Abstract
Recently, UAV formations have been designed to support latency-sensitive tasks, such as situational awareness and emergency command, which require deterministic end-to-end data transmission. However, due to the dynamic networking of UAV formation, the traditional static TDMA method cannot meet the deterministic transmission requirements. Consequently, to satisfy the deterministic transmission of time-sensitive services, a hybrid CSMA/TDMA resource dynamic allocation scheme is proposed, which not only supports dynamic node access but also flexibly adapts to dynamic changes in services. Firstly, to tackle the issue of uncertain access delay caused by node collisions, a Random Backoff with Centralized Collision Avoidance (RB-CCA) algorithm is proposed; a Markov chain is proposed to model the entire state transition process, to analyze the collision probability and access success probability of existing and unconnected nodes. Secondly, we establish a minimum time-sensitive service delay model, and design a DySTMap Ivy Algorithm (DIvyA) to obtain the minimum delay and required slot length for nodes. The simulation results in Exata demonstrate that RB-CCA can reduce idle listening by 30% compared to existing random backoff algorithms; during the service transmission phase, the proposed scheme reduces end-to-end delay by 20% compared to existing slot allocation schemes. Finally, the proposed solution is implemented on an FPGA platform, and semi-physical scenario experimental results show that the end-to-end delay is below 5ms, with jitter less than 0.12ms.
Similar content being viewed by others
Introduction
With the advancement of Unmanned Aerial Vehicle (UAV) technology, emerging applications such as early warning surveillance, remote command and control, and wide-area coverage have raised higher demands on the real-time performance and determinism of data transmission. However, in UAV formation networks, to ensure the flexibility of node access, the Carrier Sense Multiple Access with Collision Avoidance (CSMA/CA) mechanism is typically used for channel contention. Due to the limitations of wireless channel resources, simultaneous resource competition among multiple UAVs can lead to collisions, resulting in network delays and congestion. Moreover, UAV formations always be deployed with Time Division Multiple Access (TDMA) with fixed resource allocation, which can lead to insufficient or wasted time slots for dynamic changes in service demands. These problems can cause end-to-end delays ranging from 50 to 500 ms, with jitter varying from tens to hundreds of milliseconds1. Therefore, adopting dynamic changes in UAV formation, reducing collisions and improving resource allocation efficiency are the key issue to guarantee deterministic communication in UAV formations.
Firstly, carrier sense multiple access (CSMA) extended protocols based on Distributed Coordination Function (DCF) were proposed to improve the flexibility of node access through adaptive channel listening and random back-off mechanisms2. The traditional binary exponential back-off (BEB) algorithm avoids collisions by exponentially increasing the contention window sizes of different nodes3,4,5. However, this approach leads to an increase in idle listening by nodes, making it impossible to determine the node access delay. Moreover, when the number of nodes in the network becomes large, packet collisions will be more severe, resulting in increased access delay and overhead for CSMA contention, as well as significantly reduced channel utilization. References6,7,8,9,10 have proposed a large number of methods to reduce packet collisions and access overhead. In reference6, after multiple consecutive successful transmissions, the station halves the size of its contention window. Furthermore, as mentioned in7, the size of the contention window is adjusted by the number of consecutive idle sensing events. However, these methods still result in a non-zero probability of data collisions. In reference8, the station announces its backoff count in the MAC header of the transmitted data frame, then all neighboring stations receive the backoff count and select their own backoff counts by excluding the same values. Nevertheless, due to the dynamic data rates among stations, some neighboring stations may fail to detect the backoff count in the data frame. References9,10 propose a semi-random backoff scheme, where a station employs the standard random backoff of DCF if it fails to contend for the channel. If successful, the station sets its backoff count to a deterministic value. However, the initial backoff window size limits the maximum number of stations successfully accessing the channel.Notably, the core mechanism of Wi-Fi DCF also includes the RTS/CTS handshake – before transmitting data, a node first sends a Request to Send (RTS) frame, and the target node replies with a Clear to Send (CTS) frame to reserve the channel, thereby reducing collisions caused by hidden terminals through distributed coordination11. However, in UAV formations, high mobility can lead to RTS/CTS handshake timeouts (e.g., due to rapid node movement causing CTS frames to be lost), and the handshake process itself introduces additional overhead, which may actually reduce efficiency in high-density node scenarios12.
Consequently, since time division multiple access (TDMA) based protocols can distinguish channels for different terminals using distinct time slots, which were introduced to minimize the probability of collisions and bounded delay13,14. Currently in US military, Joint Tactical Information Distribution System (JTIDS) was employed with a static TDMA approach15, where time slots are pre-allocated to participating nodes before communication. If a node has no data to transmit during its allocated slot or if the slot is insufficient for data transmission, communication delays may increase, channel utilization may decrease, and scalability may be limited. Reference16 proposes a TDMA-CA scheme based on a graph color algorithm, aiming to avoid conflicts in time slot allocation, but it cannot address the issue of retransmissions in case of transmission failures. Reference17 introduces a cooperative dynamic retransmission algorithm, where nodes use idle slots of neighboring nodes to retransmit data packets upon transmission failure. However, when network collisions occur, significant additional time is required to regenerate an optimized time slot allocation table.
Moreover, hybrid protocols have gained increasing attention from researchers in recent years18,19. These protocols combine CSMA and TDMA, leveraging the complementary advantages of both to effectively enhance network communication performance. Reference19 proposes an adaptive MAC adjustment mechanism that allows nodes to enter a conflict-free period without prior knowledge of load levels or the number of network nodes. In addition, OFDMA and uplink scheduling mechanisms in Wi-Fi offer new perspectives for collision avoidance. OFDMA divides the channel into multiple orthogonal subcarriers, allowing different nodes to transmit in parallel within the same time slot20. When combined with the proposed strategy, time slots in the TDMA phase can be further subdivided into frequency-domain resources, enhancing resource reuse. Moreover, trigger-based frame designs (such as UL MU-MIMO trigger frames in 802.11ax) enable centralized scheduling of uplink transmissions by the AP, reducing contention among nodes. However, the high mobility of UAV formations demands simplified trigger frame structures (e.g., shorter frame lengths to reduce transmission delay) and adaptations to rapid channel variations caused by fast node movement. These requirements align well with the centralized slot allocation approach proposed in this paper, though existing solutions have not been optimized specifically for UAV formation scenarios. However, most existing dynamic slot allocation protocols21 fail to address the issues of deterministic access for dynamic nodes, dynamic changes in service demands, and retransmissions caused by poor communication quality. These shortcomings ultimately hinder the guarantee of deterministic transmission for time-sensitive missions.
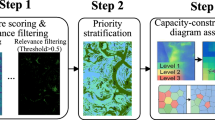
In this paper, to meet the demands of dynamic service changes, we propose a hybrid CSMA/TDMA resource dynamic allocation scheme to enhance resource utilization and access fairness. Moreover, we conduct experiments based on the Exata and FPGA platforms to verify the performance our proposed scheme. The main contributions are as follows.
-
1.
To address the issue of uncertain access delay caused by collisions among dynamic nodes, a Random Back-off with Centralized Collision Avoidance (RB-CCA) algorithm is proposed. Unconnected nodes compete for the channel through carrier sensing and send requests to the master node, which assigns a unique back-off state to the source node via an acknowledgment frame. We introduce a Markov chain to model the entire state transition process, then, the collision probability and access success probability for both existing and unconnected nodes in the network can be analyzed and derived. Based on the back-off states of the nodes, the communication window of the master node can be calculated. Finally, the relationship between the node access success probability and the average back-off delay is utilized to obtain the average access delay of the nodes.
-
2.
To meet the dynamics of UAV network in transmission phase, a delay-optimized dynamic time slot allocation scheme is designed. The scheme characterizes the length of each time slot in the superframe based on the traffic models of individual nodes and channel quality. Then, the end-to-end delay composition of time-sensitive data is analyzed, and a minimum end-to-end delay model for time-sensitive services is established. An improved Ivy algorithm is employed to solve the model, to obtain the minimum delay and the required time slot length for each node.This scheme is adaptable to potential OFDMA extensions by jointly allocating time slots and subcarrier resources, further improving parallel transmission efficiency. At the same time, it simplifies trigger frame design for broadcasting slot assignment instructions, thereby reducing collisions. By dynamically adjusting time slot resources, the deterministic end-to-end transmission of time-sensitive services is ensured.
-
3.
To validate the effectiveness of the proposed scheme, we construct experiments on Exata platform to compare the performance of the proposed algorithm. Subsequently, the proposed solution is implemented on an FPGA platform, and its feasibility for deterministic communication in UAV formations is verified through semi-physical experiments.
Problem statements
The primary consideration for deterministic transmission requirements in UAV formations is the inter-node distance within the formation. For general missions such as surveillance, photography, or patrol, a formation typically consists of several dozens of UAVs. To ensure coordination and safety within the formation, the distance between nodes is generally varied between 20 m and 100 m, with delays ranging from tens to hundreds of milliseconds and jitter within a few to tens of milliseconds22.
Reconnaissance UAV Formation Network.
As shown in Fig. 1, a scenario is depicted in which a reconnaissance UAV formation is executing a mission. The formation consists of two types of nodes: the leader and the wingmen. During the CSMA phase, the wingman nodes synchronize their clocks with the leader node and request access to the network. Once successfully connected, the wingman nodes transmit reconnaissance target data to the leader node using TDMA for scientific analysis. The leader node serves a dual purpose: on one hand, it acts as a control station to collect situational information from the wingman nodes and distribute decision-making commands; on the other hand, it responds to telemetry data from the wingman nodes. During the formation’s flight, if a wingman (e.g., Wingman 4 in the figure) needs to leave the formation due to low battery or being destroyed, a new UAV (e.g., Wingman 7 in the figure) must be assigned to join the network to ensure comprehensive target reconnaissance. However, the random access of Wingman 7 may collide with existing nodes in the network, leading to prolonged node access delays and network uncertainty. Additionally, if the number of reconnaissance targets for Wingman 3 changes dynamically, the static TDMA approach may allocate insufficient time slots, resulting in increased end-to-end delays for critical data. In addition, wireless channel instability (such as errors caused by occlusion or interference) can lead to data transmission failures. In such cases, the absence of a retransmission mechanism or an improperly designed one can further exacerbate delay jitter. Therefore, to ensure the deterministic transmission of time-sensitive data, the following key issues must be addressed.
(1) Coupling of Dynamic Node Access Delay and Retransmission Uncertainty In the formation, each wingman node is required to periodically report its status to the leader node, including whether the node is still in the network and its own traffic volume, among other information. Therefore, the CSMA phase can ensure the random access of new nodes to the network. But there exist two levels of uncertainty: (a) The randomness of access delay: Assuming the number of nodes in the network is \(N\), the channel state monitored by wingman node \(i\) at time \(t\) is denoted as \({X_i}(t)\), the backoff time is \({B_i}(t)\), and the probability of sending data is \({P_i}(t)\). Thus, the node access delay during the CSMA phase can be expressed as:
Among them, \({B_i}(t)\) is commonly calculated using algorithms such as exponential backoff or binary exponential backoff. Taking binary exponential backoff as an example, the node access delay can be expressed as,
Where, \({k_n}\) represents the expected number of collisions for successful network access; IFS denotes the inter-frame spacing specified by IEEE 802.11; and \({B_j}/{R_{sp}}\) indicates the time required for a node to transmit data of size \({B_j}\) at the rate \({R_{sp}}\) upon joining the network. However, although the CSMA-based access method can enhance network flexibility, the uncertainty of \({B_i}(t)\) during the collision backoff process leads to indeterminate node access delays in the network. This results in a mismatch between the generation time of time-sensitive data and subsequent TDMA time slots, thereby causing unstable data forwarding delays and lower throughput. (b) The cumulative impact of retransmissions on delay: Existing CSMA schemes do not account for retransmissions caused by channel errors (e.g., corrupted packets) during the access process23. If the initial access attempt fails, the node must re-contend for the channel, further increasing access delay. Moreover, the number of retransmissions is strongly correlated with channel quality (i.e., bit error rate), exacerbating the uncertainty in delay
(2) Static slot allocation cannot accommodate traffic dynamics and retransmission demands In UAV formations, the randomness of reconnaissance targets can lead to uneven traffic loads (transmission time slots), and the static TDMA access method may result in insufficient or fragmented time slots, causing incomplete or inefficient data transmission, thereby increasing data transmission delays and unpredictability.Furthermore, if the communication quality is poor (e.g., the bit error rate \(\gamma\) increases), retransmissions due to transmission failures must be taken into account to ensure reliable data delivery. However, the static scheme does not reserve retransmission time slots, causing retransmissions to compete for time slots allocated to other nodes, which leads to new collisions and increased delay. Specifically, if the link bit error rate is \(\gamma\), then the data packet loss rate can be expressed as:
Where \({L_d}\) is the effective length of the data packet. At this point, the actual number of packets a node needs to transmit is \(\frac{1}{1 - \tau }\) times the original amount, but the static time slot allocation does not account for the impact of \(\tau\), resulting in a mismatch between the required and allocated time slots, which further amplifies the transmission delay. Therefore, it is necessary to explicitly model the impact of link bit errors and incorporate it into the resource scheduling process.
Dynamic slot allocation for UAV formation networks
System model
This paper assumes that the UAV formation network consists of \(n + 1\) nodes (one leader and \(n\) wingman), each with a unique ID and communicating using omnidirectional antennas. To meet the communication requirements of UAV swarm systems under varying conditions, this paper divides the wireless channel into three key phases: the CSMA phase, the Centralized Time Slot Allocation (CTSA) phase, and the TDMA phase. Each phase is designed to accommodate dynamic service access and retransmission demands caused by bit errors, as shown in Fig. 2. Each wingman nodes dynamically access the network during the CSMA phase and transmit telemetry data in real-time during the TDMA phase.
the Architecture of our UAV communication System.
In the CSMA phase of each superframe, the leader UAV node first synchronizes the clocks of all follower nodes in the network by broadcasting a Beacon frame, ensuring time alignment across the entire system. After successful synchronization, each follower node senses the carrier to assess the channel’s occupancy status. When the channel is idle, follower node jjj sends a feedback packet to the leader node, which carries the error-aware effective queue length \({Q'_{t,j}}\), rather than the original queue length \({Q_{t,j}}\). This adjusted value accounts for the redundant retransmission demand caused by the channel bit error rate \({\tau _{t,j}}\), i.e., \({Q'_{t,j}} = {Q_{t,j}}/(1 - {\tau _{t,j}})\). If the channel is detected as busy, the follower node will wait for a random backoff time before attempting to retransmit. Once a node successfully sends a slot request, the leader node assigns it a unique contention state (including retransmission priority), which will be used as the node’s random backoff value in the next stage. Let N denote the set of all follower nodes in the network and \(N'\) denote the subset of nodes that successfully transmit feedback packets. During superframe ttt, the leader node maintains the reported effective queue lengths of all admitted follower nodes in the form \({\{ {Q'_{t,j}}\} _{j \in N'}}\).The total duration of the CSMA phase can thus be expressed as the time from the leader’s initial Beacon broadcast to the completion of all slot requests by the follower nodes:
where\(\sum \nolimits _{j = 1}^n {{T_j}}\) is the time required for all wingman nodes to complete network access, also known as the network convergence time; \({R_j}\) denotes the number of retransmission attempts for the access request of wing node j, and \({T_{re}}\) represents the average time consumed per retransmission attempt, which is positively correlated with \({\tau _{t,j}}\); \({{L_{bc}}}\) is the data size of the Beacon frame broadcast by the leader node; \({{R_{wl}}}\) represents the data transmission rate; and \({T_{sync}}\) indicates the time required for the wingman nodes to receive the Beacon frame, extract relevant clock information, and synchronize their local clocks.
In the CTSA phase, the lead node calculates the optimal time slot allocation table based on the effective queue length \({Q'_{t,j}}\) and the channel quality \({\tau _{t,j}}\) reported by wing nodes, and then broadcasts it to other nodes. The time slot allocation must meet the total demand of “original transmission + maximum number of retransmissions.” For wing node j, the base number of time slots is \({C_{t,j}}\), and the reserved time slots for retransmissions are calculated as \(C_{t,j}^r = [{C_{t,j}} \cdot {\tau _{t,j}}/(1 - {\tau _{t,j}})]\). Therefore, the total allocated time slots are \({C'_{t,j}} = {C_{t,j}} + C_{t,j}^r\). Therefore, the length of the CTSA phase can be expressed as:
Where \(T_{\text {calculate}}^{\text {time}}\) represents the time required for the leader node to allocate slots based on the slot requirements of all nodes, and \(L_{\text {TRST}}\) denotes the data size of the time slot schedule broadcasted by the leader node.
At the beginning of the TDMA phase in superframe \(t\), wingman node \(j\) receives the time slot table broadcasted by the leader node during the CTSA phase, thereby obtaining the number of slots \({C'_{t,j}}\) (adaptively extended based on the bit error rate, enhancing the system’s robustness and adaptability) allocated by the leader node and the length of the CSMA phase \(T_C\), and communicates data in the corresponding slots according to the slot table, \({T_s}\) is the duration of a single time slot.. The length of the TDMA phase can then be expressed as:
Design of contention-based access time slots
Random backoff algorithm with centralized collision avoidance
In a centralized formation network, the transmission slots of nodes need to be uniformly planned by the leader node. Therefore, during the CSMA phase, each wingman node must randomly select a backoff value to compete for the channel and report its slot requirements to the leader node. However, multiple wingman nodes may choose the same backoff value, leading to collisions when wingman nodes request slots from the leader node. This increases the delay jitter of services and adversely affects the deterministic transmission of time-sensitive services. Therefore, to ensure the random access of dynamic nodes, this paper proposes an RB-CCA algorithm during the CSMA phase, as shown in Algorithm 1. The leader node uniformly allocates the backoff states, including the backoff stage and backoff count, to each wingman node in the network, thereby controlling the random backoff of nodes to reduce packet collisions and determine the access delay of each node.
Due to node switching in UAV formation tasks, the length of the contention access phase must account for the time required for dynamic nodes to join or leave the network. As shown in Fig. 3, the process of wingman node access and the leader node assigning backoff states in RB-CCA is described. Unconnected wingman node 1, after receiving the Beacon frame, independently selects a random number 4 as its non-synchronized backoff count to compete for the channel and sends a network access request message, i.e., an information feedback data frame, to the leader node, as shown in step \(\textcircled {1}\). Upon successfully receiving the information feedback data frame, the leader node replies with an ACK frame, including the backoff stage and a randomly selected number 6 from the range \([0, CW_i - 1]\) as the synchronized backoff count for wingman node 1, as shown in step \(\textcircled {2}\). Similarly, wingman node 2 completes the access process and obtains its synchronized backoff count through steps \(\textcircled {4}\) to \(\textcircled {6}\). Here, \(CW_i = 2^i \cdot CW_0\) represents the backoff window for the \(i\)-th backoff stage, where \(CW_0\) denotes the minimum backoff window. If a wingman node successfully obtains a synchronized backoff count, it is referred to as an RB-CCA sub-node (CSN); if a wingman node fails to access or does not receive an ACK frame, it continues to use the CSMA mechanism to generate a new non-synchronized backoff count for channel contention, and is then referred to as a non-RB-CCA sub-node (CUN).
Node access process.
RB-CCA Algorithm.
Markov model
To obtain the node access latency under RB-CCA, this paper analyzes the entire state transition process using a Markov model, thereby deriving the theoretical performance of node access collision probability and delay. Within the convergence time, to quantify the access delay and collision probability of RB-CCA, a Markov model is established to analyze the state transitions in the backoff process. Here, \(\rho\) denotes the state transition probability, p represents the collision probability, m is the maximum backoff stage, and \(P_i^l\) denotes the probability of selecting a unique backoff count at backoff stage i when the number of wing nodes centrally assigned by the lead node is l. The state is defined as \(\left( {i,k} \right)\), where ii indicates the collision stage and k is the backoff count. First, at backoff stage i, the backoff count k decreases with each time step (the stage remains unchanged in the absence of collisions):
Second, after a successful data transmission (with probability \(1 - p\)), the wing node enters a new backoff stage j and reselects a backoff count (with uniqueness ensured by \(P_j^l\), which is the probability of being assigned a unique backoff count at stage j):
Then, after undergoing \(i - 1\) backoff attempts, the wing node recontends for the channel at backoff stage i:
Finally, when the wing node reaches the maximum backoff stage m, it remains in this stage until it successfully contends for the channel.
According to the limiting property of Markov processes, where the steady-state probability distribution equals the transition probability in the limit, and based on the assumption of uniform distribution of backoff counts (within backoff stage \(i\), the probability of count \(k\) is positively correlated with \({C{W_i} - k}\), since the count decreases over time and smaller \(k\) is closer to the transmission attempt), the backoff state \({b_{i,k}}\) for nodes with \(i \in [0,m]\) and \(k \in [0,C{W_i} - 1]\) can be expressed as:
Here, \(C{W_i}\) denotes the backoff window size at stage \(i\), typically defined as \(C{W_i} = {2^i} \cdot C{W_0}\) , where \(C{W_0}\) is the initial window size. The term \(\frac{{C{W_i} - k}}{{C{W_i}}}\) represents the uniform distribution weight of the backoff count, reflecting that smaller kkk values are more likely as the counter decreases over time. \(p\) is the collision probability for a single node at backoff stage \(i\), and \(P_i^l\) is the probability that the lead node assigns a unique backoff count to a wing node at stage \(i\). \({b_{i,0}}\) as shown in Eq. (12), is the total steady-state probability that all nodes are in backoff stage \(i\) with backoff count 0. \(m\) is the maximum backoff stage. Equation (11a) represents the initial backoff stage without any prior collisions. Equation (11b) corresponds to intermediate backoff stages, influenced by both collisions and successful transmissions in the previous stage. Equation (11c) describes the maximum backoff stage, which is affected by collisions from both the previous stage and the current one.
Equations (12) and (13) are special cases of Eq. (11) when the backoff count \(k = 0\) (i.e., the critical state where the backoff count reaches zero and the node is about to contend for the channel).Since \(\sum \limits _{i = 0}^m {\sum \limits _{k = 0}^{C{W_i} - 1} {{b_{i,k}}}} = 1\) in the Markov chain state transition, we have:
Where \(f_i^j (l) = p^{(i-1-j)} \frac{P_{j+1}^l}{P_0^l}\). Therefore, the node transmission success probability \(\lambda\) can be expressed as:
When the number of CSNs in the UAV formation network is \(l\), the probability \(P_{\text {ctr}}(l)\) that at least one node starts transmitting data within a CSMA slot time is:
Where \(P_{\text {ctr}}^{\text {cun}}(l)\) represents the probability that at least one CUN starts transmitting, and \(P_{\text {ctr}}^{\text {csn}}(l)\) denotes the probability that at least one CSN starts transmitting. Therefore, we have:
Where \(N_i^l\) represents the number of nodes selecting synchronized backoff counts at the \(i\)-th backoff stage; \(\frac{N_0^l}{C{W_0} - 1}\) denotes the density of backoff counts selected at the 0-th backoff stage; \(1 - \frac{N_0^l}{C{W_0} - 1}\) denotes the density of unassigned backoff counts in this range; \(1 - {P_{\text {ctr}}}{P_s}{Z^l}\) denotes the probability of assigning non-zero backoff counts; \({P_s}(l)\) and \({Z^l}\) denote the probability of successful data transmission and the probability of selecting zero as the backoff count, respectively, when the number of CSNs is \(l\). Thus:
Where Eq. (19a) represents the successful transmission probability of a CUN, which requires the condition that “the CUN transmits while all other CUNs remain silent.” Eq. (19b) represents the successful transmission probability of a CSN, which requires the condition that “the CSN transmits while all CUNs remain silent.” Therefore, in the CSMA phase, the probability \(p\) of a packet collision is equal to the probability that at least one of the other \(n - 1\) nodes (excluding the current node) begins transmitting data in that time slot. If a CUN begins transmitting data during the CSMA period, and all other \(n - l - 1\) CUNs and \(l\) CSNs do not start transmitting data at the same time, there will be no collision. In the case when a CSN begins transmitting data, since each CSN has a unique backoff counter, there will be no collision if the \(n - l\) CUNs do not start transmitting data simultaneously. Therefore, we have:
Specifically, Eq. (20a) represents the probability of a collision occurring during CUN data transmission, which requires the condition that “the CUN transmits while at least one other node (including CSNs) also transmits.” Equation (20b) represents the probability of a collision occurring during CSN data transmission, which requires the condition that “the CSN transmits while at least one CUN also transmits” (collisions among CSNs do not occur due to unique backoff counts). Taking their average, the collision probability p in the CSMA phase is:
From Eqs. (16) and (21), given \(l\) and \(n\), \(\lambda\) and \(p\) can be determined, thereby obtaining the expected number of collisions \(\frac{1}{\lambda }\) for a wingman node to successfully request a slot in the CSMA phase. After successfully receiving the slot request from the \(n\)-th wingman node, the leader node records the current backoff stage \(i\) and \(N_i^l\). Therefore, the average delay required for node \(j\) to successfully join the network in superframe \(t\) is:
Thus, the length of the contention access period \(T_C\) in the network is:
Dynamic time slot allocation based on delay optimization
Due to the limited total number of time slots, overly loose slot allocation can reduce network capacity, while overly tight slot allocation may prevent nodes from completing tasks and degrade transmission reliability. When determining the length of transmission slots, the communication quality of the entire network must be considered; when allocating the number of slots, the traffic volume of each node must be taken into account to ensure the reliability and fairness of data transmission. Based on the characteristics of wireless networks, this paper assumes that each terminal node communicates on a single channel and power level, and the unit slot length \({T_s}\) is adjustable. The slot length for each node is an integer multiple of \({T_s}\). Considering that the packet sizes of different nodes may vary, this paper adopts the A-MPDU frame aggregation method, assuming that all transmitted packets have the same size \({L_d} + {L_h}\), where \({L_d}\) represents the effective data of the A-MPDU packet, and \({L_h}\) represents the header length of the A-MPDU packet, both measured in bytes. Therefore, the unit slot \({T_s}\) in the TDMA phase can be expressed as:
Ideally, the number of slots required by node \(i\) in superframe \(t\) is \(M_{t,i} = B_{s_{t,i}} / L_d\), where \(B_{s_{t,i}}\) represents the effective data packet size of the node. However, in the IEEE 802.11 standard, data loss, errors, timeouts, or the receiver’s inability to process data in a timely manner may occur due to poor network quality, interference, and other issues. In such cases, the sender triggers a retransmission mechanism according to the protocol’s retransmission strategy to ensure reliable data transmission24. Nevertheless, existing schemes rarely consider the differences between wireless nodes and communication environments when allocating slots, making it difficult to fully meet the end-to-end delay requirements of time-sensitive data. To ensure the reliability and fairness of data transmission, retransmission mechanisms must be implemented for failed data packets. The communication quality of a link can be measured by the bit error rate (BER), where the transmission of each bit follows a binomial distribution \({\mathop {\mathrm{{B}}}\nolimits } (n, 1 - {\gamma _t})\). Therefore, if the BER of the link is \({\gamma _t}\), the packet loss rate \({\zeta _{t,i}}\) of the link can be expressed as:
To ensure that all data packets are successfully transmitted, the actual number of unit slots \({C_{t,i,s}}\) and the slot length required for data stream \({s_{t,i}}\) of node \(i\) in superframe \(t\) are respectively:
Where \(\big \lceil \cdot \big \rceil\) denotes the ceiling function (rounding up to the nearest integer), and \({T_g}\) represents the guard band length during node slot switching.
End-to-End delay analysis
In UAV formations, ensuring the deterministic transmission of time-sensitive services requires precise characterization of the overall delay of time-sensitive data, determining the position of its transmission slots, and guaranteeing that time-sensitive data can be scheduled and transmitted in a timely manner. This improves network efficiency and enhances the mission coordination performance of UAVs. Assume that the time-sensitive data stream \(s_{t,i}\) of node \(i\) in superframe \(t\) has a generation period of \(T_{t,i}\) and a data volume of \(B_{t,i}^s\), with a wireless port transmission rate of \(R_{wl}\). Therefore, the objective function with the goal of minimizing the end-to-end delay of time-sensitive data is:
Here, \(D_{t,i,s_{t,i}}^{\text {trans}}\) represents the transmission delay of the data packet, \(D_{t,i,s_{t,i}}^{\text {prop}}\) represents the propagation delay over the wireless link, and \(D_{t,i,s_{t,i}}^{\text {wait}}\) represents the waiting delay of the node. Constraint C1 specifies the unit transmission time slot length in the TDMA phase. Constraint C2 defines the number of time slots required for node \(i\) under the current communication environment during superframe \(t\), while C3 ensures that the required time slots are no fewer than the theoretical calculation. C4 ensures that the total number of slots in the TDMA phase is the sum of the slots required by all nodes in the network. C5 limits the delay of node \(i\)’s data stream within the superframe \(t\) to below its maximum allowable end-to-end delay. Finally, C6 and C7 specify the time slot length requirements for the CSMA and CMOP phases. The waiting delay \(D_{t,i,s_{t,i}}^{\text {wait}}\) can be defined as the time between the generation of the data packet and its allocated slot, expressed as:
DySTMap Ivy algorithm
When the wingman nodes report their time slot requests during the CSMA phase, the leader node can solve for the end-to-end delay of time-sensitive data and the required time slot table for the TDMA phase using a dynamic slot allocation algorithm during the CMOP phase. The Ivy Optimization Algorithm25 is a novel population-based metaheuristic algorithm that simulates the orderly coordinated growth of ivy populations and the diffusion-evolution process of ivy plants. It is characterized by its speed and minimal parameter requirements. This algorithm mimics the behavior of ivy plants in nature by selecting the closest and most significant neighbors for self-improvement, with each ivy individual representing a potential solution. Based on an analysis of the characteristics of the Ivy Optimization Algorithm, this paper proposes an improved version, termed the DySTMap Ivy Algorithm (DIvyA), as shown in Algorithm 2. to rapidly solve for the end-to-end delay of time-sensitive data and the time slot lengths for each node.
First, the population is randomly generated, and the positions and growth rates of the individuals are initialized. The position of each individual represents the location of the wingman node during the TDMA phase, while the growth rate of the individual denotes the length of the unit time slot. At the beginning of the DIvyA algorithm,is presented in Algorithm 2. The initial positions of the DIvyA population in the search space are randomly determined using Eq. (30):
where \({I_{\max }}\) and \({I_{\min }}\) represent the upper and lower bounds of the search space, respectively, and \(\odot\) denotes the Hadamard product of two vectors.
In Eq. (31), \(DySTMap(1,D)\) represents the generation of a D-dimensional chaotic sequence using the Tent-Logistic-Cosine mapping. Starting from an initial value \(x_0\) for each iteration, the value of \(x\) is updated according to the aforementioned chaotic mapping. Each \(x_i^{(i)}\) is the result of the \(i\)-th iteration computed based on the chaotic mapping formula.
Equations (32) and (33) describe how member \({I_i}\) utilizes member \({I_{ii}}\) to climb and perform logical movement along the direction of the light source. Equation (34) describes the growth rate of an individual.
Here, \(|DySTMap(1,D)|\) is a vector, \(\odot \Delta {G_{{v_i}}}\) denotes the growth increment, and \({N_{pop}}\) indicates the population size.
After the phase in which member \({I_i}\) roams globally through the search space to the nearest and most significant neighbor \({I_{ii}}\), there is a phase where member \({I_i}\) attempts to directly follow the best member of the entire population \({I_{Bset}}\) to search for a better optimal solution, as expressed by Eq. (35):
Subsequently, the new growth rate \(\Delta G_{{v_i}}^{new}\) of the current member \(I_i^{new}\) is calculated using Eq. (36). The workflow of the DIvyA algorithm is summarized in Algorithm 2.
DIvyA Algorithm.
Experiments and results analysis
This paper first constructs a UAV formation network simulation scenario on the Exata network simulation platform to conduct a comparative analysis of the performance of the proposed RB-CCA algorithm and DIvyA dynamic slot allocation scheme against existing algorithms. The RB-CCA algorithm is compared with the Binary Exponential Backoff (BEB), the latest Priority Fibonacci Backoff (PFB)26, and the Multi-Agent Distributed Training and Distributed Execution (DTDE) framework based on a reconfigurable MAC protocol27 to evaluate the performance of different backoff algorithms. The DIvyA dynamic slot allocation scheme is compared through simulation with the Adaptive Slot Assignment Protocol (ASAP)28, Time-spread Multiple-Access (TSMA)29, Tdma-based Centralized Scheduling Algorithm (TCSA)30, and the Cross-Layer mTSP Solution (CLMS)31.Subsequently, a semi-physical UAV formation network testbed is built using the Zynq + AD9631 development board to verify the feasibility and performance of the proposed schemes.
Validation of model performance
To validate the effectiveness of the proposed Markov model in predicting the access performance of RB-CCA, a set of comparative experiments was conducted. Specifically, key performance metrics were obtained through both analytical modeling and network simulation, and the results were compared for consistency. The Markov model derives theoretical expressions for the collision probability \(p\) and access success rate \(\lambda\) based on state transition probabilities of each node. In contrast, the simulation data were obtained from the high-fidelity Exata network simulation platform, which accurately emulates MAC-layer behavior. The simulator recorded the actual access process under varying network sizes (e.g., 5–25 nodes), including the number of successful accesses and collision events in each round. To ensure the comparability between the model predictions and simulation data, the simulation parameters (e.g., backoff window size, channel quality, and traffic load per node) were strictly aligned with the analytical assumptions. As shown in Fig. 4(a) and Fig. 4(b), as the number of network nodes increases, the Markov model’s predictions of access success rate and collision probability closely match the results from Exata simulations, with an average error of less than 5% and a high degree of agreement in overall trends. This confirms the model’s effectiveness in characterizing the access behavior of the RB-CCA protocol. Notably, even under high node density, the model maintains strong predictive stability and accurately reflects the access bottlenecks and increased collision phenomena that occur under heavy network load.
Comparison Between Markov Model Predictions and Simulation Data (a) Collision Probability and (b) Node Access Success Rate.
Algorithm performance simulation comparison
The UAV formation simulation scenario built on the Exata platform in this paper is shown in Fig. 5. The leader node is located at the center, and the wingman nodes outside the red circle represent newly accessed nodes after a certain period.
UAV formation simulation scenario.
Since this paper is based on further design and implementation of the IEEE 802.11n protocol, the data frame transmission rate in the simulation is set to 54 Mbps, the ACK frame rate is set to 6 Mbps, the Distributed Coordination Function Interframe Space (DIFS) and Short Interframe Space (SIFS) are set to 34 \(\mu\)s and 16 \(\mu\)s, respectively, and the maximum distance between the leader node and each wingman node is set to 50 m. As this paper primarily considers the deterministic access problem of dynamic nodes, the number of wingman nodes in the network is increased sequentially from 1 to 30, while the minimum and maximum backoff windows are set to 16 and 1024, respectively. The settings for the data information transmitted by each node in the TDMA phase are based on reference32, as shown in Table 1. Among them, pressure, temperature, and video surveillance information are set as time-sensitive services, while the remaining client information is set as non-time-sensitive services.
Figure 6(a) shows the throughput of BEB, RB-CCA, PFB, and DTDE for different payloads when the number of wingman nodes in the UAV formation network is 4. It can be clearly observed from the figure that as the payload increases from 16 Bytes to 256 Bytes, the throughput of RB-CCA outperforms the existing BEB, PFB, and DTDE algorithms. For BEB, the throughput increases from 4% at a payload of 16 Bytes to 59% at a payload of 236 Bytes. Similarly, compared to PFB, the throughput gain ranges from 1% (at 16 Bytes) to 21% (at 176 Bytes). At a payload of 260 Bytes, RB-CCA achieves 27.9% higher throughput than DTDE. This is because RB-CCA centrally controls the backoff states via the lead node, directly avoiding random backoff collisions, whereas DTDE relies on online learning to adjust the contention window, which causes strategy convergence delays under increasing load. Since the network contains 4 wingman nodes and has not reached the saturation state of RB-CCA, the throughput of RB-CCA continues to increase.
Throughput Performance Comparison (a) Total Throughput of Different Backoff Algorithms and (b) Comparison of Total Throughput for Multi-Node Networks.
Figure 6(b) illustrates the throughput per unit time for payloads of 256 Bytes and 1400 Bytes as the number of network nodes increases from 1 to 20 for the four algorithms. Due to a large number of collisions and wasted slots in the superframe, the throughput of BEB begins to decline after 4 nodes. PFB, which introduces smaller backoff window gaps and accordingly adjusts the backoff window, starts to decline in throughput when the number of nodes reaches 8. For DTDE, the throughput peaks and then declines after 6 nodes under a 256-Byte payload; in the high-load scenario of 1400 Bytes, the decline begins even earlier at 5 nodes. Ultimately, at 20 nodes, the throughput drops to 8 Mbps (256 Byte payload) and 12 Mbps (1400 Byte payload). Although DTDE performs worse than RB-CCA, it still outperforms the late-stage performance of BEB and PFB. This is because DTDE employs a distributed negotiation mechanism; as the number of nodes increases, the slot request collision probability surges from 10% to 45%, causing some nodes to enter the retransmission queue due to failed requests, further reducing throughput. However, the proposed RB-CCA centrally allocates node backoff states, reducing access collisions without adjusting the contention window size. Therefore, the throughput of RB-CCA only begins to decline after 14 nodes. According to the total network throughput results, RB-CCA reduces idle slots by 30% compared to the BEB and PFB random backoff algorithms. The decline in RB-CCA throughput is due to the decreasing probability of idle slots in the network per unit time, which cannot meet the access demands of more nodes.
The variation in throughput of RB-CCA at different times with the number of nodes.
When the throughput is in an upward trend, it indicates that the nodes in the network are accessing without collisions, i.e., the convergence time required to reach a collision-free state. Therefore, to test the convergence time of the RB-CCA algorithm for nodes to reach a collision-free state, the changes in network throughput with increasing node numbers over 1 s, 10 s, and 60 s are analyzed, as shown in Fig. 7. The figure shows that 14 nodes can reach a collision-free state within 1 s, 16 nodes within 10 s, and 20 nodes within 60 s. In summary, the more nodes in the network, the more time is required to reach a collision-free state, and once the saturation state is exceeded, the network throughput drops sharply with the increase in nodes.
Performance comparison of slot allocation Algorithms.
Figure 8 illustrates the end-to-end delay variations for time-sensitive services using DIvyA, ASAP, TSMA, TCSA, and CLMS under different numbers of network nodes. It can be observed that, as the number of nodes increases, the end-to-end delay of time-sensitive data using the proposed DIvyA slot allocation scheme is significantly lower than those of the other four schemes. When the number of nodes reaches 20, the end-to-end delay of DIvyA stabilizes below 10 ms, while ASAP’s delay is around 17 ms, TSMA’s delay is about 25 ms, CLMS’s delay is 24.0 ms, and TCSA’s delay stabilizes at 34.83 ms. Compared to these four slot allocation schemes, DIvyA reduces the end-to-end delay by more than 20%. The delay of CLMS becomes slightly lower than that of TSMA when the number of nodes is 13, because CLMS dynamically adjusts slot allocation based on physical-layer channel quality feedback and reserves resources specifically for time-sensitive services. In contrast, TCSA’s delay rises sharply after 3 nodes and eventually stabilizes at 35 ms. Compared to these four slot allocation schemes, DIvyA reduces the end-to-end delay by 20%. This is because DIvyA aggregates frame data within unit time slots during slot allocation and considers retransmissions caused by communication failures during data transmission. This approach not only addresses the low slot utilization problem caused by varying frame lengths but also ensures reliable data transmission.
Semi-physical scenario validation and analysis
To test the feasibility and effectiveness of the proposed scheme, the RB-CCA and dynamic slot allocation strategy were designed and implemented on an FPGA platform. This paper constructs an actual network consisting of one leader node and four wingman nodes, with the test scenario illustrated in Fig. 9(a), where each node is spaced 50 meters apart. Additionally, this paper directly connects wingman node 3 to the network for a period, then disconnects and reconnects it. Based on the characteristics of onboard service data, four types of service data with different attributes are configured for the nodes. Taking the wingman node test scenario as an example, as shown in Fig. 9(b), four types of services are connected to the wingman node through a network port and transmitted according to TDMA slot scheduling. These include three types of periodic time-sensitive data and one type of aperiodic non-time-sensitive service data (motor, camera, and infrared sensor transmit time-sensitive services, while the light transmits non-time-sensitive services). The traffic volume dynamically varies from 256 Bytes to 1400 Bytes. Since the onboard transmission power cannot meet the 50-meter transmission distance, an external high-gain antenna is used to improve the communication range.
Semi-Physical Scenario Test Diagram (a) Schematic Diagram of the Test Scenario and (b) Wingman Node Service Configuration.
Figure 10(a) shows the end-to-end delay test for three types of periodic time-sensitive services and one type of aperiodic service. The system first buffers data with different time sensitivities in separate queues and represents different time sensitivities with priorities. Then, when allocating slots to all nodes in the network, the master node allocates slots in order of priority from high to low based on the slot request information. Finally, the entire slot table is constructed primarily with periodic time-sensitive services. From the figure, it can be observed that the end-to-end delays of the three types of periodic time-sensitive services remain relatively stable. Specifically, the average end-to-end delay for the motor is 4.1 ms, for the camera is 8.05 ms, and for the infrared sensor is 5.85 ms. Additionally, the average jitter for these three time-sensitive services remains below 0.12 ms, meeting the operational network requirements for UAV formation flight33. However, the aperiodic non-time-sensitive service transmitted by the light exhibits significant delay fluctuations and higher jitter compared to fixed slot allocation due to the randomness of its generation period, which prevents the allocated slot positions from aligning with its generation time. Furthermore, the delays for the camera and infrared sensor are slightly higher than that of the motor because the former two have shorter data generation periods and larger data volumes. Figure 10(b) shows the comparison of end-to-end delays using different wireless protocols. It can be observed that as the transmission rate of non-time-sensitive services increases, the delay of DIvyA remains stable at around 4.5 ms, with end-to-end jitter within 1 ms. As the load increases, data collisions intensify, causing the end-to-end delay of the CSMA/CA protocol to rise sharply. The static TDMA slot allocation algorithm shows a slight increase in delay as the network load increases, as its slot allocation algorithm does not consider the generation of time-sensitive services, resulting in additional waiting time for data until its slot arrives.
Performance Testing of Dynamic Slot Allocation (a) End-to-End Delay of Time-Sensitive Services and (b) Comparison of End-to-End Delay Across Wireless Protocols.
Conclusion
In this paper, a dynamic time slot allocation strategy was proposed for deterministic communication in UAV formations, to address the issues of flexible access and dynamic service changes in UAV formation networks. Firstly, an RB-CCA algorithm is introduced during the CSMA phase to resolve the problem of uncertain node access delays caused by collisions. Then, to avoid resource waste and delays caused by fixed slot sizes, a DIvyA dynamic slot allocation scheme is designed. Finally, the performance of the proposed algorithms was evaluated on the Exata simulation platform. Moreover, we implement the proposed scheme on an FPGA platform, and conduct semi-physical scenario experiments to verify that the strategy can meet the common requirements of UAV formation operations. In our future work, we will try to find the backoff window settings to reduce the convergence time to a collision-free state and improve overall network throughput while ensuring the deterministic transmission requirements of time-sensitive services.
Data availability
The data generated and analyzed during the current study are not publicly available due to the complexity of the Exata network simulation environment and the specific configuration of the Zynq + AD9631 development board-based semi-physical scenario, which involve proprietary settings and potential security risks. However, the data can be made available from the corresponding author upon reasonable request and with the permission of the research team and relevant institutions. All requests for data access should be sent to xiaojunfang@cdp.edu.cn.
References
Tian, W. et al. Large-scale deterministic networks: Architecture, enabling technologies, case study, and future directions. IEEE Network 38, 284–291 (2024).
Muzakkari, B. A., Mohamed, M. A., Kadir, M. F., Mohamad, Z. & Jamil, N. Recent advances in energy efficient-qos aware mac protocols for wireless sensor networks. Int. J. Adv. Comput. Res. 8, 212–228 (2018).
Galmés, S. A new collision resolution mechanism based on the discovery of colliding sources. In 2024 IEEE Wireless Communications and Networking Conference (WCNC), 1–6 (IEEE, 2024).
Zhao, Q. et al. Full-duplex time-domain contention for wifi networks: Opportunities and challenges. IEEE Wirel. Commun , 142–151 (2024).
Wang, H., Gu, J. & Xia, L. Improved beb algorithm for computer network optimization. In 2023 2nd International Conference for Innovation in Technology (INOCON), 1–5 (IEEE, 2023).
Iskandarani, M. Z. Vehicular connectivity modeling and simulation using modified np-csma. In 2023 3rd International Conference on Electrical, Computer, Communications and Mechatronics Engineering (ICECCME), 1–7 (IEEE, 2023).
Jiang, S. & Zheng, J. A drqn-based initial contention window optimization algorithm for nr-u and wifi coexistence networks. In GLOBECOM 2022-2022 IEEE Global Communications Conference, 6019–6024 (IEEE, 2022).
Wang, H., Chen, P. & Wang, P. Deterministic scheduling algorithms for wia-pa industrial wireless sensor networks. Acta Electron. Sin. 46, 68–74 (2018).
Zheng, Y., Xu, A., Song, Y., Zhao, W. & Liu, M. Industrial wireless deterministic communication based on wlan: Design, implementation and analysis. In 2009 IEEE International Conference on Communications Technology and Applications, 274–278 (IEEE, 2009).
Sari, R. F., Harwahyu, R. & Cheng, R.-G. Load estimation and connection request barring for random access in massive c-iot. IEEE Internet Things J. 7, 6539–6549 (2020).
Sharma, N. et al. A novel routing protocol over time-varying iot network using rts/cts framework. In 2024 IEEE International Conference on Advanced Networks and Telecommunications Systems (ANTS), 1–6 (IEEE, 2024).
Wang, J., Ma, J., Jin, M., Huang, S. & Liang, S. Research on the improvement of rts/cts mechanism in wapi protocol for power systems. In 2025 IEEE 8th Information Technology and Mechatronics Engineering Conference (ITOEC), vol. 8, 1011–1015 (IEEE) (2025).
Xu, D. Latency minimization for tdma-based wireless federated learning networks. IEEE Trans. Veh. Technol. , 13974-13979 (2024).
Papageorgiou, Y., Karaliopoulos, M., Choumas, K. & Koutsopoulos, I. Joint controller placement and tdma scheduling in software defined wireless multihop networks. IEEE Trans. Netw. Serv. Manag., 2807-2821 (2025).
Liang, J., Li, Y. & Liu, H. Research and analysis of anti-jamming performance on the joint tactical information distribution system. In 2022 IEEE 2nd International Conference on Information Communication and Software Engineering (ICICSE), 146–150 (IEEE, 2022).
Wu, D., Wang, G.-Y. & Li, X.-L. Distributed tdma scheduling protocol based on conflict-free for wireless sensor networks. In 2010 International Conference on Intelligent Computing and Integrated Systems, 876–879 (IEEE, 2010).
Lee, J.-K., Noh, H.-J. & Lim, J. Dynamic cooperative retransmission scheme for tdma systems. IEEE Commun. Lett. 16, 2000–2003 (2012).
Park, J., Baek, H. & Lim, J. A dynamic tdma scheme for uav based relay in combat net radio networks. In 2019 International Conference on Information Networking (ICOIN), 290–295 (IEEE, 2019).
Tuysuz, M. F. & Mantar, H. A. Exploiting the channel using uninterrupted collision-free mac adaptation over ieee 802.11 wlans. Wirel. Commun. Mob. Comput. 15, 889–909 (2015).
Yeh, B.-H., Wu, J.-M. & Chang, R. Y. Efficient doppler compensation for leo satellite downlink ofdma systems. IEEE Trans. Veh. Technol., 18863-18877 (2024).
Chittapragada, B. M., Kumar, R., Doley, V. & Chandavarkar, B. Improving dynamic tdma for wireless sensor networks. In 2023 14th International Conference on Computing Communication and Networking Technologies (ICCCNT), 1–7 (IEEE, 2023).
Khodaverdian, M., Hajshirmohamadi, S., Hakobyan, A. & Ijaz, S. Predictor-based constrained fixed-time sliding mode control of multi-uav formation flight. Aerosp. Sci. Technol. 148, 109113 (2024).
Shao, C. & Muta, O. When lorawan meets csma: Trends, challenges, and opportunities. IEEE Internet Things Mag. 7, 90–96 (2024).
Xu, Y. et al. Packet retransmission schemes and trials for broadcast services in mobile scenarios. IEEE Trans. Broadcast., 1113-1125 (2024).
Ghasemi, M. et al. Optimization based on the smart behavior of plants with its engineering applications: Ivy algorithm. Knowl.-Based Syst. 295, 111850 (2024).
Khan, P. et al. Performance analysis of different backoff algorithms for wban-based emerging sensor networks. Sensors 17, 492 (2017).
Keshtiarast, N., Renaldi, O. & Petrova, M. Wireless mac protocol synthesis and optimization with multi-agent distributed reinforcement learning. IEEE Netw. Lett., 242-246 (2024).
Gonzalez, G. et al. Asap: A semi-autonomous precise system for telesurgery during communication delays. IEEE Trans. Med. Robot. Bionics 5, 66–78 (2023).
Ma, Y., Ma, G. & Ai, B. Multicarrier tandem spreading multiple access (mc-tsma) for high-speed railway (hsr) scenario. IEEE Internet Things J. 8, 3490–3499 (2020).
Zhong, S., Sun, H., Yuan, J. & Tang, J. A practical method for blind detection of centralized unique word tdma signal. In 2022 4th International Conference on Communications, Information System and Computer Engineering (CISCE), 7–10 (IEEE, 2022).
Keshavamurthy, B. & Michelusi, N. Orchestrating uavs for prioritized data harvesting: A cross-layer optimization perspective. In 2024 IEEE International Conference on Communications Workshops (ICC Workshops), 1268–1273 (IEEE, 2024).
Zhu, Y. et al. Traffic modeling and performance analysis for remote sensing satellite networks. In 2018 IEEE Global Communications Conference (GLOBECOM), 1–6 (IEEE, 2018).
Sayeed, M. A. & Kumar, R. An efficient mobility model for improving transmissions in multi-uavs enabled wsns. Drones 2, 31 (2018).
Acknowledgements
This research was supported by the Natural Science Foundation of Chongqing, China (Grant No. CSTB2023NSCQ-LZX0129).
Author information
Authors and Affiliations
Contributions
Junfang Xiao: Oversaw the overall research planning, led the systematic literature review, designed the system model architecture, coordinated experiment design, execution, and result analysis, and reviewed and revised the manuscript. Jianming Huang: Assisted in the literature review, participated in the design and implementation of some modules of the system model, and was responsible for experimental operations and data collection. Qin Chen: Focused on the screening and sorting of references, optimized the system model, and took the lead in analyzing and processing experimental data to draw conclusions. Chuan Xu: Supported the literature review by collecting relevant materials, assisted in model debugging and verification, and helped with experimental preparations, including equipment setup and adjustment. Guofeng Zhao: Participated in the discussion of research results, provided constructive suggestions, assisted in manuscript writing and proofreading, and coordinated technical support and resources. All authors reviewed the manuscript.
Corresponding author
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Xiao, J., Huang, J., Chen, Q. et al. Dynamic time slot allocation method for deterministic communication in UAV formation. Sci Rep 16, 841 (2026). https://doi.org/10.1038/s41598-025-30533-0
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1038/s41598-025-30533-0