Abstract
With the rapid development of smart cities and intelligent vehicles, the communication scale in Vehicular Ad-Hoc Networks (VANETs) is expanding significantly. Simultaneously, due to the low latency, and security requirements of the Internet of Vehicles (IoV), there is an increased demand for the performance of vehicle access authentication and key agreement protocols. Traditional identity authentication and key agreement protocols less frequently consider the impact of efficiency, and they use complex computations, which result in increased communication costs and reduced efficiency. As a result, these protocols are no longer suitable for resource-constrained VANETs applications. The Semiconductor Superlattice Physically Unclonable Function (SSL-PUF) which belongs to strong PUF has attracted significant attention from scholars worldwide and prompting extensive research into the applications of cryptography. This paper proposes a lightweight identity authentication and a group key agreement scheme based on SSL-PUF for vehicle–road coordination, providing information-theoretical security proofs. Finally, performance comparisons, considering communication load and computational costs, demonstrate that the proposed scheme offers significant advantages in both security and lightweight characteristics, and holds considerable significance for the security requirements in vehicle–road coordination scenarios.
Similar content being viewed by others
Introduction
With the vigorous development of network technology, the Internet of Things has gradually entered various industries, and concepts such as smart cities, smart transportation, smart homes, and smart healthcare have emerged1,2. Among them, the intelligent transportation system utilizes advanced information technology, sensor technology, network communication technology, electronic control technology, etc., and is comprehensively applied to the traffic management system, which can effectively improve the safety of the transportation system, reduce the incidence of accidents, and achieve efficient management of urban traffic3,4. As an important component of intelligent transportation systems, VANETs are mainly composed of three components: Trusted Authority (TA), Roadside Unit (RSU), and Onboard Unit (OBU)5,6.
In the application scenario of vehicle–road collaboration, VANETs have forever changed the intelligent transportation system through the connection of V2X (Vehicle to Everything). Traffic safety, congestion and road connections depend on the ability of the car to interact with each other and its surroundings. V2X communication has many benefits7. However, since VANETs are exposed to open networks, it is possible to receive various internal and external cyber-attacks at any time10, and users are very vulnerable to message modification, tampering, counterfeiting, signature forgery and side channel attacks8. In addition, VANETs are characterized by rapid changes in the network topology graph. Therefore, how to ensure the security of vehicle networking system communication in a complex and high-speed changing vehicle networking environment will become the primary problem to be solved in the future development of smart transportation11,12.
To enhance the security of VANETs, researchers have integrated identity authentication technology into these networks. This approach safeguards the privacy and security of both communicating parties through the implementation of the Authentication Key Agreement (AKA) protocol13. The AKA protocols enable communication parties to authenticate each other’s identities, simultaneously generating session keys and constructing secure encrypted channels, which can ensure the privacy and security of information during vehicle operation. However traditional AKA protocols are mainly divided into schemes based on Public Key Infrastructure (PKI) or Identity Based Cryptography (IBC), among which the most widely used is PKI based authentication protocol14.
However, identity authentication schemes that utilize Public Key Infrastructure (PKI) mechanisms often depend on certificate management authorities for the distribution and administration of digital certificates. This reliance introduces complex management challenges, escalates resource expenditures, and results in diminished efficiency during key agreement processes. Identity authentication schemes based on IBC often require multiple bilinear pairing operations and communication interactions at each authentication terminal, which can result in longer delays in the authentication key agreement process15. Due to the characteristics of low latency, heterogeneity, and limited resources of the Internet of Vehicles (IoV)16,17, and vehicles have the demand for high-speed mobility and periodic broadcasting of safety messages in the IoV, therefore, higher requirements have been put forward for the communication, computing, and storage costs of vehicle identity authentication18. The above solutions have the problem of not being able to balance efficiency and security. Vehicles are vulnerable to various security threats, including replay attacks, identity forgery attacks, etc. How to achieve secure key agreement in resource-constrained IoV devices has become an urgent problem.
The emergence of physical unclonable function (PUF)19,20 can effectively solve the problem that efficiency and security cannot be considered. SSL-PUF is a typical time domain strong PUF, and its CRP number expands exponentially with the increase of the length of the challenge. Even if an attacker masters many CRPs, it is impossible to predict the response signal corresponding to unknown challenge signals, and the interface of its challenge response is not limited (i.e., the attacker can access the PUF at any time when the user is not using it). At present, SSL-PUF has been widely accepted as a basic security primitive and is mainly used in random number generators and identity authentication9. Superlattice has the characteristics of unclonability, stability, uniqueness and unpredictability. Unclonability is the fundamental guarantee for the PUF to realize security19. Using physical entities as unique authentication and identification is the most basic application method of PUF, which is exactly the same as the idea of authenticating based on human biometrics (fingerprints and iris, etc.). SSL-PUF is lightweight and high security, does not require additional resources and only runs when needed. It not only provides physical security, but also can operate conveniently and efficiently in resource-constrained devices, bringing new solutions to key generation and key storage problems. As a representative time-domain strong PUF, its CRP space expands exponentially with increasing challenge length. This exponential growth ensures computational infeasibility of predicting responses to unknown challenges, even when attackers possess numerous CRP samples. Currently recognized as a fundamental security primitive, SSL-PUF has gained widespread acceptance, particularly in random number generation and identity authentication applications.
Additionally, our main contributions are as follows:
-
1.
SSL-PUF is introduced to implement authentication and key agreement scheme in VANETs, which is a strong PUF and does not need to store keys. The proposed scheme achieves approximately 75% reduction in communication latency. while providing information-theoretical security.
-
2.
We propose an SSL-PUF-based identity authentication scheme for OBUs. By combining the inherent uniqueness of SSL-PUF with fuzzy extractor, this scheme enables the Trusted Authority (TA) to perform both unique identification and trusted authentication without requiring pre-shared keys.
-
3.
We propose a key agreement scheme based on SSL-PUF. The proposed scheme enables information-theoretically secure key agreement among multiple OBU terminals integrated with SSL-PUFs, mediated by the TA. By disclosing only helper data and initial challenge over public channels, the solution is particularly suitable for VANETs scenarios that are highly sensitive to latency and communication overhead.
Related work
Research on identity authentication in IoV
In response to security requirements, many scholars have conducted research on privacy protection and identity authentication issues in the IoV and proposed many privacy protection identity authentication schemes. In 2005, Raya et al.21 proposed an anonymous certificate authentication scheme based on a public key infrastructure system. However, this scheme requires a large number of public and private key pairs and digital certificates to be preloaded on the vehicle nodes, resulting in significant storage overhead. In 2007, Calandriello et al.22 proposed to minimize the number of pseudonymous signatures while ensuring security, and reducing the storage overhead of digital certificates. However, this scheme lacks traceability and cannot resist replay attacks. To compensate for the shortcomings of PKI authentication schemes, Zhang et al.23 constructed an identity based conditional privacy protection scheme that reduces storage and communication overhead. However, this scheme has a key custody issue. Once the master key of the trusted institution is leaked, it will threaten the communication security between the RSU and the vehicle. Zhang et al.24 proposed a novel privacy protection authentication scheme for VANETs. Subsequently, Lee and Lai25 claim that this scheme24 is not efficient in resisting replay attacks and denial of service attacks. In addition, they proposed a key agreement scheme using bilinear pairing to provide more effective security features. However, Bayat et al.26 pointed out that scheme25 is susceptible to impersonation attacks. Bayat et al.26 designed an improved key agreement scheme. This scheme performs computationally complex bilinear pairing operations during authentication, while also introducing key custody issues. Luo et al.52. proposed an efficient blockchain-assisted cross-domain authentication mechanism for bandwidth-constrained wide-area IoT scenarios. This scheme significantly improved the efficiency and scalability of cross-domain authentication by building a multi-chain parallel blockchain architecture and designing a lightweight consensus algorithm. Although the consensus communication volume has been optimized, the design of multi-round message interaction may still increase the complexity of the system when the node scale is expanded, which is not conducive to the deployment and maintenance of large-scale heterogeneous devices. Lin et al.53. proposed a blockchain-assisted certificateless key negotiation protocol for the Internet of Vehicles scenario in intelligent transportation systems. The protocol combines blockchain technology with certificateless public key cryptography, ensuring secure communication while avoiding key escrow and certificate management issues in traditional PKI. However, these protocols involve a lot of elliptic curve cryptographic operations, which, although relatively efficient, still imposes a computational burden on resource-constrained onboard devices. Cui et al.46. proposed an efficient message authentication scheme for VANETs based on edge computing. This scheme introduces a collaborative verification mechanism utilizing edge nodes and employs elliptic curve cryptography to replace bilinear pairing operations, significantly improving message processing efficiency in high-density traffic scenarios. However, the scheme relies on centralized management of temporary keys by edge nodes, which may introduce single-point failure risks. Additionally, it does not address the load balancing issue of edge nodes in dynamic network topologies. Zhong et al.47. presented an identity-based broadcast encryption scheme tailored for key distribution in VANETs. By enabling single-time encryption to generate fixed-length ciphertexts for multiple vehicles, the scheme effectively reduces information redundancy. Nevertheless, the number of pairing operations in its encryption and decryption phases grows linearly with the group size, leading to a sharp increase in computational overhead during group expansion. This makes it challenging to meet the efficiency requirements of resource-constrained vehicles. Hong Zhong et al.48 addressed the efficiency bottleneck of the TA in V2I communications within VANETs by proposing an optimized broadcast encryption scheme. The framework leverages bilinear pairing and hash functions to enable the TA to broadcast encrypted messages to multiple vehicles in a single operation. However, the computational burden of bilinear pairing operations remains significant.
All the aforementioned schemes exhibit the drawbacks of high computational costs; in contrast, our proposed scheme offers significant advantages in this regard. Our approach is lightweight than public key-based schemes and provides enhanced security compared to symmetric key-based methods, which require prior key establishment.
Research on identity authentication based on PUF
PUF is a physical cryptographic technique based on the intrinsic mechanisms of physical devices, with a mature research system. It introduces physical entities into the perspective of cryptographic applications for research and has formed a relatively mature theoretical research system for physical cryptography.
In 2012, Maes et al.27 first proposed a protocol for key generation and storage using PUF. NXP Corporation uses SRAM PUF to store keys in smart card products, but weak PUFs have been reported to pose significant security threats28. Brzuska et al.29 were the first to consider PUF based key distribution protocols, but they only considered a key agreement between servers and devices, assuming a strong PUF model. Beckmann et al.30 proposed a decentralized key exchange protocol based on public PUF (PPUF), but it requires exchanging a large amount of data and has a high computational cost, making it difficult to apply in resource constrained scenarios.
Zhang Zheng et al.31 proposed using PUF to replace the vulnerability of private keys and passwords in the Kerberos protocol, but this scheme only focuses on authentication and does not provide a corresponding key exchange protocol. Aman et al.32 implemented session key exchange for IoT terminal nodes equipped with PUFs through a trusted third-party server. This protocol increased the time for message exchange in exchange for zero storage of the terminal, resulting in multiple rounds of mutual authentication required for the complete protocol operation. Chuang et al.33first proposed a PUF based authentication key exchange protocol in the context of the Internet of Things, and proved its security in the random oracle model. However, the CDH problem resulted in high computational resource consumption. Pehl et al.34 proposed a key distribution protocol for terminal questioning based on Multi PUF, but did not provide a specific PUF model and detailed security analysis. In reference35, PUF was combined with PKC on elliptic curves, and the private key was recovered with the help of PUF to achieve authentication and key exchange between nodes. However, completing this protocol requires 16 rounds of elliptic curve point multiplication, and the computational cost of the protocol is difficult to accept in lightweight devices. In reference36, Zheng et al. proposed a PUF based terminal key exchange protocol, but only for point-to-point scenarios. In 2024, Bhattarai et al.55. introduced a lightweight, anonymous, application-aware authentication and key agreement protocol for the Internet of Drones. The scheme simplifies computational processes using PUF, XOR operations, and hash functions, thereby reducing computational overhead. However, it lacks formal security proofs.
After inputting a challenge Ci into PUF, a stable response Ri can be obtained. The combination of challenges and responses (Ci, Ri) is called challenge-response pairs (CRP). According to the different quantities of CRP, different types of PUFs are classified into strong PUFs and weak PUFs. Strong PUFs have an exponentially complex one-way function input–output relationship, supporting enough of CRPs which grow exponentially with the size, while weak PUFs only provide a limited number of CRPs.
SSL-PUF is a typical time-domain strong PUF37. From the perspective of material structure and physical mechanism, the key space of semiconductor SSL-PUF can reach 24500×50, with a huge number of challenge-response pairs, which can be used for typical cryptographic applications such as key generation38. At present, SSL-PUFs have been widely accepted as basic security primitives, mainly used in random number generators, identity authentication, peer-to-peer key distribution technology, etc.39,40. However, in the diversified communication network scenario, peer-to-peer key distribution can no longer meet the high concurrency interaction needs.
Chen et al.41 proposed to incorporate the physical function characteristics discovered in superlattice devices into the research under the framework of PUF cryptography theory. Wu Han42,43 introduced the theoretical framework of PUF to analyze the inherent security mechanism and cryptographic application modes of superlattice devices, and proposed the physical mechanism analysis model, cryptographic characteristic detection and evaluation method for superlattice devices, which lays the theoretical foundation. Xu Liwei38 proposed a set of access authentication and key distribution schemes based on universal SSL-PUF devices and twin devices for the application scenarios of the Space-Air-Ground Integrated Network (SAGIN).
PUF based identity authentication uses pre-shared CRP between the device and server to achieve identity authentication and key agreement. The server has restored a large amount of CRP. During the authentication process, the same challenge data is input to the PUF device and server, and the server uses the challenge data as an index to retrieve the corresponding response data. The PUF will generate response data that is consistent with the server-side, and the two will be compared to achieve identity authentication. A strong PUF which response data can be used as a key or derived to generate a completely consistent key for key agreement. CRPs need to be securely stored on the server to ensure that only the server can access them. Only by obtaining the physical device can the corresponding data be obtained. Security is based on the physical device, and the unclonability and unpredictability of PUF ensure that attackers cannot forge or guess to obtain key data.
The only difference is that the superlattices are analog devices, and the response signal obtained from the same challenge signal will have slight differences each time. Therefore, it is necessary to use fuzzy extraction techniques to eliminate differences in the superlattice response data and ensure the uniqueness of the output response data. Fuzzy extractor (FE) was proposed by Dodis et al. in 2004. It generally includes two parts: Information Reconciliation (IR) and Privacy Amplification (PA)44. The IR process is used to correct the deviation of analog signals and generate error correction codes; In the PA process, sufficient entropy was extracted to generate the key.
Figure 1 shows the principal diagram of the key agreement for SSL-PUF. From the figure, the same challenge signal c is given to both the SSL-PUF and the authentication server. Under the stimulation of challenge signal c, the SSL-PUF generates a response signal r, which undergoes BCH encoding to generate an error correction code u, and finally generates a secret key K through a PA process.
The principal diagram of the key agreement for universal superlattice devices38.
The authentication server receives the challenge signal c and error correction code u from the superlattice device. Firstly, find the response data \(r^{\prime}\) corresponding to the challenge signal c in the locally pre stored CRPs by looking up the table. The response data here is \(r^{\prime}\), which participates in the BCH decoding process together with the error correction code u. With the help of error correction code u, error correction decoding is completed. Finally, after the PA process, we can get the secret identical key K.
There are two key points to focus on in Fig. 1: Firstly, the error correction code u can be sent through a public channel without a special secure channel, which can greatly reduce the management complexity of key agreement; Secondly, the challenge signal c cannot be reused, and the authentication server needs to be properly marked and judged to avoid replay attacks.
In summary, SSL-PUF has not yet been applied in the scenario of IoV, and the existing key agreement solutions cannot balance the relationship between privacy protection and costs.
Results
System model
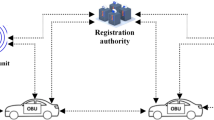
In the vehicle road collaboration application scenario, the system model contains three components: Trusted Third-Party Agent (TA), Roadside Unit (RSU), and Vehicle. Figure 2 shows the system model of vehicle road collaboration.
-
1.
Trusted Third Party Agent (TA): TA is the central authority for identity verification, responsible for registering and verifying vehicles, and storing confidential information such as CRP of other entities. TA has the highest communication and computing capabilities required to verify a large number of RSUs and vehicles. The SSL-PUF used in the vehicle needs to complete the registration of the corresponding CRP in TA. We believe that TA is completely trustworthy here and will not be attacked.
-
2.
Roadside Unit (RSU): RSU is the central point of communication between TA and vehicles, responsible for forwarding communication between them. RSU is connected to TA through a public communication channel. All RSUs are located on the roadside, so all vehicles can easily exchange information with TA through RSUs. In addition, RSU is responsible for data collection and distribution, edge computing processing.
-
3.
Vehicles: Each vehicle is integrated with an onboard unit (OBU) and equipped with SSL-PUF as the unique physical identifier for that terminal. The vehicle can communicate with TA through RSU with the help of OBU. In the V2I environment, OBU shares information with TA through RSU. OBU is attached to the vehicle, storing identity information and the actual identity of the vehicle to perform encryption functions.
System model of vehicle road collaboration.
Security assumption
Assuming that TA is in a completely trusted environment, CRPs for all vehicles support safe storage and use. All vehicles implement the registration process in a secure channel environment and assume that the RSU is completely trusted. Assuming that the attacker has the attack capability in the Dolev-Yao attack model, that is, the attacker can interact with legitimate participants and attack the system, can initiate a dialogue with the vehicle, RSU, and TA, can obtain any information in the process of protocol interaction, know the details of the communication protocol, and have the ability to listen, modify or terminate the interaction protocol.
Based on the above security assumptions, the security objectives of this protocol are as follows:
-
(1)
Identity authentication: TA supports the identity authentication of vehicle OBU;
-
(2)
Key agreement: the access authentication scheme can realize the vehicle key agreement;
-
(3)
Confidentiality of messages: users who are not authenticated successfully and have access to the group cannot obtain messages within the group;
-
(4)
Resist common attacks and forward security: access authentication can resist counterfeiting attacks, replay attacks, man in the middle attacks, and other common attacks. Even when SSL-PUF devices are out of control, the protocol can maintain forward security.
Our proposed protocol
In this section, an identity authentication and key agreement scheme based on SSL-PUF is proposed for vehicle road collaboration scenarios. The symbols used in this paper are described in Table 1.
-
Registration phase
Vehicles Vi (i = 1, 2,…, n) integrate OBU and are equipped with SSL-PUF universal device to achieve session key agreement without using asymmetric keys or preshared keys. RSU is responsible for establishing group communication within its communication range and acting as a relay communication, forwarding nonsensitive auxiliary information transmitted between the vehicle OBU and TA. Further, achieve key agreement between vehicles. The scheme is divided into two parts: vehicle registration phase, vehicle access authentication, and key agreement phase.
Vehicle registration is conducted over a secure channel and is unable to be attacked by attackers. TA registers CRPs for each PUF, i.e. stores a certain amount of CRPs for each PUF on the TA server. Taking the registration of vehicle V1 as an example, the specific registration process is shown in Fig. 3.
-
(1)
Vehicle V1 sends a registration Request and its unique identity IDV1 to TA;
-
(2)
TA verifies the uniqueness and legality of IDV1. After passing the verification, TA selects a random number cstart as the starting point for the challenge and stores it in the database. Then set challenge c1 = cstart and sends it to vehicle V1;
-
(3)
Vehicle V1 stores c1 as the starting point for the challenge. V1 uses c1 to challenge the SSL-PUF, and obtains the response r, then, calculates a new challenge c2 = Hash (c1). Next, V1 use c2 to stimulate the SSL-PUF again and obtains the new response r. Repeat this step N times, where N is the number of CRPs registered for each on-board OBU terminal, until N groups of CRPsare obtained. Finally V1 sends the response CRPs to TA;
-
(4)
After receiving the CRPs, the TA calculates the index value Hash (IDV1 ||c1) corresponding to each group of CRPs and saves (Hash (IDV1 || c1), r) to the database. This step is repeated N times until all N groups of CRPs are successfully stored.
The vehicle registration process.
Finally, vehicle V1 completes registration. TA stores the vehicle ID, initial value of challenge signal c1, and CRPs of N groups of vehicles in the database. The vehicles also store the initial value cstart of the challenge signal. After each authentication, update the challenge c1 = Hash(c1) and delete the CRPs that have been used by TA. Note that TA stores (Hash(IDV1 || c1),r) instead of the common c1, to ensure forward security. Even if vehicle V1 loses control, the attacker can obtain the superlattice device SSL, but they cannot reverse deduce c1 from the (Hash(IDV1 || c1),r) stored in TA, so they cannot obtain the corresponding response r through the SSL-PUF.
-
Vehicle access authentication and key agreement phase
Whether a vehicle can enter an RSU grouping is determined by the grouping list preset by the RSU to the TA in advance. When the TA confirms the identity of the vehicle and the information of the vehicle is on the RSU group list, it enters the key agreement phase. The group key K of RSU is also preset by the RSU to the TA in advance. The main process of vehicle access authentication and key agreement is as follows. Take vehicle Vi (i = 1, 2,…, n) as an example:
Vehicle access authentication phase:
-
(1)
Vehicle Vi reads the challenge starting point \(c_{start}\) locally, sets the challenge \(c_{i} = c_{start}\), and updates the challenge starting point \(c_{start} = Hash(c_{start} )\) at the same time. And get the current time Timei. After using \(c_{i}\) to stimulate PUFVi, the response r is obtained. The error correction code \(u_{i}\) is generated through BCH encoding link, and then the key KCi is generated through the security enhancement link, and then generated \(m_{i} = ID_{Vi} ||c_{i} ||Time_{i} ||u_{i}\), \(Hmac_{{K_{{Ci}} }} (m_{i} )\). Vehicle Vi sends {\(m_{i}\), \(Hmac_{{K_{{C_{i} }} }} (m_{i} )\)} to RSU. RSU forwards {\(m_{i}\), \(Hmac_{{K_{{C_{i} }} }} (m_{i} )\)} to TA.
-
(2)
Firstly, TA checks Timei to prevent replay attacks. Then calculate \(I_{i} = Hash(ID_{Vi} ||c_{i} )\). Use IDVi to find the registered CRP list, query the PUF response r corresponding to Ii, recover the key KCi with the help of an error correction code \(u_{i}\), verify \(Hmac_{{K_{{C_{i} }} }} (m_{i} )\) with KCi to verify the true identity, and determine whether the vehicle can join this group. If failed to pass the identity authentication, the key agreement service will be rejected. If pass the identity authentication, then enter the key agreement phase.
Key agreement phase:
-
(1)
Helper data generation phase: Calculate \(c_{i} = Hash(c_{i} )\), \(I_{i} = Hash(ID_{Vi} ||c_{i} )\), and TA retrieves the response corresponding to each PUF stimulus based on the registered CRP information, specifically \(r = CRP_{Vi} (I_{i} )\). Subsequently, TA generates a physical random number wAB of length Nk from the integrated random number generator, and selects an error correction code to encode the physical random number \(O = encode_{i} (w_{AB} )\), resulting in the codeword \(O\). The response r from the PUF is utilized to mask the codeword \(O\), yielding the publicly accessible auxiliary file hi, where \(h_{i} = O \oplus r\). \(m_{i}{\prime} = h_{i} ||Time_{i}\) and \(Hmac_{{K_{{C_{i} }} }} (m_{i}^{\prime } )\) are transmitted to vehicle Vi via the RSU.
-
(2)
Vehicle Vi response recovery phase: Vehicle Vi initially verifies Timei to avert replay attacks and verifies \(Hmac_{{K_{{C_{i} }} }} (m_{i}^{\prime } )\). Subsequently, it sets the challenge \(c_{i} = c_{start}\) and simultaneously updates \(c_{start} = Hash(c_{start} )\). After stimulating PUFVi with \(c_{i}\), a response \(\overset{\lower0.5em\hbox{$\smash{\scriptscriptstyle\frown}$}}{r}\) is obtained. Owing to unavoidable disparities in the simulation system, slight differences exist between \(\overset{\lower0.5em\hbox{$\smash{\scriptscriptstyle\frown}$}}{r}\) and r. By XORing the auxiliary file hi with \(\overset{\lower0.5em\hbox{$\smash{\scriptscriptstyle\frown}$}}{r}\), codeword Ō containing errors is derived. Subsequently, decoding Ō and recovering the random number \(w_{AB}\) selected by TA, denoted as \(w_{AB} = decode_{i} ()\). Since the disclosure and response entropy of the auxiliary file may leak information about \(w_{AB}\), a strong extractor is employed to extract \(w_{AB}\), thereby obtaining an unconditionally secure full entropy key K.
At this juncture, the key agreement process for vehicle Vi is concluded, enabling secure communication using the distributed key K. Figure 4 shows the process of vehicle access authentication and session key agreement.
Vehicle access authentication and session key agreement.
After vehicle Vi extracts the group key, it can utilize this key to engage in symmetric encrypted communication with other vehicles within the group. The strong PUF properties of the superlattice guarantee the changing of key for each session. Only the OBU device in vehicle Vi, equipped with a legitimate SSL-PUF, can retrieve the correct key from the publicly available auxiliary data provided by TA. Consequently, both the TA and each terminal device inherently possess a self-authentication function, enabling them to verify the authenticity of each other’s identities mutually. Legal devices possess the capability to obtain the correct key through helper data, while illegal devices are unable to derive the same key as legal ones. Each device is assigned a unique ID, and before each key agreement, the \({\rm H}mac_{C||ID}\) must be verified for identity authentication to safeguard against man-in-the-middle attacks.
The protocol presented in this paper is designed for intra-group communication among multiple vehicles, with each RSU functioning as a group, and having the capability to schedule updates for the group key. This protocol exhibits remarkable flexibility, enabling it to adapt to key establishment in diverse network topologies. Due to significant variations in the physical environments of individual terminal devices, there may be substantial discrepancies between the actual and registered responses. Consequently, this protocol accommodates different vehicles in selecting varied error correction code parameters to counteract adaptability issues stemming from temperature fluctuations or other environmental changes. When applying randomness extraction, the choice of extraction parameters should be based on the minimum value among the parameters of the two (or multiple) parties involved, serving as the final extraction parameters for all devices.
Security analysis and proof
-
Informal security analysis
-
(1)
Impersonation attack. Assuming C is the attacker, it can intercept messages on a public channel transmitted by a legitimate vehicle B which can join a specific group. Attacker C may impersonate vehicle B to perform TA verification, thereby acquiring auxiliary data hB. Nevertheless, owing to the unclonability of PUF, the attacker cannot derive an error codeword within the error correction range by XORing their own PUF output with hB, rendering it impossible to retrieve the group key. Given that cloning a specific SSL-PUF entails immense costs and resources, it is virtually unachievable. Consequently, only legitimate vehicles can obtain the group key.
-
(2)
Replay attack. During the process of vehicle A establishing a session key, attacker C intercepts the challenges sent between the vehicle and the TA, and replies them using the previous challenge, attempting to force them to communicate using the previous key. In this scheme, the TA deletes the used CRP after verifying each incentive signal, thereby preventing replay attacks.
-
(3)
Forward Secrecy. As TA and the vehicles collaboratively select challenge signals to generate CRPs during vehicle registration, these random numbers are not disclosed through public transmission in the channel, with the TA’s database storing the index pair of (HASH(IDV1||c),r). Even if the attackers manage to obtain the TA’s stored information, they remain unable to retrieve the CRPs. If the on-board OBU is compromised and an attacker gains access to the legitimate SSL-PUF. It’s worth noting that in our design, the challenge signal is uniquely and freshly generated between the vehicle and the TA for each communication session. This ensures the forward security in our scheme.
-
(1)
We selected schemes 46–48 as comparative schemes. These schemes are identity-based encryption systems that integrate elliptic curve and bilinear pairing technologies to facilitate identity verification and group communication. In Table 2, we analyzed five aspects (SF₁ to SF₅), including replay attack resistance (SF₁), man-in-middle attack resistance (SF₂), lightweight operation (SF₃), forward security (SF₄) and mutual authentication (SF₅). The comparison shows that our scheme has certain advantages in security and lightweight.
In summary, the multi-party key agreement protocol proposed in this paper, leveraging a trusted third party and the SSL-PUF, offers effectively defending against impersonation attacks, replay attacks, and more. Furthermore, given that a key agreement is conducted before each session and no key-related information is stored on the device side, forward security is guaranteed.
-
Formal security proof
In this sub-section, we presented a formal security proof for the access authentication and key agreement scheme, leveraging the Mao Boyd logic50 which was enhanced by Mao et al. based on BAN logic49. The symbols and fundamental rules of Mao Boyd’s logic are introduced in the following section. Drawing on the flow of protocol and the process of logical proof, an idealized protocol is obtained detailed below:
-
(a)
\(\begin{aligned} & V_{1} \to TA:Time_{1} {\kern 1pt} {\kern 1pt} {\kern 1pt} \Re {\kern 1pt} {\kern 1pt} {\kern 1pt} Hmac_{{K_{{c1}} }} (m_{1} ) \\ & V_{{\text{i}}} \to TA:Time_{i} {\kern 1pt} {\kern 1pt} {\kern 1pt} \Re {\kern 1pt} {\kern 1pt} {\kern 1pt} Hmac_{{K_{{ci}} }} (m_{i} )\,(i = 1,2,3 \ldots n) \\ \end{aligned}\)
-
(b)
\(\begin{aligned} & TA \leftarrow V_{1} :Time_{1} {\kern 1pt} {\kern 1pt} {\kern 1pt} \Re {\kern 1pt} {\kern 1pt} {\kern 1pt} Hmac_{{K_{{c1}} }} (m_{1}^{\prime } ) \\ & TA \leftarrow V_{i} :Time_{i} {\kern 1pt} {\kern 1pt} {\kern 1pt} \Re {\kern 1pt} {\kern 1pt} {\kern 1pt} Hmac_{{K_{{ci}} }} (m_{i}^{\prime } )\,(i = 1,2,3 \ldots n) \\ \end{aligned}\)
In the above assumption, V1 and Vi use different kc. According to the idealized rules of BAN logic, irrelevant information in the protocol can be ignored. After presenting an idealized description of the protocol, it is also essential for BAN logic to outline the security assumptions of the protocol.
Propositions (1)–(4) are the security assumptions of the system. Specifically, key sharing between vehicle V and TA is facilitated by SSL-PUF, hence Proposition (1) and (2) are established as the system’s security assumption. The timestamp Timei, being an instantaneous value within the protocol, is unique for each instance and non-reusable, establishing security assumption Proposition (3) and (4).
The formal security analysis given in Fig. 5.
The process of formal security analysis.
The objective of proving the access authentication and key agreement scheme is to enable the key agreement can be conducted between vehicles, that is:
The following proposition can be obtained from message (a):
Drawing upon (1) and (6), we deduce the following based on the authentication rules (16):
Considering the response observed by TA in the message (a) corresponding to the timestamp Timei, alongside proposition (6), the subsequent proposition is derived:
By applying the freshness rule proposition (19) to assumption (3) and proposition (8), the following proposition emerges:
By applying the nonce-verification rule (18) to assumption (8) and proposition (9), the following proposition emerges:
Therefore, TA can confirm the authenticity of vehicle Vi.
The following proposition can be obtained from message (b):
Drawing upon (2) and (11), we deduce the following based on the authentication rules (16):
Considering the response observed by Vi in the message (b) corresponding to the timestamp Timei, alongside proposition (11), the subsequent proposition is derived:
By applying the freshness rule proposition (19) to assumption (4) and proposition (13), the following proposition emerges:
By applying the nonce-verification rule (18) to proposition (12) and (14), the following proposition emerges:
Therefore, Vi trusts the authenticity of TA, thereby completing the mutual identity authentication between TA and Vi. Simultaneously, Vi can acquire auxiliary data hi from the trustworthy entity \(m^{\prime}_{i}\), which enables the recovery of the group key K. Subsequently, Vi can derive WAB through its local computation Ō = \(\overset{\lower0.5em\hbox{$\smash{\scriptscriptstyle\frown}$}}{r}\) ⊕ hi. By applying the operation K = Ext(wAB) to WAB, K can be obtained. In summary:
The target proposition (4) aligns with the proposition (13), thereby confirming the target.
Experiment
The excitation signal travels through the IMX6ULL development board and reaches the SSL-PUF board. Once the SSL-PUF generates a response signal, it is converted into a digital signal by the analog-to-digital converter and subsequently sent back to the I.MX6ULL development board.
We implemented the entire experimental process in C. The OBU comprises the following software modules: challenge generation and transmission module, response reception and preprocessing module, fuzzy extractors, and communication module. TA includes four software modules: challenge generation module, fuzzy extractors, communication module, and hash module.
The initial value is hashed by the hash module to produce challenge data, which is then transmitted to the SSL-PUF via the challenge generation and transmission module. The response data is acquired in the response reception and preprocessing module, and a consistent key K is derived using the fuzzy extractors.
In this section, we also selected schemes46,47,48,54 as comparative schemes. Given that they all rely on public-key encryption, their associated overhead is relatively high. In contrast, our scheme leverages semiconductor superlattice digital PUFs, eliminating the necessity for pre-installed keys and simplifying computational processes, thereby incurring a relatively lower overhead. Below, we will assess and compare the computational overhead and communication burden of these protocols.
In this protocol, we primarily analyze the computational overhead of vehicles (terminals) and TA. We selected the Cortex-A7 I.MX6ULL development board as the OBU processor and interconnected it with an SSL-PUF board (comprising of a digital-to-analog converter, an SSL-PUF chip, and an analog-to-digital converter) to establish a terminal experimental environment. The experimental environment of TA is shown in Table 3. For the experiment, we employed the OpenSSL-1.0.2e library to simulate cryptographic algorithm operations, with the basic operations and cryptographic operation durations listed in Table 4. Notably, Tpuf, TBCHE, TBCHD, and TPA, are exclusive operations of the SSL-PUF, signifying the response time of the SSL-PUF, the time required for BCH encoding/decoding operations, and the time for privacy enhancement operations, respectively. The parameter of BCH error correction code (n, k, t) = (255, 147, 14). We choose SM4 as the symmetric encryption algorithm, SM3 as the hash function. The computational overhead of the schemes compared to ours is calculated based on specific details outlined in their respective protocols. The specific operations are extracted from the protocol design, and the ultimate computational overhead is derived using the basic overhead figures provided in Table 4.
-
Computational costs
The identity authentication and key agreement phases serve as the primary considerations when determining computational overhead. In our protocol, each full key negotiation process for vehicle Vi entails 4 times of hash operations, 2 times of PUF operations, 1 time of BCH decoding operation, and 1 time of confidentiality-enhanced computation, resulting in a total computational overhead of 703.1 microseconds for Vi. The TA, on the other hand, executes 5 times of hash operations, 1 time of BCH encoding operation,1 time of confidentiality-enhanced computation, and 1 time of pseudo-random number operation, amounting to a total computational overhead of 17.53 microseconds. Consequently, the overall computational overhead of our protocol stands at 720.63 microseconds. The computational overheads of all pertinent protocols46,47,48,54 have been measured similarly, as presented in Tables 4 and 5. To provide a more intuitive comparison of TA operation times, Fig. 6 illustrates how the time taken by TA to authenticate vehicle identity information and distribute extracted group key auxiliary information varies with an increasing number of authenticated vehicles. Our scheme demonstrates a clear advantage in terms of computational cost.
Comparison of TA runtime across different schemes.
-
Communication costs
In VANETs, given the limited capacity of smart devices, the communication cost is of paramount importance. Communication overhead signifies the number of bits exchanged among participants to finalize the identity verification process. In this subsection, we present a comparison of the communication overhead between the proposed protocol and related protocols, referencing46,47,48,54. Our primary focus for calculating the communication overhead is on the messages exchanged during the authentication and key agreement phases between vehicle Vi and the TA. The lengths of the parameters utilized in this scheme are detailed in Table 6 Specifically, the lengths of the challenge c, response r, error correction code u, and key agreement auxiliary data h for the SSL-PUF are all configured to be 256 bits.
In our protocol, any vehicle Vi is required to exchange an authentication message with the TA, which includes \(m_{i} = c_{i} ||Time_{i} ||u_{i} ||ID_{Vi}\) and \(Hmac_{{K_{C} }} (m_{i} )\), totaling 704 bits of data to be transmitted. The TA, in response, sends key negotiation data comprising Timei and auxiliary data hi and \(Hmac_{{K_{C} }} (m_{i}^{\prime } )\) to Vi, amounting to 432 bits of data. The communication overhead for all pertinent protocols46,47,48,54 has been measured similarly, with the comparison results presented in Table 7.
It is evident that our scheme, which is based on semiconductor SSL-PUF, boasts lower overhead and is more lightweight compared to those relying on elliptic curve and bilinear pairing technologies.
Discussion
This paper focuses on the characteristics of high mobility, low latency, and high-security requirements of the VANETs. Leveraging the SSL-PUF, we proposed a lightweight access authentication and key agreement scheme tailored for VANETs. Drawing upon the system model of vehicle road collaboration, we meticulously designed the identity authentication and key agreement processes for vehicles, and conducted a thorough security analysis under various attack scenarios, including impersonation attacks, replay attacks, and man-in-the-middle attacks. Ultimately, through experimental validation and comparative analysis, we demonstrated that the scheme proposed in this paper exhibits substantial advantages in terms of both security and lightweight. In the future, we will further investigate the use of SSL-PUFs to enhance intra-group communication management functions, as well as to implement switching authentication functions between groups, enabling SSL-PUFs to play a greater role in VANETs.
Methods
BAN logic is a set of logical rules based on postulates and assumptions for defining trustworthy and secure message exchange protocols. Utilizing Ban logic to prove identity authentication protocols typically encompasses three stages: the idealization of protocol messages, the security assumptions of the protocol, and the process of reasoning and proof. Firstly, we will introduce the symbolic interpretations utilized in Ban logic proofs, followed by the presentation of fundamental proof rules. The Ban logic definition construction is described as follows38,51:
-
(a)
\(P| \equiv X\) denotes P believes X is true.
-
(b)
\(P \triangleleft M\) denotes P sees M.
-
(c)
\(P\mathop \triangleleft \limits^{K} M\) denotes P sees M decrypt with secret K.
-
(d)
\(P|\sim M\) denotes P sent M.
-
(e)
\(P \Rightarrow M\) denotes P can control M.
-
(f)
\(\# (M)\) denotes that M is fresh and has never been sent before.
-
(g)
\(P\mathop \leftrightarrow \limits^{K} Q\) denotes P and Q share a secret K.
-
(h)
\(\{ M\}_{K}\) denotes M is hashed using a secret K.
-
(i)
\(A{\kern 1pt} {\kern 1pt} \Re {\kern 1pt} {\kern 1pt} B\) denotes A concatenated with B.
W. Mao et al. further abstracted and categorized the protocol data of identity authentication protocols, utilizing Ban logic, into such classes as atomic messages, challenges, challenged responses, responses, and meaningless messages. Additionally, they introduced novel inference rules. For a comprehensive understanding, please consult the paper by W. Mao et al.50. Here, the essential rules for analysis of our scheme are described as follows49,50,51:
R1: The authentication rules:
R2: Nonce-verification rule:
R3: Freshness rule:
Data availability
All data generated or analysed during this study are included in this published article.
References
Lee, I. & Lee, K. The Internet of Things (IoT): Applications, investments, and challenges for enterprises. Bus. Horizons 58(4), 431–440. https://doi.org/10.1016/j.bushor.2015.03.008(2015) (2015).
Yang, Y. Y. et al. Survey of IoT security research: Threats, detection and defense. J. Commun. 42, 188. https://doi.org/10.11959/j.issn.1000-436x.2021124 (2021).
Horng, S. J. et al. Enhancing security and privacy for identity-based batch verification scheme in VANETs. IEEE Trans. Veh. Technol. 99, 1–1. https://doi.org/10.1109/TVT.2015.2406877 (2017).
Wang, N. et al. A blockchain based privacy-preserving federated learning scheme for Internet of Vehicles. Digit. Commun. Netw. 10, 126–134. https://doi.org/10.27251/d.cnki.gnjdc.2023.001045 (2024).
Chen, J. N. et al. Efficient certificate-based aggregate signature scheme for vehicular ad hoc networks. IET Netw. 9, 290–297. https://doi.org/10.1049/iet-net.2020.0019 (2020).
Umar, M. et al. Provable secure identity-based anonymous and privacy-preserving inter-vehicular authentication protocol for VANETs using PUF. IEEE Trans. Veh. Technol. 70, 12158–12167. https://doi.org/10.1109/TVT.2021.3118892 (2021).
Venkatasamy, T. et al. Intrusion detection system for V2X communication in VANET networks using machine learning-based cryptograph ic protocols. Sci. Rep. 14, 31780. https://doi.org/10.1038/s41598-024-82313-x (2024).
Rajkumar, Y. & Santhosh Kumar, S. V. N. A Dickson polynomial based group key agreement authentication scheme for ensuring conditional privacy preservation and traceabilityin VANETs. Sci. Rep. 15, 6211. https://doi.org/10.1038/s41598-025-89208-5 (2025).
Xie, J., Liu, J., Wu, H., Xu, L. & Chen, X. Lightweight and information-theoretical secure key agreement protocol based on superlattice PUF. J. Cryptol. Res. 11(2), 387–402. https://doi.org/10.13868/j.cnki.jcr.000687 (2024).
Yuhan, C. Research on lightweight authentication key agreement protocols in the internet of vehicles environment. Internet Things Technol. 14, 57–60. https://doi.org/10.16667/j.issn.2095-1302.2024.06.015 (2024).
Chen Fuyuan, D. J. & Dong, Z. Overview of internet of vehicles security protection technology. Telecommun. Sci. 39, 1. https://doi.org/10.11959/j.issn.1000-0801.2023046 (2023).
Xu, Z. et al. A secure and computationally efficient authentication and key agreement scheme for internet of vehicles. Comput. Electr. Eng. 95, 107409. https://doi.org/10.1016/j.compeleceng.2021.107409 (2021).
Wang Xinming, D. K. & Cao, Y. Sm2-based authentication and key agreement protocol for internet of vehicles. Internet Things Technol. 14, 62–65. https://doi.org/10.16667/j.issn.2095-1302.2024.03.015 (2024).
Ying, B. & Nayak, A. Anonymous and lightweight authentication for secure vehicular networks. IEEE Trans. Veh. Technol. 66, 10626–10636. https://doi.org/10.1109/TVT.2017.2744182 (2017).
Wang 2021, T. Y. Overview of the development of mobile communication security technology. Commun. Technol. 54, 2291–2300. https://doi.org/10.3969/j.issn.1002-0802.2021.10.001.
Javaid, U., Aman, M. N. & Sikdar, B. A scalable protocol for driving trust management in internet of vehicles with blockchain. IEEE Internet Things J. 7, 11815–11829. https://doi.org/10.1109/JIOT.2020.3002711 (2020).
Elhalawany, B. M., El-Banna, A. A. A. & Wu, K. Physical-layer security and privacy for vehicle-to-everything. IEEE Commun. Mag. 57, 84–90. https://doi.org/10.1109/MCOM.001.1900141 (2019).
Yinzhu, Y. Research on blockchain based secure authentication and privacy protection scheme in internet of vehicles. Master’s thesis, University of Electronic Science and Technology of China. https://doi.org/10.27005/d.cnki.gdzku.2023.004688 (2023).
Pappu, R. et al. Physical one-way functions. Science 297, 2026–2030. https://doi.org/10.1126/science.1074376 (2002).
Maes, R. Physically unclonable functions: Properties, 49–80 (2013).
Raya, M. & Hubaux, J. P. The security of vehicular ad hoc networks. Secur. Ad hoc Sensor Netw. ACM https://doi.org/10.1145/1102219.1102223 (2005).
Calandriello, G., Papadimitratos, P. & Hubaux, J. P, et al. Efficient and robust pseudonymous authentication in VANET. In The 4th ACM International Workshop on Vehicular Ad Hoc Networks, 19–28. https://doi.org/10.1145/1287748.1287752 (2007).
Zhang, C., Lu, R. & Lin, X, et al. An efficient identity-based batch verification scheme for vehicular sensor networks. In IEEE INFOCOM 2008—The 27th Conference on Computer Communications, 246–250. https://doi.org/10.1109/INFOCOM.2008.58 (2008).
Zhang, L. et al. A scalable robust authentication protocol for secure vehicular communications. IEEE Trans. Veh. Technol. 59, 1606–1617. https://doi.org/10.1109/TVT.2009.2038222 (2010).
Lee, C. C. & Lai, Y. M. Toward a secure batch verification with group testing for VANET. Wirel. Netw. 19, 1441–1449. https://doi.org/10.1007/s11276-013-0543-7 (2013).
Bayat, M. et al. A secure authentication scheme for VANETs with batch verification. Wirel. Netw. 20, 2275–2289. https://doi.org/10.1007/s11276-014-0881-0 (2014).
Maes, R., Herrewege, A. V. & Verbauwhede, I. Pufky: A fully functional PUF-based cryptographic key generator. In Prouff, E. & Schaumont, P. (eds.) Cryptographic Hardware and Embedded Systems—CHES 2012, 302–319 (2012).
Semiconductors, N. Nxp strengthens SmartMX2 security chips with PUF anti-cloning technology. Accessed: 2023-02-12. (2023)
Brzuska, C., Fischlin, M. & Schrder, H, et al. Physically uncloneable functions in the universal composition framework. In Rogaway, P. (ed.) Advances in Cryptology—CRYPTO 2011, 51–70 (2011).
Beckmann, N. & Potkonjak, M. Hardware-based public-key cryptography with public physically unclonable functions. In Katzenbeisser, S. & Sadeghi, A.-R. (eds.) Information hiding, 206–220 (2009).
Zheng, Z., Yanan, L. & Daren, Z. PUF-based kerberos extension protocol with formal analysis. Netinfo Secur. 20, 91. https://doi.org/10.3969/j.issn.1671-1122.2020.12.012 (2020).
Aman, M. N., Chua, K. C. & Sikdar, B. Mutual authentication in IoT systems using physical unclonable functions. IEEE Internet Things J. https://doi.org/10.1109/JIOT.2017.2703088 (2017).
Chuang, Y. H. & Lei, C. L. PUF based authenticated key exchange protocol for IoT without verifiers and explicit CRPs. IEEE Access https://doi.org/10.1109/ACCESS.2021.3103889 (2021).
Pehl, M., Frisch, C. & Feist, C. P., et al. KeLiPUF: A key-distribution protocol for lightweight devices using physical unclonable functions[C/OL]. In Proceedings of 17th escar Europe: Embedded Security in Cars. https://d-nb.info/1199614297/34. (2019)
Li, S. et al. A provably secure and practical PUF-based end-to-end mutual authentication and key exchange protocol for IoT. IEEE Sens. J. 21, 5487–5501. https://doi.org/10.1109/JSEN.2020.3028872 (2021).
Zheng, Y. et al. PUF-based mutual authentication and key exchange protocol for peer-to-peer IoT applications. IEEE Trans. Depend. Secur. Comput. 20, 3299–3316. https://doi.org/10.1109/TDSC.2022.3193570 (2023).
Tong, X., Chen, X. & Xu, S. Advances in superlattice cryptography research. Chin. Sci. Bull. 65(2–3), 108–116. https://doi.org/10.1360/TB-2019-0291(2021) (2021).
Xu, L. Research on PUF theory and typical cryptography applications based on semiconductor superlattice (Beijing University of Posts and Telecommunications, 2023). https://doi.org/10.26969/d.cnki.gbydu.2023.000340.
Liu, W. et al. A secret key distribution technique based on semiconductor superlattice chaos devices. Sciellce Bull. 63(16), 1034–1036. https://doi.org/10.1016/j.scib.2018.06.017 (2018).
Wu, H. et al. An experimental demonstration of long-haul public-channel key distribution using matched superlattice physical unclonable function pairs. Sci. Bull. 65, 879–882. https://doi.org/10.1016/j.scib.2020.02.029 (2020).
Xinhai Tong, S. X. & Xiaoming, C. Research progress on superlattice codes. Chin. Sci. Bull. 65, 10–18. https://doi.org/10.1360/TB-2019-0291 (2020).
H, W. The Technical research and system implementation of the superlattice key distribution. Ph.D. thesis, University of Science and Technology of China (2021).
Wu, H. et al. Design and implementation of true random number generators based on semiconductor superlattice chaos. Microelectron. J. 114, 105119. https://doi.org/10.1016/j.mejo.2021.105119 (2021).
Dodis, Y. et al. Fuzzy extractors: How to generate strong keys from biometrics and other noisy data. Adv. Eurocrypt. 38(1), 97–139. https://doi.org/10.1137/060651380 (2006).
Ryan, W. & Lin, S. Channel codes: Classical and modern (2009).
Cui, J., Wei, L., Zhang, J., Xu, Y. & Zhong, H. An efficient message-authentication scheme based on edge computing for vehicular ad hoc networks. IEEE Trans. Intell. Transp. Syst. 20, 1621–1632. https://doi.org/10.1109/TITS.2018.2827460 (2019).
Zhiwang, H. E. Anonymous group key distribution scheme for the internet of vehicles. Chin. J. Netword Inf. Secur. 9, 127. https://doi.org/10.11959/j.issn.2096-109x.2023070 (2023).
Zhong, H., Zhang, S., Cui, J., Wei, L. & Liu, L. Broadcast encryption scheme for V2I communication in VANETs. IEEE Trans. Veh. Technol. 71, 2749–2760. https://doi.org/10.1109/TVT.2021.3113660 (2022).
Burrows, M., Abadi, M. & Needham, R. M. A logic of authentication. ACM Trans. Comput. Syst. 8, 18–36. https://doi.org/10.1145/77648.77649 (1990).
Mao, W. & Boyd, C. Towards formal analysis of security protocols. In [1993] Proceedings Computer Security Foundations Workshop VI, 147–158, https://doi.org/10.1109/CSFW.1993.246631 (1993).
Alfadhli, S. A. et al. MFSPV: A multi-factor secured and lightweight privacy-preserving authentication scheme for VANETs. IEEE Access 8, 142858–142874. https://doi.org/10.1109/ACCESS.2020.3014038 (2020).
Luo, D., Zhang, Y., Sun, G., Yu, H. & Niyato, D. An efficient consensus algorithm for blockchain-based cross-domain authentication in bandwidth-constrained wide-area IoT networks. IEEE Internet Things J. 11, 31917–31931. https://doi.org/10.1109/JIOT.2024.3420719 (2024).
Lin, H.-T. & Jhuang, W.-L. Blockchain-based lightweight certificateless authenticated key agreement protocol for V2V communications in IoV. IEEE Internet Things J. 11, 27744–27759. https://doi.org/10.1109/JIOT.2024.3400320 (2024).
Liang, Y., Luo, E. & Liu, Y. Physically secure and conditional-privacy authenticated key agreement for VANETs. IEEE Trans. Veh. Technol. 72, 7914–7925. https://doi.org/10.1109/TVT.2023.3241882 (2023).
Pu, C., Choo, K. K. & Korać, D. A lightweight and anonymous application-aware authentication and key agreement protocol for the internet of drones. IEEE Internet Things J. 11, 19790–19803. https://doi.org/10.1109/JIOT.2024.3367799 (2024).
Acknowledgements
This work is supported by the Fundamental Research Funds for the Central Universities under Grant Number: 3282024014, 3282023017, 3282024056.
Author information
Authors and Affiliations
Contributions
H.F., L.X. and J.X. proposed and guided the work. X.L. and M.L. conceived and conducted the experiments, wrote the paper. The security analysis section is handled by M.L. and L.X. J.X. and X.L. complete the performance analysis section. R.S. helped with results analysis. All authors reviewed the manuscript.
Corresponding authors
Ethics declarations
Competing interests
The authors declare no competing interests.
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
About this article
Cite this article
Li, X., Li, M., Xu, L. et al. Lightweight identity authentication and key agreement scheme for VANETs based on SSL-PUF. Sci Rep 15, 21469 (2025). https://doi.org/10.1038/s41598-025-06098-3
Received:
Accepted:
Published:
Version of record:
DOI: https://doi.org/10.1038/s41598-025-06098-3