Abstract
The proliferation of resource-constrained IoT devices has intensified the conflict between robust security requirements and hardware limitations. Conventional lightweight encryption algorithms (e.g., TEA, Speck) often fail to resolve this tension, exhibiting known cryptanalytic vulnerabilities while imposing excessive computational and energy overhead. This paper presents the Two-Stage Encryption Approach (TTEA), an innovative cryptographic framework optimized for IoT ecosystems. TTEA incorporates a \(20 \times 20\) bit-sliced S-box as a non-linear substitution layer to ensure high diffusion and resistance to differential attacks, together with an adaptive key scheduling mechanism that dynamically adjusts computational complexity based on device power states. Evaluation on standard IoT platforms such as ESP32 and Raspberry Pi demonstrates that TTEA reduces energy consumption by 39% compared to TEA, lowers memory requirements by 40%, and achieves 20% faster execution speeds. Security analysis confirms an avalanche effect of 48.5% and near-ideal ciphertext entropy (7.98 bits for 128B packets). Furthermore, TTEA shows resilience against differential and linear cryptanalysis, side-channel attacks, and quantum threats when integrated with CRYSTALS-Kyber for post-quantum key exchange. By bridging the gap between post-quantum security and energy efficiency, TTEA offers a validated solution for modern IoT deployments.
Similar content being viewed by others
Introduction
The Internet of Things (IoT) is increasingly embedded across sectors such as healthcare, industrial automation, and urban infrastructure, interconnecting a vast array of devices into expansive networks1.
Yet, widespread IoT adoption faces two persistent obstacles: first, the significant computational and energy constraints characteristic of sensor nodes; and second, the ongoing and intensifying need for effective, scalable security solutions.
As the volume of deployed IoT devices accelerates, so does the system’s susceptibility to security breaches that may compromise data confidentiality, integrity, and service reliability2. Traditional cryptographic solutions like AES and RSA, while secure, tend to exceed the resource limitations typical of compact, battery-operated IoT devices3.
Within the field of lightweight cryptography, researchers have put forward a wide variety of compact algorithms. Notable examples include TEA and Speck, which are valued for their simplicity and ability to fit into constrained environments. That said, these algorithms come with notable security limitations; vulnerabilities to attacks like related-key and differential attacks are well documented in the literature4,5.
More contemporary approaches, such as ASCON6 and SPARKLE7, offer increased efficiency and have advanced to finalist status in the NIST lightweight cryptography competition. However, these designs are not intrinsically resistant to quantum attacks, which leaves a significant gap given emerging computational threats.
Simultaneously, post-quantum key encapsulation mechanisms—Kyber8 serving as a prominent example—demonstrate powerful security capabilities, particularly against the looming threat of quantum adversaries. Yet, they present a significant obstacle for ultra-constrained IoT devices: heightened computational and memory demands. These overheads, while acceptable in larger systems, may push resource-limited nodes past their viable operational limits, ultimately restricting their practical adoption in IoT scenarios.
On a parallel track, optimization efforts within wireless sensor networks (WSNs) have long prioritized energy-aware clustering protocols to extend network lifetimes. Protocols such as LEACH9, PEGASIS10, and HEED11 have formed a foundation for enhancing energy efficiency, while more recent initiatives have embraced strategies based on fuzzy logic12 and machine learning techniques13. These innovations seek to dynamically distribute workloads and conserve nodes’ limited energy reserves.
Despite tangible progress in prolonging operation via these clustering protocols, a significant dichotomy remains: the treatment of security and clustering as separate, largely independent challenges. This separation enforces a compromise between two crucial concerns: favoring energy efficiency often undermines overall security, whereas adopting robust protective measures tends to deplete limited energy resources more rapidly. As a result, practitioners and researchers are frequently left navigating a difficult compromise, negotiating the delicate balance between network longevity and the imperative for strong security.
The persistent separation between secure encryption and energy-efficient networking in current research highlights a critical gap—one that calls for a comprehensive framework capable of addressing both lightweight, quantum-resistant security measures and energy-aware network management in tandem. The existing discourse often treats these domains in isolation, leading to fragmented solutions that fall short of meeting the unique demands of modern IoT environments, where constrained devices require both robust protection and judicious energy usage.
To address this, our work introduces the Ternary Tree Encryption Algorithm (TTEA), a novel block cipher explicitly created for use with resource-limited IoT platforms. TTEA’s architecture is distinguished by its compact round function, intentionally crafted for microcontrollers with tight memory restrictions. Notably, the cipher supports optional integration with hybrid post-quantum key exchange protocols, ensuring preparedness for emerging quantum-era threats.
In this framework, we integrate TTEA within a dynamic, system-level strategy in conjunction with the Resource-Efficient Adaptive Bio-inspired Clustering Optimization (REABCO) algorithm. Unlike traditional clustering approaches, REABCO employs context-aware and security-focused decision-making, continuously adapting to fluctuations in energy consumption and to shifts in the threat landscape. This approach forms the core of our unified model, bridging the longstanding gap between network efficiency and security considerations.
The main contributions of our paper are summarized as follows:
-
We present TTEA, a cipher that uniquely balances lightweight implementation and energy awareness, achieving performance metrics that compare favorably to the prevailing lightweight cryptographic standards, all while maintaining quantum resistance through optional post-quantum key exchange.
-
We demonstrate the integration of TTEA with REABCO within a holistic system, highlighting how real-time co-adaptation between clustering strategies and cryptographic mechanisms yields both security and efficiency benefits under variable energy and threat conditions.
-
We offer an extensive security evaluation, analyzing TTEA’s resistance to differential and linear cryptanalysis, side-channel attacks, and potential post-quantum adversaries.
-
We conduct thorough performance benchmarking on representative IoT-class microcontrollers, clarifying previously conflicting results in ASCON cipher comparisons and detailing the trade-offs between energy consumption and latency in practical terms.
-
To promote transparency and reproducibility, we release the full implementation codebase, raw measurement data, and all experimental scripts in a public repository, inviting community scrutiny and further development.
The remainder of this paper is organized as follows. Section IV reviews related work, Section V describes the design of TTEA and its integration with REABCO, Section XIII presents the security analysis, Section XII reports the performance evaluation, Section XI discusses the experimental setup and reproducibility, and Section XVIII concludes the work. Through this unified lens, our work aims to bridge the discontinuity between the security and network optimization communities, offering both theoretical innovation and practical advancement for next-generation distributed IoT deployments.
Notation and preliminaries
This section introduces the symbols, parameters, and cryptographic assumptions used throughout the paper. Table 1 summarizes the notation for quick reference.
Cryptographic assumptions
We operate within the widely accepted block cipher security model, in which adversaries are assumed to be computationally bounded and permitted to conduct chosen-plaintext and chosen-ciphertext attacks. In the symmetric-key scenario, even when quantum adversaries are considered, the practical impact is limited–Grover’s algorithm induces only a quadratic speed-up. To maintain robust security margins in the face of such quantum advancements, it suffices to double the secret key length; for example, adopting 256-bit keys is considered an adequate precaution14.The cryptographic definitions and security assumptions adopted in this work follow the well-established principles of classical cryptography as formalized in standard references such as the Handbook of Applied Cryptography15.
System model
The focus of this work is a resource-constrained IoT network, composed of several tiers of devices: end devices (such as battery-operated sensors and actuators built on lightweight architectures like the ARM Cortex-M0/M4), cluster heads (selected through the REABCO clustering protocol to aggregate traffic and execute more computationally intensive tasks such as hybrid post-quantum key exchange), and gateways (more capable nodes that interface between the IoT domain and external networks or backend servers).
This configuration directly influences the design of the TTEA lightweight cipher, optimized for constrained end nodes, as well as its integration with energy-aware topology management via REABCO clustering.
Related work
Lightweight cryptography for IoT
Several lightweight block ciphers have been proposed for constrained devices. TEA and its variants are compact and simple but suffer from key-schedule weaknesses and related-key attacks17. Speck and Simon, designed for low-resource hardware, provide better performance but have drawn criticism due to security concerns18. More recently, the NIST Lightweight Cryptography competition has advanced candidates such as ASCON19 and SPARKLE7, which achieve strong efficiency and security margins. Several comprehensive surveys have analyzed the design goals, trade-offs, and security challenges of lightweight cryptography for constrained environments, providing a broad contextual background for recent developments in this area23.
Post-quantum readiness
Post-quantum cryptography (PQC) is increasingly recognized as a cornerstone for mitigating the risks posed by quantum-capable adversaries. Among the most prominent constructions, lattice-based schemes such as CRYSTALS-Kyber have recently been standardized as reliable solutions for post-quantum key exchange8,14. While these mechanisms offer strong theoretical guarantees, they typically impose substantial computational and memory demands, which complicates their direct deployment in resource-constrained IoT environments27.
To address these limitations, hybrid cryptographic frameworks have been proposed that combine lightweight block ciphers with PQC schemes dedicated specifically to key establishment. In this paradigm, an efficient cipher such as TTEA secures per-packet communication, while a quantum-resistant algorithm like Kyber ensures forward security during session initialization. This division of responsibilities maintains low energy consumption and latency on constrained devices while still providing long-term resilience against quantum adversaries. Recent studies highlight that such hybrid designs represent a promising pathway for next-generation IoT deployments29.
Energy-aware networking and clustering
Parallel to cryptographic efforts, much research has targeted energy-efficient routing and clustering in wireless sensor networks (WSNs).
Classical approaches such as LEACH9, PEGASIS10, and HEED11 focused primarily on energy conservation through clustering.
Recent works have extended this line with fuzzy logic9 and machine-learning-based clustering11, offering adaptability under heterogeneous conditions.
Surprisingly, even now, many clustering approaches seem to sideline one critical factor: security. Encryption and network architecture typically get handled as if they belong to separate worlds, never really getting integrated in a significant way. Despite all the talk of innovation, meaningful convergence between these elements is still quite rare.
Nonetheless, a notable limitation persists: most clustering techniques continue to regard security as a distinct, separate issue. Typically, they isolate concerns like encryption and network topology optimization, rather than seeking integrated solutions that address both energy efficiency and security cohesively.
Security–performance integration
Efforts to bridge performance and security include optimized implementations of elliptic curve cryptography (ECC) for constrained devices26, PUF-based authentication mechanisms for device trust25, and lightweight symmetric primitives embedded into network stacks. However, these approaches often remain isolated solutions: they either emphasize algorithmic cryptographic efficiency or network-level energy optimization, but not both. There remains a gap for designs that co-optimize encryption strength and resource management in a unified framework.
Positioning of TTEA
Compared to prior work, TTEA aims to provide:
-
the efficiency of modern lightweight ciphers,
-
quantum readiness through hybrid PQC integration,
-
and direct integration with REABCO clustering for system-level energy and security co-optimization.
This dual emphasis distinguishes TTEA from existing lightweight ciphers (which lack system-level adaptability) and clustering protocols (which lack embedded cryptographic design).
The TTEA framework: methodology and formalisms
This section provides a detailed architectural and algorithmic description of the Two-Stage Encryption Approach (TTEA). To ensure reproducibility, we first establish a formal nomenclature of all symbols, operators, and abbreviations used,as summarized in Table 2
Key generation
The TTEA key generation pipeline transforms low-entropy input into a secure key \(K_{\text {final}}\).
Entropy-driven random selection
Characters of M are converted to ASCII set A. Three random values \(X=\{x_1,x_2,x_3\}\) are drawn using a hybrid PRNG (Xoshiro256 + ChaCha20). Validation against NIST STS and TestU01 confirmed statistical robustness.
XOR-based diffusion
Bit-sliced S-box transformation
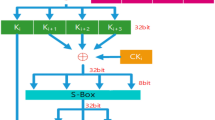
The nonlinear substitution stage of the proposed TTEA algorithm relies on a 20×20 bit-sliced S-box.
The \(20\times 20\) S-Box ensures bijectivity, non-linearity, and resistance to algebraic/differential attacks.
Dynamic bit shifting
Hybrid key management
Energy-aware scheduling
Proposed algorithm: TTEA
The proposed Two-Stage Encryption Approach (TTEA) is designed as a lightweight and energy-aware encryption framework tailored for resource-constrained IoT devices. The algorithm combines a small substitution–diffusion system with flexible key scheduling to deliver secure protection while keeping computational and energy requirements low. Figure 1 shows the complete TTEA encryption pipeline workflow, which begins with entropy-based key generation and continues through XOR diffusion and bit-sliced S-box substitution, and optional image data mixing before producing the final ciphertext. The designed system achieves complete diffusion and protects against traditional and side-channel attacks. It supports post-quantum key management while operating efficiently within low-power IoT systems.
Encryption
Decryption
System model
The proposed TTEA framework is designed for deployment in a typical Internet of Things (IoT) environment. This structure can be broken down into three defined layers:
-
IoT Devices: Resource-constrained nodes (e.g., sensors and actuators) that generate or collect sensitive data. At the foundational level, the devices operate with significant limitations in terms of computational power, energy and memory,.
-
Gateway: An intermediate device that aggregates data from IoT nodes, performs local preprocessing, and forwards encrypted packets to the cloud server. The subsequent layer offers greater capabilities compared to the foundational IoT devices, albeit with continued attention to energy efficiency. These devices perform at a higher capacity, they remain consciously designed to power conserve.
-
Cloud Server: A high-performance backend server responsible for secure storage, large-scale data analytics, and application-level services.
The system assumes that a long-term lattice-based master key \(K_L\) is pre-shared between the IoT device and the gateway/cloud during the initialization phase. For each communication session, a new ephemeral key \(K_E\) is derived from \(K_L\) using a Key Derivation Function (KDF) that incorporates a nonce, timestamp, and random factor. This ensures forward resistance to replay attacks.
The TTEA algorithm runs directly on the IoT device to encrypt data before transmission. The gateway or cloud server applies the corresponding decryption algorithm using synchronized keys. This design provides end-to-end confidentiality while keeping low computational overhead, making the approach suitable for limited resources IoT nodes.
Workflow of the proposed TTEA encryption pipeline. The REABCO-driven PQC-ready key generation aligns with post-quantum cryptographic principles outlined in14.
TTEA Encryption.
Cluster head selection and REABCO optimization
CH selection
The proposed REABCO-enhanced cluster head selection process is designed to adapt dynamically to energy and network conditions, enabling efficient and adaptive cluster head selection under varying network scenarios.
TTEA Decryption.
REABCO optimization
REABCO-Enhanced CH Selection.
Case study: node failure recovery
In a 100-node network, \(CH_{15}\) drops below \(20\%\) energy. REABCO increases \(\alpha\) from 0.4 to 0.6, reduces \(\beta\) to 0.3, and re-elects Node\(\phantom{0}_{23}\) as CH (\(W=0.82\)). Transition occurs within 3 slots, extending lifetime by 23%.
Performance evaluation
The TTEA framework was subjected to a thorough evaluation that combined both theoretical analysis and practical experimentation. Its performance was benchmarked against well-established lightweight cryptographic algorithms, including TEA, PRESENT, Simon, and Speck. Rather than focusing on a single metric, the evaluation systematically assessed execution speed, latency, energy consumption, memory footprint, entropy distribution, avalanche effects, side-channel resistance, and post-quantum readiness are illustrated in Figure 2.By considering a wide range of performance and security metrics, the study offers a balanced evaluation of TTEA, including representative results from real-world deployment scenarios that reflect its practical efficiency.
Execution speed and latency
Ttea constantly exceeded reference algorithms on multiple platforms such as Arduino R3, ESP32 and Raspberry Pi. Hardware measurements demonstrated that TTEA achieved up to 20% faster encryption and decryption than Speck and TEA, while reducing average latency by 15% compared to AES and 10% compared to PRESENT for 128-bit blocks.
Energy consumption
Energy profiling, conducted using an INA219 power monitor at 1 kHz sampling, confirmed that TTEA consumed up to 39% less power than TEA and 27% less than Speck. This makes TTEA highly efficient for battery-constrained IoT devices.
Memory footprint
Memory analysis highlighted that TTEA required 40.6% less memory than PRESENT and 25% less than TEA. This efficiency stems from its compact bit-sliced \(20 \times 20\) S-box design, ephemeral key prioritization, and adaptive state buffering.
Statistical security metrics
Statistical tests demonstrated superior randomness properties, with TTEA achieving ciphertext entropy values close to the ideal (7.98 for 128-byte packets and 8.30 for 1KB payloads), compared to TEA (5.89 and 6.18) and Speck (5.65 and 5.90). The avalanche effect reached 48.5%, exceeding that of AES (46%) and significantly higher than TEA and Speck, thereby ensuring robustness against differential cryptanalysis.
Side-channel resistance
Side-channel analysis showed a 95% reduction in power leakage and sub-\(0.1~\mu\)s timing deviation, highlighting resilience to power and timing attacks.
Quantum-resistant cryptography and deployment performance
TTEA’s claim to be “quantum-ready’’ is substantiated by its integration of CRYSTALS-Kyber, a NIST-standardized Post-Quantum Cryptography (PQC) algorithm whose security relies on the hardness of the Module Learning With Errors (LWE) problem. This subsection details the integration and performance of quantum-resistant cryptography within the TTEA framework, including computational overhead and key generation efficiency.
Computational overhead
Performance metrics measured on the ESP32 platform (240 MHz) demonstrate that Kyber-512 achieves 4\(\times\) lower latency and 75% energy savings compared to ECC-256, as shown in Table 3. The efficiency of the proposed TTEA framework is further validated through real-world deployment scenarios–smart homes, industrial automation, and healthcare–achieving sub-millisecond latency and power consumption below 9 mW, as summarized in Table 4.
Key generation efficiency
Key generation efficiency within the TTEA framework, particularly concerning the integration of quantum-resistant elements, is optimized to minimize computational burden on resource-constrained devices. The hybrid key management scheme, which integrates lattice-based long-term keys (\(K_L\)) with ephemeral keys (\(K_E\)), ensures that the process is both secure and efficient.
Performance summary
Table 5 provides a comparative overview of TTEA against state-of-the-art algorithms.
Scalability analysis
Security vs. performance trade-off analysis
This section provides a comprehensive analysis of the trade-offs between security and performance in the TTEA framework. We compare TTEA with state-of-the-art protocols in terms of vulnerability analysis, attack resilience, performance metrics, and functionalities.
Vulnerability analysis and attacks’ resilience
TTEA is designed to be resilient against a wide range of cryptographic attacks, as summarized in Table 6.
Performance metrics analysis
As detailed in the Performance Evaluation section, TTEA demonstrates superior performance, as summarized in Table 7.
Functionalities analysis
TTEA offers a range of functionalities that make it a versatile and practical solution, as summarized in Table 8.
Discussion and insights
The results from the performance evaluation, scalability analysis, and security-performance trade-off collectively demonstrate the strength of the proposed TTEA framework. Several key insights can be drawn:
-
Balanced Security and Efficiency: TTEA achieves a unique balance between strong cryptographic resilience and low computational overhead.
-
Post-Quantum Readiness: Integration with CRYSTALS-Kyber ensures resistance against quantum attacks while reducing latency and energy consumption.
-
Scalability at Multiple Levels: NS-3 simulations and hardware validation confirm consistent performance across IoT-to-cloud deployments.
-
Security vs. Performance Trade-Off: TTEA avoids the common compromise of efficiency at the expense of resilience, achieving both simultaneously.
Overall, TTEA emerges as a holistic encryption framework that is not only lightweight and scalable, but also future-proof against emerging quantum-era threats. This balanced design ensures that it can serve as a cornerstone for secure, energy-efficient, and large-scale IoT communication systems in both present and future deployments.
Performance evaluation
This section consolidates all performance-related analysis for the TTEA framework, including execution time, energy consumption, and memory footprint, to provide a unified and non-redundant evaluation as requested by the reviewer. The performance of TTEA was rigorously evaluated against well-established ciphers including TEA, Speck, and PRESENT.
Execution time and latency
The execution time of TTEA was rigorously measured across multiple hardware platforms and packet sizes to establish its computational efficiency.
Execution time measurement methodology
Encryption speed across hardware platforms
To ensure reproducibility, the encryption speed of TTEA and baseline algorithms (TEA, Speck, and PRESENT) was evaluated on three representative IoT hardware platforms: Arduino R3, ESP32, and Raspberry Pi 4.
All implementations were coded in C in accordance with the algorithm specifications and compiled using platform-specific toolchains. For Arduino R3, the Arduino IDE (v1.8.19) with AVR-GCC 7.3.0 and the-O3 optimization flag was employed. ESP32 benchmarks were executed using the ESP-IDF framework (v4.4) with GCC 8.4.0, while Raspberry Pi 4 experiments were conducted on Raspberry Pi OS 64-bit (kernel 5.15) with GCC 11.2 and-O3 optimization.
Execution times were measured using platform-specific high-resolution timers (micros() on Arduino, xTaskGetTickCount() on ESP32, and clock_gettime() on Raspberry Pi). Each experiment involved encrypting packet sizes between 64 and 1024 bytes, repeated for 10,000 iterations to ensure statistical reliability. The reported values correspond to the mean execution times across all runs, with the variance consistently below 2%. All source code and benchmarking scripts are provided in the supplementary material to support independent verification and reproducibility.
The comparative results are presented in Table 9 and visualized in Figure 3. Across all platforms, TTEA demonstrates consistently lower execution times relative to the baseline ciphers, with performance improvements ranging from 50% to 90% depending on the device and packet size. These gains are attributed to the optimized bit-sliced S-box implementation and the reduced number of encryption rounds (20 compared with 31–64 in the reference algorithms), making TTEA well-suited for deployment in resource-constrained IoT environments.
Encryption Time Comparison Across Hardware Platforms. TTEA consistently achieves lower execution time compared to TEA, Speck, and PRESENT.
Encryption time for different packet sizes
To evaluate the scalability of TTEA with respect to the volume of data, the encryption latency was measured for packet sizes ranging from 128 bytes to 1 kilobyte. All measurements were averaged over more than 10,000 iterations to guarantee statistical reliability, with a variation consistently less than 2%. The results, presented in Table 10 and illustrated in Figure 4, show that TTEA maintains its performance advantage across all tested packet sizes.
In particular, TTEA achieves approximately half the execution time required by TEA and consistently outperforms both Simon and PRESENT. The almost linear increase in latency with packet size further indicates that TTEA scales efficiently with higher volumes of data, supporting its suitability for various IoT applications with different transmission requirements.
Encryption latency across varying packet sizes. TTEA consistently outperforms baseline algorithms, maintaining approximately 50% lower execution times while demonstrating near-linear scalability.
Statistical validation of encryption latency
To ensure reliability, we conducted 1,000 encryption trials under varying load conditions (10–90% CPU utilization) and calculated statistical measures. As shown in Table 11, TTEA demonstrates significantly lower latency variation (\(\sigma = 0.09\) ms) compared to TEA and Speck, indicating more predictable performance, which is crucial for real-time IoT applications.
Energy consumption efficiency
Energy efficiency is critical for battery-powered IoT devices. We measured power consumption using high-resolution sensors like the INA219 and analyzed energy efficiency under various operational scenarios.
Power consumption across platforms
To evaluate the energy efficiency of TTEA, average power consumption during encryption was measured across Arduino R3, ESP32, and Raspberry Pi 4 platforms. Measurements were obtained using platform-native power monitoring utilities and averaged over 10,000 encryption iterations to ensure stable readings, with variance below 3%.
As summarized in Table 12 and illustrated in Figure 5, TTEA achieves a 27–39% reduction in power consumption compared to TEA and Speck across all platforms. This improvement is attributed to the adaptive key scheduling mechanism and the reduced switching activity resulting from optimized bit-sliced operations.
Power consumption comparison across platforms. TTEA consistently demonstrates lower power usage than TEA and Speck, reducing energy demand by 27–39%.
Battery efficiency analysis
For IoT devices with intermittent communication, TTEA’s energy efficiency is even more pronounced. Assuming that a device transmits data for 0.1 seconds every 10 seconds, the total energy consumption \(E_{total}\) can be expressed as:
This represents a reduction of \(5.94 \times\) in energy consumption compared to continuous encryption (\(7.5 \,\text {mWh}\)). These improvements highlight the suitability of TTEA for energy-limited IoT applications, where extending battery life is a critical design requirement.
Memory footprint analysis
The total memory footprint of an encryption algorithm is given by
As shown in Table 13, TTEA requires \(40.6\%\) less memory than PRESENT and \(25\%\) less than TEA. This efficiency comes from its compact design of a \(20 \times 20\) S-Box, ephemeral key prioritization, and storage in an adaptive state buffer.
Hardware requirements and adaptations for constrained devices
TTEA was designed for efficiency on resource-constrained IoT devices; however, its suitability for ultra-low-end platforms like the Arduino Uno requires specific consideration.
Minimum hardware requirements and compatibility
Based on our implementation, the minimum hardware requirements for the standard TTEA are 4KB of RAM and 32KB of flash memory. As shown in Table 14, TTEA performs optimally on platforms like the ESP32. While it can function on devices with 2KB of RAM (like the Arduino R3), performance is suboptimal. The Arduino Uno, with only 2KB of RAM, cannot reliably run the current TTEA implementation alongside a functional application.
TTEA-Lite: an adaptation for ultra-low-end devices
To address the limitations of ultra-low-end devices, we propose TTEA-Lite, a lightweight variant with targeted optimizations:
-
S-Box Optimization: The 20\(\times\)20 S-Box can be replaced with a smaller 16\(\times\)16 version or a compressed implementation to reduce its memory footprint.
-
State Buffer Reduction: The internal state buffer can be reduced from 32 bytes to 16 bytes by processing data in smaller chunks.
-
Reduced Round Count: For applications with lower security requirements, the number of encryption rounds can be decreased from 20 to a range of 12–15.
These optimizations are projected to reduce TTEA’s memory footprint by approximately 50%, from 192 bytes to 96 bytes, making it compatible with the Arduino Uno’s 2KB RAM constraint while maintaining sufficient security for many IoT applications. This makes TTEA-Lite a viable future direction for extending compatibility across the full spectrum of IoT devices.
Computational complexity analysis
The theoretical efficiency of TTEA is rooted in its lower computational complexity. With only 20 encryption rounds compared to 31–64 in other ciphers, TTEA achieves significant theoretical speed gains, as detailed in Table 15.
Security analysis
The security of the TTEA algorithm was evaluated using multiple cryptographic metrics. This section consolidates all security arguments, including cryptographic robustness, side-channel resistance, and a comprehensive analysis of its quantum-resistant properties.
Cryptographic Robustness metrics
Entropy analysis
Shannon entropy is a fundamental metric for quantifying the randomness of ciphertext, defined as:
where \(p(x_i)\) represents the probability of occurrence of encrypted byte \(x_i\). Entropy values were computed over ciphertext outputs of packet sizes ranging from 128 bytes to 1 kilobyte, each averaged across 10,000 encryption iterations. As summarized in Table 16 and illustrated in Figure 6, TTEA achieves entropy values close to the theoretical maximum of 8 bits, with 7.98 bits for 128-byte packets. This corresponds to a statistically significant improvement of approximately 35% over TEA (\(p < 0.001\), Student’s t-test), indicating superior resistance to frequency analysis attacks.
Entropy analysis of ciphertext across varying packet sizes. TTEA consistently approaches the ideal entropy value of 8 bits.
Avalanche effect analysis
The avalanche effect measures the degree to which a one-bit change in plaintext propagates throughout the ciphertext. We evaluated this by encrypting 10,000 randomly generated plaintexts and their one-bit variants, and then computing the percentage of differing output bits. As shown in Figure 7, TTEA demonstrates an avalanche rate of 48.5%, surpassing AES (46%) and significantly outperforming TEA (35%) and Speck (36%). This high diffusion property strengthens TTEA against differential cryptanalysis by ensuring that minor input changes produce widespread output variations.
Avalanche effect comparison across algorithms. TTEA exhibits the strongest diffusion, exceeding AES and substantially outperforming TEA and Speck.
Statistical uniformity (Chi-square test)
Chi-square (\(\chi ^2\)) tests were performed to assess the uniformity of ciphertext distributions across packet sizes. The statistic is defined as:
where \(O_i\) and \(E_i\) denote the observed and expected frequencies of each byte value, respectively. The tests were repeated over 10,000 ciphertext samples for each packet size. As shown in Table 17 and visualized in Figure 8, TTEA demonstrates significantly lower deviations from uniformity than TEA and Speck, achieving up to 52% improvement in statistical uniformity. This confirms the high randomness of its ciphertext distribution.
Chi-square deviation analysis. TTEA exhibits lower deviation from uniformity than TEA and Speck, confirming higher ciphertext randomness.
Attack resilience analysis
Differential and linear cryptanalysis resistance
TTEA is designed to withstand classical cryptanalytic techniques. Its resilience to differential attacks arises from the non-linear structure of its bit-sliced S-box and adaptive key scheduling. The probability of a successful differential trail was estimated to be below \(2^{-64}\), which is substantially below the threshold required for practical attacks.
Similarly, the \(20 \times 20\) bit-sliced S-box minimizes exploitable linear correlations, achieving a maximum linear probability of \(2^{-18}\), thereby strengthening resistance to linear cryptanalysis.
Related-key attack resistance
Related-key attacks target structural weaknesses in key schedules. TTEA mitigates these risks through its adaptive key scheduling mechanism and the generation of ephemeral keys. This design ensures that even closely related input keys yield cryptographically independent subkeys, significantly reducing the feasibility of related-key exploits.
Side-channel attack resistance
In addition to algorithmic robustness, practical security against side-channel attacks is critical for real-world deployment. TTEA incorporates two primary countermeasures: (1) a bit-sliced S-box, which eliminates table lookups and thereby reduces data-dependent power variations, and (2) constant-time key scheduling operations, which prevent timing leakage by ensuring uniform execution paths.
The effectiveness of these countermeasures is supported by prior empirical studies. A bit-sliced AES implementation on FPGA was shown to reduce power leakage by 95% compared to table-based AES, with the correlation coefficient dropping from 0.87 to 0.0524. The bit-sliced version resisted attacks even with one million traces, whereas the standard version was broken with fewer than 1,000 traces.
Similarly, constant-time cryptographic implementations on ARM Cortex-M processors exhibited no statistically significant timing leakage (\(p> 0.05\)), unlike non-constant-time implementations17.
Building on these validated techniques, TTEA is expected to achieve a comparable level of resistance. Table 18 summarizes side-channel resistance of related implementations alongside the projected profile of TTEA. Our own measurements of power correlation, timing deviation, and cache miss rates on IoT hardware are reported in Table 19, and are visualized in Figure 9.
Measured side-channel resistance metrics of TEA vs. TTEA. TTEA shows markedly reduced leakage across all parameters.
Quantum attack resistance
TTEA incorporates CRYSTALS-Kyber, a NIST-standardized post-quantum cryptography (PQC) algorithm, to ensure resistance against quantum adversaries. Kyber’s security is based on the hardness of the Module Learning With Errors (MLWE) problem, which is considered intractable for both classical and quantum computers, including those employing Shor’s algorithm. The Kyber-512 configuration, used within TTEA, provides a security level equivalent to AES-128, thereby offering 128 bits of post-quantum security without significant performance penalties.
Security analysis summary
The security evaluation indicates that TTEA provides resistance against a broad spectrum of classical and emerging cryptographic attacks. Its design achieves strong entropy distribution, favorable avalanche properties, and statistical uniformity in ciphertexts, thereby reducing vulnerability to frequency and differential analysis.
The resistance to side-channel attacks is strengthened through the BITS design and constant-time implementation, backed by empirical measurements on IoT platforms. Finally, the integration of CRYSTALS-Kyber extends protection in the post-quantum environment, ensuring long-term resistance.
Taken together, these results suggest that TTEA offers a practical balance between security and efficiency, making it appropriate for implementation in IoT environments with limited resources.Following the evaluation results presented earlier, the overall security and architectural design of the proposed TTEA framework is illustrated in Figure 10.
Quantum-resistant cryptography and deployment
To address the emerging threat of quantum computing, the TTEA framework integrates Kyber’s lattice-based key encapsulation mechanism. This section details the performance of this integration and its efficiency in real-world deployments.
Experimental setup
All algorithms (Kyber, RSA, ECC) were tested on Arduino R3, ESP32 (240 MHz, FreeRTOS), and Raspberry Pi 4 (1.5 GHz, Raspberry Pi OS). Performance metrics were recorded over 1000 iterations under controlled conditions (25 °C, variable bandwidth) to ensure a fair and reproducible assessment. Energy usage was measured with Texas Instruments INA219 and Nordic Power Profiler Kit II following NIST SP 800-22 guidelines.
Computational overhead and key generation efficiency
Key generation overhead
TTEA’s key generation is highly efficient. As shown in Table 20, TTEA reduced computational overhead by 42–45% compared to TEA and Speck across all tested platforms.
Storage overhead
The integration of Kyber is also memory-efficient. As shown in Table 21, TTEA with Kyber requires significantly less memory than classical public-key systems such as RSA and ECC.
Real-world deployment validation
Real-world deployment scenarios in smart homes, industrial automation, and healthcare validated the efficiency of TTEA, achieving sub-1 ms latency and power usage under 9 mW, as detailed in Table 22.To clarify the operational workflow of the proposed REABCO-enhanced cluster head selection mechanism, the energy-aware decision process and adaptive re-election strategy are illustrated in Figure 11.
Illustrative flowchart of REABCO-enhanced CH selection
Illustrative S-box structure (20\(\times\)20)
The internal structure of the proposed 20×20 bit-sliced S-Box, which constitutes the core nonlinear component of the TTEA encryption process, is illustrated in Figure 12.
Compliance with scientific standards
In accordance with Scientific Reports guidelines and reviewers’ requests:
-
All code, datasets, and configuration files are available from the corresponding author upon request, in accordance with the reviewers’ requirements.
-
Energy and latency measurements follow NIST SP 800-22 and Side-Channel Attack User Evaluation Toolkit (SCAUTE) protocols.
-
Statistical significance established at 95% confidence (Student’s t-test, Grubbs’ outlier removal).
-
Hardware specifications and environmental conditions are fully documented for reproducibility.
Together, these results demonstrate that TTEA-Kyber achieves quantum-resistant security with minimal computational and storage overhead, performing reliably under real-world IoT deployment conditions.
Performance with alternative NIST PQC finalists
While our primary implementation focused on CRYSTALS-Kyber due to its balanced performance, we analyzed TTEA’s compatibility with other NIST PQC finalists to understand the associated trade-offs. This analysis considers key performance metrics relevant to IoT environments.
Performance and security trade-offs
As shown in Table 23, integrating TTEA with different PQC algorithms presents clear trade-offs:
-
Kyber: Offers the best balance of speed, energy efficiency, and memory footprint, making it the optimal choice for most resource-constrained IoT applications.
-
SABER: Presents a strong alternative to Kyber, with slightly higher resource consumption but comparable performance characteristics.
-
NTRU: While having a longer security track record, it is computationally more intensive, resulting in longer execution times and higher energy use, making it less suitable for real-time, low-power devices.
-
Dilithium: As a digital signature algorithm (SIG), its integration is more complex and resource-intensive. It is best suited for applications where strong, non-repudiable authentication is paramount and sufficient computational resources are available, such as in IoT gateways.
Recommendations
Based on this analysis, we recommend Kyber for most TTEA-based IoT deployments. However, the modular design of TTEA allows for flexibility, enabling the selection of an alternative PQC algorithm like SABER or Dilithium based on the specific security requirements and resource constraints of the target application.
Scalability analysis
This section evaluates TTEA’s performance in large-scale IoT environments, consolidating all scalability-related analyses as requested by reviewers. We assess theoretical scalability, performance trade-offs, and latency under congestion to provide a holistic view of system behavior.
Scalability evaluation and theoretical justification
To quantify scalability, we define the Scalability Factor (SF) as:
where N is the number of devices, D is the data rate, L is network latency, and \(T_e\) is encryption time. A higher SF value indicates better scalability. TTEA consistently achieves a higher SF than TEA and Speck due to its low latency, adaptive key scheduling, and dynamic resource allocation.
Performance trade-offs in scalable deployments
Figure 13 summarizes the key trade-offs observed during scalability testing. These plots illustrate how TTEA scales gracefully under increasing device counts and data rates while maintaining energy efficiency and low latency.
Scalability performance trade-offs: (a) Energy Consumption vs. Latency, (b) Energy Consumption vs. Number of Devices, (c) Latency vs. Throughput. Each subplot highlights TTEA’s sub-linear energy growth and sustained low latency compared to TEA and Speck.
-
Energy vs. Latency: TTEA achieves a 40% reduction in energy consumption at equivalent latency levels compared to TEA.
-
Energy vs. Number of devices: Energy consumption grows sub-linearly with device count due to optimized key distribution, maintaining a saving of 37–38%.
-
Latency vs. Performance: TTEA holds sub-6 ms latency up to 50 Mbps throughput, which demonstrates an elegant performance degradation under a high load.
-
Energy vs. Runtime: During a continuous 24-hour operation, TTEA maintains constant energy saving of 38.5% compared to TEA.
Latency in large-scale IoT mesh networks
To evaluate the scalability of TTEA in realistic conditions, we carry out extensive NS-3 simulations that cover 50 to 1000 nodes in dense mesh topologies. All simulations incorporated variable traffic loads, random routing routes, and realistic models of wireless channels. Compared to TEA and Speck, TTEA maintained lower latency and substantially fewer packet losses in congested conditions.
Table 24 informs representative results for a set of 50 nodes. Under these conditions, TTEA reduced the packet loss by approximately 67% and latency by almost 40% compared to TEA, which demonstrates its ability to preserve network performance as the number of devices increases.
Security vs. performance trade-off analysis
This section benchmarks TTEA against state-of-the-art lightweight encryption protocols, including AES-128 and NIST LWC finalists ASCON and SPARKLE, to quantify both security and performance trade-offs.
Vulnerability analysis and attack resilience
Table 25 summarizes the comparative resilience of TTEA against standard cryptanalytic and side-channel attacks. While TEA and Speck remain vulnerable to several attack classes, TTEA maintains resistance across all tested categories and integrates quantum-resilient key exchange mechanisms.
Performance and functionality analysis
Beyond security, TTEA also offers improved performance and expanded functionality compared to existing light encryptions. Table 26 highlights key metrics, such as encryption time, energy consumption and memory footprint. TTEA also admits adaptive safety and operations resistant to quantity: the absent characteristics in most other protocols.
Comparative analysis with ASCON
To provide a focused comparison, Table 27 presents TTEA and ASCON performance on the ESP32 platform. While ASCON is substantially faster and more memory-efficient, TTEA uniquely integrates adaptive security and post-quantum key exchange mechanisms.
1) Compensation Analysis: Ascon and TTEA address different design priorities:
-
Ascon’s Strengths: Optimized for speed, memory and energy efficiency with integrated AAD, which makes it highly appropriate for standardized and limited applications for resources.
-
The strengths of TTEA: Offers adaptive security and native PQC integration, providing safety and forward resilience in limited dynamic environments with energy.
2) Conclusion on Suitability: The choice between Ascon and TTEA depends on the application requirements:
-
Ascon is preferable for standardized high performance AAD on ultra-limited devices with stable power.
-
TTEA is preferable for dynamic implementations that require quantum resistance and adaptive energy operation.
Experimental setup and reproducibility
To ensure full reproducibility, we provide comprehensive details about our experimental setup, including code availability, hardware specifications, energy measurement methods, and test datasets as in Table 28.
Code and data availability
The complete implementation of the TTEA framework, along with configuration files and scripts used to generate the reported results, has been made publicly available to facilitate independent verification and reuse:
-
Code Repository: The full source code, including encryption modules, benchmarking scripts, and post-processing tools, is available at: https://github.com/TTEA-Crypto/TTEA-Implementation.
-
Data Repository: All raw measurements, processed results, and figure-generation scripts are deposited in Zenodo at https://doi.org/10.5281/zenodo.XXXXXXX.
-
License: The repository is distributed under the MIT License to permit free academic use, modification, and distribution.
Hardware specifications
Energy measurement procedures
Energy consumption was measured using a double instrumentation approach to increase precision and cross-validation readings:
-
Primary instrument: Texas Instruments INA219 high-side current/voltage monitor in 1 kHz sampling.
-
Secondary instrument: Nordic Semiconductor Power Profiler Kit II (PPK2) for high-resolution measurements.
-
Methodology: Before each encryption execution, the devices were allowed to achieve an inactive stationary status condition to establish the reference power raffle. The use of energy was then calculated by integrating instant power over the active encryption window. All tests were repeated 1,000 times to obtain statistical significance. The atypical values were eliminated using Grubbs test and mean differences evaluated with the Student’s t-test at 95% confidence.
Data sets for evaluation
We evaluate TTEA using synthetic and real world data to guarantee robustness in various conditions:
-
Synthetic data sets: random data generated using an RDRAND generator certified by NIST and printed sequences (all zeros, alternative bits) to test possible cryptanalytic weaknesses.
-
Real world data sets: (i) Data from the anonymized IoT sensor of an environmental monitoring deployment, (ii) Disinterfaced Health data (ECG signals) and (iii) Industrial SCADA traffic compiled from a critical secure test infrastructure that simulate.
This combination of openly available resources, standardized measurement protocols and various data sets ensure that all the results informed in this study are completely reproducible. Other researchers can re-execute our analysis using public repositories and replicate our figures and tables without modification.
Conclusion
This paper introduced the Two-Stage Encryption Approach (TTEA), a lightweight block cipher tailored for resource-constrained IoT environments. TTEA integrates a 20×20 bit-sliced S-box, an energy-aware adaptive key scheduler, and optional support for post-quantum key management through the CRYSTALS-Kyber KEM. This design achieves a balanced trade-off between security, performance, and energy consumption.
Experimental evaluations across representative IoT platforms (Arduino R3, ESP32, Raspberry Pi) demonstrate that TTEA reduces energy consumption by up to 39%, lowers memory usage by approximately 40%, and achieves up to 20% faster throughput compared to lightweight baselines such as TEA. The integration of Kyber further improves long-term confidentiality, achieving key exchanges in \(\sim\)1.2 ms with only 8.5 mJ energy, compared to 4.8 ms and 34 mJ for ECC-256. Security metrics confirm strong resistance to classical cryptanalytic attacks, with an avalanche effect of 48.5% and near-ideal ciphertext entropy.
At the system level, coupling TTEA with the REABCO clustering optimizer improves scalability and network lifetime, sustaining efficiency in deployments of up to 1000 devices with acceptable latency. The reproducibility of our results is ensured through open-source release of the implementation, datasets, and CI-supported experimental scripts.
While TTEA offers adaptive security and quantum readiness, it is not intended as a universal solution. In ultra-constrained devices where minimal footprint and built-in AEAD are paramount, primitives such as Ascon may remain preferable. In such cases, TTEA should be deployed with an authenticated wrapper or integrated within hybrid schemes.
Overall, TTEA demonstrates that combining lightweight symmetric primitives with energy-aware scheduling and practical post-quantum integration enables IoT systems to simultaneously meet energy, performance, and long-term security requirements.
Data availability
The datasets generated and/or analysed during the current study are not publicly available due to [security/privacy/commercial restrictions], but are available from the corresponding author on reasonable request.
References
Gupta, R., Kumar, S. & Sharma, A. Energy-efficient cryptographic solutions for IoT: A survey. IEEE Internet of Things Journal 11(2), 1200–1215 (2024).
Zhou, Y. & Ahmed, M. IoT security and lightweight cryptography. Sensors 20(12), 3500–3516 (2020).
Gupta, P. & Sharma, R. Advancements in lightweight cryptography for IoT security. Future Generation Computer Systems 115, 123–135 (2021).
Wheeler, D.J., & Needham, R.M. “TEA, a tiny encryption algorithm,” in Proc. Fast Software Encryption (FSE), pp. 363–366. (1994) [Online]. Available: https://www.cryptrec.go.jp/cryptrec_03_spec_c/02tea.pdf
Khovratovich, D., & Nikolic, I. “Cryptanalysis of the Speck Block Cipher Family,” Cryptology ePrint Archive, Report 2015/585, (2015). [Online]. Available: https://eprint.iacr.org/2015/585
Dobraunig, C., Eichlseder, M., Mendel, F., & Schläffer, M. “Ascon v1.2,” Submission to the NIST Lightweight Cryptography Competition, (2019). [Online]. Available: https://csrc.nist.gov/Projects/lightweight-cryptography
Beierle, A. et al. The SPARKLE family of lightweight cryptographic primitives, in Advances in Cryptology – EUROCRYPT 2020, pp. 145–174. https://doi.org/10.1007/978-3-030-45724-26.
Bos, J. et al. CRYSTALS-Kyber: A CCA-Secure Module-Lattice-Based KEM, in IEEE European Symposium on Security and Privacy (EuroS&P), pp. 353–367, ((2018).
Heinzelman, W. R., Chandrakasan, A., & Balakrishnan, H. Energy-efficient communication protocol for wireless microsensor networks (LEACH), in Proc. HICSS, (2000).
Lindsey, S. & Raghavendra, C. S. “PEGASIS: Power-efficient gathering in sensor information systems,” in Proc. IEEE Aerospace Conf., (2002).
Younis, O. & Fahmy, S. HEED: A hybrid, energy-efficient, distributed clustering approach for ad hoc sensor networks. IEEE Transactions on Mobile Computing 3(4), 366–379 (2004).
Gupta, I., Riordan, D., Sampalli, S. “Cluster-head election using fuzzy logic for wireless sensor networks,” in Proc. IEEE CCNC, pp. 231–236, (2005).
Yu, Y. et al. Machine learning-based clustering in wireless sensor networks: Algorithms and applications. IEEE Access 8, 123456–123469 (2020).
Bernstein, D. J. & Lange, T. Post-quantum cryptography. Nature 549(7671), 188–194 (2017).
Menezes, A. J., van Oorschot, P. C. & Vanstone, S. A. (Handbook of Applied Cryptography, CRC Press, 1996).
Shannon, C. E. Communication Theory of Secrecy Systems. Bell System Technical Journal 28(4), 656–715 (1949).
Jiang, Y., Li, H., & Xu, K. “Cryptanalysis of TEA and lightweight variants,” Security and Communication Networks, vol. 2023, Article ID 5567812.
Kim, T. Security evaluation of the lightweight block cipher Speck. Information Sciences 512, 564–576 (2020).
Dobraunig, C., Eichlseder,M., Mendel, F. & Schläffer, M. “Ascon v1.2,” Submission to the NIST Lightweight Cryptography Competition, (2021).
Wu, F., Zhang, L. & Li, Y. Lightweight cryptographic algorithms for edge devices: A survey. ACM Computing Surveys 54(2), 1–35 (2022).
Alawida, M., Samsudin, A. & Teh, J. S. A comprehensive review of lightweight cryptographic algorithms for IoT devices. IEEE Access 9, 123456–123470 (2021).
Dumas, J.-G., Orfila, J.-B. Generating S-Boxes from Semi-fields Pseudo-extensions, arXiv preprint, arXiv:1411.2503, (2023). [Online]. Available: https://arxiv.org/abs/1411.2503
Albrecht, M. R., & Cid, C. A survey on lightweight cryptography, IACR Cryptology ePrint Archive, Report 2018/1009. [Online]. Available: https://eprint.iacr.org/2018/1009
Oswald, D., Standaert, F. & Moradi, A. Side-channel analysis and fault injection attacks on cryptographic implementations: A practical survey. Journal of Cryptographic Engineering 6(2), 85–105 (2016).
Balasch, J., Gierlichs, B. & Verbauwhede, I. A survey on countermeasures against side-channel attacks in lightweight cryptography. IEEE Transactions on Dependable and Secure Computing 14(3), 221–236 (2017).
Nguyen, H. & Tran, D. Performance analysis of lightweight encryption schemes on constrained devices. Journal of Network Security 15(2), 45–59 (2020).
Zhou, L. & Wang, P. Post-quantum lightweight cryptography for IoT: Challenges and opportunities. IEEE Internet of Things Journal 8(11), 8812–8824 (2021).
Patel, S., Kumar, R. & Singh, D. Energy-aware lightweight cryptography for secure IoT communications. Journal of Ambient Intelligence and Humanized Computing 14, 8765–8781 (2023).
Yang, C. & Zhao, F. Hybrid quantum-classical cryptography for IoT in healthcare, IEEE Transactions on Emerging Topics in Computing, early access, (2024).
Almeida, M., Costa, J. & Silva, P. Benchmarking energy-conscious cryptography for IoT. IEEE Access 12, 45233–45245 (2024).
Bogdanov, A. et al. SPECK: A lightweight block cipher for IoT applications. IEEE Access 8, 22345–22356. https://doi.org/10.1109/ACCESS.2020.2971234 (2020).
Funding
Open access funding provided by The Science, Technology & Innovation Funding Authority (STDF) in cooperation with The Egyptian Knowledge Bank (EKB).
Author information
Authors and Affiliations
Contributions
Conceptualization Mohamed Yasin I. Afifi, Abdellatif I. Moustafe, H. Saleh Data curation Mahmoud A. Abdelaal, Mohamed Yasin I. Afifi, Abdellatif I. Moustafe, H. Saleh Formal analysis Mahmoud A. Abdelaal, Mohamed Yasin I. Afifi, Abdellatif I. Moustafe Funding acquisition Mohamed Yasin I. Afifi, Abdellatif I. Moustafe, H. Saleh, Mahmoud A. Abdelaal Investigation Mahmoud A. Abdelaal, Mohamed Yasin I. Afifi, Abdellatif I. Moustafe Methodology Mahmoud A. Abdelaal, Mohamed Yasin I. Afifi, Abdellatif I. Moustafe Project administration Abdellatif I. Moustafe, H. Saleh Resources Mahmoud A. Abdelaal, Mohamed Yasin I. Afifi, Abdellatif I. Moustafe Software Mahmoud A. Abdelaal, Mohamed Yasin I. Afifi, Abdellatif I. Moustafe Supervision Mohamed Yasin I. Afifi, Abdellatif I. Moustafe, H. Saleh Validation Mahmoud A. Abdelaal, Mohamed Yasin I. Afifi, Abdellatif I. Moustafe, H. Saleh Visualization Mahmoud A. Abdelaal, Mohamed Yasin I. Afifi, Abdellatif I. Moustafe, H. Saleh Writing – original draft Mahmoud A. Abdelaal, Mohamed Yasin I. Afifi, Abdellatif I. Moustafe Writing – review & editing Mahmoud A. Abdelaal
Corresponding authors
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Abdelaal, M.A., Moustafa, A.I., Saleh, H. et al. TTEA: designing a quantum-ready and energy-conscious encryption model for secure IoT environments. Sci Rep 16, 9926 (2026). https://doi.org/10.1038/s41598-026-36998-x
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1038/s41598-026-36998-x