) (2020).
Digikey and employee, DAC DAC121S101 Pmod Controller (VHDL). https://forum.digikey.com/t/dac-dac121s101-pmod-controller-vhdl/13031 (Accessed 4 March 2021).
Diligent, PmodDA2™ Reference Manual. https://digilent.com/reference/_media/reference/pmod/pmodda2/pmodda2_rm.pdf (Accessed 24 May 2016).
Kingni, S. T. et al. Dynamical analysis, FPGA implementation and its application to chaos based random number generator of a fractal Josephson junction with unharmonic current-phase relation. Eur. Phys. J. B https://doi.org/10.1140/epjb/e2020-100562-9 (2020).
Merah, L. et al. Design and FPGA implementation of Lorenz chaotic system for information security issues. Appl. Math. Sci. 7, 237–246 (2013).
Nguyen, N. T. et al. Designing a pseudo-random bit generator with a novel 5D-hyperchaotic system. IEEE Trans. Ind. Electron. 69(6), 6101–6110 (2022).
Adeyemi, V.-A. FPGA realization of the parameter-switching method in the Chen oscillator and application in image transmission. Symmetry 13(6), 923 (2021).
Sambas, A. et al. A new hyperjerk system with a half line equilibrium: Multistability, period doubling reversals, antimonotonocity, electronic circuit, FPGA design, and an application to image encryption. IEEE Access 12, 9177–9194 (2024).
Hasan, F. S. Speech encryption using fixed point chaos based stream cipher (FPC-SC). Eng. Technol. J. 34, 2152–2166 (2016).
Yu, F. et al. Design and FPGA implementation of a pseudo-random number generator based on a hopfield neural network under electromagnetic radiation. Front. Phys. 9, 690651 (2021).
Bassham III, L. E. et al. Sp 800-22 rev. 1a. A Statistical Test Suite for Random and Pseudorandom Number Generators for Cryptographic Applications (National Institute of Standards and Technology, 2010).
de la Fraga, L., Mancillas-López, C. & Tlelo-Cuautle, E. Designing an authenticated Hash function with a 2D chaotic map. Nonlinear Dyn. https://doi.org/10.1007/s11071-021-06491-3 (2021).
Adeyemi, V. et al. FPGA implementation of parameter-switching scheme to stabilize chaos in fractional spherical systems and usage in secure image transmission. Fractal Fract. 7, 440 (2023).
Ayemtsa Kuete, G. P. et al. Medical image crytosystem using a new 3-D map implemented in a microcontroller. Multimed. Tools Appl. https://doi.org/10.1007/s11042-024-18460-0 (2024).
Merah, L. et al. Real-time implementation of a chaos based cryptosystem on low-cost hardware. Iran. J. Sci. Technol. Trans. Electr. Eng. 45(4), 1127–1150 (2021).
Flores-Vergara, A. et al. Implementing a chaotic cryptosystem in a 64-bit embedded system by using multiple-precision arithmetic. Nonlinear Dyn. 96(1), 497–516 (2019).
Yao, W. et al. An image encryption algorithm based on a 3D chaotic Hopfield neural network and random row–column permutation. Front. Phys. https://doi.org/10.3389/fphy.2023.1162887 (2023).
Alvarez, G. & Li, S. Some basic cryptographic requirements for chaos-based cryptosystems. Int. J. Bifurc. Chaos 16, 2129–2151 (2006).
Author information
Authors and Affiliations
Contributions
Fritz NGUEMO KEMDOUM, Justin Roger MBOUPDA PONE, Gideon Pagnol AYEMTSA KUETE: Conceptualization, Methodology, Software, Visualization, Investigation, Writing- Original draft preparation. Serge Raoul DZONDE NAOUSSI, Mohamed LOUZAZNI, Salah KAMEL: Data curation, Validation, Supervision, Resources, Writing—Review & Editing. Mohit Bajaj, Milkias Berhanu: Project administration, Supervision, Resources, Writing—Review & Editing.
Corresponding authors
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher's note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Nguemo Kemdoum, F., Mboupda Pone, J.R., Bajaj, M. et al. FPGA based implementation of a perturbed Chen oscillator for secure embedded cryptosystems. Sci Rep 14, 21262 (2024). https://doi.org/10.1038/s41598-024-71531-y
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1038/s41598-024-71531-y